sql登录名和用户名
This article speaks to, how to copy SQL Logins on the new server with Server Level roles and database-level permissions as existing Source to Destination SQL Server instance using a script.
本文讨论了如何使用脚本将具有服务器级别角色和数据库级别权限的新服务器上SQL登录名复制为目标SQL Server实例的现有源。
Every rendition of SQL Server has distinctive security highlights, as does every form of Windows, with later forms having improved usefulness over before ones. Understand that security includes alone can’t ensure a protected database application. Database Administrator plays out the errand to Move or Copy SQL Logins when a new server is going to an arrangement on any environment (Development\ Testing \Staging or Production) or presenting the new database on any of the environment.
与Windows的每种形式一样,SQL Server的每种形式都具有独特的安全性亮点,而较新的形式具有更高的实用性。 理解仅包含安全性并不能确保受保护的数据库应用程序。 当新服务器要在任何环境(开发\测试\登台或生产)上进行布置或在任何环境中展示新数据库时,数据库管理员都会执行“移动或复制SQL登录名”的任务。
Microsoft SQL Server gives the user and role-based security. Server predefined role with a group of permissions will be appointed to the user rather than individual permission and this arrangement of permissions of SQL Server roles can’t be changed. Every role will have recognized authorizations (permissions) and extent of access to the SQL Server and its databases.
Microsoft SQL Server提供了基于用户和角色的安全性。 具有一组权限的服务器预定义角色将被指派给用户,而不是单个权限,并且SQL Server角色的这种权限安排无法更改。 每个角色都有公认的授权(权限)和对SQL Server及其数据库的访问范围。
Each SQL login of SQL Server can be doled out to SQL Server roles in database security. indeed, even we can utilize user characterized roles also with the number of principle consents as required. fundamentally, we have three sorts of login in SQL Server, for example, Windows Login, SQL Logins and Windows Group Login (Active Directory).
SQL Server的每个SQL登录名都可以分发给数据库安全性中SQL Server角色。 的确,即使我们也可以利用具有用户特征的角色以及所需的原则同意数。 从根本上讲,我们在SQL Server中具有三种登录名,例如Windows登录名,SQL登录名和Windows组登录名(Active Directory)。
A user could have Grant or Deny for various object types, thusly we can create a script to give permissions to access objects to the users on another server. As a feature of database security, we ought not to give full access to everybody. along these lines, we bifurcate the user’s permissions with the SQL Logins to the assigned individual. For every database, we ought to have several SQL logins with various object-level authorizations.
用户可以为各种对象类型设置“授予”或“拒绝”,因此我们可以创建一个脚本,向其他服务器上的用户授予访问对象的权限。 作为数据库安全性的一项功能,我们不应该向所有人授予完全访问权限。 按照这些思路,我们将用户SQL登录名的权限分为指定的个人。 对于每个数据库,我们应该有几个具有各种对象级授权SQL登录名。
In a schedule, we can enable the current users to have permissions to access on recently made database or we can adjust the authorizations or permission on the existing arrangement with the utilization of GRANT and DENNY articulations. In any case, if there should be an occurrence of server relocation or Hardware refreshment action, the permissions set ought to be foreordained with the number of permissions as best rehearses.
在时间表中,我们可以使当前用户具有访问最近制作的数据库的权限,或者可以利用GRANT和DENNY链接来调整对现有安排的授权或许可。 在任何情况下,如果应该发生服务器重定位或硬件更新操作,则应预先设置权限集,并以最佳演练的权限数来代替。
如何复制或移动登录名? (How to Copy or Move Logins? )
Generate script at Source Server and execute at Destination with 3 errands.
