#re刷题第二天
0x00 python-trade
题目给了一个pyc文件,很明显是pyc逆向,这里给出一个网站,或者可以使用uncompyle进行反编译
correct = 'XlNkVmtUI1MgXWBZXCFeKY+AaXNt'
flag = ''
print 'Input flag:'
flag = raw_input()
if encode(flag) == correct:
print 'correct'
else:
print 'wrong'
import base64
def encode(message):
s = ''
for i in message:
x = ord(i) ^ 32
x = x + 16
s += chr(x)
return base64.b64encode(s)
correct = 'XlNkVmtUI1MgXWBZXCFeKY+AaXNt'
flag = ''
print 'Input flag:'
flag = raw_input()
if encode(flag) == correct:
print 'correct'
else:
print 'wrong'
直接拿到python源码,写出解密脚本即可
import base64
correct = 'XlNkVmtUI1MgXWBZXCFeKY+AaXNt'
flag = ''
de_cor = base64.b64decode(correct)
for i in range(len(de_cor)):
flag += chr((ord(de_cor[i])-16)^32)
print flag
0x01 getit
载入IDA,分析下算法

发现会将s奇数位减1,偶数位加1填充到SharifCTF{%s}中并写入文件,但是在最后文件会被删除,直接写脚本解码出来
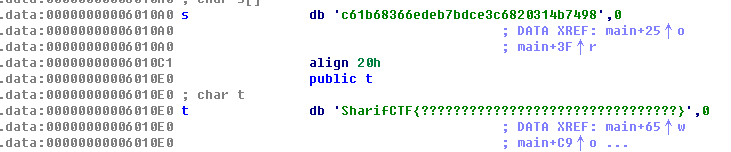
str1 = 'c61b68366edeb7bdce3c6820314b7498'
flag = ''
for i in range(len(str1)):
if i%2 == 0:
flag += chr(ord(str1[i])-1)
else:
flag += chr(ord(str1[i])+1)
print flag
0x02 csaw2013reversing2
载入IDA分析

可以看到这里直接将409b10处的字符输出

所以会导致乱码的问题

401000里边可以看到有将409b10异或的过程,409b38处所为密钥
写出脚本,得到flag
cipher = [0xbb, 0xcc, 0xa0, 0xbc, 0xdc, 0xd1, 0xbe, 0xb8, 0xcd, 0xcf, 0xbe, 0xae, 0xd2, 0xc4, 0xab, 0x82, 0xd2, 0xd9, 0x93, 0xb3, 0xd4, 0xde, 0x93, 0xa9, 0xd3, 0xcb, 0xb8, 0x82, 0xd3, 0xcb, 0xbe, 0xb9, 0x9a, 0xd7, 0xcc, 0xdd]
key = [0xbb,0xaa,0xcc,0xdd]
flag = ''
for i in range(len(cipher)):
flag += chr(cipher[i]^key[i%4])
print flag
0x03 maze
载入IDA,查看main函数分析
__int64 __fastcall main(__int64 a1, char **a2, char **a3)
{
__int64 v3; // rbx
int v4; // eax
bool v5; // bp
bool v6; // al
const char *v7; // rdi
int v9; // [rsp+0h] [rbp-28h]
int v10; // [rsp+4h] [rbp-24h]
v10 = 0;
v9 = 0;
puts("Input flag:");
scanf("%s", &s1);
if ( strlen(&s1) != 24 || strncmp(&s1, "nctf{", 5uLL) || *(&byte_6010BF + 24) != '}' )
{
LABEL_22:
puts("Wrong flag!");
exit(-1);
}
v3 = 5LL;
if ( strlen(&s1) - 1 > 5 )
{
while ( 1 )
{
v4 = *(&s1 + v3);
v5 = 0;
if ( v4 > 78 )
{
if ( (unsigned __int8)v4 == 'O' )
{
v6 = sub_400650(&v10);
goto LABEL_14;
}
if ( (unsigned __int8)v4 == 'o' )
{
v6 = sub_400660(&v10);
goto LABEL_14;
}
}
else
{
if ( (unsigned __int8)v4 == '.' )
{
v6 = sub_400670(&v9);
goto LABEL_14;
}
if ( (unsigned __int8)v4 == '0' )
{
v6 = sub_400680(&v9);
LABEL_14:
v5 = v6;
goto LABEL_15;
}
}
LABEL_15:
if ( !(unsigned __int8)sub_400690((__int64)map, v10, v9) )
goto LABEL_22;
if ( ++v3 >= strlen(&s1) - 1 )
{
if ( v5 )
break;
LABEL_20:
v7 = "Wrong flag!";
goto LABEL_21;
}
}
}
if ( map[8 * v9 + v10] != '#' )
goto LABEL_20;
v7 = "Congratulations!";
LABEL_21:
puts(v7);
return 0LL;
}
可以发现是走迷宫,迷宫是8x8的,大致是这个样子
******
* * *
*** * **
** * **
* *# *
** *** *
** *
********
是O,o,.,0四个键代表上下左右,0和.代表下和上,O和o代表左和右,最后和nctf{%s}做拼接就可以得到flag。
nctf{o0oo00O000oooo…OO}
0x04 dmd-50
载入IDA
可以看到v41这块儿是按位进行比较的,v41是v40,而v40是md5加密过后的,直接查下md5就会得到flag
0x05 Shuffle
载入IDA,发现flag

0x06 re2-cpp-is-awesome
载入IDA,可以看到这处比较

分析得出将6020c0处的数值作为字符串下标,从字符串中取值拼接就是flag,写出脚本
cipher = [36, 0, 5, 54, 101, 7, 39, 38, 45, 1, 3, 0, 13, 86, 1, 3, 101, 3, 45, 22, 2, 21, 3, 101, 0, 41, 68, 68, 1, 68, 43]
key = 'L3t_ME_T3ll_Y0u_S0m3th1ng_1mp0rtant_A_{FL4G}_W0nt_b3_3X4ctly_th4t_345y_t0_c4ptur3_H0wev3r_1T_w1ll_b3_C00l_1F_Y0u_g0t_1t'
flag = ''
print key[0]
for x in cipher:
flag += key[x]
print flag
0x07 crackme
载入PEiD,发现NsPack壳,这里我懒得脱壳,直接带壳调了

这里是计算长度,要求长度为42

取输入和402130处的key进行异或,然后与402150处进行比较,key循环使用

写脚本,得到flag
cipher = [0x12,0x04,0x08,0x14,0x24,0x5C,0x4A,0x3D,0x56,0x0A,0x10,0x67,0x00,0x41,0x00,0x01,0x46,0x5A,0x44,0x42,0x6E,0x0C,0x44,0x72,0x0C,0x0D,0x40,0x3E,0x4B,0x5F,0x02,0x01,0x4C,0x5E,0x5B,0x17,0x6E,0x0C,0x16,0x68,0x5B,0x12]
key = 'this_is_not_flag'
flag = ''
for i in range(len(cipher)):
flag += chr(cipher[i]^ord(key[i%len(key)]))
print flag
0x08 re-for-50-plz-50
载入IDA,发现是MIPS的程序,简单读一下

发现是密文和0x37进行异或,写出脚本,得到flag
cipher = 'cbtcqLUBChERV[[Nh@_X^D]X_YPV[CJ'
flag = ''
for i in range(len(cipher)):
flag += chr(ord(cipher[i])^0x37)
print flag






















 3512
3512











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








