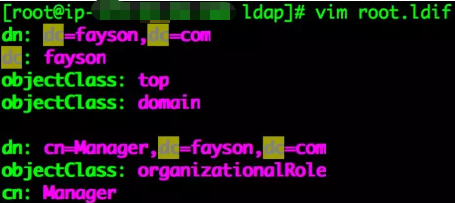
129.1 导入根域及管理员账号
- root.ldif文件创建
[root@ip-xxx-xx-xx-xxx ldap]# vim root.ldif
dn: dc=fayson,dc=com
dc: fayson
objectClass: top
objectClass: domain
dn: cn=Manager,dc=fayson,dc=com
objectClass: organizationalRole
cn: Manager
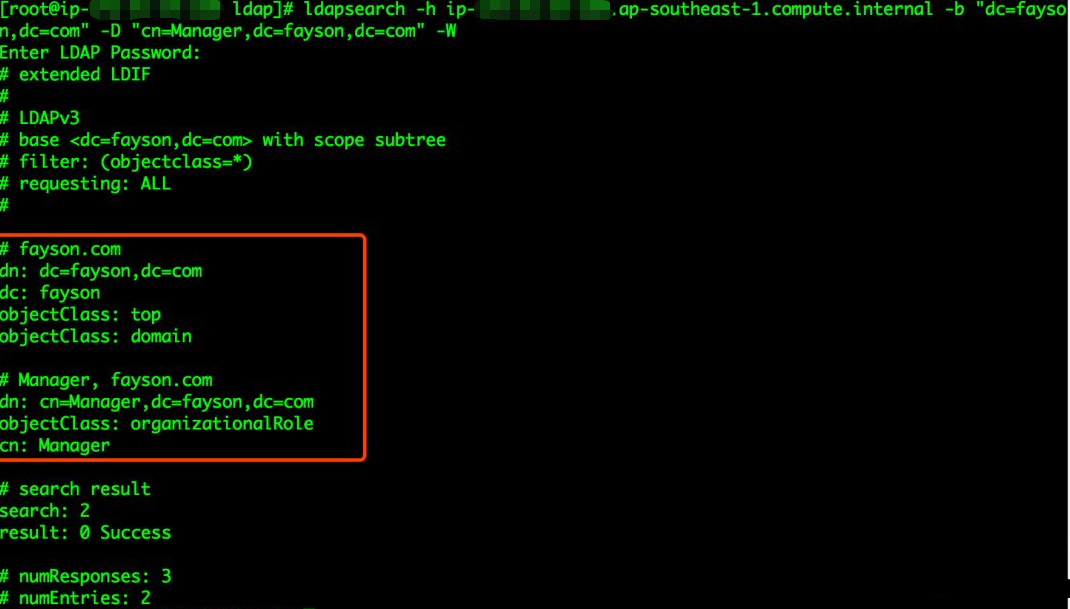
- 导入根域及管理员信息
[root@ip-xxx-xx-xx-xxx ldap]# ldapadd -D "cn=Manager,dc=fayson,dc=com" -W -x -f root.ldif
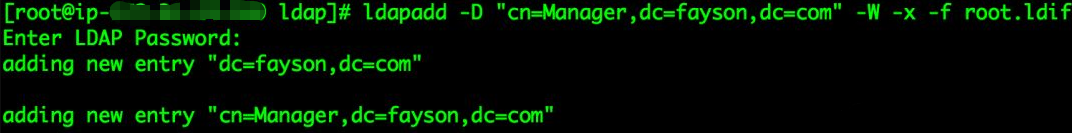
- 查看是否导入成功
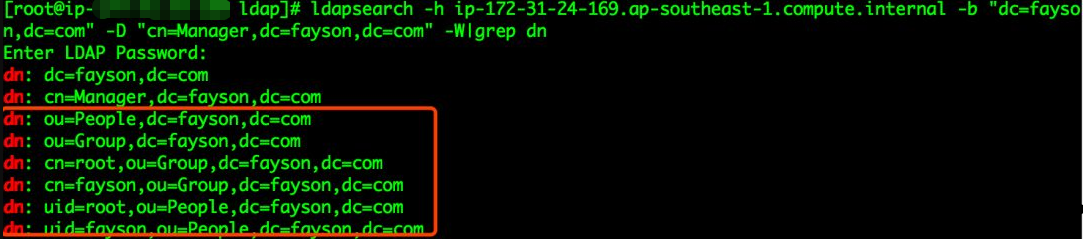
[root@ip-xxx-xx-xx-xxx ldap]# ldapsearch -h ip-xxx-xx-xx-xxx.ap-southeast-1.compute.internal -b "dc=fayson,dc=com" -D "cn=Manager,dc=fayson,dc=com" -W
129.2 导入基础文件及用户和用户组
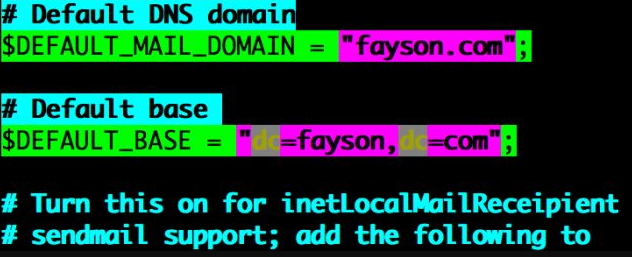
- migrate_common.ph文件修改
# Default DNS domain
$DEFAULT_MAIL_DOMAIN = "fayson.com";
# Default base
$DEFAULT_BASE = "dc=fayson,dc=com";
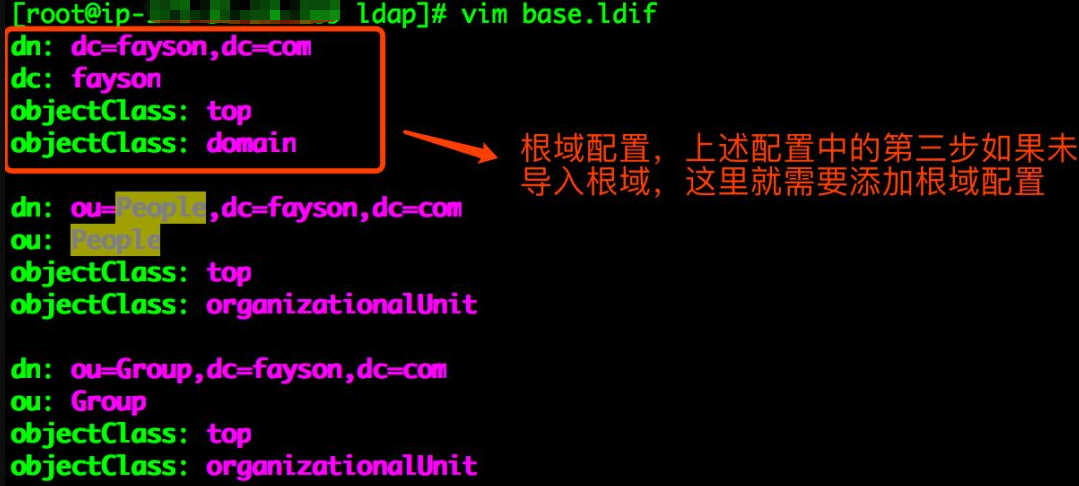
