
OpenSSH 是 SSH (Secure SHell) 协议的免费开源实现。SSH协议族可以用来进行远程控制, 或在计算机之间传送文件。而实现此功能的传统方式,如telnet(终端仿真协议)、 rcp ftp、 rlogin、rsh都是极为不安全的,并且会使用明文传送密码。OpenSSH提供了服务端后台程序和客户端工具,用来加密远程控制和文件传输过程中的数据,并由此来代替原来的类似服务。

网络安全一刻也不能放松,为了系统安全尽量将 OPENSSH 升级到最新版本,目前最新版本为 8.2 P1,下面开始准备升级。
- 实验环境 CentOS 7.5
- 为了预防万一升级失败后,无法登陆远程主机的问题,需要先安装 、启动Telnet 服务,确保可以远程登录。
- 安装、配置 Telnet 以及超级守护进程 xinetd 服务
- 编辑 telnet 主配置文件 /etc/xinetd.d/telnet
- vim /etc/xinetd.d/telnet
service telnet
{
disable = no
flags = REUSE
socket_type = stream
wait = no
user = root
server = /usr/sbin/in.telnetd
log_on_failure += USERID
} - 配置telnet登录的终端类型,在 /etc/securetty 文件末尾增加一些pts终端
vim /etc/securettypts/0
pts/1
pts/2
pts/3 - 启动telnet服务
systemctl start telnet.socket
查看服务状态
systemctl status telnet.socket
查看侦听端口
ss -atnl | grep 23
安装完成后,将xinetd服务加入开机自启动:
systemctl enable xinetd.service
将telnet服务加入开机自启动:
systemctl enable telnet.socket




- 使用 telnet 测试登录



- 接下来开始升级 OPENSSH
- 首先在官网上下载最新版本的源码包
- OPENSSH 源码包下载地址:https://openbsd.hk/pub/OpenBSD/OpenSSH/portable/
- OPENSSL 源码包下载地址:https://ftp.openssl.org/source/old/
- wget https://openbsd.hk/pub/OpenBSD/OpenSSH/portable/openssh-8.2p1.tar.gz
- wget https://ftp.openssl.org/source/old/1.1.1/openssl-1.1.1c.tar.gz
- 接下来安装 openssh 和 openssl 依赖包
- yum -y install epel-release
yum -y install perl gcc gcc-c++ glibc make && yum -y group install 'Development Tools' && yum -y install pam-devel libselinux-devel zlib-devel openssl-devel && echo $? -
备份原先的 openssl 文件
mv /usr/bin/openssl /usr/bin/openssl.old - mv /usr/lib64/openssl /usr/lib64/openssl.old
- mv /usr/lib64/libssl.so /usr/lib64/libssl.so.old
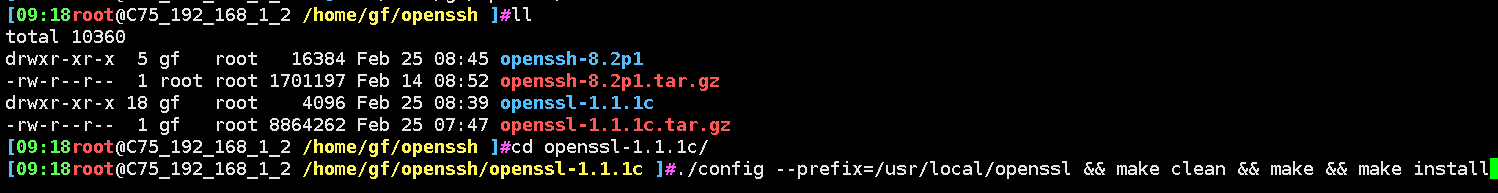
- 解压 openssl 包,编译安装(需要 root 用户)
- tar xf openssl-1.1.1c.tar.gz
- ./config --prefix=/usr/local/openssl && make clean && make && make install && echo $?

