上文我们讲过,Kubernetes以其良好的容器管理特性和丰富的平台管理能力获得越来越多的开发者的青睐。但是对于那些运行在Kubernetes Pod中的应用程序而言,运维是方便多了,但是调试却成了大大的问题。不同于本地调试,运行在Kubernete Pod中的应用程序受限于容器封装形式、网络环境、开发语言等带给了开发者新的挑战。所谓“磨刀不误砍柴工”,对于开发者而言,寻找合适的、可用的调试方法,花再多的精力和时间都是值得的。本文我就给大家分享一种简单而实用的调试方法,希望对大家有用。(笔者的开发环境是Ubuntu 18.04)
一、安装 krew
# set -x; cd "$(mktemp -d)" &&
curl -fsSLO "https://github.com/kubernetes-sigs/krew/releases/latest/download/krew.tar.gz" &&
tar zxvf krew.tar.gz &&
KREW=./krew-"$(uname | tr '[:upper:]' '[:lower:]')_amd64" &&
"$KREW" install krew
# export PATH=$HOME/.krew/bin:$PATH二、安装ksniffer插件
# kubectl krew install sniff三、在你的ubuntu系统中安装wireshark或者tcpdump
四、测试,比如本例中我要调试其他应用对minio服务的访问的细节:
# kubectl sniff minio-7784cf8ddb-bznhk -n minio执行时候的log信息如下:
INFO[0000] sniffing method: upload static tcpdump
INFO[0000] using tcpdump path at: '/root/.krew/store/sniff/v1.4.2/static-tcpdump'
INFO[0000] no container specified, taking first container we found in pod.
INFO[0000] selected container: 'minio'
INFO[0000] sniffing on pod: 'minio-7784cf8ddb-bznhk' [namespace: 'minio', container: 'minio', filter: '', interface: 'any']
INFO[0000] uploading static tcpdump binary from: '/root/.krew/store/sniff/v1.4.2/static-tcpdump' to: '/tmp/static-tcpdump'
INFO[0000] uploading file: '/root/.krew/store/sniff/v1.4.2/static-tcpdump' to '/tmp/static-tcpdump' on container: 'minio'
INFO[0000] executing command: '[/bin/sh -c ls -alt /tmp/static-tcpdump]' on container: 'minio', pod: 'minio-7784cf8ddb-bznhk', namespace: 'minio'
INFO[0000] command: '[/bin/sh -c ls -alt /tmp/static-tcpdump]' executing successfully exitCode: '1', stdErr :'ls: /tmp/static-tcpdump: No such file or directory
'
INFO[0000] file not found on: '/tmp/static-tcpdump', starting to upload
INFO[0001] verifying file uploaded successfully
INFO[0001] executing command: '[/bin/sh -c ls -alt /tmp/static-tcpdump]' on container: 'minio', pod: 'minio-7784cf8ddb-bznhk', namespace: 'minio'
INFO[0001] command: '[/bin/sh -c ls -alt /tmp/static-tcpdump]' executing successfully exitCode: '0', stdErr :''
INFO[0001] file found: '-rwxr-xr-x 1 root root 2696368 Jan 1 1970 /tmp/static-tcpdump
'
INFO[0001] file uploaded successfully
INFO[0001] tcpdump uploaded successfully
INFO[0001] spawning wireshark!