- OpenLdap的base.ldif文件导出
[root@ip-xxx-xx-xx-xxx ldap]# /usr/share/migrationtools/migrate_base.pl >base.ldif
[root@ip-xxx-xx-xx-xxx ldap]# ll
[root@ip-xxx-xx-xx-xxx ldap]# vim base.ldif

- 配置Fayson
dn: ou=People,dc=fayson,dc=com
ou: People
objectClass: top
objectClass: organizationalUnit
dn: ou=Group,dc=fayson,dc=com
ou: Group
objectClass: top
objectClass: organizationalUnit
- 操作系统的group.ldif文件导出
[root@ip-xxx-xx-xx-xxx ldap]# /usr/share/migrationtools/migrate_group.pl /etc/group > group.ldif
[root@ip-xxx-xx-xx-xxx ldap]# ll
[root@ip-xxx-xx-xx-xxx ldap]# vim group.ldif
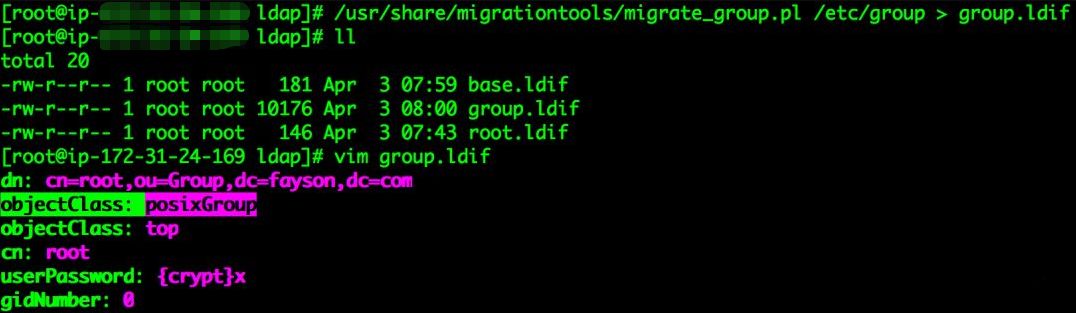
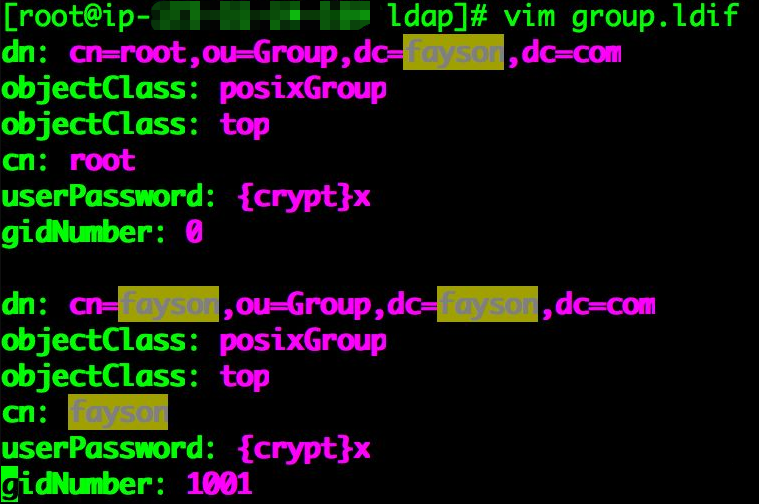
# 根据需要删除不需要导入OpenLDAP服务的group,如下是Fayson的配置
dn: cn=root,ou=Group,dc=fayson,dc=com
objectClass: posixGroup
objectClass: top
cn: root
userPassword: {crypt}x
gidNumber: 0
dn: cn=fayson,ou=Group,dc=fayson,dc=com
objectClass: posixGroup