在源服务器上生成脚本,并在目标上执行3条任务。
- Create SQL Logins 创建SQL登录名
- Assign Server role to the SQL login 将服务器角色分配给SQL登录名
- Create User at Database Level with object permissions 在数据库级别创建具有对象权限的用户
创建SQL登录 (CREATE SQL Logins)
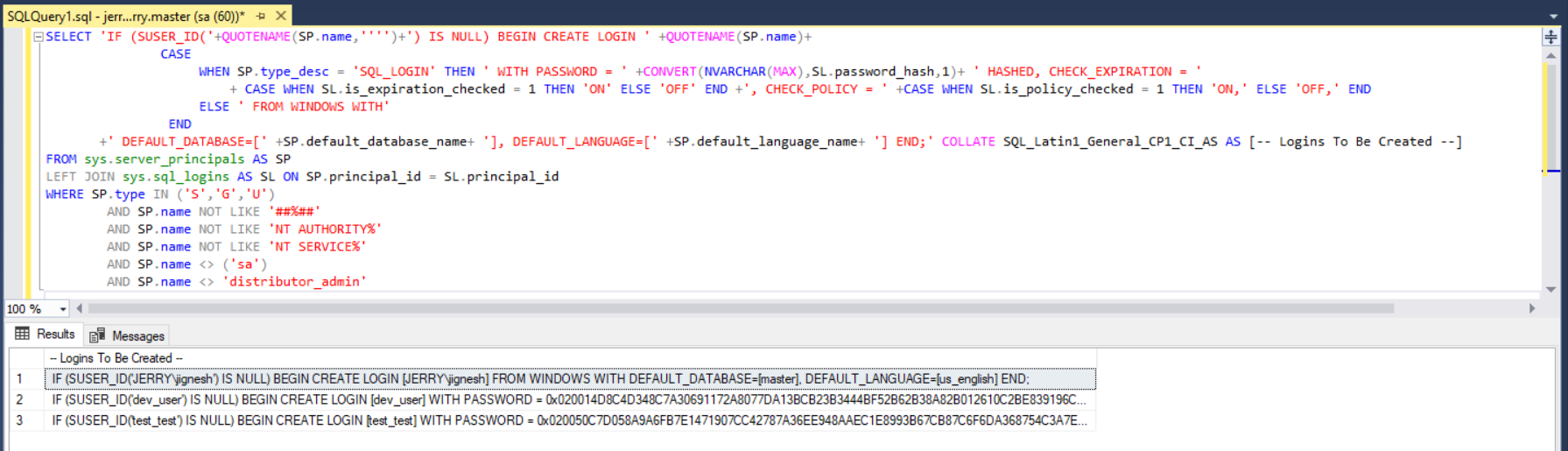
Below query will create all logins with a password that exist on SQL Server Instance. It ought to be executed on the source server.
下面的查询将使用SQL Server实例上存在的密码创建所有登录名。 它应该在源服务器上执行。
sys.sql_logins incorporates SQL Server inside service level users and System Administrator. So we can bar those users in the script while setting it up for SQL Server migrate logins.
sys.sql_logins在服务级别用户和系统管理员中合并了SQL Server。 因此,我们可以在为SQL Server迁移登录设置脚本时在脚本中禁止这些用户。
SELECT 'IF (SUSER_ID('+QUOTENAME(SP.name,'''')+') IS NULL) BEGIN CREATE LOGIN ' +QUOTENAME(SP.name)+
CASE
WHEN SP.type_desc = 'SQL_LOGIN' THEN ' WITH PASSWORD = ' +CONVERT(NVARCHAR(MAX),SL.password_hash,1)+ ' HASHED, CHECK_EXPIRATION = '
+ CASE WHEN SL.is_expiration_checked = 1 THEN 'ON' ELSE 'OFF' END +', CHECK_POLICY = ' +CASE WHEN SL.is_policy_checked = 1 THEN 'ON,' ELSE 'OFF,' END
ELSE ' FROM WINDOWS WITH'
END
+' DEFAULT_DATABASE=[' +SP.default_database_name+ '], DEFAULT_LANGUAGE=[' +SP.default_language_name+ '] END;' COLLATE SQL_Latin1_General_CP1_CI_AS AS [-- Logins To Be Created --]
FROM sys.server_principals AS SP
LEFT JOIN sys.sql_logins AS SL ON SP.principal_id = SL.principal_id
WHERE SP.type IN ('S','G','U')
AND SP.name NOT LIKE '##%##'
AND SP.name NOT LIKE 'NT AUTHORITY%'
AND SP.name NOT LIKE 'NT SERVICE%'
AND SP.name <> ('sa')
AND SP.name <> 'distributor_admin'
See here, you can see the number of logins with hash organized password. T-SQL query will create the script for Windows logins and SQL Logins for SQL Server migrate logins. To reject the Windows Login, we can apply the filter on sp.type section by including SP.type <> ‘U’ in the above SQL explanation.
在这里看到,您可以看到使用哈希组织密码登录的次数。 T-SQL查询将为Windows登录创建脚本,为SQL Server迁移登录创建SQL登录。 要拒绝Windows登录,可以通过在上述SQL解释中包含SP.type <>'U'来对sp.type部分应用筛选器。
Execute the outcome set of above articulation at goal server and check those new logins are readied or not utilizing sys.sql_logins DMV. Now, logins are copied however roles that are mapped in the source server that won’t be integrated with SQL logins at the Destination Server.
在目标服务器上执行上述操作的结果集,并使用sys.sql_logins DMV检查是否已准备好新的登录名。 现在,复制了登录名,但是源服务器中映射的角色将不会与目标服务器上SQL登录名集成在一起。
将服务器角色分配给登录名 (Assign Server role to the login)
Server roles are kept up by the Database Engineer or Administrator and apply to the whole server, not an individual database document. The public role sets the fundamental permission for all users. Each user that is added to SQL Server is consequently relegated to the public role, you don’t have to do anything. Database roles are connected to an individual database as part of security.
