
有个假flag,先字符串定位到判断处

sub_7FF6A7F412C0表面是这个

实际上我们动调一下会发现这里的函数被篡改
跑飞了?找一下反调试函数吧

插件找一下1
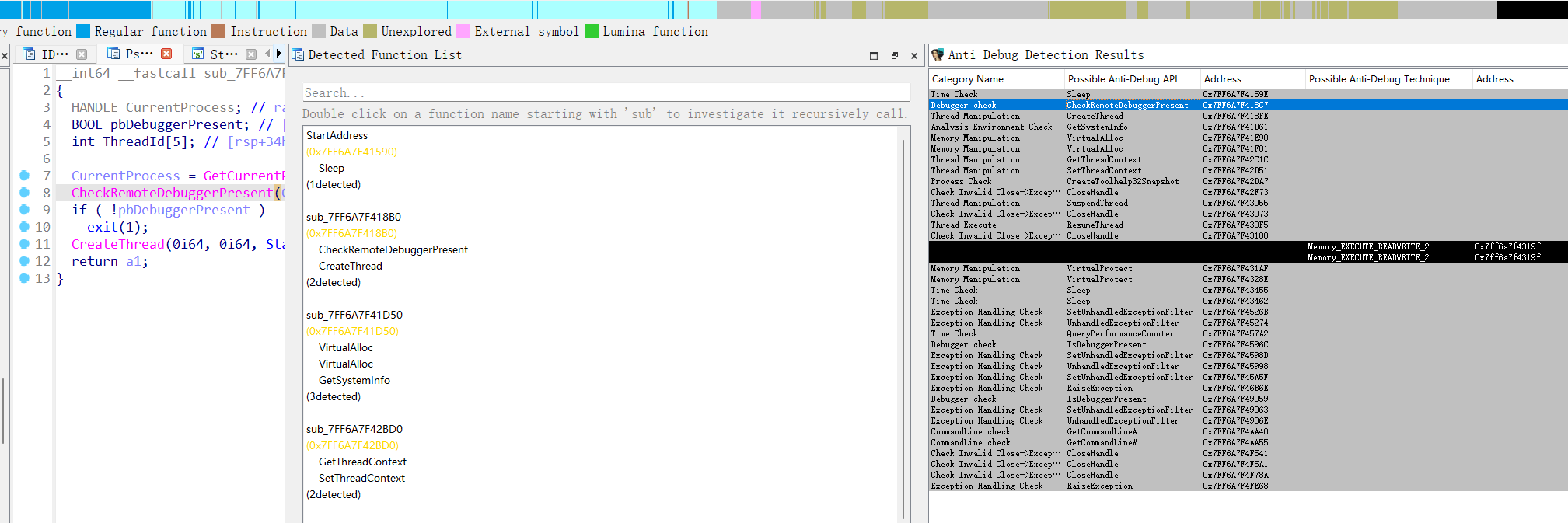
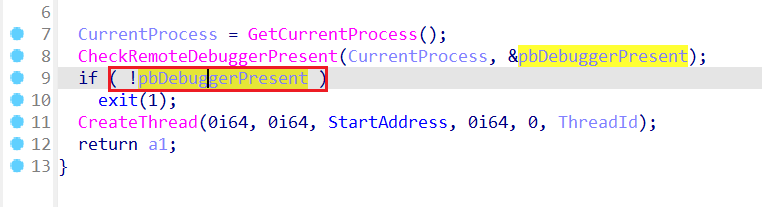
这里改一下汇编绕过,或者动调时改一下标志位都可以

这里F7进去


一个rc4,不好动调,直接套个脚本
#钩子 wp
def rc4(data, key):
S = list(range(256))
j = 0
out = []
for i in range(256):
j = (j + S[i] + key[i % len(key)]) % 256
S[i], S[j] = S[j], S[i]
i = j = 0
for char in data:
i = (i + 1) % 256
j = (j + S[i]) % 256
S[i], S[j] = S[j], S[i]
out.append(char ^ S[(S[i] + S[j]) % 256])
return bytes(out)
data = bytes([ 0x02, 0xCC, 0x47, 0xB3, 0x4D, 0x6C, 0xFD, 0x9A, 0x4C, 0x4E,
0xD4, 0x8B, 0x1E, 0x81, 0x19, 0x0A, 0x34, 0x26, 0xD0, 0xFF,
0x70, 0xB6, 0xB0, 0x92, 0x49, 0xB3, 0x00, 0x00])
key = bytes([ 0x88, 0xE3, 0xEE, 0x11, 0xC6, 0x49, 0x74, 0xA5, 0xDD, 0x98,
0x59, 0xE9, 0x48, 0xF7, 0x6E, 0xBF, 0x3A, 0xB3, 0x9B, 0xDF,
0x10, 0x42, 0xFF, 0x99, 0x6C, 0xE3, 0x3E, 0x05, 0x2C, 0x65,
0x47, 0xEF])
decrypted = rc4(data, key)
print(decrypted)
#b'flag{ho00OoOoOoked_gotcha}Zy'




















 2万+
2万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








