目录
4/22周赛WP 一根香烟 学姐的凝视 babyre easyre 学姐的凝视 签到 easyCrypto 你会解方程组不会?ikun计算器 easyre1好玩的时间戳
一根香烟
<?php
error_reporting(0);
highlight_file(__FILE__);
$a = $_POST['heizi'];
if (isset($a)){
if(substr($a,0,4) == "ding" and substr($a,-4,4) == "zhen"){
if ($a == "dingzhen"){
die( "Hack!!");
}
if (preg_match('/ding.+?zhen/is',$a)){
echo 'Hack!!!';
}
system('ls');
}else{
die("????");
}}
?>
考点:preg_match绕过
PHP利用PCRE回溯次数限制绕过某些安全限制 | 离别歌 (leavesongs.com)
play: POST heizi=ding(a*1000000)zhen
SLsec{coossssadagaLLLLLLLL!}
学姐的凝视
babyre
这道题是西湖论剑2022的原题,网上有大把的wp
easyre
这道题本意是想出难一点的,但由于自身实力不够,不知道写了个什么鸟东西
直接看伪代码
puts("please input your flag:");
scanf("%s", Str);
if ( strlen(Str) == 32 )
{
for ( i = 0; i <= 7; ++i )
v4[i] = Str[i];
v4[8] = 0;
fun1(v4, 8i64, Str1);
Str2 = "f7fae20f2f0b7facff1281fdd1e8fdf6d14cd4c1";
if ( !strcmp(Str1, "f7fae20f2f0b7facff1281fdd1e8fdf6d14cd4c1") )
{
for ( j = 0; j <= 8; ++j )
v8[j] = Str[j + 8];
v8[9] = 0;
fun2(v8, v7);
v13 = "JBUWED{WK";
if ( !strcmp(v7, "JBUWED{WK") )
{
for ( k = 0; k <= 15; ++k )
v5[k] = Str[k + 17];
v12 = (char *)fun3(v5, 15);
v11 = "WPrYVgNoQx6vTPNuU8e!";
if ( !strcmp(v12, "WPrYVgNoQx6vTPNuU8e!") )
{
printf("you are so good!");
free(v12);
return 0;
}
else
{
printf("wrong3!");
return 1;
}
}
else
{
printf("wrong2!");
return 1;
}
}
else
{
printf("wrong1!");
return 1;
}
}
else
{
puts("Error!");
return 1;
}
}
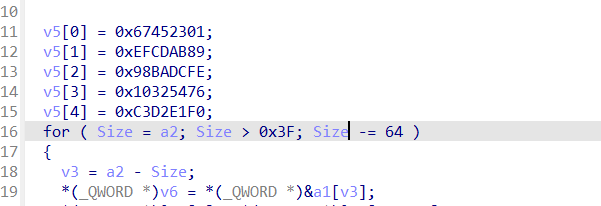
首先就看到flag总共是32位,其中前八位进行了如下加密在fun1里加密
for ( i = 0; i <= 7; ++i ) v4[i] = Str[i]; v4[8] = 0; fun1(v4, 8i64, Str1);
fun1点进去根据特征值可以判断打出来是sha1加密
我们知道flag的格式是SLsec{xxxxx},总共八位,已知6位,所以可以爆破出来前八位
import hashlib
known_prefix = "SLsec{"
known_hash = "f7fae20f2f0b7facff1281fdd1e8fdf6d14cd4c1"
# 枚举后两位字符
for i in range(256):
for j in range(256):
candidate = known_prefix + chr(i) + chr(j)
candidate_hash = hashlib.sha1(candidate.encode()).hexdigest()
if candidate_hash == known_hash:
print("Found the original string: ", candidate)
exit()
接着往下看
for ( j = 0; j <= 8; ++j )
v8[j] = Str[j + 8];
v8[9] = 0;
fun2(v8, v7);
v13 = "JBUWED{WK";
在fun2里加密了flag的第9位到第17位,而且fun2函数也仅仅是一个异或
v3 = strlen(a1); for ( i = 0i64; i < v3; ++i ) a2[i] = (a1[i] ^ 0x66) + 66;
解密
for i in str2: flag += chr(0x66^(ord(i)-66))
接着最后15进行了fun3加密
for ( k = 0; k <= 15; ++k )
v5[k] = Str[k + 17];
v12 = (char *)fun3(v5, 15);
v11 = "WPrYVgNoQx6vTPNuU8e!";
if ( !strcmp(v12, "WPrYVgNoQx6vTPNuU8e!") )
{
printf("you are so good!");
free(v12);
return 0;
}
fun3是一个换表的base64,python也就两行代码的事
最后完整exp
import hashlib
import base64
import string
# 已知信息
flag = ''
known_prefix = "SLsec{"
known_hash = "f7fae20f2f0b7facff1281fdd1e8fdf6d14cd4c1"
# 枚举后两位字符
for i in range(256):
for j in range(256):
candidate = known_prefix + chr(i) + chr(j)
candidate_hash = hashlib.sha1(candidate.encode()).hexdigest()
if candidate_hash == known_hash:
print(candidate,end='')
break;
str2 = 'JBUWED{WK'
for i in str2:
print(chr(0x66^(ord(i)-66)),end='')
str1 = "WPrYVgNoQx6vTPNuU8e!"
