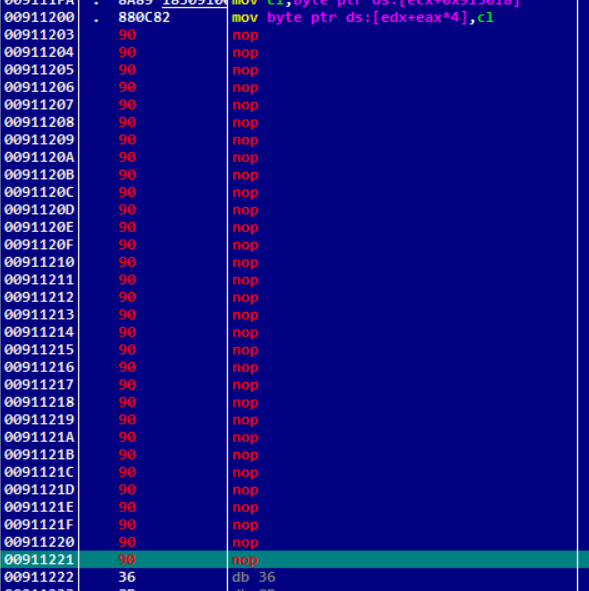
有花指令,nop掉后用IDA打开(Ghidra好像自动过滤花指令,下次试试)
int __cdecl main(int argc, const char **argv, const char **envp)
{
int v3; // eax
int v4; // eax
const wchar_t *v5; // edx
int v6; // eax
char v8[108]; // [esp+4h] [ebp-70h] BYREF
memset(v8, 0, 0x64u);
v3 = sub_401670(std::wcout, (int)L"hello, flag: ");
std::wostream::operator<<(v3, sub_4018B0);
sub_4019B0(std::cin);
sub_401320((int)v8); // 加密flag
v4 = strcmp(a2aycdfl2fs1btm, v8); // 比较加密后的flag
if ( v4 )
v4 = v4 < 0 ? -1 : 1;
v5 = L"right!";
if ( v4 )
v5 = L"error 2333!";
v6 = sub_401670(std::wcout, (int)v5);
std::wostream::operator<<(v6, sub_4018B0);
system("pause");
return 0;
}
加密函数
int __cdecl sub_401320(int a1)
{
int result; // eax
char *v2; // [esp+10h] [ebp-2Ch]
char *Buffer; // [esp+14h] [ebp-28h]
signed int v4; // [esp+1Ch] [ebp-20h]
int i; // [esp+28h] [ebp-14h]
v4 = strlen(flag);
dword_4054A0 = v4;
if ( v4 % 3 == 1 || v4 % 3 != 2 )
{
Buffer = &flag[dword_4054A0++];
sub_401020(Buffer, "=");
}
v2 = &flag[dword_4054A0++];
sub_401020(v2, "=");
for ( i = 0; i < dword_4054A0; i += 3 ) // 对flag的每3位进行加密
sub_4011A0((int)flag, i, a1);
result = v4 / 3;
if ( v4 % 3 == 1 )
return sub_401020((char *)(a1 + 4 * (v4 / 3)), "==");
if ( v4 % 3 == 2 )
result = sub_401020((char *)(a1 + 4 * (v4 / 3)), "=");
return result;
}
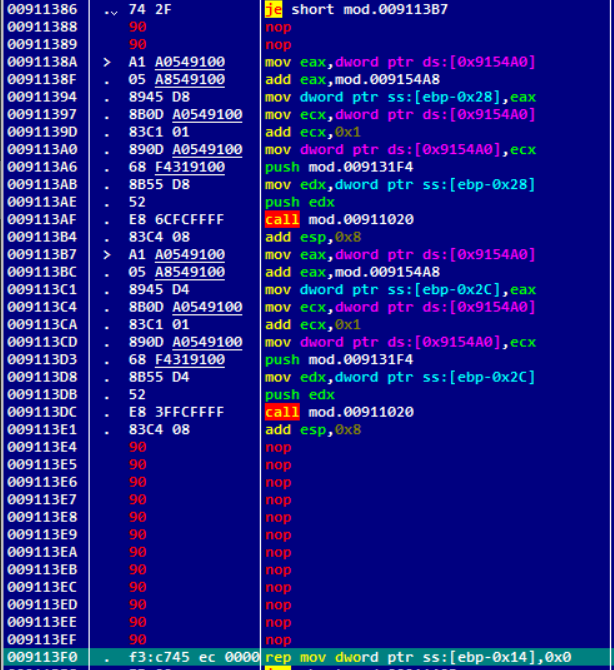
魔改base64
int __cdecl sub_4011A0(int flag, int i, int a3)
{
int result; // eax
_BYTE v4[64]; // [esp+14h] [ebp-40h] BYREF
memset(v4, 0xCCu, sizeof(v4));
*(_BYTE *)(a3 + 4 * (i / 3)) = byte_405018[((4 * (*(_BYTE *)(i + flag + 2) & 3)) | *(_BYTE *)(i + flag + 1) & 0x30 | *(_BYTE *)(i + flag) & 0xC0) >> 2];
*(_BYTE *)(a3 + 4 * (i / 3) + 1) = byte_405018[((4 * (*(_BYTE *)(i + flag) & 3)) | *(_BYTE *)(i + flag + 2) & 0x30 | *(_BYTE *)(i + flag + 1) & 0xC0) >> 2];
*(_BYTE *)(a3 + 4 * (i / 3) + 2) = byte_405018[((4 * (*(_BYTE *)(i + flag + 1) & 3)) | *(_BYTE *)(i + flag) & 0x30 | *(_BYTE *)(i + flag + 2) & 0xC0) >> 2];
result = i / 3;
*(_BYTE *)(a3 + 4 * (i / 3) + 3) = byte_405018[(*(_BYTE *)(i + flag + 2) & 0xC | (4 * *(_BYTE *)(i + flag + 1)) & 0x30 | (16 * *(_BYTE *)(i + flag)) & 0xC0) >> 2];
return result;
}
写个脚本爆破一下
exp
byte_405018 = 'ABCDFEGH1JKLRSTMNP0VWQUXY2a8cdefijklmnopghwxyqrstuvzOIZ34567b9+/'
key = '2aYcdfL2fS1BTMMF1RSeMTTASS1OJ8RHTJdBYJ2STJfNMSMAYcKUJddp'
flag = []
t = 0
while t < len(key):
for x in range(32, 127):
for y in range(32, 127):
for z in range(32, 127):
a = ord(byte_405018[(4 * (z & 3) | y & 0x30 | x & 0xC0) >> 2])
b = ord(byte_405018[(4 * (x & 3) | z & 0x30 | y & 0xC0) >> 2])
c = ord(byte_405018[(4 * (y & 3) | x & 0x30 | z & 0xC0) >> 2])
d = ord(byte_405018[(z & 0XC | 4 * y & 0x30 | 16 * x & 0xC0) >> 2])
if ord(key[t]) == a and ord(key[t + 1]) == b and ord(key[t + 2]) == c and ord(key[t + 3]) == d:
flag.append(x)
flag.append(y)
flag.append(z)
break
t += 4
print(''.join(map(chr, flag)))























 9239
9239











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








