1.病毒介绍
该病毒通过仿冒浏览器,播放器和一些游戏等进行传播,一旦用户手机不慎被感染,该病毒将立即下载提权文件来获取root权限,频繁推送广告,监控用户短信记录,私自发送扣费短信,注入大量恶意文件到手机系统用于守护病毒,防止病毒被卸载。
病毒样本的下载来源大多是来自国外的云服务器如cloudfront.net和amazonaws.com,软件名通常为全英文如WatermelonShare、Calc Master等,推送的广告内容以及下载的软件也都是国外软件,以此推测此病毒的目标应该是国外用户;从病毒功能及代码注释信息上看,此病毒是国内制造的,因此推测此病毒是国内制造,国外流行的典型广告木马,我们根据感染量较大的一个样本中的一些线索推测木马作者可能是在福建福州,一家从事app市场的公司。
病毒感染量变化趋势:
2.样本信息
包名: com.mobo.mrclean
证书: 1D90BFFEC2A26B6CC50151757CBCEE04
Assets目录下的子包
3.恶意行为
1) 病毒运行后,立即下载提权文件来获取root权限,夺取系统的控制权;
2) 注入大量恶意文件到手机系统,阻止病毒被卸载;
3) 私自发送扣费短信,造成用户极大的财产损失;
4) 下载并静默安装恶意子包至手机rom内;
5) 频繁推送恶意广告,影响用户正常使用手机;

4.病毒执行流程
5.详细分析
1) 病毒母包行为
加载子包assets/a
调用in1方法解码assets/c,assets/s,生成mcr.apk和libdt.so
调用in2方法加载libdt.so
libdt.so中通过in3方法了mcr.apk
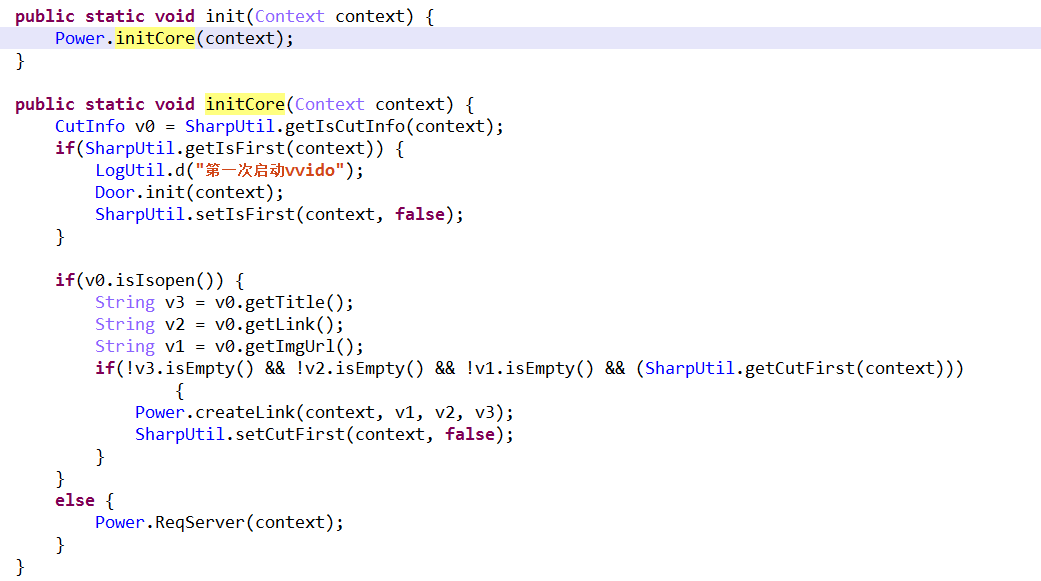
libdt.so的in4方法通过loadClass方式调用了mcr.apk的com.android.provider.power.Power类中的init方法
com.android.provider.power.Power类中的init方法
initcore方法中通过getIsFirst方法判断程序是否第一次被运行
若是首次运行则调用Door.init(context);方法初始化配置并启动服务b和服务d,激活广告功能
服务b,启动线程DetectAppTask并通过timerSet定时持续发送广播
检测包名通过之后,线程DetectAppTask发送弹窗广播Action"com.fpt.alk.clk"
广播接收器通过接收广播弹出广告
服务d启动诱导消费模块
通过startservice方式启动服务c
启动计费服务,创建线程GasLogicRun
启动线程GasLogicRun,调用handlerRet方法发送短信
handlerRet方法解析JSONObject获取相关的计费信息并发送短信进行扣费
拦截含有指定关键字的短信
扣费成功后向服务器上传信息
DataStore类用于操作存放屏蔽关键词的数据库fmoonStore.db
Cpsavd类用于监控短信变化
2) Root相关模块
Root启动模块子包com.xx.mas.demo,判断root方案文件是否存在,若存在则加载进行root,若不存在则创建生成再进行root
/data/data/包名/files/.sunny目录下的b.png解压后为r1~r4,分别是四种root方案,利用了CVE-2012-6442、WooYun-2013-21778、CVE-2013-6282等漏洞来进行root提权。
3) 其他恶意文件功能简要说明
elf文件.ukd,注入恶意文件至手机系统中
如下注入恶意文件到/system/xbin/.pr.io
Elf文件.pr.io用于守护包名为com.music.store.fore.go的恶意apk并与服务器交互信息
elf文件.pe用于保护root权限;
elf文件supolicy
用于在init.rc和install-recovery.sh中添加恶意文件开机启动
修改后的install-recovery.sh

mkdevsh文件
将恶意文件注入系统中并修改权限
.debuggerd.no注入恶意文件至系统中并设置守护线程
.ir文件用于设置守护线程
4) rom恶意apk子包分析
用户量情况
B90A7FCB2019BB59799646F77746FAEF11EECE37
启动后加载资源子包\assets\is.png,主要用于广告的统计与服务器的交互,也有私自下载静默安装的风险
29E9B1F1285D73612C751ACF3D755A99B31F3509
EF28DE725D2AF36E7BE5E063ADF6D1DF358AE95D
32486B0757215FC94684D85762C836007A6811D0
E6E87065821C5FDEC3F5C1CF6C2A1736B0AC1B8B
A715A1A36DF454C2DCC242D5884DF40150670574
启动后解密并加载资源子包\res\raw\protect.apk,用于唤醒病毒主模块进程,并私自下载安装其他软件
私自下载安装其他软件

5) 样本相关链接
推广信息图片:
http://d3********iyhtno.cloudfront.net/pic/pic1.jpg
Root模块:
http://down.c*****xa.com/b****okr/rtt_0310_577.apk
http://down.c******xa.com/testapk/is1010_1154.jar
Rom内恶意子包netalpha:
http://down.co****n.com/o****in/mains2.apk
6.查杀截图
7.清除方案
要将此病毒彻底清除需要清理系统中的恶意文件:





































































 1044
1044











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








