64位无壳

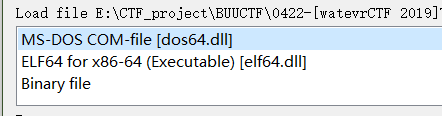
.com文件?拖到ida64看看

反汇编不出来。
但拖入ida64时显示了elf,去掉后缀改成elf应该就可以正常显示汇编代码了。
查看main函数代码如下:
int __cdecl main(int argc, const char **argv, const char **envp)
{
signal(14, sig);
alarm(1u);
delay(6000000LL);
can_continue = 1337;
return 0;
}
是几个反调试函数,主函数里是看不出什么了。
一个个翻function发现一个generate函数很可疑,if里的条件竟然就是main函数末尾的can_continue = 1337,应该是这个关键函数没错了。
unsigned __int64 generate()
{
char s[131]; // [rsp+0h] [rbp-B0h] BYREF
char v2[14]; // [rsp+83h] [rbp-2Dh] BYREF
char v3[31]; // [rsp+91h] [rbp-1Fh] BYREF
*(_QWORD *)&v3[23] = __readfsqword(0x28u);
if ( can_continue == 1337 )
{
s[64] = 35;
s[65] = 60;
s[66] = 73;
s[67] = 100;
s[68] = 85;
s[69] = 46;
s[70] = 119;
s[71] = 32;
s[72] = 45;
s[73] = 115;
s[74] = 63;
s[75] = 125;
s[76] = 44;
s[77] = 56;
s[78] = 108;
s[79] = 83;
s[80] = 84;
s[81] = 42;
s[82] = 90;
s[83] = 106;
s[84] = 87;
s[85] = 58;
s[86] = 102;
s[87] = 94;
s[88] = 77;
s[89] = 54;
s[90] = 101;
s[91] = 110;
s[92] = 112;
s[93] = 104;
s[94] = 99;
s[95] = 47;
s[96] = 79;
s[97] = 118;
s[98] = 37;
s[99] = 75;
s[100] = 11;
s[101] = 52;
s[102] = 76;
s[103] = 82;
s[104] = 103;
s[105] = 96;
s[106] = 95;
s[107] = 69;
s[108] = 123;
s[109] = 114;
s[110] = 59;
s[111] = 126;
s[112] = 74;
s[113] = 10;
s[114] = 107;
s[115] = 113;
s[116] = 67;
s[117] = 36;
s[118] = 92;
s[119] = 40;
s[120] = 34;
s[121] = 64;
s[122] = 50;
s[123] = 68;
s[124] = 98;
s[125] = 80;
s[126] = 13;
s[127] = 38;
s[128] = 49;
s[129] = 55;
s[130] = 12;
qmemcpy(v2, "]y>=xaVYA[BF3", 13);
v2[13] = (unsigned __int8)&unk_400BB4;
strcpy(v3, "!tQHu0Xi5|\t9N+zmG)o");
strcpy(s, "watevr{3ncrytion_is_overrated_youtube.com/watch?v=OPf0YbXqDm0}");
puts(s);
}
return __readfsqword(0x28u) ^ *(_QWORD *)&v3[23];
}
嫌弃变量太多,我选择直接进入栈空间从上到下选中变量右击申明成arry

现在变成了下面的伪代码:
unsigned __int64 generate()
{
_QWORD s[22]; // [rsp+0h] [rbp-B0h] BYREF
s[21] = __readfsqword(0x28u);
if ( can_continue == 1337 )
{
qmemcpy(&s[8], "#<IdU.w -s?},8lST*ZjW:f^M6enphc/Ov%K\v4LRg`_E{r;~J\nkqC$\\(\"@2DbP\r&17", 66);
BYTE2(s[16]) = 12;
qmemcpy(&s[16] + 3, "]y>=xaVYA[BF3", 13);
LOBYTE(s[18]) = &unk_400BB4;
strcpy(&s[18] + 1, "!tQHu0Xi5|\t9N+zmG)o");
strcpy(s, "watevr{3ncrytion_is_overrated_youtube.com/watch?v=OPf0YbXqDm0}");
puts(s);
}
return __readfsqword(0x28u) ^ s[21];
}
发现这道题其实打开generate就能找到flag,虽说前面有一些字符串的操作,但最后s是被flag给覆盖了,看来是一道水题。。
flag{3ncrytion_is_overrated_youtube.com/watch?v=OPf0YbXqDm0}























 1811
1811











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