objectClass: top
cn: fayson
userPassword: {crypt}x
gidNumber: 1001
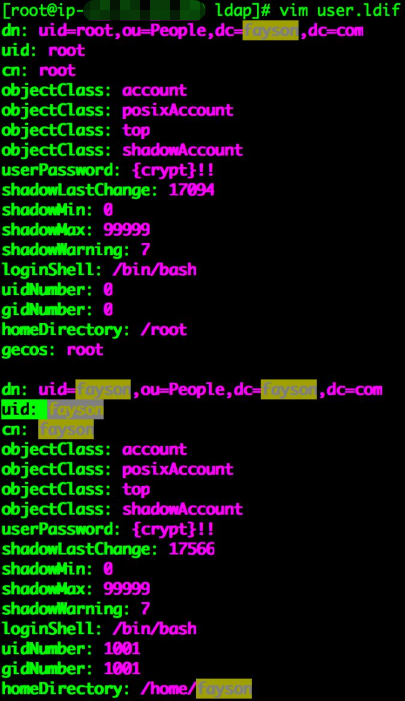
- 用户的ldif文导出
[root@ip-xxx-xx-xx-xxx ldap]# /usr/share/migrationtools/migrate_passwd.pl /etc/passwd >user.ldif
[root@ip-xxx-xx-xx-xxx ldap]# ll
[root@ip-xxx-xx-xx-xxx ldap]# vim user.ldif

# 根据需要保留user.ldif文件中需要导入OpenLDAP服务的用户信息,注意用户信息与group.ldif中组的对应,否则会出现用户无相应组的问题,如下是Fayson的配置
dn: uid=root,ou=People,dc=fayson,dc=com
uid: root
cn: root
objectClass: account
objectClass: posixAccount
objectClass: top
objectClass: shadowAccount
userPassword: {crypt}!!
shadowLastChange: 17094
shadowMin: 0
shadowMax: 99999
shadowWarning: 7
loginShell: /bin/bash
uidNumber: 0
gidNumber: 0
homeDirectory: /root
gecos: root
dn: uid=fayson,ou=People,dc=fayson,dc=com
uid: fayson
cn: fayson
objectClass: account
objectClass: posixAccount
objectClass: top
objectClass: shadowAccount
userPassword: {crypt}!!
