题目地址
SycloverTeam提供了题目的docker环境
https://github.com/SycloverTeam/SCTF2021/tree/master/web/Upload_it_1
wp
首先题目给了composer.json
{
"name": "sctf2021/upload",
"authors": [
{
"name": "AFKL",
"email": "upload@qq.com"
}
],
"require": {
"symfony/string": "^5.3",
"opis/closure": "^3.6"
}
}
导入了两个包,那就肯定是组件相关的攻击了
"symfony/string": "^5.3",
"opis/closure": "^3.6"
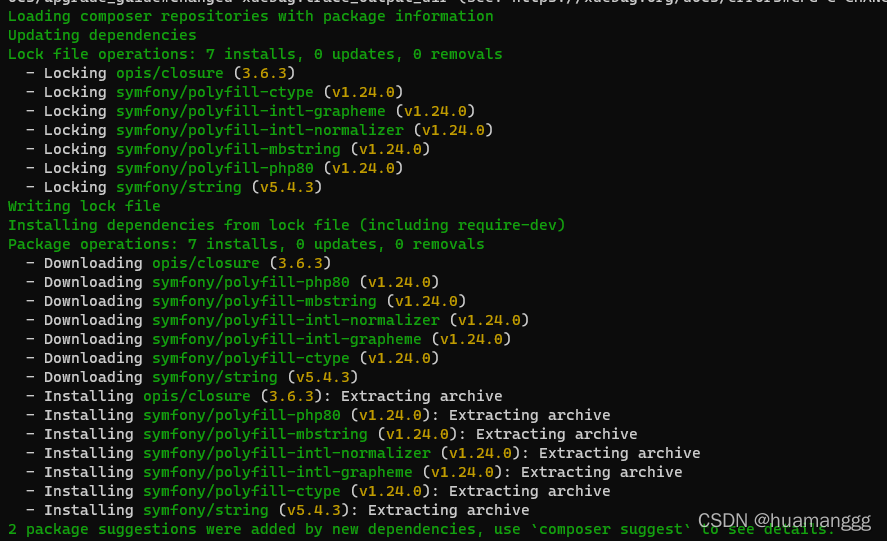
composer update一下
第二个组件是关于闭包反序列化的,所以猜测和序列化有关
index.php内的主要逻辑代码
if (!empty($_POST['path'])) {
$upload_file_path = $_SESSION["upload_path"]."/".$_POST['path'];
$upload_file = $upload_file_path."/".$file['name'];
} else {
$upload_file_path







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章
















 464
464











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










