brainfuck
题目描述:
++++++++[>>++>++++>++++++>++++++++>++++++++++>++++++++++++>++++++++++++++>++++++++++++++++>++++++++++++++++++>++++++++++++++++++++>++++++++++++++++++++++>++++++++++++++++++++++++>++++++++++++++++++++++++++>++++++++++++++++++++++++++++>++++++++++++++++++++++++++++++<<<<<<<<<<<<<<<<-]>>>>>>>++++++.>----.<-----.>-----.>-----.<<<-.>>++..<.>.++++++.....------.<.>.<<<<<+++.>>>>+.<<<+++++++.>>>+.<<<-------.>>>-.<<<+.+++++++.--..>>>>---.-.<<<<-.+++.>>>>.<<<<-------.+.>>>>>++.
题目分析:
brainfuck直接解
flag{Oiiaioooooiai#b7c0b1866fe58e12}
Caesar’s Secert
题目描述:
kqfl{hf3x4w'x_h1umjw_n5_a4wd_3fed}
题目分析:
凯撒解密
flag{ca3s4rs_c1pher_i5_v4ry_3azy}
Fence
题目描述:
fa{ereigtepanet6680}lgrodrn_h_litx#8fc3
题目分析:
w型栅栏解密
flag{reordering_the_plaintext#686f8c03}
Vigenère
题目描述:
pqcq{qc_m1kt4_njn_5slp0b_lkyacx_gcdy1ud4_g3nv5x0}
题目分析:
维吉尼亚解密
flag 对应 pqcq,得到密钥kfc
flag{la_c1fr4_del_5ign0r_giovan_batt1st4_b3ll5s0}
用不知密钥维吉尼亚解密直接秒
babyencoding
题目描述:
part 1 of flag: ZmxhZ3tkYXp6bGluZ19lbmNvZGluZyM0ZTBhZDQ=
part 2 of flag: MYYGGYJQHBSDCZJRMQYGMMJQMMYGGN3BMZSTIMRSMZSWCNY=
part 3 of flag: =8S4U,3DR8SDY,C`S-F5F-C(S,S<R-C`Q9F8S87T`
题目分析:
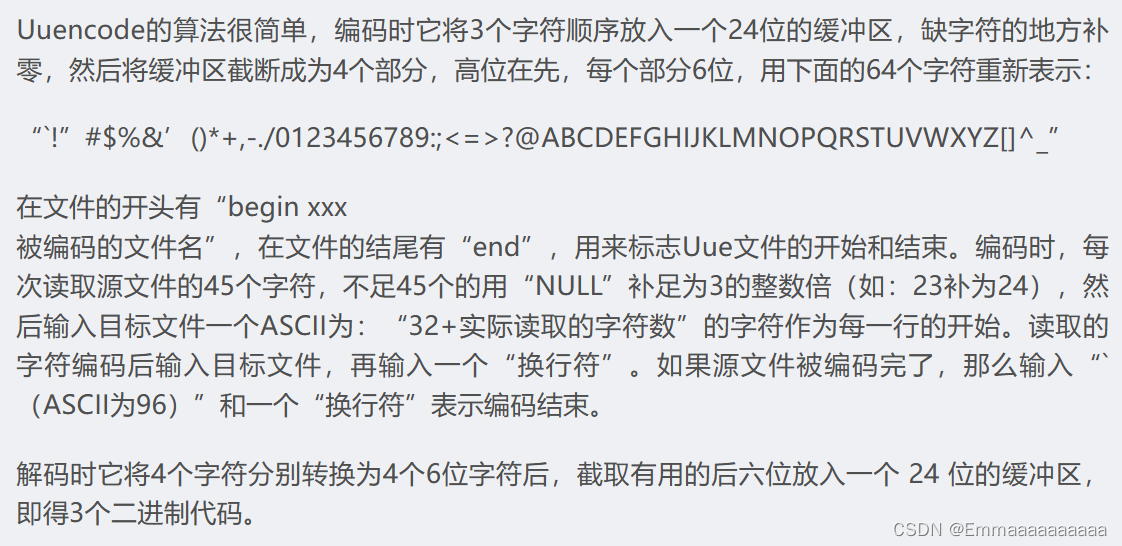
1.base64得到flag{dazzling_encoding#4e0ad4
2.base32得到f0ca08d1e1d0f10c0c7afe422fea7
3.uuencode得到c55192c992036ef623372601ff3a}
flag{dazzling_encoding#4e0ad4f0ca08d1e1d0f10c0c7afe422fea7c55192c992036ef623372601ff3a}
babyrsa
题目描述:
from Crypto.Util.number import *
from flag import flag
def gen_prime(n):
res = 1
for i in range(15):
res *= getPrime(n)
return res
if __name__ == '__main__':
n = gen_prime(32)
e = 65537
m = bytes_to_long(flag)
c = pow(m,e,n)
print(n)
print(c)
n = 17290066070594979571009663381214201320459569851358502368651245514213538229969915658064992558167323586895088933922835353804055772638980251328261
c = 14322038433761655404678393568158537849783589481463521075694802654611048898878605144663750410655734675423328256213114422929994037240752995363595
题目分析:
分解n后直接常规rsa
from Crypto.Util.number import *
n = 17290066070594979571009663381214201320459569851358502368651245514213538229969915658064992558167323586895088933922835353804055772638980251328261
c = 14322038433761655404678393568158537849783589481463521075694802654611048898878605144663750410655734675423328256213114422929994037240752995363595
phi = euler_phi(n)
d = inverse_mod(65537,phi)
m = pow(c,d,n)
long_to_bytes(int(m))
# flag{us4_s1ge_t0_cal_phI}
small d
题目描述:
from secret import flag
from Crypto.Util.number import *
p = getPrime(1024)
q = getPrime(1024)
