前言
本篇将介绍在自己创建的私有CA下,tomcat启用SSL/TLS支持。
私钥CA除了在内网中使用,我还真不知道有什么其他用处………………
至于SSL/TSL不熟悉的请自行百度或者看本人其他文章:
常见加密类型及通信安全:http://blog.csdn.net/hylexus/article/details/53048305
SSL、openSSL、CA:http://blog.csdn.net/hylexus/article/details/53058135
对于本篇文章来说,或许,我们只需要知道:TLS(Transport Layer Layer)和他的前生SSL(Secure Socket Layer)是一种浏览器和服务器之间安全通信的技术。就够了吧。
在tomcat中启用SLL/TLS支持,至少有两种方式(以下两种叫法并不是专业术语):
- APR类型的Connector下启用HTTPS
- BIO/NIO类型的Connector下启用HTTPS
对于这几种Connector不熟悉的,可以参考本人另一篇介绍APR的文章:http://blog.csdn.net/hylexus/article/details/53137721
Tomcat currently operates only on JKS, PKCS11 or PKCS12 format keystores. The JKS format is Java’s standard “Java KeyStore” format, and is the format created by the keytool command-line utility. This tool is included in the JDK. The PKCS12 format is an internet standard, and can be manipulated via (among other things) OpenSSL and Microsoft’s Key-Manager.
由以上这段来自tomcat官方文档的介绍可知:
- tomcat目前支持JKS, PKCS11 或 PKCS12格式的keystore
- JKS是java标准的秘钥管理格式,通过java内置的命令keytool来操作
- PKCS是互联网通用的格式,可以用openssl或微软的Key-Manager来操作
下文就这两种(keytool和openssl)方式来实现tomcat对HTTPS的支持
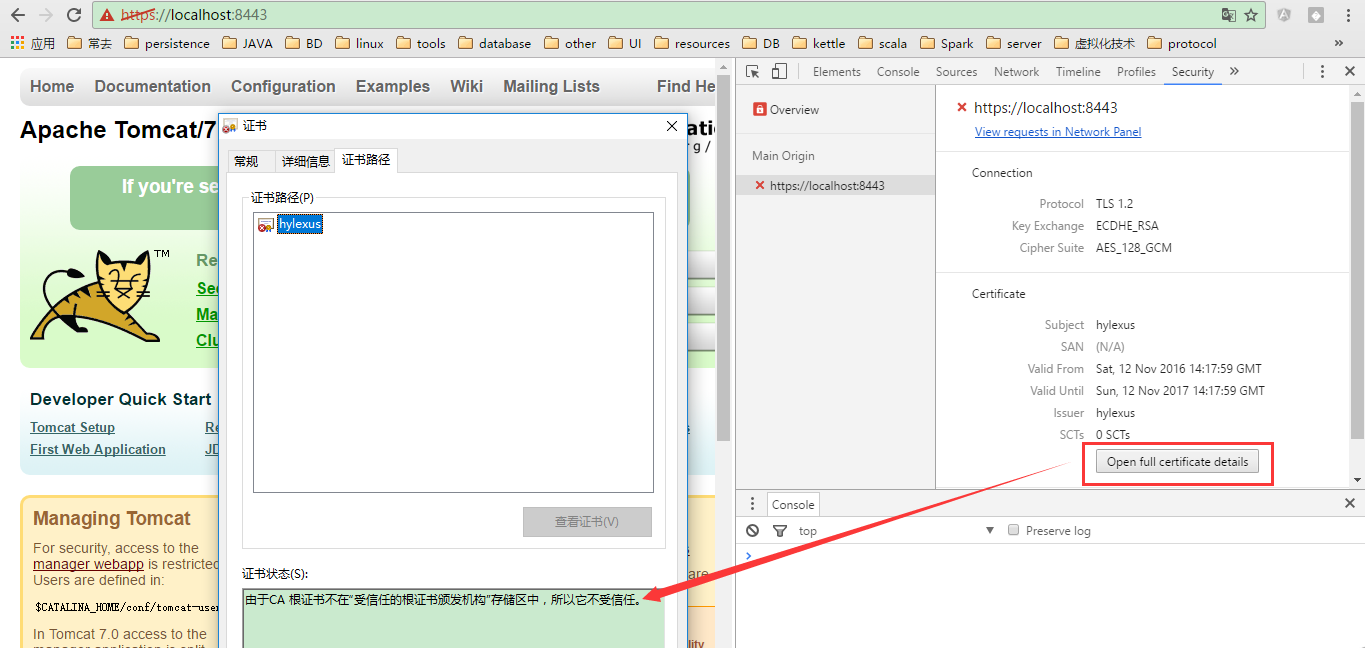
1 基于keytool实现
1.1 生成自签署证书
# 此处本人在目录D:\java-env\apache-tomcat-7-80\ssl\ks下操作
keytool -genkeypair \
-alias tomcat \
-keyalg rsa \
-keysize 2048 \
-validity 365 \
-keystore keystore
# 此处将keystore的位置指定为:D:\java-env\apache-tomcat-7-80\ssl\ks\keystore1.2 配置tomcat
此处使用NIO类型的Connector
<Connector
protocol="org.apache.coyote.http11.Http11NioProtocol"
port="8443" maxThreads="200"
scheme="https" secure="true" SSLEnabled="true"
keystoreFile="${catalina.home}/ssl/ks/keystore" keystorePass="123456"
clientAuth="false" sslProtocol="TLS"/>1.3 效果
2 基于openssl实现
2.1 将自己的机器配置为私有CA
这部分参加本人另一篇文章: http://blog.csdn.net/hylexus/article/details/53058135#4-openssl实现私有ca
2.2 生成CSR
此处本人在tomcat安装目录下新建ssl目录,在ssl目录中操作
# 生成私钥tomcat.key
[root@hylexus ssl]# (umask 077;openssl genrsa -out tomcat.key 2048)
