W's Cipher
| Time Limit: 1000MS |
| Memory Limit: 10000K |
| Total Submissions: 5021 |
| Accepted: 2519 |
Description
WeirdWally's Wireless Widgets, Inc. manufactures an eclectic assortment of small,wireless, network capable devices, ranging from dog collars, to pencils, tofishing bobbers. All these devices have very small memories. Encryptionalgorithms like Rijndael, the candidate for the Advanced Encryption Standard(AES) are demonstrably secure but they don't fit in such a tiny memory. Inorder to provide some security for transmissions to and from the devices, WWWWuses the following algorithm, which you are to implement.
Encrypting a message requires three integer keys, k1, k2, and k3. The letters[a-i] form one group, [j-r] a second group, and everything else ([s-z] andunderscore) the third group. Within each group the letters are rotated left byki positions in the message. Each group is rotated independently of the othertwo. Decrypting the message means doing a right rotation by ki positions withineach group.
Consider the message the_quick_brown_fox encrypted with ki values of 2, 3 and1. The encrypted string is _icuo_bfnwhoq_kxert. The figure below shows thedecrypting right rotations for one character in each of the three charactergroups.
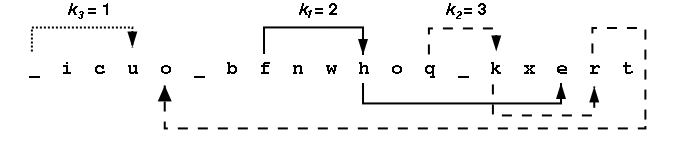
Looking at all the letters in the group [a-i] we see {i,c,b,f,h,e} appear atpositions {2,3,7,8,11,17} within the encrypted message. After a right rotationof k1=2, these positions contain the letters {h,e,i,c,b,f}. The table belowshows the intermediate strings that come from doing all the rotations in thefirst group, then all rotations in the second group, then all the rotations inthe third group. Rotating letters in one group will not change any letters inany of the other groups.
All input strings contain only lowercase letters and underscores(_). Eachstring will be at most 80 characters long. The ki are all positive integers inthe range 1-100.
Input
Inputconsists of information for one or more encrypted messages. Each problem beginswith one line containing k1, k2, and k3 followed by a line containing theencrypted message. The end of the input is signalled by a line with all keyvalues of 0.
Output
For eachencrypted message, the output is a single line containing the decrypted string.
SampleInput
2 3 1
_icuo_bfnwhoq_kxert
1 1 1
bcalmkyzx
3 7 4
wcb_mxfep_dorul_eov_qtkrhe_ozany_dgtoh_u_eji
2 4 3
cjvdksaltbmu
0 0 0
SampleOutput
the_quick_brown_fox
abcklmxyz
the_quick_brown_fox_jumped_over_the_lazy_dog
ajsbktcludmv
#include<stdio.h>
#include<string.h>
char s[107],t[3][107],p[3][107];
int order[107];//记录顺序
void f(char t[107],int l,int k,char p[107])
{
if(l) k%=l;//循环防移出
for(int i=0;i<l;i++)
p[(i+k)%l]=t[i];
}
int main()
{
int k1,k2,k3,l1,l2,l3,i;
while(scanf("%d%d%d",&k1,&k2,&k3),k1|k2|k3)
{
scanf("%s",s);
l1=l2=l3=0;
for(i=0; i<strlen(s); i++)
{
if(s[i]>='a'&&s[i]<='i')
{
t[1][l1++]=s[i];
order[i]=1;
}
else if(s[i]>='j'&&s[i]<='r')
{
t[2][l2++]=s[i];
order[i]=2;
}
else
{
t[3][l3++]=s[i];
order[i]=3;
}
}
f(t[1],l1,k1,p[1]);
f(t[2],l2,k2,p[2]);
f(t[3],l3,k3,p[3]);
l1=l2=l3=0;
for(i=0;i<strlen(s);i++)
if(order[i]==1)
printf("%c",p[1][l1++]);
else if(order[i]==2)
printf("%c",p[2][l2++]);
else
printf("%c",p[3][l3++]);
printf("\n");
}
return 0;
}





















 123
123











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








