exeinfope打开发现是64位无壳程序

ida64打开,搜索关键字符串

进入目标字符串的汇编窗口

我们发现无法F5,发现了几处反ida调试,我们进行如下修改:
首先定位标红处,发现jnz和jz矛盾,还有loope这部分代码无用,所以这三行代码都用nop填充,其他一些标红同样是这类问题。

后来我们向下翻还可以发现被main函数调用的loc_C22实际并未申明作为函数,双击进入。

我们发现了里面有一大段未被反编译成功,而且还有可疑指令,猜测是花指令,

光标移到in处,Edit -> Patch program -> change byte查看字节码

in的字节码是E4,后面紧跟一个C7,C7其实就是mov查看字节码索引表
所以基本确定了是花指令,现在顺带把E4改成90(对应操作码是nop)
所有都改完之后,从main开头到retn选中按p申明成一个新函数,再把刚刚的loc_C22申明选中申明成函数,之后就可以F5了。
伪代码如下:
__int64 __fastcall main(int a1, char **a2, char **a3)
{
__int64 result; // rax
char v4; // [rsp+Fh] [rbp-151h]
int v5; // [rsp+10h] [rbp-150h]
int v6; // [rsp+14h] [rbp-14Ch]
char *v7; // [rsp+18h] [rbp-148h]
char v8[10]; // [rsp+26h] [rbp-13Ah] BYREF
_QWORD v9[2]; // [rsp+30h] [rbp-130h] BYREF
int v10; // [rsp+40h] [rbp-120h]
__int64 v11[3]; // [rsp+50h] [rbp-110h] BYREF
char v12; // [rsp+68h] [rbp-F8h]
__int64 v13[3]; // [rsp+70h] [rbp-F0h] BYREF
char v14; // [rsp+88h] [rbp-D8h]
__int64 v15[6]; // [rsp+90h] [rbp-D0h] BYREF
__int16 v16; // [rsp+C0h] [rbp-A0h]
char v17[136]; // [rsp+D0h] [rbp-90h] BYREF
unsigned __int64 v18; // [rsp+158h] [rbp-8h]
v18 = __readfsqword(0x28u);
v5 = 0;
v11[0] = 0LL;
v11[1] = 0LL;
v11[2] = 0LL;
v12 = 0;
v13[0] = 0LL;
v13[1] = 0LL;
v13[2] = 0LL;
v14 = 0;
v15[0] = 0LL;
v15[1] = 0LL;
v15[2] = 0LL;
v15[3] = 0LL;
v15[4] = 0LL;
v15[5] = 0LL;
v16 = 0;
strcpy(
v17,
"**************.****.**s..*..******.****.***********..***..**..#*..***..***.********************.**..*******..**...*..*.*.**.*");
v9[0] = 0LL;
v9[1] = 0LL;
v10 = 0;
v7 = &v17[22];
strcpy(v8, "sctf_9102");
puts("plz tell me the shortest password1:");
scanf("%s", v15);
v6 = 1;
while ( v6 )
{
v4 = *(v15 + v5);
switch ( v4 )
{
case 'w':
v7 -= 5;
break;
case 's':
v7 += 5;
break;
case 'd':
++v7;
break;
case 'a':
--v7;
break;
case 'x':
v7 += 25;
break;
case 'y':
v7 -= 25;
break;
default:
v6 = 0;
break;
}
++v5;
if ( *v7 != 46 && *v7 != 35 )
v6 = 0;
if ( *v7 == 35 )
{
puts("good!you find the right way!\nBut there is another challenge!");
break;
}
}
if ( v6 )
{
puts("plz tell me the password2:");
scanf("%s", v11);
sub_C22(v11, v13);
if ( sub_F67(v13, v8) == 1 )
{
puts("Congratulation!");
puts("Now,this is the last!");
puts("plz tell me the password3:");
scanf("%s", v9);
if ( sub_FFA(v9) == 1 )
{
puts("Congratulation!Here is your flag!:");
printf("sctf{%s-%s(%s)}", v15, v11, v9);
}
else
{
printf("something srong...");
}
result = 0LL;
}
else
{
printf("sorry,somthing wrong...");
result = 0LL;
}
}
else
{
printf("sorry,is't not a right way...");
result = 0LL;
}
return result;
}
一、password1

