目录
一、构建主 DNS 域名解析服务器
1.主域名服务器概述
主域名服务器通常架设在 Internet 环境中,提供某一个域或几个域内的主机名与 IP地址的查询服务。为了分担域名查询的压力、提供区域数据的备份,有时还会另外架设一台从 域名服务器,与主域名服务器同时提供服务。
2.构建主域名服务器步骤及示例
实验环境:
- 主、从域名服务器均位于 Internet 中,所负责的 DNS 区域为“Rz.com”
- 主服务器 IP 地址 192.168.100.100/24,主机名为 ns1.Rz.com
- 从服务器 IP 地址 192.168.100.110/24,主机名为 ns2.Rz.com
- 在 linuxli.com 区域中,除了 NS 记录以外提供的解析记录包括如下内容:
网站服务器:www.88851.top, IP地址 192.168.100.10/24
邮件服务器:mail.Rz.com,IP 地址 192.168.100.1/24
新闻服务器:news.Rz.com,IP 地址 192.168.100.2/24
论坛服务器:bbs.Rz.com, IP 地址 192.168.100.2/24
- 参考上述各服务器的地址映射关系,为 192.168.100.0/24 网段提供反向解析
- 设置 linuxli.com 域的泛域名解析,对应 IP 地址 192.168.100.10/24
- 客户机将首选、备用 DNS 服务器分别设为 192.168.100.100 和 192.168.100.110
(1).确认本机的网络地址、主机映射、默认 DNS 服务器地址
[root@ns1 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:a5:9f:9d brd ff:ff:ff:ff:ff:ff
inet 192.168.108.61/24 brd 192.168.108.255 scope global noprefixroute dynamic ens33
valid_lft 976sec preferred_lft 976sec
inet6 fe80::263a:6187:5a6e:8890/64 scope link noprefixroute
valid_lft forever preferred_lft forever
inet6 fe80::2927:91cc:cf86:e229/64 scope link tentative noprefixroute dadfailed
valid_lft forever preferred_lft forever
3: ens34: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:a5:9f:a7 brd ff:ff:ff:ff:ff:ff
inet 192.168.100.1/24 brd 192.168.100.255 scope global noprefixroute ens34
valid_lft forever preferred_lft forever
[root@ns1 ~]# hostname
ns1.rz.com
更改主机映射文件:
[root@ns1 ~]# vim /etc/hosts
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
192.168.100.1 ns1.Rz.com
192.168.100.2 ns2.Rz.com
查看DNS:
[root@ns1 ~]# cat /etc/resolv.conf
# Generated by NetworkManager
search localdomain rz.com
nameserver 192.168.100.1
nameserver 192.168.100.2(2).修改主配置文件 /etc/named.conf
[root@ns1 ~]# rpm -qa |grep bind
bind-libs-9.11.4-26.P2.el7_9.9.x86_64
bind-9.11.4-26.P2.el7_9.9.x86_64
bind-utils-9.11.4-26.P2.el7_9.9.x86_64
bind-libs-lite-9.11.4-26.P2.el7_9.9.x86_64
bind-export-libs-9.11.4-26.P2.el7_9.9.x86_64
bind-chroot-9.11.4-26.P2.el7_9.9.x86_64
bind-license-9.11.4-26.P2.el7_9.9.noarch
[root@ns1 ~]# cd /etc/
[root@ns1 etc]# cp named.conf named.conf.$(date +%Y%m%d%H%M)
[root@ns1 etc]# vim named.conf
options {
13 listen-on port 53 { 192.168.100.1; };
14 listen-on-v6 port 53 { ::1; };
15 directory "/var/named";
16 dump-file "/var/named/data/cache_dump.db";
17 statistics-file "/var/named/data/named_stats.txt";
18 memstatistics-file "/var/named/data/named_mem_stats.txt";
19 recursing-file "/var/named/data/named.recursing";
20 secroots-file "/var/named/data/named.secroots";
21 allow-query { any; };
22
23 recursion yes;
24
25 # dnssec-enable no;
26 # dnssec-validation no;
27
28 bindkeys-file "/etc/named.root.key";
29 managed-keys-directory "/var/named/dynamic";
30 pid-file "/run/named/named.pid";
31 session-keyfile "/run/named/session.key";
32 };
33
34 logging {
35 channel default_debug {
36 file "data/named.run";
37 severity dynamic;
38 };
39 };
40
41 zone "Rz.com" IN {
42 type master;
43 file "Rz.com.zone";
44 allow-transfer { 192.168.100.2; };
45 };
46 zone "100.168.192.in-addr.arpa" IN {
47 type master;
48 file "192.168.100.arpa";
49 allow-transfer { 192.168.100.2; };
50 };
检查配置文件:
[root@ns1 etc]# named-checkconf /etc/named.conf
(3).建立正、反向区域数据文件
1>建立正向区域数据文件
[root@ns1 etc]# cd /var/named/
[root@ns1 named]# cp -p named.empty Rz.com.zone
[root@ns1 named]# vim Rz.com.zone
$TTL 1D
@ IN SOA Rz.com. root.ns1.Rz.com. (
2022071901 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ) ; minimum
NS ns1.Rz.com.
NS ns2.Rz.com.
MX 10 mail.Rz.com.
ns1 A 192.168.100.1
ns2 A 192.168.100.2