d = getPrime(32)
e = inverse(d, (p-1)*(q-1))
n = p*q
m = bytes_to_long(flag)
c = pow(m,e,n)
print(c)
print(e)
print(n)
c = 6755916696778185952300108824880341673727005249517850628424982499865744864158808968764135637141068930913626093598728925195859592078242679206690525678584698906782028671968557701271591419982370839581872779561897896707128815668722609285484978303216863236997021197576337940204757331749701872808443246927772977500576853559531421931943600185923610329322219591977644573509755483679059951426686170296018798771243136530651597181988040668586240449099412301454312937065604961224359235038190145852108473520413909014198600434679037524165523422401364208450631557380207996597981309168360160658308982745545442756884931141501387954248
e = 8614531087131806536072176126608505396485998912193090420094510792595101158240453985055053653848556325011409922394711124558383619830290017950912353027270400567568622816245822324422993074690183971093882640779808546479195604743230137113293752897968332220989640710311998150108315298333817030634179487075421403617790823560886688860928133117536724977888683732478708628314857313700596522339509581915323452695136877802816003353853220986492007970183551041303875958750496892867954477510966708935358534322867404860267180294538231734184176727805289746004999969923736528783436876728104351783351879340959568183101515294393048651825
n = 19873634983456087520110552277450497529248494581902299327237268030756398057752510103012336452522030173329321726779935832106030157682672262548076895370443461558851584951681093787821035488952691034250115440441807557595256984719995983158595843451037546929918777883675020571945533922321514120075488490479009468943286990002735169371404973284096869826357659027627815888558391520276866122370551115223282637855894202170474955274129276356625364663165723431215981184996513023372433862053624792195361271141451880123090158644095287045862204954829998614717677163841391272754122687961264723993880239407106030370047794145123292991433
题目分析:
大e,维纳攻击
from Crypto.Util.number import *
def continuedFra(x, y):
cf = []
while y:
cf.append(x // y)
x, y = y, x % y
return cf
def gradualFra(cf):
numerator = 0 # 分子
denominator = 1 # 分母
for x in cf[::-1]:
numerator, denominator = denominator, x * denominator + numerator
return numerator, denominator
def getGradualFra(cf):
gf = []
for i in range(1, len(cf) + 1):
gf.append(gradualFra(cf[:i]))
return gf
def wienerAttack(e, n):
cf = continuedFra(e, n)
gf = getGradualFra(cf)
for d, k in gf: # 不得不说最后要倒一下呀!