string1 = "123456789ABCDEFGHJKLMNPQRSTUVWXYZabcdefghijkmnopqrstuvwxyz+/@!#$"
string2 = "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/"
print (base64.b64decode(str1.translate(str.maketrans(string1,string2))))
#SLsec{confused_soul_run_quietly}
学姐的凝视
猜测账号为QQ号(也可以采用集束炸弹进行爆破)
弱口令爆破即可
进入下载图片二进制打开最下面有base64解密即可。
签到
http://211.69.16.145:3322 在他界面跳转之前抓包,发包即可
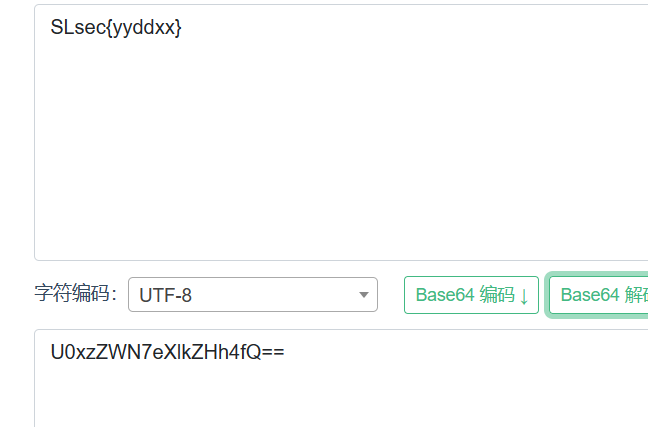
easyCrypto
签到题,看给的python代码,是base加密,分别是16,32,64
import base64 s = '4B555948513653324B3548444F5653484E425947474D4A5A4F425254434F4C494C415A56553344444E5A57474D595A534E523247475233594E524D444751545A4D495A4749364B5A4B345954533D3D3D' print(base64.b64decode(base64.b32decode(base64.b16decode(s))))
你会解方程组不会?
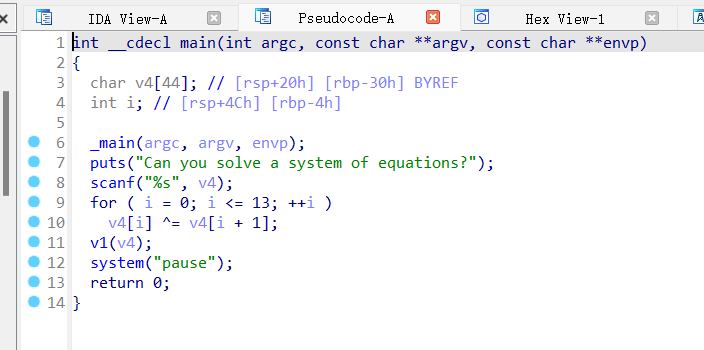
主函数,for循环是对输入的字符出进行异或加密,然后看v1,是一个if函数,函数里面是一堆方程组,我写代码的时候,可能环境问题,导致这个反编译显示代码格式不是很正常,但是不影响写脚本。
from z3 import *
v2 = Int('a2')
v3 = Int('a3')
v4 = Int('a4')
v5 = Int('a5')
v6 = Int('a6')
v7 = Int('a7')
v8 = Int('a8')
v9 = Int('a9')
v10 = Int('a10')
v11 = Int('a11')
v12 = Int('a12')
v13 = Int('a13')
v14 = Int('a14')
v15 = Int('a15')
s = Solver()
s.add(15 * v11
+ -36 * v10
+ 13 * v9
+ 25 * v8
+ 43 * v6
+ 65 * v4
+ 88 * v2
+ 67 * v3
- 5 * v5
+ 89 * v7
+ 11 * v12
+ 47 * v13
- 60 * v14
+ 29 * v15 == 22748,
-41 * v13
+ 2 * v12
+ 8 * v11
+ 7 * v3
+ 89 * v2
+ 12 * v4
- 25 * v5
+ 41 * v6
+ 23 * v7
+ 20 * v8
- 66 * v9
+ 31 * v10
- 39 * v14
+ 17 * v15 == 7258,
-34 * v14
+ 90 * v13
+ 101 * v12
+ -33 * v10
+ 15 * v9
+ 27 * v8
+ 53 * v6
+ 35 * v3
+ 28 * v2
+ 16 * v4
- 65 * v5
+ 39 * v7
+ 13 * v11
+ 23 * v15 == 26190,
(v9 * 128)
+ 81 * v7
+ -59 * v5
+ 35 * v4
+ 34 * v3
+ 23 * v2
