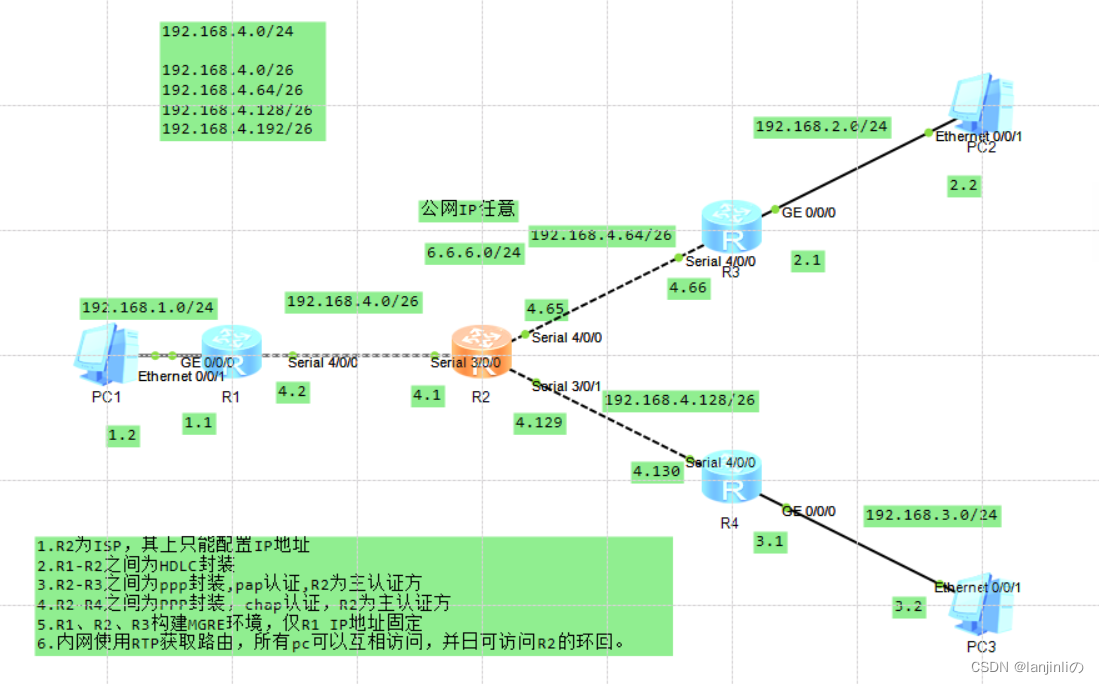
点到点、NBMA综合实验
题目与ip规划
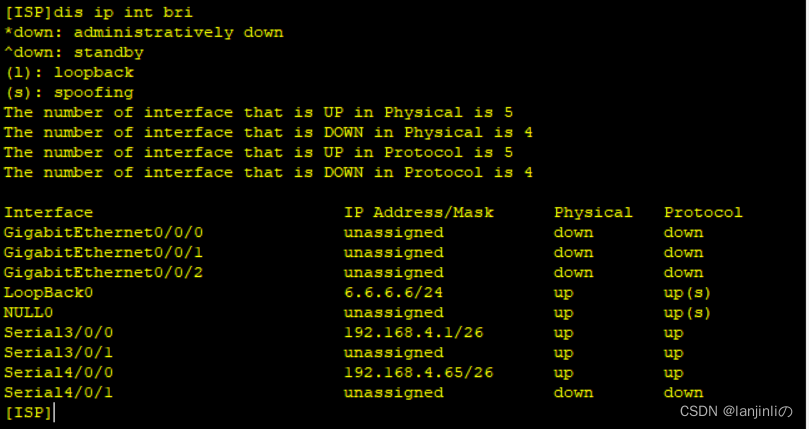
ISP环回和ip配置
R2配置
[ISP]int loop0
[ISP-LoopBack0]ip add 6.6.6.6 24
[ISP-LoopBack0]q
[ISP]int S3/0/0
[ISP-Serial3/0/0]ip add 192.168.4.1 26
[ISP-Serial3/0/0]q
[ISP]int S4/0/0
[ISP-Serial4/0/0]ip add 192.168.4.65 26
[ISP-Serial4/0/0]q
[ISP]int S3/0/1
[ISP-Serial3/0/1]ip add 192.168.4.129 26
R1-R2之间的HDLC封装
R1
[R1-Serial4/0/0]link-protocol hdlc
Warning: The encapsulation protocol of the link will be changed. Continue? [Y/N]:y
Aug 3 2023 19:12:34-08:00 R1 %%01IFNET/4/CHANGE_ENCAP(l)[1]:The user performed
the configuration that will change the encapsulation protocol of the link and then selected Y.
