一、dos攻击
1、常见DoS攻击
详见:http://blog.csdn.net/scythe666/article/details/52989907
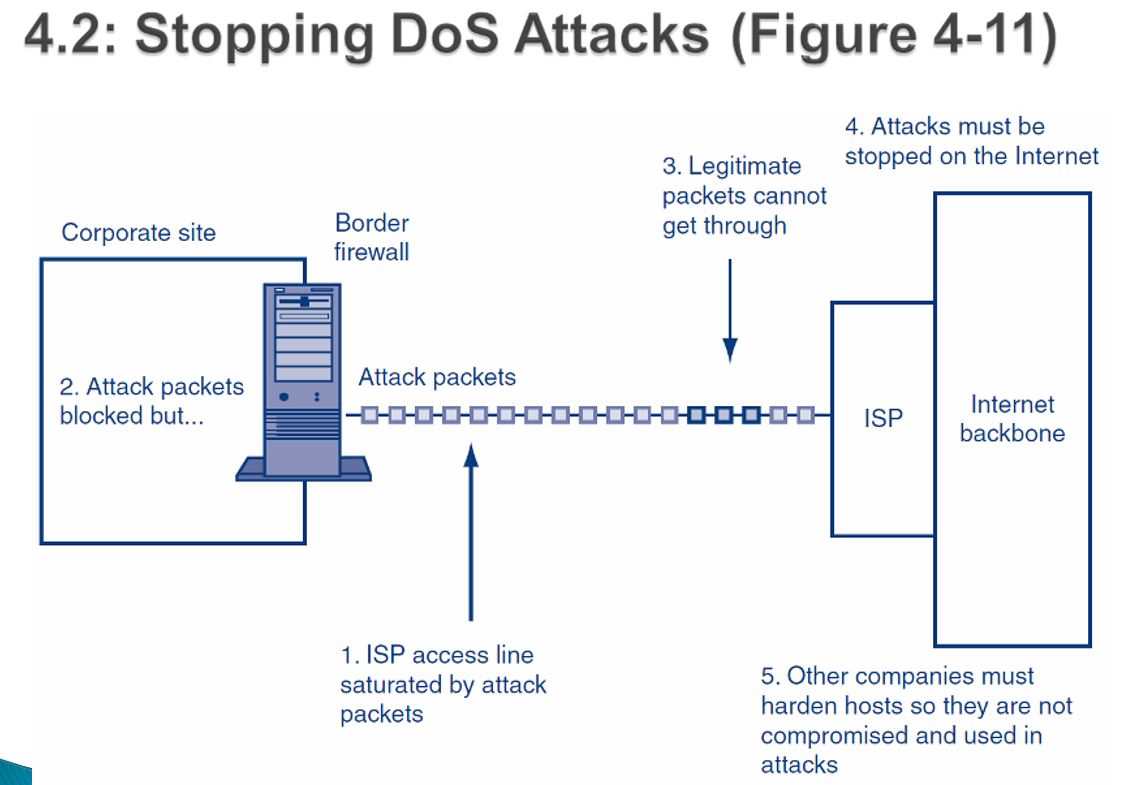
2、如何预防DoS攻击
Black holing
Drop all IP packets from an attacker
Not a good long-term strategy because attackers can quickly change source IP addresses
An attacker may knowingly try to get a trusted corporate partner black holed
丢掉所有ip包,不是长期策略,因为攻击者会修改ip包
攻击者可能会利用被信任的合作方来采取攻击
Validating the handshake
Whenever a SYN segment arrives, the firewall itself sends back a SYN/ACK segment, without passing the SYN segment on to the target server (false opening)
When the firewall gets back a legitimate ACK the firewall send the original SYN segment on to the intended server
验证三次握手,相当于通过防火墙来阻止一次syn报文
Rate limiting
Used to reduce a certain type of traffic to a reasonable amount
Can frustrate attackers, and legitimate users
减少特定网络拥塞的阈值,但是可能会阻碍正常用户
3、ARP Poisoning
The problem: ARP requests and replies do NOT require authentication or verification
All hosts trust all ARP replies
ARP spoofing uses false ARP replies to map any IP address to any MAC address
An attacker can manipulate ARP tables on all LAN hosts
The attacker must send a continuous stream of unsolicited ARP replies
ARP是不进行验证的协议,很容易被利用
二、firewalls
附录:
[1] 课本地址

























 4137
4137

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








