安装
官方文档(centos):Install Docker Engine on CentOS | Docker Documentation
删除旧版本
yum remove docker \
docker-client \
docker-client-latest \
docker-common \
docker-latest \
docker-latest-logrotate \
docker-logrotate \
docker-engine设置源仓库
这里设置阿里云
yum install -y yum-utils device-mapper-persistent-data lvm2
yum-config-manager --add-repo https://mirrors.aliyun.com/docker-ce/linux/centos/dockerce.repo安装
sudo yum install docker-ce docker-ce-cli containerd.io docker-buildx-plugin docker-compose-plugin配置国内镜像加速
vim /etc/docker/daemon.json
{
"registry-mirrors": [
"https://sopn42m9.mirror.aliyuncs.com",
"https://hub-mirror.c.163.com",
"https://mirror.baidubce.com"
]
}启动,测试
systemctl start docker
docker run hello-world
docker ps -a
docker rm -f $(docker ps -a|awk '/hello-world/{print $1}')kubernetes集群搭建
环境(关闭防火墙selinux,时间同步):
| 主机名 | IP |
|---|---|
| k8s-master | 192.168.126.29 |
| k8s-node1 | 192.168.126.30 |
| k8s-node2 | 192.168.126.31 |
关闭swap:
swapoff -a # 临时
sed -i 's/.swap./#&/' /etc/fstab # 永久
将桥接的IPv4流量传递到iptables的链(三台主机统一操作)
cat > /etc/sysctl.d/k8s.conf << EOF
net.bridge.bridge-nf-call-ip6tables = 1
net.bridge.bridge-nf-call-iptables = 1
EOF
sysctl --system # 生效
master免密登录其它节点(master操作)
# 创建密钥
ssh-keygen -t rsa # 一直回车
# 分发密钥
ssh-copy-id -i .ssh/id_rsa.pub root@k8s-node1
ssh-copy-id -i .ssh/id_rsa.pub root@k8s-node2安装Docker/kubeadm/kubelet(三台统一)
安装docker
vim /etc/docker/daemon.json
{
"registry-mirrors": ["http://f1361db2.m.daocloud.io"],
"exec-opts":["native.cgroupdriver=systemd"]
}wget https://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo -O
/etc/yum.repos.d/docker-ce.repo
yum -y install docker-ce-19*
systemctl enable docker && systemctl start docker
docker --version添加阿里云源
wget -O /etc/yum.repos.d/CentOS-Base.repo http://mirrors.aliyun.com/repo/Centos-7.repo配置安装k8s需要的yum源
vim /etc/yum.repos.d/kubernetes.repo
[kubernetes]
name=Kubernetes Repo
baseurl=https://mirrors.aliyun.com/kubernetes/yum/repos/kubernetes-el7-x86_64/
gpgcheck=0
enabled=1
yum clean all
yum makecache fast安装kubeadm,kubelet和kubectl
yum install -y kubelet-1.17.0 kubeadm-1.17.0 kubectl-1.17.0
systemctl enable kubelet
配置Kubernetes master结点(主结点操作)
初始化配置(复制输出最内容后一行)
kubeadm init --apiserver-advertise-address=192.168.126.29 --image-repository registry.aliyuncs.com/google_containers --kubernetes-version v1.17.0 --service-cidr=10.96.0.0/12 --pod-network-cidr=10.244.0.0/16
mkdir -p $HOME/.kube
cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
chown $(id -u):$(id -g) $HOME/.kube/config将主节点中的/etc/kubernetes/admin.conf文件拷贝到从节点相同目录下
scp /etc/kubernetes/admin.conf 192.168.126.30:/etc/kubernetes/admin.conf
scp /etc/kubernetes/admin.conf 192.168.126.31:/etc/kubernetes/admin.conf配置环境变量
echo "export KUBECONFIG=/etc/kubernetes/admin.conf" >> ~/.bash_profile
source ~/.bash_profile安装Pod网络插件
wget https://raw.githubusercontent.com/flannel-io/flannel/master/Documentation/kube-flannel.yml
kubectl apply -f kube-flannel.yml从节点加入集群
kubeadm join 192.168.126.29:6443 --token onrz40.vmhu3bbhtjtq8bzr --discovery-token-ca-cert-hash sha256:cf0a20d2fe6ff4c652253b0d8ceaa2ba16f8588ce51e9a551c993f9d9d4a16d7验证
三台主机查看