[R1-Serial4/0/0]
R2
[ISP]int S3/0/0
[ISP-Serial3/0/0]link-protocol hdlc
Warning: The encapsulation protocol of the link will be changed. Continue? [Y/N]:y
Aug 3 2023 19:19:42-08:00 ISP %%01IFNET/4/CHANGE_ENCAP(l)[0]:The user performed
the configuration that will change the encapsulation protocol of the link and then selected Y.
[ISP-Serial3/0/0]
3.R2-R3之间为ppp封装,pap认证,R2为主认证方
R2
[ISP-Serial4/0/0]link-protocol ppp
[ISP]aaa.
[ISP-aaa]local-user a password cipher 123456
Info: Add a new user.
[ISP-aaa]local-user a service-type ppp
[ISP-aaa]q
[ISP]int S4/0/0
[ISP-Serial4/0/0]ppp authentication-mode pap
[ISP-Serial4/0/0]
R3
[R3-Serial4/0/0]link-protocol ppp
[R3-Serial4/0/0]q
[R3]int S4/0/0
[R3-Serial4/0/0]ppp pap local-user a password cipher 123456
[R3-Serial4/0/0]
认证通过后:Protocol由down’变为up
R2-R4之间为PPP封装,chap认证,R2为主认证方
R2
[ISP-Serial3/0/1]link-protocol ppp
[ISP-Serial3/0/1]q
[ISP]aaa.
[ISP-aaa]local-user a password cipher 123456
Info: Add a new user.
[ISP-aaa]local-user a service-type ppp
[ISP-aaa]q
[ISP]int S3/0/1
[ISP-Serial3/0/1]ppp authentication-mode chap
R4
[R4]int S4/0/0
[R4-Serial4/0/0]ppp chap user a
[R4-Serial4/0/0]ppp chap password cipher 123456
[R4-Serial4/0/0]
R1、R2、R3构建MGRE环境,仅R1 IP地址固定
R1、R3、R4的缺省路由(使各个外网访问内网)
R1
[R1]ip rout 0.0.0.0 0 192.168.4.1
R3
[R3]ip rout 0.0.0.0 0 192.168.4.65
R4
[R4]ip rout 0.0.0.0 0 192.168.4.129
构建MGRE环境
R1
[R1]int Tunnel 0/0/0
[R1-Tunnel0/0/0]ip add 192.168.5.1 24
[R1-Tunnel0/0/0]tunnel-protocol gre p2mp
[R1-Tunnel0/0/0]source 192.168.4.2
[R1-Tunnel0/0/0]nhrp entry multicast dynamic
[R1-Tunnel0/0/0]nhrp network-id 100
[R1-Tunnel0/0/0]
R3
[R3]int Tunnel 0/0/0
[R3-Tunnel0/0/0]ip add 192.168.5.2 24
[R3-Tunnel0/0/0]tunnel-protocol gre p2mp
[R3-Tunnel0/0/0]source Serial 4/0/0
[R3-Tunnel0/0/0]nhrp entry 192.168.5.1 192.168.4.2 register
[R3-Tunnel0/0/0]nhrp network-id 100
[R3-Tunnel0/0/0]
R4
内网使用RIP获取路由,所有pc可以互相访问,并日可访问R2的环回。
R1
[R1]rip 1
[R1-rip-1]ver 2
[R1-rip-1]network 192.168.4.0
[R1-rip-1]network 192.168.1.0
[R1-rip-1]network 192.168.5.0
[R1-rip-1]
R3
[R3]rip 1
[R3-rip-1]version 2
[R3-rip-1]network 192.168.4.0
[R3-rip-1]network 192.168.2.0
[R3-rip-1]network 192.168.5.0
[R3-rip-1]
R4
[R4]rip 1
[R4-rip-1]version 2
[R4-rip-1]network 192.168.4.0
[R4-rip-1]network 192.168.3.0
[R4-rip-1]q
[R4]
NAT配置
R1
[R1]acl 2000
[R1-acl-basic-2000]rule permit source any
[R1-acl-basic-2000]int S4/0/0
[R1-Serial4/0/0]nat outbound 2000
[R1-Serial4/0/0]
R3
[R3]acl 2000
[R3-acl-basic-2000]rule permit source any
[R3-acl-basic-2000]int S4/0/0
[R3-Serial4/0/0]nat outbound 2000
[R3-Serial4/0/0]
R4
[R4]acl 2000
[R4-acl-basic-2000]rule permit source any
[R4-acl-basic-2000]int S4/0/0
[R4-Serial4/0/0]nat outbound 2000
[R4-Serial4/0/0]





















 325
325











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