-
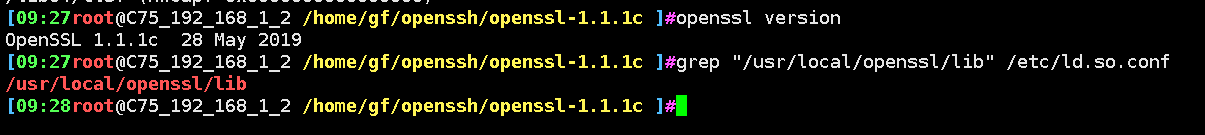
编译、安装无误后,下面开始配置 OPENSSL
设置 openssl 命令的软链接
ln -s /usr/local/openssl/bin/openssl /usr/bin/openssl - ln -s /usr/local/openssl/include/openssl /usr/include/openssl
- ln -s /usr/local/openssl/lib/libssl.so /usr/lib64/libssl.so
- echo "/usr/local/openssl/lib" >> /etc/ld.so.conf
- ldconfig -v
- openssl version

-
开始安装 openssh 前,先备份原先的 openssh 文件
- mv /etc/ssh/* /bak/sshbak
- tar xf openssh-8.2p1.tar.gz
- ./configure --prefix=/usr --sysconfdir=/etc/ssh --with-ssl-dir=/usr/local/openssl \
- --with-md5-passwords --mandir=/usr/share/man \
- --with-pam=enable && make clean && make && make install && echo $?
- echo $? --> 0 确保编译安装无误后,复制启动脚本和PAM验证文件
- cp /home/gf/openssh/openssh-8.2p1/contrib/redhat/sshd.init /etc/init.d/sshd
cp /home/gf/openssh/openssh-8.2p1/contrib/redhat/sshd.pam /etc/pam.d/sshd.pam - 编辑 /etc/ssh/sshd.conf 配置文件
- Port 22
PermitRootLogin no
PasswordAuthentication yes
UsePAM yes
UseDNS no
Subsystem sftp /usr/libexec/sftp-server - 给运行脚本添加执行权限 : chmod +x /etc/init.d/sshd
- 把原先的 systemd 管理的 sshd 启动脚本文件删除或者移走
mv /usr/lib/systemd/system/sshd.service /bak/sshbak && mv /usr/lib/systemd/system/sshd.socket /bak/sshbak && echo $? - 重新加载服务配置文件后重启 sshd 服务
- systemctl daemon-reload && sleep 1 &&systemctl restart sshd &&chkconfig sshd on && echo $?
- 重启确认无误后可以停掉 telnet 服务
- systemctl disable telnet


- 使用 ssh 测试重新登录



-
更改默认端口和指定允许访问的网段
- #Port 22
Port 2222 #更改端口,注意不要被占用起冲突
#AddressFamily any
#ListenAddress 0.0.0.0 #默认允许所有主机链接
ListenAddress 192.168.2.2:2222 #注意这里设定的是服务器本地的IPv4网络IP地址和端口
#ListenAddress :: #IPv6