很明显是个maze,但只有5列,而且还有6个移动键不知道是为什么,参考别的博主的wp原来发现是个立体迷宫。给出迷宫图如下:
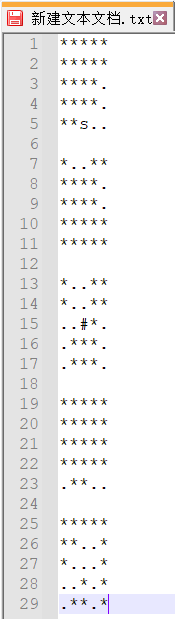
迷宫规则分析如下:
w:上,s:下,a:左,d:右
x:去上一层,y:去下一层。
*:墙, . :路径, #:终点, s:起点。
走一下我们得到ddwwxxssxaxwwaasasyywwdd
二、password2

进入sub_C22函数
unsigned __int64 __fastcall sub_C22(const char *a1, __int64 a2)
{
int v2; // eax
int v3; // eax
int v4; // eax
int v6; // [rsp+14h] [rbp-24Ch]
int v7; // [rsp+18h] [rbp-248h]
int v8; // [rsp+1Ch] [rbp-244h]
int v9; // [rsp+20h] [rbp-240h]
int v10; // [rsp+24h] [rbp-23Ch]
int v11; // [rsp+28h] [rbp-238h]
int v12; // [rsp+2Ch] [rbp-234h]
const char *v13; // [rsp+48h] [rbp-218h]
int v14[130]; // [rsp+50h] [rbp-210h] BYREF
unsigned __int64 v15; // [rsp+258h] [rbp-8h]
v15 = __readfsqword(0x28u);
qmemcpy(v14, &unk_1740, 0x200uLL);
v7 = 3;
v6 = 0;
v9 = 0;
v10 = 0;
v11 = strlen(a1);
v13 = a1;
while ( 1 )
{
v12 = 0;
if ( v9 < v11 )
break;
LABEL_7:
if ( v9 >= v11 )
goto LABEL_8;
}
do
{
if ( a1[v9] != 25 )
break;
++v9;
++v12;
}
while ( v9 < v11 );
if ( v9 != v11 )
{
++v9;
goto LABEL_7;
}
LABEL_8:
v8 = 0;
while ( v11 > 0 )
{
v7 -= v14[*v13] == 64;
v6 = v14[*v13] & 0x3F | (v6 << 6);
if ( ++v8 == 4 )
{
v8 = 0;
if ( v7 )
{
v2 = v10++;
*(v2 + a2) = BYTE2(v6);
}
if ( v7 > 1 )
{
v3 = v10++;
*(v3 + a2) = BYTE1(v6);
}
if ( v7 > 2 )
{
v4 = v10++;
*(v4 + a2) = v6;
}
}
++v13;
--v11;
}
return __readfsqword(0x28u) ^ v15;
}
其实真正有用的代码是下面的while循环里的代码。