www A 192.168.100.10
mail A 192.168.100.1
news A 192.168.100.12
bbs CNAME news
* A 192.168.100.10
2>建立反向区域数据文件
[root@ns1 named]# cp -p Rz.com.zone 192.168.100.arpa
[root@ns1 named]# vim 192.168.100.arpa
$TTL 1D
@ IN SOA Rz.com. root.ns1.Rz.com. (
2022071901 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ) ; minimum
NS ns1.Rz.com.
NS ns2.Rz.com.
1 PTR ns1.Rz.com.
2 PTR ns2.Rz.com.
10 PTR www.Rz.com.
1 PTR mail.Rz.com.
12 PTR news.Rz.com.
12 PTR bbs.Rz.com.
3>测试配置文件
[root@ns1 named]# named-checkzone linuxli.com Rz.com.zone
zone linuxli.com/IN: loaded serial 0
OK
[root@ns1 named]# named-checkzone 1.168.192-addr.arpa 192.168.100.arpa
zone 1.168.192-addr.arpa/IN: loaded serial 2022071901
OK
(4).启动 named 服务或重载配置
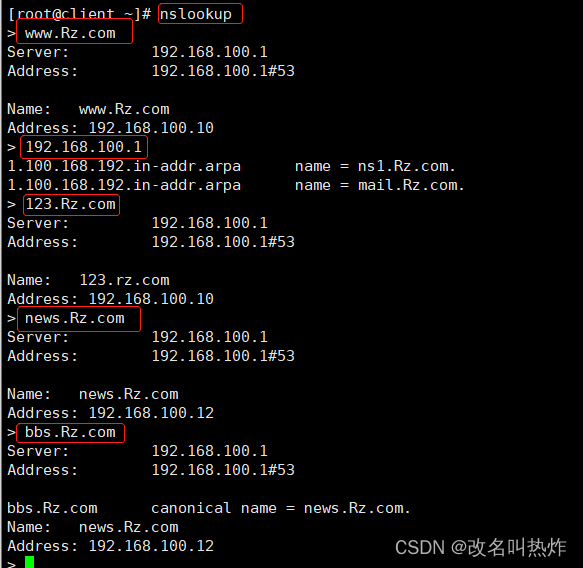
[root@ns1 named]# systemctl restart named(5).客户机测试
[root@client ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:0e:65:b7 brd ff:ff:ff:ff:ff:ff
inet 192.168.108.62/24 brd 192.168.108.255 scope global noprefixroute dynamic ens33
valid_lft 1717sec preferred_lft 1717sec
3: ens34: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:0e:65:c1 brd ff:ff:ff:ff:ff:ff
inet 192.168.100.3/24 brd 192.168.100.255 scope global noprefixroute ens34
valid_lft forever preferred_lft forever
[root@client ~]# cat /etc/resolv.conf
# Generated by NetworkManager
search rz.com
nameserver 192.168.100.1
nameserver 192.168.100.2
二、构建从 DNS 域名解析服务器
1.从域名解析服务器概述
与主域名解析服务器提供完全相同的 DNS 解析服务,通常用于 DNS 服务器的热备份。对客户机来说,无论使用主域名服务器还是从域名服务器,查询结果都是一样的。
2.构建从域名服务器步骤及示例
实验环境:
- 主、从域名服务器均位于 Internet 中,所负责的 DNS 区域为“linuxli.com”
- 主服务器 IP 地址 192.168.100.100/24,主机名为 ns1.amber.com
- 从服务器 IP 地址 192.168.100.110/24,主机名为 ns2.linuxli.com
- 客户机将首选、备用 DNS 服务器分别设为 192.168.100.1 和 192.168.100.2
(1).确认本机的网络地址、主机映射、默认 DNS 服务器地址
[root@ns2 ~]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST> mtu 1500 qdisc pfifo_fast state DOWN group default qlen 1000
link/ether 00:0c:29:99:9e:5a brd ff:ff:ff:ff:ff:ff
3: ens34: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:99:9e:64 brd ff:ff:ff:ff:ff:ff
inet 192.168.100.2/24 brd 192.168.100.255 scope global noprefixroute ens34
valid_lft forever preferred_lft forever
[root@ns2 ~]# hostname
ns2.rz.com
##更改主机映射文件
[root@ns2 ~]# cat /etc/hosts
127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4
::1 localhost localhost.localdomain localhost6 localhost6.localdomain6
192.168.100.1 ns1.Rz.com
192.168.100.2 ns2.Rz.com
##查看DNS
[root@ns2 ~]# cat /etc/resolv.conf
# Generated by NetworkManager
search rz.com
nameserver 192.168.100.1
nameserver 192.168.100.2(2).修改主配置文件/etc/named.conf
[root@ns2 ~]# yum -y install bind bind-utils bind-chroot
[root@ns2 ~]# cd /etc/
[root@ns2 etc]# cp named.conf named.conf.$(date +%Y%m%d%H%M)
[root@ns2 etc]# vim named.conf
options {
listen-on port 53 { 192.168.100.2; };
listen-on-v6 port 53 { ::1; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
recursing-file "/var/named/data/named.recursing";
secroots-file "/var/named/data/named.secroots";
allow-query { any; };
recursion yes;
// dnssec-enable yes;
// dnssec-validation yes;
//
/* Path to ISC DLV key */
// bindkeys-file "/etc/named.root.key";
// managed-keys-directory "/var/named/dynamic";
// pid-file "/run/named/named.pid";
// session-keyfile "/run/named/session.key";
};
logging {
channel default_debug {
file "data/named.run";
severity dynamic;
};
};
zone "Rz.com" IN {
type slave;
masters { 192.168.100.1; };
file "slaves/Rz.com.zone";
};
zone "100.168.192.in-addr.arpa" IN {
type slave;
masters { 192.168.100.1; };
file "slaves/192.168.100.arpa";
};