- 制定脚本自动升级
- opensshupdata/
opensshupdata/
├── openssh-8.3p1.tar.gz
├── openssh.sh
└── openssl-1.1.1j.tar.gz -
opensshupdata/openssh.sh
#!/bin/bash
#
#************************************
#author: GF
#version: 1.0
#date: 2021-05-23
#description:
#FileName: openssh.sh
#************************************if [[ `id -u` != "0" ]]; then
echo "not root!"
exit 1;
fiif [[ -n `ping -c3 www.baidu.com` ]]; then
yum -y install epel-release &> /dev/null
sleep 1;yum -y install perl gcc gcc-c++ glibc make &> /dev/null
sleep 1;yum -y group install 'Development Tools' &> /dev/null
sleep 1;yum -y install pam-devel libselinux-devel zlib-devel openssl-devel &> /dev/null
sleep 1;echo "Dependency installed successfully !"
sleep 1
else
echo "Network is unreachable !"
exit 2;
fiif [[ `echo $?` == "0" ]]; then
echo "Dependency installed successfully !"
else
echo "Dependency installed not successfully!"
exit 3;
fiif [[ -f ./openssl-1.1.1j.tar.gz ]]; then
tar xf ./openssl-1.1.1j.tar.gz &> /dev/null
sleep 2;cd ./openssl-1.1.1j
sleep 2;./config --prefix=/usr/local/openssl &> /dev/null && make clean &> /dev/null && make -j 4 &> /dev/null && make install &> /dev/null
fiif [[ `echo $?` != "0" ]]; then
echo "openssl 1.1.1j make install is faild !"
exit 4;
else
echo "openssl 1.1.1j make and make install is OK!"
sleep 1
sleep 1;mv -f /usr/bin/openssl /usr/bin/openssl.old &> /dev/null
sleep 1;mv -f /usr/lib64/openssl /usr/lib64/openssl.old &> /dev/null
sleep 1;mv -f /usr/lib64/libssl.so /usr/lib64/libssl.so.old &> /dev/null
sleep 1; ln -s /usr/local/openssl/bin/openssl /usr/bin/openssl &> /dev/null
sleep 1; ln -s /usr/local/openssl/include/openssl /usr/include/openssl &> /dev/null
sleep 1; ln -s /usr/local/openssl/lib/libssl.so /usr/lib64/libssl.so &> /dev/null
echo "/usr/local/openssl/lib" > /etc/ld.so.conf.d/openssl.conf
ldconfig -v &> /dev/null
fi/usr/bin/openssl version | grep -o "OpenSSL 1.1.1j" &> /dev/null
if [[ `echo $?` != "0" ]]; then
echo "openssl 1.1.1j is not updata !"
exit 5;
else
echo "openssl 1.1.1j updata is ok!"
cd ../
rm -rf ./openssl-1.1.1j
fiif [[ -f ./openssh-8.5p1.tar.gz ]]; then
mkdir -p /bak/sshbak &> /dev/null
mv -f /etc/ssh/* /bak/sshbak
tar xf ./openssh-8.5p1.tar.gz &> /dev/null
sleep 2;cd ./openssh-8.5p1
sleep 2;./configure --prefix=/usr --sysconfdir=/etc/ssh --with-ssl-dir=/usr/local/openssl --with-md5-passwords --mandir=/usr/share/man --with-pam=enable &> /dev/null&& make clean &> /dev/null&& make -j 4 &> /dev/null && make install &> /dev/null
else
echo "openssh-8.5p1.tar.gz not found !"
exit 12;
fiif [[ `echo $?` != "0" ]]; then
echo "openssh 8.5p1 not make install !"
exit 6;
else
echo "openssh 8.5p1 make install is ok!"
fiif [[ -f ./contrib/redhat/sshd.init ]]; then
install ./contrib/redhat/sshd.init /etc/init.d/sshd
chmod +x /etc/init.d/sshd
else
echo "sshd.init file not found!"
exit 7;
fi
if [[ -f ./contrib/redhat/sshd.pam ]]; then
install ./contrib/redhat/sshd.pam /etc/pam.d/sshd.pam
else
echo "sshd.pam file not found!"
exit 11;
fiif [[ `echo $?` != "0" ]]; then
echo "openssh not make install !"
exit 8;
fiif [[ -f /etc/ssh/sshd_config ]]; then
sed -i "s/#PermitRootLogin .*/PermitRootLogin yes/g" /etc/ssh/sshd_config
sed -i "s/PermitRootLogin .*/PermitRootLogin yes/g" /etc/ssh/sshd_config
sed -i "s/#PasswordAuthentication .*/PasswordAuthentication yes/g" /etc/ssh/sshd_config
sed -i "s/PasswordAuthentication .*/PasswordAuthentication yes/g" /etc/ssh/sshd_config
sed -i "s/#PermitEmptyPasswords .*/PermitEmptyPasswords no/g" /etc/ssh/sshd_config
sed -i "s/PermitEmptyPasswords .*/PermitEmptyPasswords no/g" /etc/ssh/sshd_config
sed -i "s/#UsePAM no/UsePAM yes/g" /etc/ssh/sshd_config
sed -i "s/UsePAM no/UsePAM yes/g" /etc/ssh/sshd_config
sed -i "s/#UseDNS no/UseDNS no/g" /etc/ssh/sshd_config
sed -i "s/UseDNS yes/UseDNS no/g" /etc/ssh/sshd_config
else
echo "file /etc/ssh/sshd_config is not found !"
exit 9:
fiif [[ `echo $?` = "0" ]]; then
mv -f /usr/lib/systemd/system/sshd.service /bak/sshbak &> /dev/null
mv -f /usr/lib/systemd/system/sshd.socket /bak/sshbak &> /dev/null
systemctl daemon-reload && sleep 1 &&systemctl restart sshd &&chkconfig sshd on
else
echo "sshd service not start !"
exit 10;
fiif [[ `echo $?` == "0" ]]; then
echo "sshd service is start!"
cd ../
rm -rf ./openssh-8.5p1
else
echo "sshd service is not start !"
exit 13;
fi
ss -a|grep ssh
ssh -V
openssl version -
测试

























 402
402











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








