第 18 章: TPM 2.0 串口通讯报文结构
18.1: 总体介绍
命令桢格式
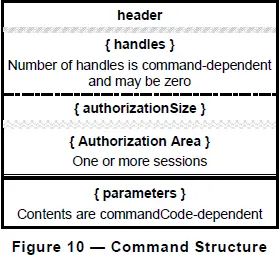
图-10.png
如图-10: 完整的命令帧包括以下5部分, 第2和第5部分可以为空, 第3和第4部分总是同时出现. 但各部分排列顺序不能颠倒.
- Header
- Handles
- Size of Authorization Area
- Authorization Area
- Parameters
 本文档介绍了TPM 2.0设备串口通讯的报文结构,包括命令帧和应答帧的详细格式,分别包含Header、Handles、Authorization Area和Parameters等关键部分,为理解TPM 2.0通信机制提供指导。
本文档介绍了TPM 2.0设备串口通讯的报文结构,包括命令帧和应答帧的详细格式,分别包含Header、Handles、Authorization Area和Parameters等关键部分,为理解TPM 2.0通信机制提供指导。
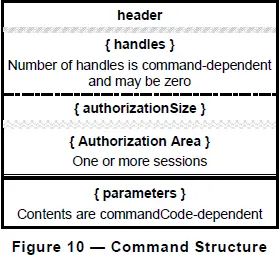
如图-10: 完整的命令帧包括以下5部分, 第2和第5部分可以为空, 第3和第4部分总是同时出现. 但各部分排列顺序不能颠倒.
 7634
7634

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?