k8s架构
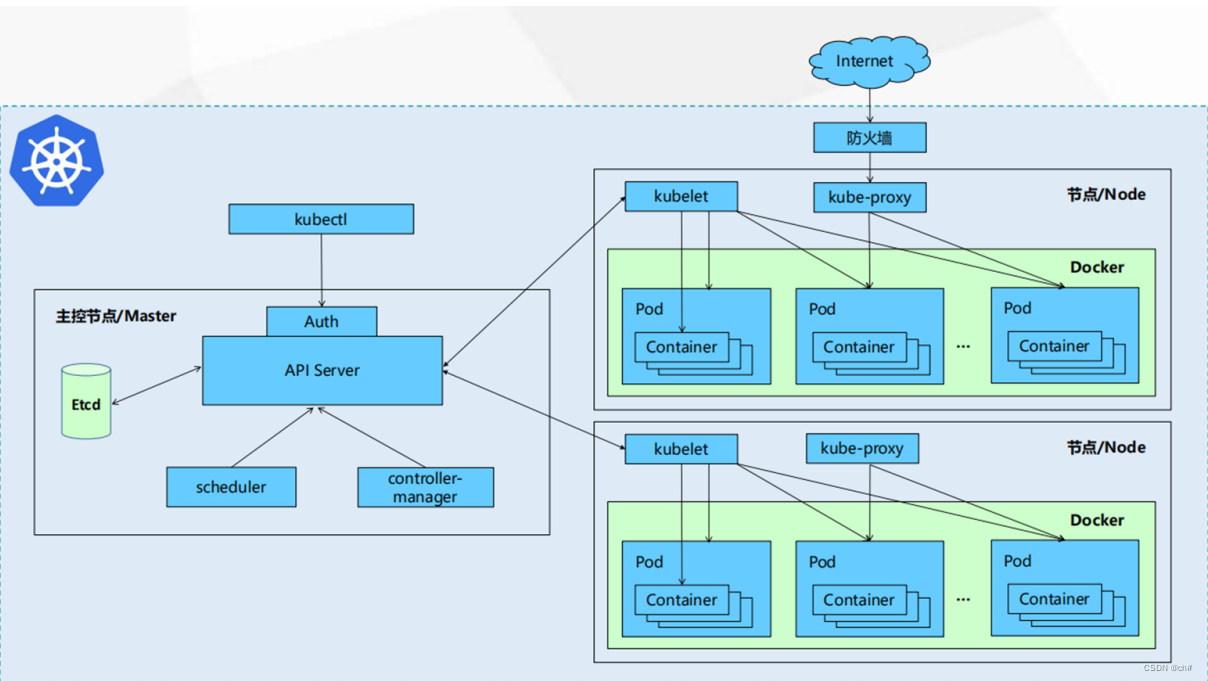
| 组件名称 | 组件作用 |
|---|---|
| ApiServer | 资源操作的唯一入口,接收用户输入的命令,提供认证、授权、API注册和发现等机制 |
| Etcd | 一致且高可用的键值存储,用作 Kubernetes 所有集群数据的后台数据库,可备份 |
| Scheduler | 负责集群资源调度,按照预定的调度策略将Pod调度到 相应的node节点上,会收集每个Worker资源的详细信息及运行情况,包括CPU、内存等 |
| ControllerManager | 负责维护集群的状态,比如程序部署安排、故障检测、 自动扩展、滚动更新等 |
| Kubelet | 负责维护容器的生命周期,即通过控制docker,来创 建、更新、销毁容器,同时也负责Volume(CVI)和网 络(CNI)的管理 |
| KubeProxy | 负责提供集群内部的服务发现和负载均衡,它可以代理转发Service的请求到Pod |
Ingress
官网图


工作原理(Ingress(Nginx)):
- 用户编写Ingress规则,说明那个域名对应kubernetes集群中的那个 Service。
- Ingress控制器动态感知Ingress服务规则的变化,然后生成一段对应的 Nginx的反向代理配置。
- Ingress控制器会将生成的Nginx配置写入到一个运行着的Nginx服务中,并动态更新。
- 到此为止,其实真正在工作的就是一个Nginx了,内部配置了用户定义的请求规则。
Ingress搭建
创建文件夹
mkdir ingress-controller
cd ingress-controller创建Ingress-nginx文件
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/nginx-0.30.0/deploy/static/mandatory.yaml
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/nginx-0.30.0/deploy/static/provider/baremetal/servicenodeport.yaml
kubectl apply -f ./创建Ingress-nginx

查看ingress-nginx生成的pod,Service(等几秒钟启动)