+ 49 * v6
+ 25 * v8
- 32 * v10
+ 75 * v11
+ 81 * v12
+ 47 * v13
- 60 * v14
+ 29 * v15 == 37136,
90 * v8
+ 79 * v7
+ 42 * v6
+ -52 * v5
+ 35 * v4
+ 97 * v3
+ 38 * v2
+ 23 * v9
- 36 * v10
+ 57 * v11
+ 81 * v12
+ 42 * v13
- 62 * v14
- 11 * v15 == 27915,
-61 * v14
+ 41 * v12
+ -26 * v10
+ 49 * v7
+ 47 * v6
+ -45 * v5
+ 35 * v4
+ 22 * v2
+ 27 * v3
+ 29 * v8
+ 18 * v9
+ 35 * v11
+ 40 * v13
+ 28 * v15 == 17298,
43 * v13
+ 76 * v12
+ 34 * v11
+ -47 * v10
+ 85 * v9
+ 23 * v8
+ 86 * v7
+ -42 * v6
+ 45 * v3
+ 12 * v2
+ 35 * v4
- 9 * v5
- 44 * v14
+ 65 * v15 == 19875,
57 * v13
+ 25 * v11
+ -30 * v10
+ 86 * v8
+ 79 * v7
+ 35 * v4
+ 62 * v3
+ 79 * v2
- 85 * v5
+ 33 * v6
+ 14 * v9
+ 11 * v12
- 50 * v14
- 9 * v15 == 22784,
47 * v13
+ 2 * v12
+ -36 * v10
+ 2 * v8
+ 29 * v7
+ (v4 * 64)
+ 8 * v2
+ 6 * v3
- 85 * v5
+ 73 * v6
+ 23 * v9
+ 5 * v11
- (v14 * 64)
+ 27 * v15 == 9710,
41 * v12
+ -38 * v10
+ -51 * v5
+ 68 * v4
+ -68 * v3
+ 67 * v2
- 43 * v6
+ 81 * v7
+ 22 * v8
- 12 * v9
+ 75 * v11
+ 27 * v13
- 52 * v14
+ 31 * v15 == 13376,
-67 * v14
+ 31 * v12
+ 15 * v9
+ -51 * v5
+ 63 * v3
+ 85 * v2
+ 5 * v4
+ 44 * v6
+ 36 * v7
+ 28 * v8
- 6 * v10
+ 45 * v11
+ 7 * v13
+ 78 * v15 == 24065,
43 * v13
+ -35 * v10
+ 25 * v8
+ 43 * v6
+ 47 * v2
+ (v3 * 64)
+ 66 * v4
- 5 * v5
+ 112 * v7
+ 13 * v9
+ 95 * v11
+ 21 * v12
- 61 * v14
+ 20 * v15 == 27687,
-61 * v14
+ 47 * v13
+ 89 * v12
+ 14 * v11
+ -92 * v10
+ 56 * v9
+ 23 * v8
+ 89 * v7
+ 49 * v6
+ -25 * v5
+ 85 * v4
+ 67 * v3
+ 89 * v2
- 29 * v15 == 29250,
-60 * v14
+ 51 * v12
+ 16 * v11
+ 12 * v9
+ 25 * v8
+ -43 * v6
+ 34 * v3
+ 95 * v2
+ 62 * v4
- 9 * v5
+ 83 * v7
- 36 * v10
+ 47 * v13