shadowLastChange: 17566
shadowMin: 0
shadowMax: 99999
shadowWarning: 7
loginShell: /bin/bash
uidNumber: 1001
gidNumber: 1001
homeDirectory: /home/fayson
- 基础文件及用户和组导入OpenLDAP
ldapadd -D "cn=Manager,dc=fayson,dc=com" -W -x -f base.ldif
ldapadd -D "cn=Manager,dc=fayson,dc=com" -W -x -f group.ldif
ldapadd -D "cn=Manager,dc=fayson,dc=com" -W -x -f user.ldif

- 查看是否导入成功
ldapsearch -h ip-xxx-xx-xx-xxx.ap-southeast-1.compute.internal -b "dc=fayson,dc=com" -D "cn=Manager,dc=fayson,dc=com" -W|grep dn
129.3 客户端配置
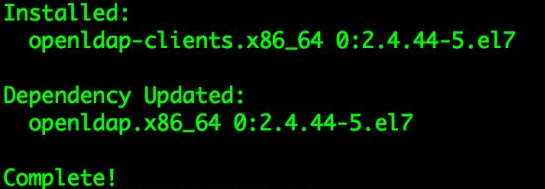
- 在ip-xxx-xx-xx-xxx节点安装OpenLDAP的客户端软件包
[root@ip-xxx-xx-xx-xxx ~]# yum -y install openldap-clients
- /etc/openldap/ldap.conf文件修改
[root@ip-xxx-xx-xx-xxx ~]# yum -y install openldap-clients
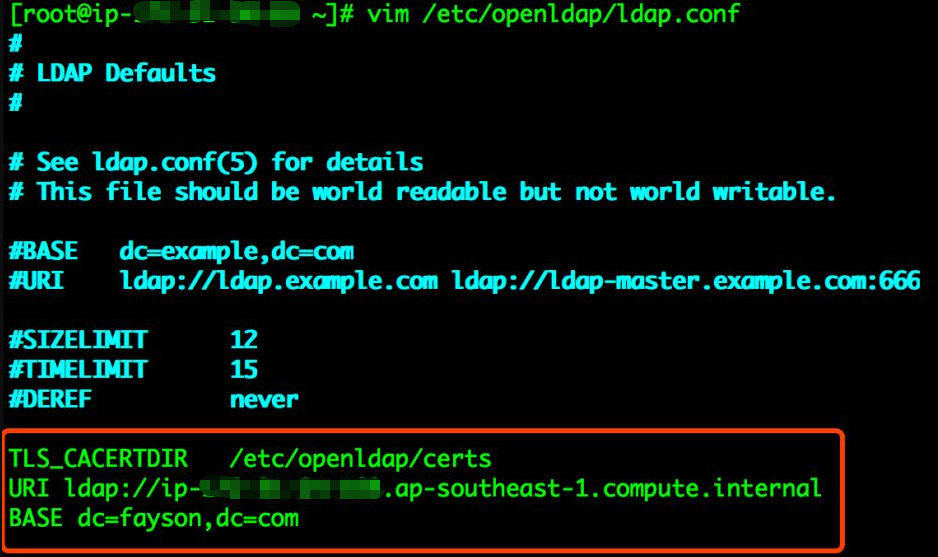
[root@ip-xxx-xx-xx-xxx ~]# vim /etc/openldap/ldap.conf
#
# LDAP Defaults
#
# See ldap.conf(5) for details
# This file should be world readable but not world writable.
#BASE dc=example,dc=com
#URI ldap://ldap.example.com ldap://ldap-master.example.com:666
#SIZELIMIT 12
#TIMELIMIT 15
#DEREF never
TLS_CACERTDIR /etc/openldap/certs
URI ldap://ip-xxx-xx-xx-xxx.ap-southeast-1.compute.internal
BASE dc=fayson,dc=com
# Turning this off breaks GSSAPI used with krb5 when rdns = false
SASL_NOCANON on
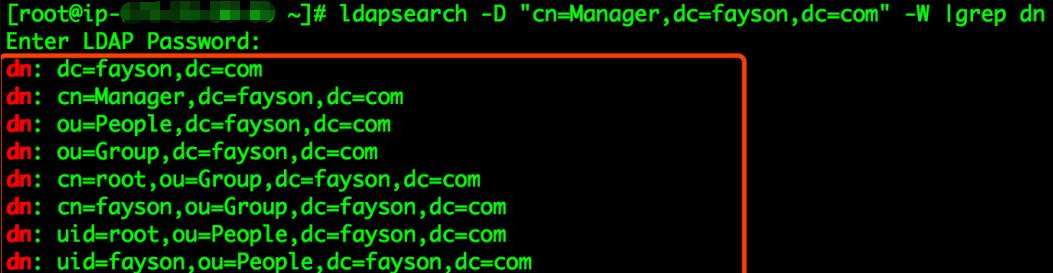
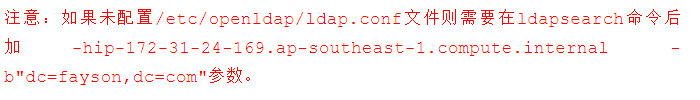
- 是否配置成功
[root@ip-xxx-xx-xx-xxx ~]# ldapsearch -D "cn=Manager,dc=fayson,dc=com" -W |grep dn
大数据视频推荐:
CSDN
人工智能算法竞赛实战
AIops智能运维机器学习算法实战
ELK7 stack开发运维实战
PySpark机器学习从入门到精通
AIOps智能运维实战
大数据语音推荐:
ELK7 stack开发运维
企业级大数据技术应用
大数据机器学习案例之推荐系统
自然语言处理
大数据基础
人工智能:深度学习入门到精通






















 1151
1151











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