服务器角色由数据库工程师或管理员维护,并应用于整个服务器,而不是单个数据库文档。 公共角色为所有用户设置基本权限。 因此,添加到SQL Server的每个用户都将被授予公共角色,您无需执行任何操作。 作为安全性的一部分,数据库角色连接到单个数据库。
Each login can have a distinctive roles and permissions.
每个登录名可以具有不同的角色和权限。
SELECT
'EXEC master..sp_addsrvrolemember @loginame = N''' + SL.name + ''', @rolename = N''' + SR.name + ''';
' AS [-- Roles To Be Assigned --]
FROM master.sys.server_role_members SRM
INNER JOIN master.sys.server_principals SR ON SR.principal_id = SRM.role_principal_id
JOIN master.sys.server_principals SL ON SL.principal_id = SRM.member_principal_id
WHERE SL.type IN ('S','G','U')
AND SL.name NOT LIKE '##%##'
AND SL.name NOT LIKE 'NT AUTHORITY%'
AND SL.name NOT LIKE 'NT SERVICE%'
AND SL.name <> ('sa')
AND SL.name <> 'distributor_admin';
On the off chance that the user has not been assigned to any role, it is doled out to ‘Public’ role of course. In the above result, “test_test” client isn’t visible, the fact that they are not allocated to any roles. We can see in below picture.
如果没有给用户分配任何角色的机会,则当然会将其分发给“公共”角色。 在以上结果中,“ test_test”客户端不可见,因为它们没有分配给任何角色。 我们可以在下图中看到。
We have enabled users to associate the SQL Server Instance utilizing the above script. Notwithstanding, for database-level permission, we have to make the user at the database level and relegate the permissions.
我们已使用户能够使用上述脚本来关联SQL Server实例。 尽管如此,对于数据库级别的权限,我们必须使用户成为数据库级别的用户并释放权限。
在数据库级别创建用户和权限 (Create User and permissions on Database Level)
As to control security imperative or to maintain a strategic distance from information harming Attacks and SQL Injection, been appointed to the role isn’t satisfactory at SQL Server. Subsequently, we apply second-level access to the database. Presently to keep it in underline with allotting permissions contingent upon sort of objects. The user ought to be allowed with important benefits just at database level by necessary privileges.
为了控制安全势在必行或与伤害信息和SQL注入保持战略距离,SQL Server被任命为该角色并不令人满意。 随后,我们对数据库进行第二级访问。 目前,为了使其与分配权限保持一致,取决于对象的种类。 应该通过必要的特权,仅在数据库级别上为用户提供重要的好处。
Different kind of Article or Object-level permissions can be incorporated with the users or roles relying upon the prerequisites, which could be DDL and DML level authorizations on schema objects suchlike EXECUTE, SELECT, DELETE, INSERT, ALTER, CONNECT, CONTROL, TAKE OWNERSHIP, VIEW DEFINITION, and so forth. SQL Server characterized roles have some pre-set permissions sets; be that as it may, the worth probably won’t get populated for every one of the roles. The permission gets impacted over the object can be stated by consent types GRANT, DENY, and so on.
可以根据先决条件将不同类型的文章或对象级别权限与用户或角色合并,可以是对诸如EXECUTE,SELECT,DELETE,INSERT,ALTER,CONNECT,CONTROL,TAKE OWNERSHIP之类的模式对象的DDL和DML级授权,视图定义等。 SQL Server特征角色具有一些预设的权限集;例如, 尽管如此,对于每个角色来说,价值可能都不会被填充。 权限受对象影响可以通过同意类型GRANT,DENY等声明。
Indeed, even inside the schema, we can access controls on different sorts of SQL Server objects, for example, the Tables (System table and User Table), Functions (Scalar Function, Table Valued Function), Views, Procedure and so on. Presently for the Financial information which should be classified, the client ought to have the entrance control on columns of the table also. All member from SQL Server login shouldn’t see the columns of the table where column level permission isn’t permitted. In this manner, when SQL Logins are being moved or copied to the next server for the same database here a similar kind of security get to permissions must be replicated and connected with logins. See here, every one of the cases we saw, we have quite recently replicated Logins and its role to SQL Instances, anyway, those ought to exist on database level too.
实际上,即使在架构内部,我们也可以访问不同种类SQL Server对象上的控件,例如,表(系统表和用户表),函数(标量函数,表值函数),视图,过程等。 当前,对于应该分类的财务信息,客户还应该在表的列上具有入口控制。 从SQL Server登录名的所有成员都不应看到不允许列级权限的表中的列。 以这种方式,当将SQL登录名移动或复制到同一数据库的下一个服务器时,此处必须复制相似的安全性获取权限并将其与登录名连接。 看到这里,我们看到的每一种情况,我们最近都将Logins及其角色复制到SQL实例,无论如何,这些也应该存在于数据库级别。
Underneath query will create a list of users which are existing in the database. With the end goal of the movement, the query can be executed in a LOOP to get it for all client databases.