- 24 * v15 == 15317)
if 'un' not in str(s.check()):
print(s.model()) #输出解
direct ={ #这点是方程组解密得到的,顺序已经替换过来了
13 : 74,
3 : 24,
4 : 119,
10 : 108,
12 : 88,
7 : 43,
14 : 88,
9 : 91,
6 : 104,
5 : 7,
8 : 28,
15 : 33,
2 : 10,
11 : 52}
flag = [0 for i in range(15)]
for i in direct:
flag[i-2] = direct[i] #顺序调整
for i in range(13, -1, -1):
flag[i] ^= flag[i + 1] #异或解密
flag_str = ''
for i in range(14):
flag_str += chr(flag[i])
print(flag_str)
主要思路是用z3模块解方程组,z3怎么搞,网上搜,写脚本需要注意的是有的变量顺序替换了,还有就是伪代码的方程组直接复制过来改一下格式就能用。
v2 = a1[2]; v3 = a1[1]; v4 = *a1; v5 = a1[3]; v6 = a1[4]; v7 = a1[5]; v8 = a1[6]; v9 = a1[7]; v10 = a1[9]; v11 = a1[8]; v12 = a1[10]; v13 = a1[11]; v14 = a1[12]; v15 = a1[13];
a1[0]和a1[2]替换了,a1[8]和a1[9]替换了,记得解完方程组,替换过来,再进行异或解密。
然后反编译的时候可能会出现(v9 << 7)这种情况,替换成v9 * 128,如果是(v9 << 6),就替换成v9 * 64.
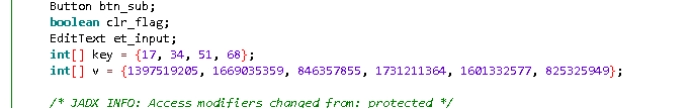
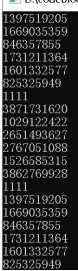
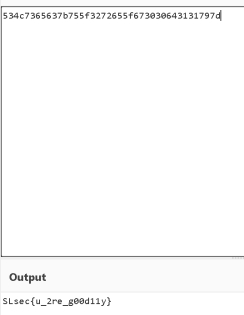
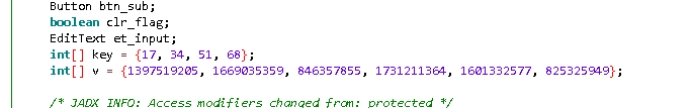
ikun计算器
题目类型:安卓逆向+tea算法
解题思路:用jdax进行反编译后,搜索关键词找到关键代码
找到v和key进行解密
解出十进制转为十六进制,然后在cyberchef用from hex得出flag
Flag:SLsec{u_2re_g00d11y}
easyre1
用ida32位打开附件,shift+f12查找字符串

点进dialogfunc看一下
这里应该是点击19999次会出flag,当然现在已经很明显的看到flag就是
BJD{%d%d2069a45792d233ac},c语言一眼顶针两处%d分别就是19999和0
flag:SLsec{1999902069a45792d233ac}
好玩的时间戳
把压缩包解压后可以看到是一堆文本,在kali里快捷查看文本内容
没什么用
结合题目看一下
随便打开一个文本看一下属性
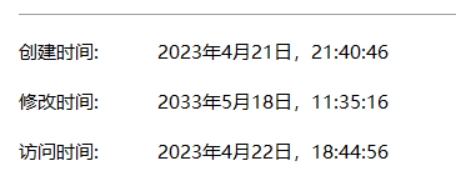
结合时间戳可以找一个网站时间戳转换十进制
时间戳(Unix timestamp)转换工具 - 在线工具
先把题目给的时间转一下

再把文本的修改时间转一下

两者相减就是116,代表的ascii码就是t
剩下的同理,最终得到t1mest@m9
flag:SLsec{t1mest@m9}





















 3320
3320











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