检查配置文件:
[root@ns2 etc]# named-checkconf /etc/named.conf
(3).启动 named 服务,查看区域数据文件是否下载成功
[root@ns2 etc]# ll /var/named/slaves/
total 0
[root@ns2 etc]# systemctl restart named
[root@ns2 etc]# ll /var/named/slaves/
total 8
-rw-r--r-- 1 named named 471 Jul 20 08:26 192.168.100.arpa
-rw-r--r-- 1 named named 475 Jul 20 08:26 Rz.com.zone
(4).客户机测试
[root@client ~]# cat /etc/resolv.conf
# Generated by NetworkManager
search rz.com
nameserver 192.168.100.2 //优先最上面得dns
nameserver 192.168.100.1

(5).将主域名服务器增加地址解析记录,修改序列号+1 查看从域名服务器/var/named/slaves/下文件的时间
从服务器:
[root@ns2 slaves]# ll
total 8
-rw-r--r-- 1 named named 471 Jul 20 08:26 192.168.100.arpa
-rw-r--r-- 1 named named 475 Jul 20 08:26 Rz.com.zone
主服务器:
[root@ns1 ~]# cd /var/named/
[root@ns1 named]# vim Rz.com.zone

[root@ns1 named]# named-checkzone Rz.com Rz.com.zone
zone Rz.com/IN: loaded serial 2022071902
OK
[root@ns1 named]# vim 192.168.100.arpa 
[root@ns1 named]# named-checkzone 1.168.192.in-addr.arpa 192.168.100.arpa
zone 1.168.192.in-addr.arpa/IN: loaded serial 2022071902
OK
(6).修改主域名解析服务器的主配置文件,添加 also-notify { 192.168.100.110; }; 观察从域名解析服务器区域数据文件是否更新
[root@ns1 named]# vim /etc/named.conf
重新加载主域名解析服务器配置文件:
[root@ns1 named]# systemctl reload named.service发现从域名服务器已自动更新区域配置文件:
[root@ns2 slaves]# ll /var/named/slaves/
total 8
-rw-r--r-- 1 named named 471 Jul 20 08:38 192.168.100.arpa
-rw-r--r-- 1 named named 475 Jul 20 08:38 Rz.com.zone
客户机测试:
























 271
271











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