里面有个 BYTEn()宏 ,具体请参考IDA逆向常用宏定义
我们根据这段代码可以写爆破脚本:
x= [0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x3E, 0x7F, 0x7F, 0x7F, 0x3F,
0x34, 0x35, 0x36, 0x37, 0x38, 0x39, 0x3A, 0x3B,
0x3C, 0x3D, 0x7F, 0x7F, 0x7F, 0x40, 0x7F, 0x7F,
0x7F, 0x00, 0x01, 0x02, 0x03, 0x04, 0x05, 0x06,
0x07, 0x08, 0x09, 0x0A, 0x0B, 0x0C, 0x0D, 0x0E,
0x0F, 0x10, 0x11, 0x12, 0x13, 0x14, 0x15, 0x16,
0x17, 0x18, 0x19, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x1A, 0x1B, 0x1C, 0x1D, 0x1E, 0x1F, 0x20,
0x21, 0x22, 0x23, 0x24, 0x25, 0x26, 0x27, 0x28,
0x29, 0x2A, 0x2B, 0x2C, 0x2D, 0x2E, 0x2F, 0x30,
0x31, 0x32, 0x33, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F]
l=[0x736374,0x665f39,0x313032]
flag=[]
for a in range(len(l)):
for i in range(32,len(x)):
for j in range(31,len(x)):
for k in range(31,len(x)):
for m in range(31,len(x)):
if ((((x[i]<<6|x[j])<<6)|x[k])<<6)|x[m]==l[a]:
print(chr(i)+chr(j)+chr(k)+chr(m))
如果觉得python太慢,也可试试C语言的exp:
#include <stdio.h>
unsigned int data[128] = {
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x3E, 0x7F, 0x7F, 0x7F, 0x3F,
0x34, 0x35, 0x36, 0x37, 0x38, 0x39, 0x3A, 0x3B,
0x3C, 0x3D, 0x7F, 0x7F, 0x7F, 0x40, 0x7F, 0x7F,
0x7F, 0x00, 0x01, 0x02, 0x03, 0x04, 0x05, 0x06,
0x07, 0x08, 0x09, 0x0A, 0x0B, 0x0C, 0x0D, 0x0E,
0x0F, 0x10, 0x11, 0x12, 0x13, 0x14, 0x15, 0x16,
0x17, 0x18, 0x19, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x1A, 0x1B, 0x1C, 0x1D, 0x1E, 0x1F, 0x20,
0x21, 0x22, 0x23, 0x24, 0x25, 0x26, 0x27, 0x28,
0x29, 0x2A, 0x2B, 0x2C, 0x2D, 0x2E, 0x2F, 0x30,
0x31, 0x32, 0x33, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F
};
int main()
{
int shuju[3] = { 0x736374,0x665f39,0x313032 };
int i0, i1, i2, i3, i4, i5;
for (i0 = 0; i0 < 3; i0++)
{
for(i1=32;i1<128;i1++)
for (i2 = 32; i2 < 128; i2++)
for (i3 = 32; i3 < 128; i3++)
for (i4 = 32; i4 < 128; i4++)
{
i5 = (((((data[i1] << 6) | data[i2]) << 6) | data[i3]) << 6) | data[i4];
if (i5 == shuju[i0])
printf("第%d组:%c%c%c%c\n", i0+1,i1, i2, i3, i4);
}
}
return 0;
}
最终我们得到第二个password。

