- 什么是加壳?
利用特殊的算法,对可执行文件的编码进行改变(比如压缩、加密),以达到保护程序代码的目的
- 什么是脱壳?
摘掉壳程序,将未加密的可执行文件还原出来(有些人也称为“砸壳”)
- iOS中有很多好用的脱壳工具
Clutch:https://github.com/KJCracks/Clutch
dumpdecrypted:https://github.com/stefanesser/dumpdecrypted/
pAppCrackr、Crackulous
- 通过otool命令行可以查看可执行文件是否脱壳
otool -l 可执行文件路径 | grep crypt
0为已经脱壳
Clutch配置
- 下载最新的Release版:https://github.com/KJCracks/Clutch/releases
- 建议去掉版本号,改名为Clutch
- 将Clutch文件拷贝到iPhone的/usr/bin目录中
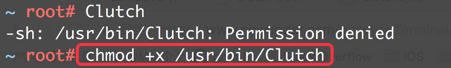
- 如果在iPhone上执行Clutch指令,权限不够的话,赋予 可执行的权限
chmod +x /usr/bin/Clutch
-
列出已经安装的APP: Clutch -i
iPhone:~ root# Clutch -i
Installed apps:
1: 腾讯视频-怒晴湘西独播 <com.tencent.live4iphone>
2: 车来了 <com.chelaile.lite>
3: Stream <com.fish.stream>
4: QQ <com.tencent.mqq>
5: UC浏览器-新闻资讯抢先看 <com.ucweb.iphone.lowversion>
6: 酷狗音乐-就是歌多 <com.kugou.kugou1002>
7: 喜马拉雅 <com.gemd.iting>
8: ボイスレコーダー-無料ボイスメモ <com.leqimea.recorderAudio>
9: 爱思加强版 <com.pd.A4Player>
10: 抖音短视频 <com.ss.iphone.ugc.Aweme>-
输入APP序号或者Bundle id进行脱壳操作:Clutch -d APP序号或BundleId
iPhone:~ root# Clutch -d 3
Zipping NetworkSniffer.app
ASLR slide: 0x10002c000
Dumping <PackageTunnelProvider> (arm64)
Patched cryptid (64bit segment)
...-
脱壳成功后会生成一个ipa文件
DONE: /private/var/mobile/Documents/Dumped/com.fish.stream-iOS9-(Clutch-2.0.4).ipa
Finished dumping com.fish.stream in 3.1 seconds
iPhone:~ root#dumpdecrypted配置
-
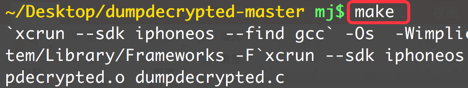
下载源代码,然后在源代码目录执行make指令进行编译,获得dylib动态库文件
https://github.com/stefanesser/dumpdecrypted/
-
将dylib文件拷贝到iPhone上(如果是root用户,建议放/var/root目录)
-
终端进入dylib所在的目录
-
使用环境变量DYLD_INSERT_LIBRARIES将dylib注入到需要脱壳的可执行文件(可执行文件路径可以通过ps-A查看获取)
DYLD_INSERT_LIBRARIES=dumpdecrypted.dylib 可执行文件路径
iPhone:~ root# DYLD_INSERT_LIBRARIES=dumpdecrypted.dylib /var/mobile/Containers/Bundle/Application/06237BF4-4E31-46DD-B667-5FC17F5FD461/ting.app/ting
mach-o decryption dumper
DISCLAIMER: This tool is only meant for security research purposes, not for application crackers.
[+] detected 64bit ARM binary in memory.
[+] offset to cryptid found: @0x10004cca8(from 0x10004c000) = ca8
[+] Found encrypted data at address 00004000 of length 61276160 bytes - type 1.
[+] Opening /private/var/mobile/Containers/Bundle/Application/06237BF4-4E31-46DD-B667-5FC17F5FD461/ting.app/ting for reading.
[+] Reading header
[+] Detecting header type
[+] Executable is a FAT image - searching for right architecture
[+] Correct arch is at offset 67125248 in the file
[+] Opening ting.decrypted for writing.
[+] Copying the not encrypted start of the file
[+] Dumping the decrypted data into the file
[+] Copying the not encrypted remainder of the file
[+] Setting the LC_ENCRYPTION_INFO->cryptid to 0 at offset 4004ca8
[+] Closing original file
[+] Closing dump file
iPhone:~ root#-
.decrypted文件就是脱壳后的可执行文件
在手机路径的/device/var/root文件里
常用格式
class-dump -H Mach-O文件路径 -o 头文件存放目录






















 1724
1724











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








