0x01 背景
Dedecms V5.8.1 bate存在前端RCE,并且利用简单,对于这种有趣的,高质量的RCE很感兴趣于是进行复现分析后有了这篇文章。
注:Dedecms源码已经开发,并且本次分析均在本地环境测试,文章仅记录分享,不得用于任何非法活动。
0x02 环境搭建
下载Dedecms:
https://github.com/dedecms/DedeCMS/releases/tag/v5.8.1
0x03 源码分析
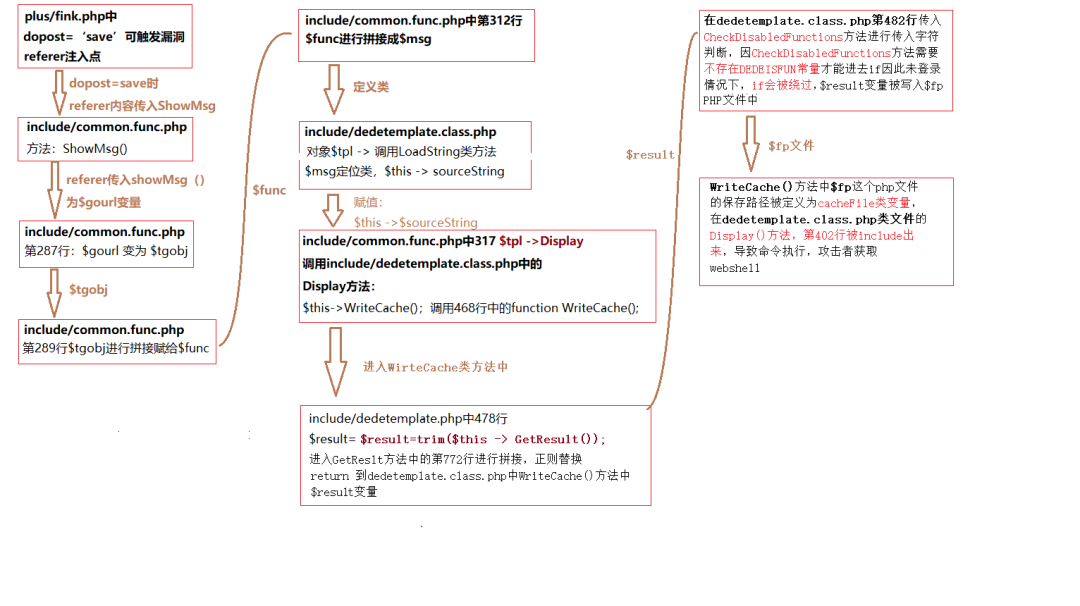
漏洞利用链整体分析:
1、定位include/common.func.php中的ShowMsg()方法:
function ShowMsg($msg, $gourl, $onlymsg = 0, $limittime = 0)
{
if (empty($GLOBALS['cfg_plus_dir'])) {
$GLOBALS['cfg_plus_dir'] = '..';
}
if ($gourl == -1) {
$gourl = isset($_SERVER['HTTP_REFERER']) ? $_SERVER['HTTP_REFERER'] : '';
if ($gourl == "") {
$gourl = -1;
}
}
$htmlhead = "html内容" . (isset($GLOBALS['ucsynlogin']) ? $GLOBALS['ucsynlogin'] : '') . "html内容";
$htmlfoot = "html内容";
$litime = ($limittime == 0 ? 1000 : $limittime);
$func = '';
if ($gourl == '-1') {
if ($limittime == 0) {
$litime = 3000;
}
$gourl = "javascript:history.go(-1);";
}
if ($gourl == '' || $onlymsg == 1) {
$msg = "";
} else {
//当网址为:close::objname 时, 关闭父框架的id=objname元素
if (preg_match('/close::/', $gourl)) {
$tgobj = trim(preg_replace('/close::/', '', $gourl));
$gourl = 'javascript:;';
$func .= "window.parent.document.getElementById('{$tgobj}').style.display='none';\r\n"; } $func .= "var pgo=0; function JumpUrl(){ if(pgo==0){ location='$gourl'; pgo=1; } }\r\n"; $rmsg = $func; $rmsg .= "document.write(\"
\");\r\n";
$rmsg .= "document.write(\"







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章














 1625
1625











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