if d.bit_length() == 32:
return d
c = 6755916696778185952300108824880341673727005249517850628424982499865744864158808968764135637141068930913626093598728925195859592078242679206690525678584698906782028671968557701271591419982370839581872779561897896707128815668722609285484978303216863236997021197576337940204757331749701872808443246927772977500576853559531421931943600185923610329322219591977644573509755483679059951426686170296018798771243136530651597181988040668586240449099412301454312937065604961224359235038190145852108473520413909014198600434679037524165523422401364208450631557380207996597981309168360160658308982745545442756884931141501387954248
e = 8614531087131806536072176126608505396485998912193090420094510792595101158240453985055053653848556325011409922394711124558383619830290017950912353027270400567568622816245822324422993074690183971093882640779808546479195604743230137113293752897968332220989640710311998150108315298333817030634179487075421403617790823560886688860928133117536724977888683732478708628314857313700596522339509581915323452695136877802816003353853220986492007970183551041303875958750496892867954477510966708935358534322867404860267180294538231734184176727805289746004999969923736528783436876728104351783351879340959568183101515294393048651825
n = 19873634983456087520110552277450497529248494581902299327237268030756398057752510103012336452522030173329321726779935832106030157682672262548076895370443461558851584951681093787821035488952691034250115440441807557595256984719995983158595843451037546929918777883675020571945533922321514120075488490479009468943286990002735169371404973284096869826357659027627815888558391520276866122370551115223282637855894202170474955274129276356625364663165723431215981184996513023372433862053624792195361271141451880123090158644095287045862204954829998614717677163841391272754122687961264723993880239407106030370047794145123292991433
d=wienerAttack(e, n)
m=pow(c, d, n)
print(long_to_bytes(m))
# flag{learn_some_continued_fraction_technique#dc16885c}
babyxor
爆破key
a = 'e9e3eee8f4f7bffdd0bebad0fcf6e2e2bcfbfdf6d0eee1ebd0eabbf5f6aeaeaeaeaeaef2'
c = bytes.fromhex(a)
for i in range(256):
flag = []
for j in c:
flag.append(j ^ i)
if b'flag' in bytes(flag):
print(bytes(flag))
# flag{x0r_15_symm3try_and_e4zy!!!!!!}
或直接求key,key = ord(‘f’) ^ (密文第一个字节)
a = 'e9e3eee8f4f7bffdd0bebad0fcf6e2e2bcfbfdf6d0eee1ebd0eabbf5f6aeaeaeaeaeaef2'
c = bytes.fromhex(a)
key = ord('f') ^ c[0]
flag = []
for j in c:
flag.append(j ^ key)
print(bytes(flag))
# flag{x0r_15_symm3try_and_e4zy!!!!!!}
Affine
题目描述:
from flag import flag, key
modulus = 256
ciphertext = []
for f in flag:
ciphertext.append((key[0]*f + key[1]) % modulus)
print(bytes(ciphertext).hex())
# dd4388ee428bdddd5865cc66aa5887ffcca966109c66edcca920667a88312064
题目分析:
解方程求key0,key1,求出key0,key1后逆一下加密函数结果也就出来了
flag这几个字母有的有解,有的没解,自行尝试即可
from gmpy2 import *
a = 'dd4388ee428bdddd5865cc66aa5887ffcca966109c66edcca920667a88312064'
cipher = bytes.fromhex(a)
from z3 import *
s = Solver()
k0,k1 = Int('k0'),Int('k1')
s.add(k0 * ord('g') + k1 == cipher[3])
s.add(k0 * ord('f') + k1 == cipher[0])
if s.check() == sat:
print(s.model())
k0 = 17
# k1 = -1513 % 256
k1 = 23
flag = []
for c in cipher:
flag.append((c - k1) * invert(k0,256) % 256)
print(bytes(flag))
# flag{4ff1ne_c1pher_i5_very_3azy}
babyaes
题目描述:
from Crypto.Cipher import AES
import os
from flag import flag
from Crypto.Util.number import *
def pad(data):
return data + b"".join([b'\x00' for _ in range(0, 16 - len(data))])
def main():
flag_ = pad(flag)
key = os.urandom(16) * 2
iv = os.urandom(16)
print(bytes_to_long(key) ^ bytes_to_long(iv) ^ 1)
aes = AES.new(key, AES.MODE_CBC, iv)
enc_flag = aes.encrypt(flag_)
print(enc_flag)
if __name__ == "__main__":
main()
'''
a = 3657491768215750635844958060963805125333761387746954618540958489914964573229
c = b'>]\xc1\xe5\x82/\x02\x7ft\xf1B\x8d\n\xc1\x95i'
'''
题目分析:
我记得buu上有一道与这题超类似的题
key等于字节a的前16位 * 2
iv = 字节a后16位 ^ key的前一半 ^ 1
key,iv都出来了,那么flag也就出来了
from Crypto.Util.number import *
from Crypto.Cipher import AES
a = 3657491768215750635844958060963805125333761387746954618540958489914964573229
c = b'>]\xc1\xe5\x82/\x02\x7ft\xf1B\x8d\n\xc1\x95i'
key = long_to_bytes(a)[:16]
iv = bytes_to_long(key) ^ bytes_to_long(long_to_bytes(a)[16:]) ^ 1
aes = AES.new(key * 2,AES.MODE_CBC,long_to_bytes(iv))
flag = aes.decrypt(c)
print(flag)
# flag{firsT_cry_Aes}
























 697
697

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