# .....
# 生成证书颁发请求tomcat.csr
[root@hylexus ssl]# openssl req -new -key tomcat.key -out tomcat.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [CN]:
State or Province Name (full name) [ShangHai]:
Locality Name (eg, city) [ShangHai]:
Organization Name (eg, company) [Default Company Ltd]:KKBC
Organizational Unit Name (eg, section) [dev]:
Common Name (eg, your name or your server's hostname) []:test.com
Email Address []:hylexus@163.com
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:2.3 私有CA颁发证书
此处由于CA是我们自己的私钥CA,和应用程序在同一台主机上。所以直接签署即可:
openssl ca -in tomcat.csr -out tomcat.crt -days 365至此,看看我们的ssl目录:
[root@hylexus ssl]# tree
.
├── tomcat.crt # 2.3步骤中生成的证书
├── tomcat.csr # 2.2步骤中生成的证书颁发请求
└── tomcat.key # 2.2步骤中生成的应用程序的私钥2.4 配置tomcat
2.4.1 基于APR-Connector的配置
前提是要启用APR,可以参考:http://blog.csdn.net/hylexus/article/details/53137721
<Connector
protocol="org.apache.coyote.http11.Http11AprProtocol"
port="8443" maxThreads="200"
scheme="https" secure="true" SSLEnabled="true"
SSLCertificateFile="${catalina.base}/ssl/tomcat.crt"
SSLCertificateKeyFile="${catalina.base}/ssl/tomcat.key"
SSLVerifyClient="optional" SSLProtocol="TLSv1+TLSv1.1+TLSv1.2"/>2.4.2 基于NIO/BIO-Connector的配置
此处还是在tomcat安装目录下新建的ssl目录下操作:
- 1) 生成私钥和keystore
# 放置于tomcat安装目录的ssl目录下的ks文件中
keytool -genkeypair -keyalg rsa -keysize 2048 -keystore ks- 2) 将私钥CA自己的证书导入到keystore(ks)中
keytool -importcert \
# 这个文件是私钥CA自己的证书并不是私钥CA颁发给tomcat的证书
-file /etc/pki/CA/cacert.pem \
-alias my_ca \ # 起名
-keystore ./ks \ # 导入到${catalina.home}/ssl/ks文件中
-trustcacerts - 3) 将私钥CA颁发给tomcat的证书导入同一个keystore(ks)
keytool -importcert \
-file tomcat.crt \ # 这个是私钥CA颁发给tomcat的证书
-alias tomcat_crt \
-keystore ./ks \
-trustcacerts- 4) 配置server.xml
NIO-Connector配置
<Connector
protocol="org.apache.coyote.http11.Http11NioProtocol"
port="8443" maxThreads="200"
scheme="https" secure="true" SSLEnabled="true"
keystoreFile="${catalina.home}/ssl/ks" keystorePass="123456"
clientAuth="false" sslProtocol="TLS"/>BIO-Connector配置
<Connector port="8443" protocol="org.apache.coyote.http11.Http11Protocol"
connectionTimeout="20000" SSLEnabled="true"
maxThreads="150" scheme="https" secure="true"
clientAuth="false" sslProtocol="TLS"
keystoreFile="${catalina.home}/ssl/ks" keystorePass="123456"
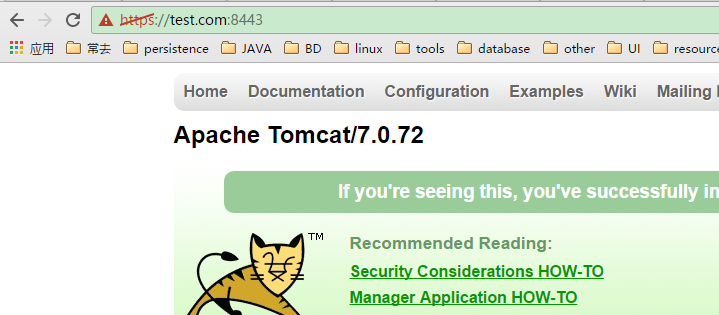
/>2.5 效果
此处注意修改hosts文件,我们在CSR中写的域名是test.com
参考文章
http://tomcat.apache.org/tomcat-7.0-doc/config/http.html#Special_Features
http://tomcat.apache.org/tomcat-7.0-doc/ssl-howto.html
http://docs.oracle.com/javase/6/docs/technotes/tools/windows/keytool.html


























 812
812

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