三、password3
直接进入sub_FFA函数:
__int64 __fastcall sub_FFA(char *a1)
{
int v2; // [rsp+18h] [rbp-158h]
int i; // [rsp+18h] [rbp-158h]
int v4; // [rsp+1Ch] [rbp-154h]
int v5; // [rsp+24h] [rbp-14Ch]
int v6; // [rsp+28h] [rbp-148h]
int v7; // [rsp+2Ch] [rbp-144h]
int v8[16]; // [rsp+30h] [rbp-140h]
int v9[16]; // [rsp+70h] [rbp-100h]
int v10[46]; // [rsp+B0h] [rbp-C0h]
unsigned __int64 v11; // [rsp+168h] [rbp-8h]
v11 = __readfsqword(0x28u);
v8[0] = 0xBE;
v8[1] = 4;
v8[2] = 6;
v8[3] = 128;
v8[4] = 197;
v8[5] = 175;
v8[6] = 118;
v8[7] = 71;
v8[8] = 159;
v8[9] = 204;
v8[10] = 64;
v8[11] = 31;
v8[12] = 216;
v8[13] = 191;
v8[14] = 146;
v8[15] = 239;
v5 = (a1[6] << 8) | (a1[5] << 16) | (a1[4] << 24) | a1[7];
v6 = (a1[10] << 8) | (a1[9] << 16) | (a1[8] << 24) | a1[11];
v7 = (a1[14] << 8) | (a1[13] << 16) | (a1[12] << 24) | a1[15];
v4 = 0;
v2 = 4;
v10[0] = sub_78A((a1[2] << 8) | (a1[1] << 16) | (*a1 << 24) | a1[3]);
v10[1] = sub_78A(v5);
v10[2] = sub_78A(v6);
v10[3] = sub_78A(v7);
do
{
v10[v2] = sub_143B(v10[v4], v10[v4 + 1], v10[v4 + 2], v10[v4 + 3]);
// 加密函数,每个元素都等于该元素的前四个元素做加密,反过来就是v10[n]=v10[n+4] ^ sub_1464(v10[n+1] ^ v10[n+2] ^ v10[n+3]);
++v4;
++v2;
}
while ( v2 <= 29 );
v9[0] = HIBYTE(v10[26]); // v11=v10[26],v11=0xBE040680;
v9[1] = BYTE2(v10[26]);
v9[2] = BYTE1(v10[26]);
v9[3] = LOBYTE(v10[26]);
v9[4] = HIBYTE(v10[27]); // v12=v10[27],v12=0xC5AF7647;
v9[5] = BYTE2(v10[27]);
v9[6] = BYTE1(v10[27]);
v9[7] = LOBYTE(v10[27]);
v9[8] = HIBYTE(v10[28]); // v13=v10[28], v13=0x9FCC401F;
v9[9] = BYTE2(v10[28]);
v9[10] = BYTE1(v10[28]);
v9[11] = LOBYTE(v10[28]);
v9[12] = HIBYTE(v10[29]); // v14=v10[29], v14=0xD8BF92EF;
v9[13] = BYTE2(v10[29]);
v9[14] = BYTE1(v10[29]);
v9[15] = LOBYTE(v10[29]);
for ( i = 0; i <= 15; ++i )
{
if ( v9[i] != v8[i] )
return 0xFFFFFFFFLL;
}
return 1LL;
}
进入加密函数sub_143B,这里的v11,v12,v13,v14我们要把它们跟v10关联起来,双击进入栈窗口,选中v10到v14的栈空间,右键声明为array,我们就能发现伪代码中的v11等变量变成了v10数组元素。
__int64 __fastcall sub_143B(int a1, int a2, int a3, unsigned int a4)
{
return a1 ^ sub_1464(a2 ^ a3 ^ a4);
}
我们再看sub_1464函数。
__int64 __fastcall sub_1464(unsigned int a1)
{
int v2; // [rsp+18h] [rbp-498h]
int v3[290]; // [rsp+20h] [rbp-490h] BYREF
unsigned __int64 v4; // [rsp+4A8h] [rbp-8h]
v4 = __readfsqword(0x28u);
qmemcpy(v3, &unk_1940, 0x480uLL);
v2 = (v3[BYTE2(a1)] << 16) | v3[a1] | (v3[BYTE1(a1)] << 8) | (v3[HIBYTE(a1)] << 24);// 取输入值作为下标从表中取值再组合。
return __ROL4__(v2, 12) ^ (__ROL4__(v2, 8) ^ __ROR4__(v2, 2)) ^ __ROR4__(v2, 6);// (循环移位宏)循环左右移不同位之后再异或取值。
}
对于v10数组,每个元素都等于该元素的前四个元素做sub_143B加密,逆向分析过来就是v10[n]=v10[n+4] ^ sub_1464(v10[n+1] ^ v10[n+2] ^ v10[n+3]),我们现在已经知道了v10数组的后四个元素,就可以反推之前的元素。
根据加密代码写exp:
#include <stdio.h>
#include "defs.h"
unsigned int ROR4(unsigned int x, int y)
{
return (x << (32 - y) | x >> y) & 0xffffffff;
}
unsigned int ROL4(unsigned int x, int y)
{