INFO[0001] start sniffing on remote container
INFO[0001] executing command: '[/tmp/static-tcpdump -i any -U -w - ]' on container: 'minio', pod: 'minio-7784cf8ddb-bznhk', namespace: 'minio'
INFO[0127] starting sniffer cleanup
INFO[0127] sniffer cleanup completed successfully 之后就会自动打开wireshark:
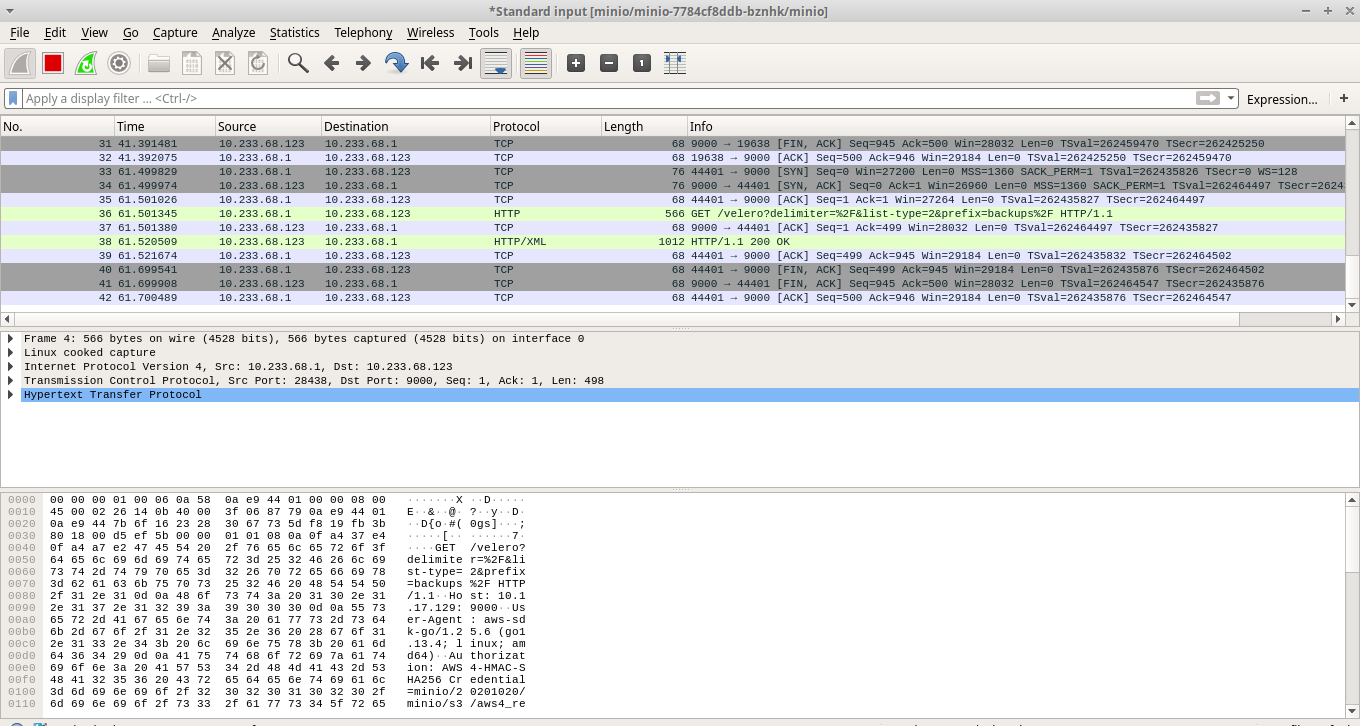
接下来就可以输入一些过滤规则来进行数据包分析了。比如我想看看velero如何和minio交互:
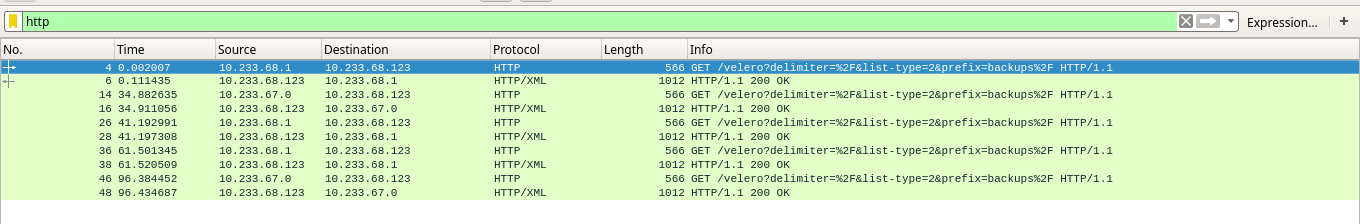
是不是很方便呢?如果对您有帮助,点个赞吧。





















 238
238











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








