1.漏洞描述
由于Jackson黑名单过滤不完整而导致,当开发人员在应用程序中通过ObjectMapper对象调用enableDefaultTyping方法时,程序就会受到此漏洞的影响,攻击者就可利用构造的包含有恶意代码的json数据包对应用进行攻击,直接获取服务器控制权限。
影响版本:Jackson-databind 2.X < 2.9.9.1
2.漏洞搭建
1、创建在桌面一个docker-compose 配置文件,命名为:CVE-2019-12384,里面添加配置文件:
version: '2'
services:
web:
image: tech1iu/servlet-with-jackson:2.9.8
container_name: jackson-fuckme
ports:
- "8080:8080"

2、拉取和启动
docker-compose -f CVE-2019-12384 up -d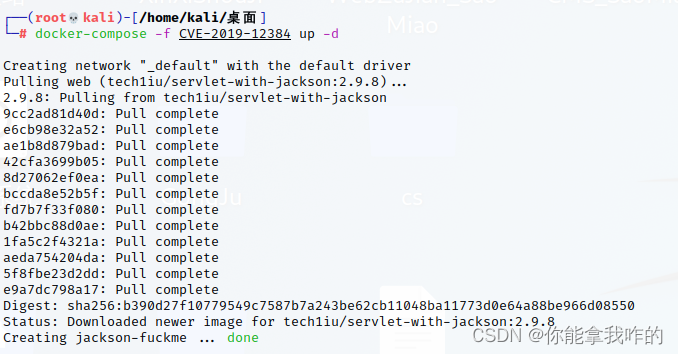
通过ps查看端口号








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章


















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








