实验 9.11.3 使用AS_PATH属性
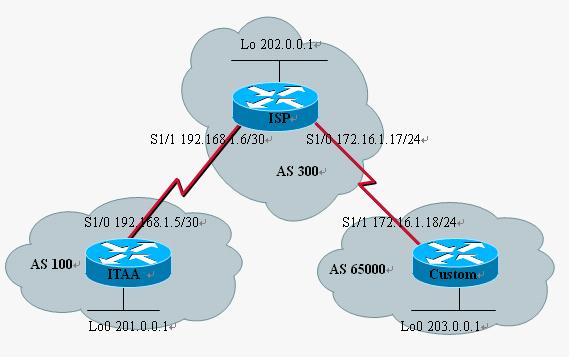
一、实验拓扑图:
二、实验目的:
国际互联网培训中心ITAA和ISP是对等的互联关系,现在ISP扩展自己的业务,给他的客户分配私有AS号码,但同时不能让他的客户得到ITAA内部的路由,自然也不能将AS65000这个私有AS号码发布出去,要在ISP路由器中作配置控制过滤。
三、具体实验内容:
步骤:
| -实验基本配置(包括BGP的配置); |
| -在ISP上将其客户BGP路由信息中的私有AS过滤掉; |
| -在ISP上过滤AS号码为100的路由信息,防止进入AS65000; |
| -整体测试 |
实验基本配置(包括BGP的配置):
| ITAA#sh run Building configuration...
Current configuration : 1328 bytes ! version 12.3 service timestamps debug datetime msec service timestamps log datetime msec no service password-encryption ! hostname ITAA ! interface Loopback0 ip address 201.0.0.1 255.255.255.0 ! interface Serial1/0 ip address 192.168.1.5 255.255.255.252 serial restart-delay 0 ! router bgp 100 no synchronization bgp log-neighbor-changes network 201.0.0.0 neighbor 192.168.1.6 remote-as 300 no auto-summary ! end | ISP#sh run Building configuration...
Current configuration : 1380 bytes ! version 12.3 service timestamps debug datetime msec service timestamps log datetime msec no service password-encryption ! hostname ISP interface Loopback0 ip address 202.0.0.1 255.255.255.0 interface Serial1/0 ip address 172.24.1.17 255.255.255.252 serial restart-delay 0 ! interface Serial1/1 ip address 192.168.1.6 255.255.255.252 serial restart-delay 0 ! router bgp 300 no synchronization bgp log-neighbor-changes network 202.0.0.0 neighbor 172.24.1.18 remote-as 65000 neighbor 192.168.1.5 remote-as 100 no auto-summary ! end |
| Custom#sh run Building configuration...
Current configuration : 1332 bytes ! version 12.3 service timestamps debug datetime msec service timestamps log datetime msec no service password-encryption ! hostname Custom ! interface Loopback0 ip address 203.0.0.1 255.255.255.0 ! interface Serial1/1 ip address 172.24.1.18 255.255.255.252 serial restart-delay 0 router bgp 65000 no synchronization bgp log-neighbor-changes network 203.0.0.0 neighbor 172.24.1.17 remote-as 300 no auto-summary end |
在ISP上将其客户BGP路由信息中的私有AS过滤掉:
一条命令搞定:
| ISP(config-router)#nei 192.168.1.5 remove-private-AS |
在ISP上过滤AS号码为100的路由信息,防止进入AS65000:
| ISP(config)#ip as-path access-list 1 deny ^100$ ISP(config)#ip as-path access-list 1 per .* (注意这些符号)
ISP(config-router)#nei 172.24.1.18 filter-list 1 out |
整体测试:
去除私有AS验证:
在ISP上面没有做私有AS去除的时候,在ITAA路由器上的BGP信息是这样的:
| ITAA# sh ip bgp BGP table version is 4, local router ID is 201.0.0.1 Status codes: s suppressed, d damped, h history, * valid, > best, i - internal, r RIB-failure, S Stale Origin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path *> 201.0.0.0 0.0.0 .0 0 32768 i *> 202.0.0.0 192.168.1.6 0 0 300 i *> 203.0.0.0 192.168.1.6 0 300 65000 i |
65000这个私有AS号码被发布到了公网上!
于是我们去除后:
| ITAA# sh ip bgp BGP table version is 5, local router ID is 201.0.0.1 Status codes: s suppressed, d damped, h history, * valid, > best, i - internal, r RIB-failure, S Stale Origin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path *> 201.0.0.0 0.0.0 .0 0 32768 i *> 202.0.0.0 192.168.1.6 0 0 300 i *> 203.0.0.0 192.168.1.6 0 300 i |
过滤ITAA路由到Custom的验证:
在未过滤之前:
| Custom#sh ip bgp BGP table version is 6, local router ID is 203.0.0.1 Status codes: s suppressed, d damped, h history, * valid, > best, i - internal, r RIB-failure, S Stale Origin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path *> 201.0.0.0 172.24.1.17 0 300 100 i *> 202.0.0.0 172.24.1.17 0 0 300 i *> 203.0.0.0 0.0.0 .0 0 32768 i |
Custom上面有ITAA内部的路由条目;
过滤之后:
| Custom#sh ip bgp BGP table version is 5, local router ID is 203.0.0.1 Status codes: s suppressed, d damped, h history, * valid, > best, i - internal, r RIB-failure, S Stale Origin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path *> 202.0.0.0 172.24.1.17 0 0 300 i *> 203.0.0.0 0.0.0 .0 0 32768 i |
OK,搞定!






















 2万+
2万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