在查询下面将创建数据库中现有的用户列表。 通过移动的最终目标,可以在LOOP中执行查询,以获取所有客户端数据库的查询。
SELECT 'USE '+ DB_NAME()+'; CREATE USER ['+dp.name+'] FOR LOGIN ['+dp.name+'];'+
'ALTER USER ['+dp.name+'] WITH DEFAULT_SCHEMA=['+dp.default_schema_name+'];' AS [-- Logins To Be Created --]
FROM sys.database_principals AS dp
INNER JOIN sys.server_principals sp ON dp.sid = sp.sid
WHERE (dp.type in ('S','G','U'))
AND dp.name NOT LIKE '##%##'
AND dp.name NOT LIKE 'NT AUTHORITY%'
AND dp.name NOT LIKE 'NT SERVICE%'
AND dp.name <> ('sa')
AND dp.default_schema_name IS NOT NULL
AND dp.name <> 'distributor_admin'
AND dp.principal_id > 4
With the expanded the size and complex nature of a database, the methodology ends up being increasingly more toilsome to deal with, specifically if attempting to allocate object-level permission to individual logins. The level of difficulty increases, and it is expanding that hitches show up during deployment, the access-control error happens, and security evades show up. This leads unavoidably to the way of least conflict where, for instance, all user accounts end up as members of the db_datawriter and db_datareader roles or, far more atrocious, reasonable access control is completely relinquished for ‘getting the application working’.
随着数据库规模的扩大和复杂性的增加,该方法最终变得越来越繁琐,尤其是在尝试为单个登录分配对象级权限时。 难度越来越高,部署期间出现故障,访问控制错误发生以及安全性回避的程度正在扩大。 这不可避免地导致一种最小冲突的方式,例如,所有用户帐户最终都成为db_datawriter和db_datareader角色的成员,或者更为残酷的是,为了“使应用程序正常运行”,完全放弃了合理的访问控制。
The initial phase in ensuring your customer’s information is figuring out which users need to see which information and after that enabling access to just those users. For instance, a finance agent presumably sees compensation figures for everybody in your organization while group directors approach pays rates for colleagues. Singular representatives have no compelling reason to see compensations by any means.
确保客户信息的初始阶段是确定哪些用户需要查看哪些信息,然后才可以访问这些用户。 例如,一个财务代理人大概会看到您组织中每个人的薪酬数字,而组长方法会为同事支付报酬。 单数代表没有任何令人信服的理由以任何方式获得赔偿。
Now, we can generate the number of schema and object permissions for the user using the below query:
现在,我们可以使用以下查询为用户生成模式和对象权限的数量:
The query needs to be executed in each database using a loop. It returns user with individual permission in a separate statement.
需要使用循环在每个数据库中执行查询。 它在单独的语句中返回具有个人权限的用户。
SELECT 'USE '+ DB_NAME()+'; '+CASE WHEN dp.state <> 'W' THEN dp.state_desc ELSE 'GRANT' END +' ' +
dp.permission_name + ' TO ' + QUOTENAME(dpg.name) COLLATE database_default +
CASE WHEN dp.state <> 'W' THEN '' ELSE ' WITH GRANT OPTION' END +';' AS [-- Permission To Be Assign to the User --]
FROM sys.database_permissions AS dp
INNER JOIN sys.database_principals AS dpg ON dp.grantee_principal_id = dpg.principal_id
WHERE dp.major_id = 0 AND dpg.principal_id > 4
AND (dpg.type in ('S','G','U'))
AND dpg.name NOT LIKE '##%##'
AND dpg.name NOT LIKE 'NT AUTHORITY%'
AND dpg.name NOT LIKE 'NT SERVICE%'
AND dpg.name <> ('sa')
AND dpg.default_schema_name IS NOT NULL
AND dpg.name <> 'distributor_admin'
AND dpg.principal_id > 4
ORDER BY dpg.name
结论 (Conclusion)
This article is designated to help and structure a legitimate database access control framework and SQL Logins Relocation or Migration utilizing script. counting single content to play out all undertaking, it would assist a great deal with making it simple. For automation, dynamic SQL script keeps running on a remote server to make it brisk.
本文旨在帮助和构建合法的数据库访问控制框架以及使用脚本SQL登录名重定位或迁移。 计算单个内容以完成所有任务,将大大简化流程。 为了实现自动化,动态SQL脚本会在远程服务器上保持运行状态,从而使其运行起来更加轻松。
翻译自: https://www.sqlshack.com/move-or-copy-sql-logins-with-assigning-roles-and-permissions/
sql登录名和用户名





















 1376
1376

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








