背景
项目业务端服务器部署在内网中,需要通过 socks5 代理服务器 ssh 登录到业务端服务器上。
环境假设信息
业务端服务器
ip:192.168.122.32
端口号:22
登录方式:私钥登录
代理服务器
IP:192.24.122.33
代理方式:socks5 代理
port:29267
运行参数
ssh -v -o ProxyCommand='ncat --proxy-type socks5 --proxy 192.24.122.33:29267 %h %p' root@192.168.122.32
执行示例
longyu@debian:~$ ssh -v -o ProxyCommand='ncat --proxy-type socks5 --proxy 192.24.122.33:29267 %h %p' root@192.168.122.32
OpenSSH_8.4p1 Debian-5, OpenSSL 1.1.1n 15 Mar 2022
debug1: Reading configuration data /etc/ssh/ssh_config
debug1: /etc/ssh/ssh_config line 19: include /etc/ssh/ssh_config.d/*.conf matched no files
debug1: /etc/ssh/ssh_config line 21: Applying options for *
debug1: Executing proxy command: exec ncat --proxy-type socks5 --proxy 192.24.122.33:29267 192.168.122.32 22
.........................................................................
debug1: Authentication succeeded (publickey).
Authenticated to 192.168.122.32 (via proxy).
debug1: channel 0: new [client-session]
debug1: Requesting no-more-sessions@openssh.com
debug1: Entering interactive session.
debug1: pledge: proc
debug1: client_input_global_request: rtype hostkeys-00@openssh.com want_reply 0
debug1: Sending environment.
debug1: Sending env LANG = en_US.UTF-8
Last login: Wed Jul 13 16:16:07 2022 from 192.168.122.32
[root@longyu ~]#
本地模拟上述过程
我在本地设备上执行如下步骤模拟上述过程:
- 使用 ssh -D -N 建立隧道并监听本地 1080 端口
[longyu@debian:08:58:52] ~ $ ssh -N -D 1080 longyu@localhost
longyu@localhost's password:
-N 参数指定 ssh 连接不执行远程命令,只用于端口转发;-D 参数配置一个本地动态应用层端口转发。当本地进程连接到 -D 参数指定的端口时,连接将会通过隧道进行转发,远端服务器会使用应用的协议来确定将流量转发到哪里。
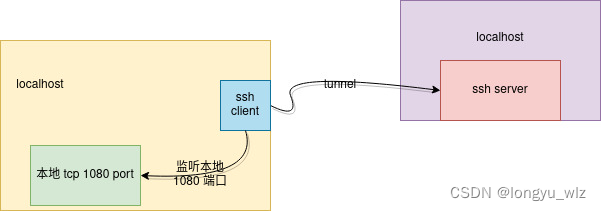
执行了上述操作后的简单拓扑如下:
- 查看监听端口
[longyu@debian:09:10:47] ~ $ netstat -anp | grep ssh
(Not all processes could be identified, non-owned process info
will not be shown, you would have to be root to see it all.)
tcp 0 0 127.0.0.1:1080 0.0.0.0:* LISTEN 6224/ssh
tcp6 0 0 ::1:1080 :::* LISTEN 6224/ssh
......................................................................................
上述输出表明 ssh 监听了本地 1080 端口,同时支持 tcp 与 tcp6。
- 使用代理连接
[longyu@debian:09:12:04] ~ $ ssh -v -o ProxyCommand='ncat --proxy-type socks5 --proxy 127.0.0.1:1080 %h %p' longyu@localhost
OpenSSH_8.4p1 Debian-5+deb11u1, OpenSSL 1.1.1n 15 Mar 2022
debug1: Reading configuration data /etc/ssh/ssh_config
debug1: /etc/ssh/ssh_config line 19: include /etc/ssh/ssh_config.d/*.conf matched no files
debug1: /etc/ssh/ssh_config line 21: Applying options for *
debug1: Executing proxy command: exec ncat --proxy-type socks5 --proxy 127.0.0.1:1080 localhost 22
.................................................................................
debug1: Next authentication method: password
longyu@localhost's password:
debug1: Authentication succeeded (password).
Authenticated to localhost (via proxy).
debug1: channel 0: new [client-session]
debug1: Requesting no-more-sessions@openssh.com
debug1: Entering interactive session.
debug1: pledge: proc
debug1: client_input_global_request: rtype hostkeys-00@openssh.com want_reply 0
debug1: Sending environment.
debug1: Sending env LANG = en_US.UTF-8
Linux debian 5.15.0-0.bpo.2-amd64 #1 SMP Debian 5.15.5-2~bpo11+1 (2022-01-02) x86_64
..............................................................................
Last login: Thu Jul 14 09:07:59 2022 from ::1
[longyu@debian:09:13:03] ~ $
- 查看端口信息:
tcp 0 0 127.0.0.1:1080 0.0.0.0:* LISTEN 6224/ssh
tcp 0 0 127.0.0.1:1080 127.0.0.1:40130 ESTABLISHED 6224/ssh
tcp 0 0 127.0.0.1:40130 127.0.0.1:1080 ESTABLISHED 6484/ncat
tcp6 0 0 ::1:1080 :::* LISTEN 6224/ssh
此时网络拓扑如下:
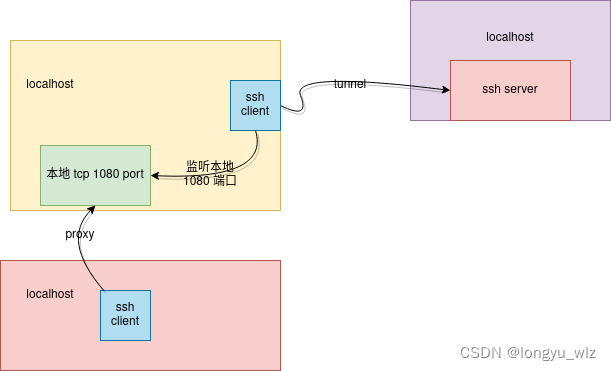
注意上面的端口信息中有两个 ESTABLISHED 的套接字,其中一个是 ncat 端发起的,另外一个是 ssh 端新建的,两个套接字的源与目的端口正好相反,这样才能正常收发数据。
一个小问题
网上搜索 ssh 使用代理的网页中很多提到使用 nc 命令,在不同的系统中 nc 命令指向的程序不太一样,使用的时候可以先查看下,然后 man 一下确定好要使用的参数。
参考链接
https://linuxize.com/post/how-to-setup-ssh-socks-tunnel-for-private-browsing/
https://superuser.com/questions/454210/how-can-i-use-ssh-with-a-socks-5-proxy






















 1977
1977











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