创建tomcat-nginx.yaml文件
apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx-deployment
spec:
replicas: 3
selector:
matchLabels:
app: nginx-pod
template:
metadata:
labels:
app: nginx-pod
spec:
containers:
- name: nginx
image: nginx:1.17.1
ports:
- containerPort: 80
---
apiVersion: apps/v1
kind: Deployment
metadata:
name: tomcat-deployment
spec:
replicas: 3
selector:
matchLabels:
app: tomcat-pod
template:
metadata:
labels:
app: tomcat-pod
spec:
containers:
- name: tomcat
image: tomcat:8.5-jre10-slim
ports:
- containerPort: 8080
---
apiVersion: v1
kind: Service
metadata:
name: nginx-service
spec:
selector:
app: nginx-pod
clusterIP: None
type: ClusterIP
ports:
- port: 80
targetPort: 80
---
apiVersion: v1
kind: Service
metadata:
name: tomcat-service
spec:
selector:
app: tomcat-pod
clusterIP: None
type: ClusterIP
ports:
- port: 8080
targetPort: 8080创建nginx tomcat对应的Service和Pod
kubectl create -f tomcat-nginx.yaml
查看Service和Pod

Http代理
创建ingress-http.yaml文件
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: ingress-http
spec:
rules:
- host: nginx.nebula.com
http:
paths:
- path: /
backend:
serviceName: nginx-service
servicePort: 80
- host: tomcat.nebula.com
http:
paths:
- path: /
backend:
serviceName: tomcat-service
servicePort: 8080创建ingress
kubectl create -f ingress-http.yaml
在master的hosts文件中添加如下的规则
192.168.126.29 nginx.nebula.com
192.168.126.29 tomcat.nebula.com
查看ingress-nginx的端口

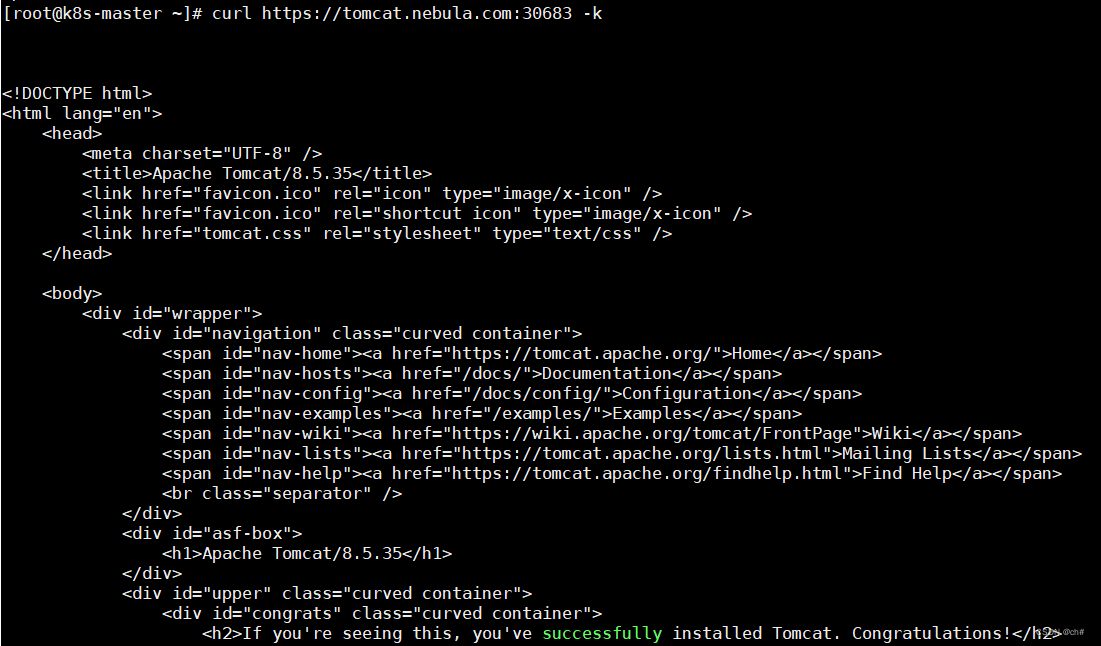
Https代理
生成证书
openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/C=CN/ST=BJ/L=BJ/O=nginx/CN=nebula.com"创建密钥
kubectl create secret tls tls-secret --key tls.key --cert tls.crt
创建ingress-https.yaml文件
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: ingress-https
spec:
tls:
- hosts:
- nginx.nebula.com
- tomcat.nebula.com
secretName: tls-secret
rules:
- host: nginx.nebula.com
http:
paths:
- path: /
backend:
serviceName: nginx-service
servicePort: 80
- host: tomcat.nebula.com
http:
paths:
- path: /
backend:
serviceName: tomcat-service
servicePort: 8080
创建https ingress
kubectl create -f ingress-https.yaml
查看
kubectl get ingress ingress-https
结果





















 381
381











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








