在master节点通过kubectl建立calico policy controller
calico-controller.yml
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: calico-kube-controllers
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: calico-kube-controllers
subjects:
- kind: ServiceAccount
name: calico-kube-controllers
namespace: kube-system
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: calico-kube-controllers
namespace: kube-system
rules:
- apiGroups:
- ""
- extensions
resources:
- pods
- namespaces
- networkpolicies
verbs:
- watch
- list
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: calico-kube-controllers
namespace: kube-system
---
apiVersion: extensions/v1beta1
kind: Deployment
metadata:
name: calico-policy-controller
namespace: kube-system
labels:
k8s-app: calico-policy
spec:
strategy:
type: Recreate
template:
metadata:
name: calico-policy-controller
namespace: kube-system
labels:
k8s-app: calico-policy
spec:
hostNetwork: true
serviceAccountName: calico-kube-controllers
containers:
- name: calico-policy-controller
image: quay.io/calico/kube-controllers:v1.0.0
env:
- name: ETCD_ENDPOINTS
value: "http://10.0.0.210:2379"
volumeMounts:
- mountPath: /etc/etcd/ssl
name: etcd-ca-certs
readOnly: true
volumes:
- hostPath:
path: /etc/etcd/ssl
type: DirectoryOrCreate
name: etcd-ca-certs
下载calicoctl
wget https://github.com/projectcalico/calicoctl/releases/download/v1.6.2/calicoctl -o /usr/local/bin/calicoctl
chmod +x /usr/local/bin/calicoctl
接下来的操作需要在所有节点进行。
wget https://github.com/projectcalico/cni-plugin/releases/download/v1.11.1/calico -o /opt/cni/bin
wget https://github.com/projectcalico/cni-plugin/releases/download/v1.11.1/calico-ipam -o /opt/cni/bin
chmod +x /opt/cni/bin/calico /opt/cni/bin/calico-ipam
mkdir -p /etc/cni/net.d
在/lib/systemd/system/下面建立文件calico-node.service
[Unit]
Description=calico node
After=docker.service
Requires=docker.service
[Service]
User=root
PermissionsStartOnly=true
ExecStart=/usr/bin/docker run --net=host --privileged --name=calico-node \
-e ETCD_ENDPOINTS=http://10.0.0.210:2379 \
-e NODENAME=${HOSTNAME} \
-e IP= \
-e NO_DEFAULT_POOLS= \
-e AS= \
-e CALICO_LIBNETWORK_ENABLED=true \
-e IP6= \
-e CALICO_NETWORKING_BACKEND=bird \
-e FELIX_DEFAULTENDPOINTTOHOSTACTION=ACCEPT \
-e FELIX_HEALTHENABLED=true \
-e CALICO_IPV4POOL_CIDR=10.244.0.0/16 \
-e CALICO_IPV4POOL_IPIP=always \
-e IP_AUTODETECTION_METHOD=interface=eth0 \
-e IP6_AUTODETECTION_METHOD=interface=eth0 \
-v /etc/etcd/ssl:/etc/etcd/ssl \
-v /var/run/calico:/var/run/calico \
-v /lib/modules:/lib/modules \
-v /run/docker/plugins:/run/docker/plugins \
-v /var/run/docker.sock:/var/run/docker.sock \
-v /var/log/calico:/var/log/calico \
quay.io/calico/node:v2.6.3
ExecStop=/usr/bin/docker rm -f calico-node
Restart=on-failure
RestartSec=10
[Install]
WantedBy=multi-user.target
在/etc/cni/net.d下面建立文件10-calico.conf
{
"name": "calico-k8s-network",
"cniVersion": "0.1.0",
"type": "calico",
"etcd_endpoints": "http://10.0.0.210:2379",
"log_level": "info",
"ipam": {
"type": "calico-ipam"
},
"policy": {
"type": "k8s"
},
"kubernetes": {
"kubeconfig": "/etc/kubernetes/kubelet.conf"
}
}
在所有节点启动calico
systemctl enable calico-node
systemctl start calico-node
在master节点查看calico nodes
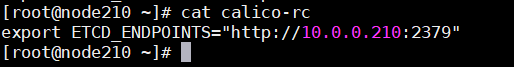
在用户主目录创建文件calico-rc
source ~/calico-rc























 2044
2044

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