return (x >> (32 - y) | x << y) & 0xffffffff;
}
__int64 sub_1464(unsigned int a1)
{
int v2;
unsigned int v3[288] = {
0xD6, 0x90, 0xE9, 0xFE, 0xCC, 0xE1, 0x3D, 0xB7,
0x16, 0xB6, 0x14, 0xC2, 0x28, 0xFB, 0x2C, 0x05,
0x2B, 0x67, 0x9A, 0x76, 0x2A, 0xBE, 0x04, 0xC3,
0xAA, 0x44, 0x13, 0x26, 0x49, 0x86, 0x06, 0x99,
0x9C, 0x42, 0x50, 0xF4, 0x91, 0xEF, 0x98, 0x7A,
0x33, 0x54, 0x0B, 0x43, 0xED, 0xCF, 0xAC, 0x62,
0xE4, 0xB3, 0x1C, 0xA9, 0xC9, 0x08, 0xE8, 0x95,
0x80, 0xDF, 0x94, 0xFA, 0x75, 0x8F, 0x3F, 0xA6,
0x47, 0x07, 0xA7, 0xFC, 0xF3, 0x73, 0x17, 0xBA,
0x83, 0x59, 0x3C, 0x19, 0xE6, 0x85, 0x4F, 0xA8,
0x68, 0x6B, 0x81, 0xB2, 0x71, 0x64, 0xDA, 0x8B,
0xF8, 0xEB, 0x0F, 0x4B, 0x70, 0x56, 0x9D, 0x35,
0x1E, 0x24, 0x0E, 0x5E, 0x63, 0x58, 0xD1, 0xA2,
0x25, 0x22, 0x7C, 0x3B, 0x01, 0x21, 0x78, 0x87,
0xD4, 0x00, 0x46, 0x57, 0x9F, 0xD3, 0x27, 0x52,
0x4C, 0x36, 0x02, 0xE7, 0xA0, 0xC4, 0xC8, 0x9E,
0xEA, 0xBF, 0x8A, 0xD2, 0x40, 0xC7, 0x38, 0xB5,
0xA3, 0xF7, 0xF2, 0xCE, 0xF9, 0x61, 0x15, 0xA1,
0xE0, 0xAE, 0x5D, 0xA4, 0x9B, 0x34, 0x1A, 0x55,
0xAD, 0x93, 0x32, 0x30, 0xF5, 0x8C, 0xB1, 0xE3,
0x1D, 0xF6, 0xE2, 0x2E, 0x82, 0x66, 0xCA, 0x60,
0xC0, 0x29, 0x23, 0xAB, 0x0D, 0x53, 0x4E, 0x6F,
0xD5, 0xDB, 0x37, 0x45, 0xDE, 0xFD, 0x8E, 0x2F,
0x03, 0xFF, 0x6A, 0x72, 0x6D, 0x6C, 0x5B, 0x51,
0x8D, 0x1B, 0xAF, 0x92, 0xBB, 0xDD, 0xBC, 0x7F,
0x11, 0xD9, 0x5C, 0x41, 0x1F, 0x10, 0x5A, 0xD8,
0x0A, 0xC1, 0x31, 0x88, 0xA5, 0xCD, 0x7B, 0xBD,
0x2D, 0x74, 0xD0, 0x12, 0xB8, 0xE5, 0xB4, 0xB0,
0x89, 0x69, 0x97, 0x4A, 0x0C, 0x96, 0x77, 0x7E,
0x65, 0xB9, 0xF1, 0x09, 0xC5, 0x6E, 0xC6, 0x84,
0x18, 0xF0, 0x7D, 0xEC, 0x3A, 0xDC, 0x4D, 0x20,
0x79, 0xEE, 0x5F, 0x3E, 0xD7, 0xCB, 0x39, 0x48,
0xC6, 0xBA, 0xB1, 0xA3, 0x50, 0x33, 0xAA, 0x56,
0x97, 0x91, 0x7D, 0x67, 0xDC, 0x22, 0x70, 0xB2,
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00
};
v2 = (v3[BYTE2(a1)] << 16) | v3[(unsigned __int8)a1] | (v3[BYTE1(a1)] << 8) | (v3[HIBYTE(a1) ] << 24);
return ROL4(v2, 12) ^ (unsigned int)(ROL4(v2, 8) ^ ROR4(v2, 2)) ^ ROR4(v2, 6);
}
int main()
{
int n = 25;
unsigned int v10[30] = { 0 };
v10[26] = 0xBE040680;
v10[27] = 0xC5AF7647;
v10[28] = 0x9FCC401F;
v10[29] = 0xD8BF92EF;
do
{
v10[n] =v10[n + 4] ^ sub_1464(v10[n + 1] ^ v10[n + 2] ^ v10[n + 3]);
--n;
} while (n >= 0);
for (int i = 0; i < 4; i++)
printf("%c%c%c%c", ((char*)&v10[i])[0], ((char*)&v10[i])[1], ((char*)&v10[i])[2], ((char*)&v10[i])[3]);
return 0;
}
因为要用到ida的宏,所以我调用了一个ida自带的头文件,这个defs.h头文件可以在ida安装目录下plugins文件夹下找到,我们把它导入。
然后我还自定义了循环移位函数,因为我导入之后发现直接用ida的循环移位宏会莫名报错,说是未检测到这个宏,目前尚未解决这个问题,欢迎各路大佬评论区解惑。
我们自此得到password3:** fl4g_is_s0_ug1y! **

四、最后
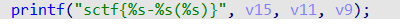
三个password组合得到flag:
flag{ddwwxxssxaxwwaasasyywwdd-c2N0Zl85MTAy(fl4g_is_s0_ug1y!)}























 5964
5964











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










